Enhanced Linked Mode (ELM) is one of the vSphere advanced features that allows connecting multiple vCenter Servers to provide a single interface where you can view, search, and manage permissions, replications of roles, policies, and licenses between various vCenter Servers.
It allows you to simplify enterprise virtual environments deployed in the same or multiple sites with multiple vCenter Server while deploying vCenter Server as VCSA or Windows Servers.
How does It work?
Enhanced Linked Mode (ELM) offers a single pane of glass across multiple vCenter Servers in the same vSphere Single-Sign-On (SSO) domain that allows virtual infrastructure engineers to easily manage different virtual environments i-e virtual desktop environment and a virtual server environment across multiple sites.
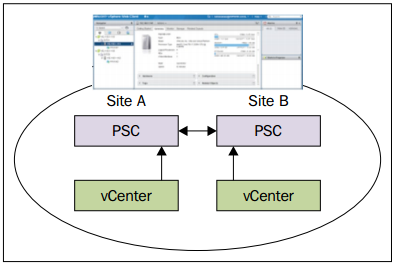
ELM doesn’t work with the standard vSphere Client; it is only supported with vSphere Web Client, and once enabled, the inventories of all vCenters that are part of the same SSO domain will be linked in Enhanced Linked Mode. Their accessibility will be managed from a single web client interface.
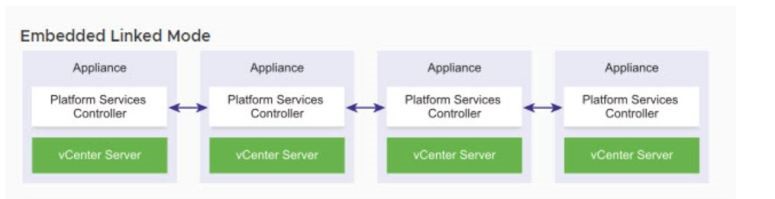
Initially, in vSphere 6.0, Platform Services Controller (PSC) was introduced as Embedded PSC for single vCenter Server and External PSC to manage multiple vCenter Servers. But, from vSphere 6.5 U2 and vSphere 6.7 onwards, External PSC has been deprecated, and Embedded PSC is recommended to manage multiple vCenter Servers and to deploy vCenter Server Appliance (VCSA) with embedded PSCs will be used now and onward and can also utilize VCSA as High Availability (HA) if it requires for your virtual data center that makes it easier to manage as vCenter and PSC on the same nodes.
vSphere 6.7 supports up to 15 nodes with vCenter Server in Enhanced Linked Mode with embedded PSC and also supports vCenter HA and vCSA backup and restores features.
Benefits of Enhanced Linked Mode with Embedded PSC
Following are some advantages of Enhanced Linked Mode (ELM) with Embedded PSC:
- A simplified backup and restore process without a separate backup appliance
- Offers pretty simplified domain architecture while managing multiple sites even without external PSC
- Simplified HA process without using a load balancer while managing up to 15 vCenter Server Appliances in Embedded Linked Mode
- Three nodes are considered as one logical vCenter Server node for vCenter HA.
There are two stages to configure vCenter Server in Embedded Linked Mode.
#1: Deploying the 1st vCenter appliance
Mount vCSA to any of the systems where you want to deploy it.
Access the host via vSphere Client to deploy the VCSA OVF, select Create/Register VM, and select the Creation Type. Select Deploy a Virtual Machine from an OVF or OVA file option and follow the installation Wizard.
Please write down SSO credentials and domain names somewhere for later use.
Once the 1st vCenter is configured correctly, we will deploy the 2nd vCenter Appliance in Linked Mode. The following are some steps to configure Stage 2 of the 2nd vCenter Server Appliance.
# 2: Deployment of the 2nd vCenter appliance in the linked mode
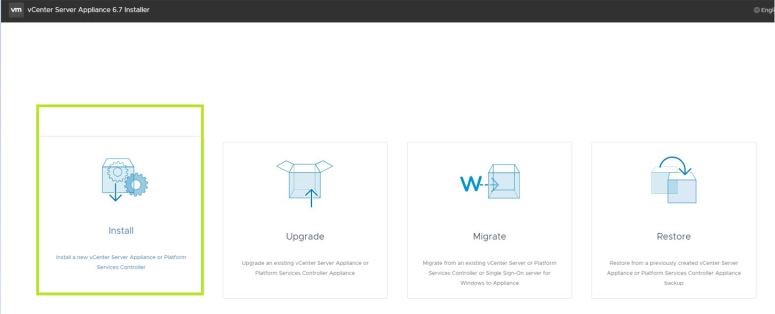
- Run the installer by navigating to the \vcsa-ui-installer\ directory, and for Windows OS, go to the win32 subdirectory, and run the installer.exe
- Click on Install
- Click Next
- Accept the End User License Agreement (EULA) and click Next to continue to the wizard.
- Select vCenter Server with an Embedded Platform Services Controller from the vCenter Server Appliance.
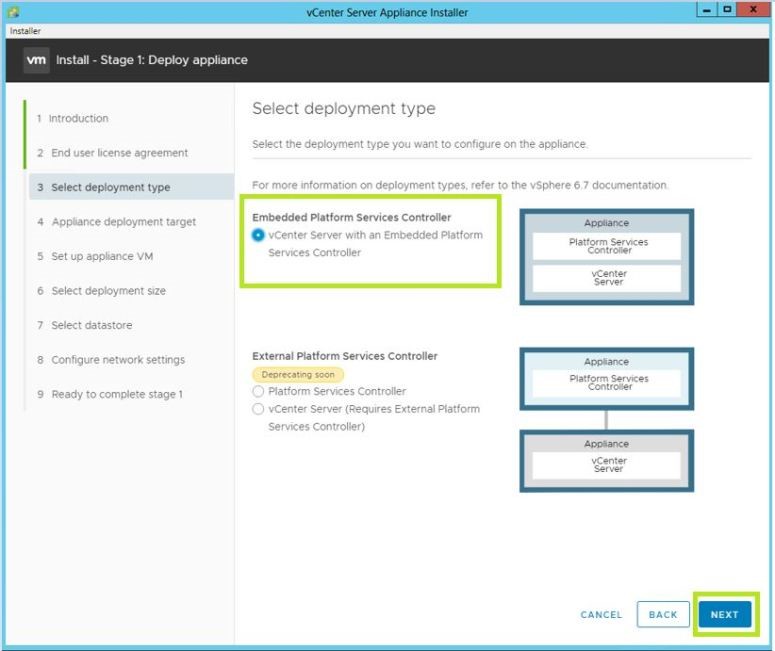
- Click Next
- Enter the Credentials and Fully Qualified Domain Name (FQDN) of the ESXi host where you would like them to install the vCenter Appliance (vCSA).
- And follow the Wizard to install the 2nd vCenter Server Appliance.
- In the end, Click Finish and wait for the deployment to complete Stage 1.
- Once the deployment is completed, click Continue to go to Stage 2, where the deployed appliance for embedded linked will be configured.
- Follow the installation wizard, and select the Join an existing SSO domain option to join the existing SSO domain of the first deployed Embedded PSC vCSA.
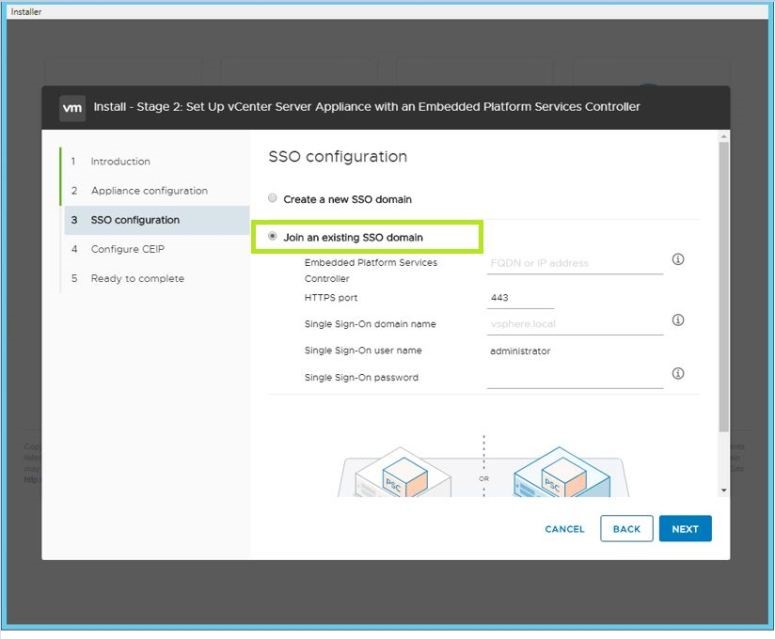
- Now, enter the FQDN of the first vCSA with Embedded PSC: <FQDN of the first vCenter>
- Now, enter the following information:
- HTTPS port: 443
- Single Sign-On domain name: vsphere.local
- Single Sign-On user name is administrator
- Single Sign-On password
- Follow the Wizard, Review the summary on the Ready to complete Install – Stage 2 page, verify settings, and click Finish.
- Wait for the Setup to Complete. Once the Setup is complete, click Close.
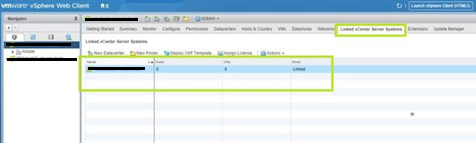
- Now, you can navigate to login to your vCenter Web client page and verify that both the vCenter Servers are enlisted.

- Select Linked vCenter Server Systems to verify the Enhanced Embedded Linked Mode.
I hope you have enjoyed reading this post. Next, you can read VMWare Interview Questions and Answers.


