Best Website Defacement Monitoring Tools in 2026

Stay up-to-date with the latest trends in the tech business world in just 3 Minutes! Join →
Sandeep Babu covers cybersecurity for Techreport. He holds an MA in English literature from Jamia Millia Islamia, New Delhi, and has completed multiple cybersecurity certifications, including the ISC2 Certified in Cybersecurity, Google Cybersecurity Professional Certificate, and many more. Sandeep Babu has been writing in the field of cybersecurity since 2019. Earlier, he wrote about cybersecurity for Geekflare, Make Use of, Small Business Trends, and Cloudwards.
Best Website Defacement Monitoring Tools in 2026

15 Open Source Vulnerability Scanners for 2026
18 Best Remote Desktop Software for SMBs in 2026

13 Best DDoS Protection Services in 2026

Best Network Mapping Software (2026)

15 Best Web Vulnerability Scanner in 2026 to Protect Against Attacks
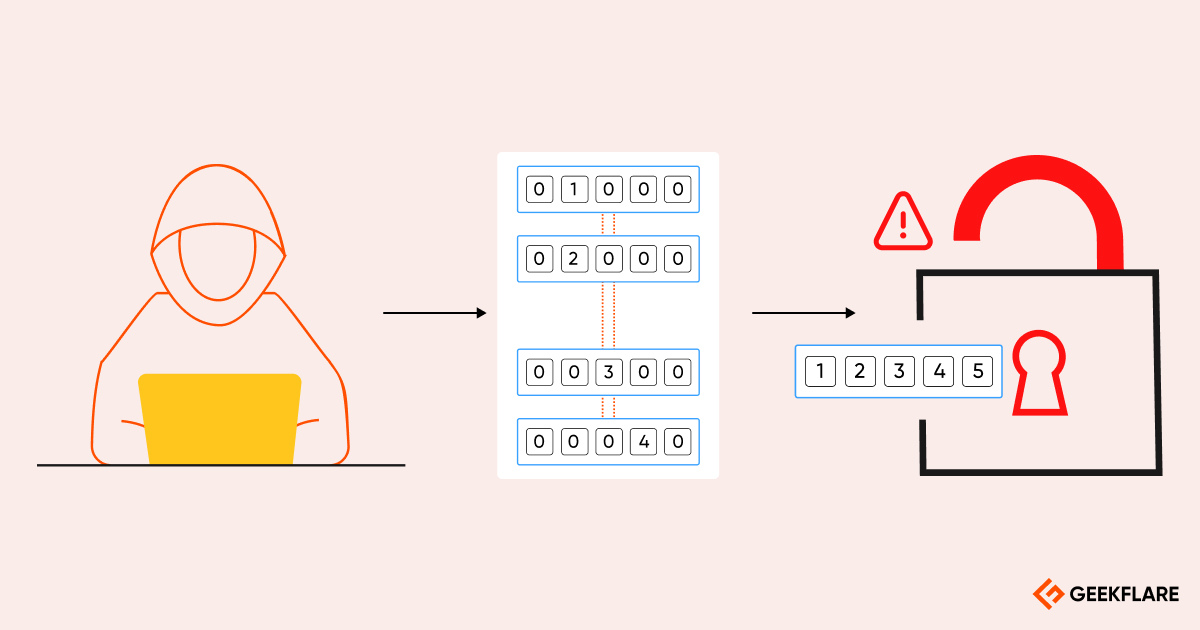
Top Brute Force Attack Tools (2026)

Top 12 Attack Surface Management Software in 2026

11 Best Network Access Control Solutions for Businesses in 2026

Is Dashlane Worth the Hype? My Testing Experience

18 Best Web Application Firewall Software [Top Picks]

13 Best GRC Tools to Manage Risk and Compliance

9 Best WiFi Analyzer to Optimize Your Network
How to Find the Subdomains of a Domain

13 Best Managed Firewalls To Safeguard Cloud Infrastructure

Best Website Malware Scanner To Find Security Risks

11 Open Source Firewall to Protect Web Application and Network

13 Best EDR Tools to Detect and Respond to Cyberattacks

Control D Review: Hands-On Testing of Its Business DNS Filtering
8 Best Data Security Solutions to Safeguard Your Business

36 Best Privacy Tools to Protect Your Digital Identity

MalCare Review: Testing Its WordPress Malware Defense

12 Best DAST Scanners for App & API Security

HostedScan Review: Features, Use Cases, Pros, Cons, and Pricing

How to Find SQL Injection Attack Vulnerabilities?

Top 12 E-Commerce Security Threats and How To Protect Your Shop

WPScan: Find WordPress Security Vulnerabilities

Information Security Management System (ISMS) Explained in 5 Minutes or Less

SIEM vs. SOAR: Which Tool Is Right for Your Security Needs?

13 Best SIEM Tools to Analyze and Manage Security Events [Free & Paid]