A temporary email generator creates short-term email addresses that disappear after a while. It helps avoid spam, protect your main email, and sign up for websites without sharing personal details.
Using a temporary email keeps your inbox clean, protects your privacy, and reduces the risk of scams when signing up for services or free trials.
Note: Temp emails should not be used for sensitive data transmission as they might be processed through third-party infrastructure with low security.
To help you pick the right platform, I have tested 16 options and selected the following temporary mail generators considering their key features, security, and more.
- 1. Guerrilla Mail
- 2. Mailinator
- 3. Temp Mail
- 4. Tempmailo
- 5. EmailOnDeck
- 6. 10 Minute Mail
- 7. YOPmail
- 8. MailTicking
- 9. AdGuard
- 10. Internxt
- Show less
You can trust Geekflare
At Geekflare, trust and transparency are paramount. Our team of experts, with over 185 years of combined experience in business and technology, tests and reviews software, ensuring our ratings and awards are unbiased and reliable. Learn how we test.
1. Guerrilla Mail
Guerrilla Mail is a widely used disposable email service that allows users to create temporary email addresses instantly. It helps users protect their primary inbox from spam, phishing attempts, and unwanted messages.
Here is a screenshot of Guerrilla Mail, a temp email generator. It shows a disposable email address and an inbox with a welcome message. You can receive emails and use features like “Scramble Address” for added privacy.

The service is entirely free, does not require registration, and allows both receiving and sending emails. Emails remain active for an hour before they are automatically deleted, ensuring enhanced anonymity.
Guerrilla Mail Key Features
- Get an instant temporary email with no registration.
- Scramble your email address for added privacy.
- Send emails, unlike most disposable services.
- Supports 15+ languages.
- Runs on Go-Guerrilla, an open-source project that improves reliability and transparency.
2. Mailinator
Mailinator is designed to receive emails without requiring an account or registration. It is widely used for testing, verification, and avoiding spam when signing up for online services. It does not support sending emails or filling out forms.
Here is a screenshot of Mailinator showing a private team inbox with received messages, including subjects and timestamps. The left panel provides options for managing teams, message rules, and authentication.

Unlike traditional temp mail services, Mailinator offers both public and private inboxes, making it useful for developers, testers, and businesses that require temporary email solutions.
Mailinator
- Access public or private inboxes for flexibility.
- Create private domains for controlled email testing.
- Receive emails instantly for real-time testing.
- Integrate with applications using the Mailinator API.
- Auto-delete emails after a short period for security.
3. Temp Mail
Temp Mail lets you create temporary email addresses for quick use. It helps you avoid spam, protect your privacy, and receive emails without using your personal inbox. No registration is needed, just visit the site and get an instant email address for sign-ups, verifications, or any online activity.
Here is a screenshot of Temp Mail showing a temporary generated email id.

Emails received in Temp Mail are automatically deleted after some time, ensuring privacy. This service is useful for avoiding unwanted newsletters, spam, and phishing emails. It’s a quick and easy way to keep your inbox clean and stay anonymous online.
Temp Mail
- Create a temporary email instantly in seconds.
- Automatically delete emails after a short period.
- Block spam and junk emails from reaching your main inbox.
- Use the service without registration for quick access.
- Access on any device via web, mobile apps, and browser extensions.
- Stay private and secure with no personal data stored.
4. Tempmailo
Tempmailo provides users with temporary email addresses for receiving emails. It is designed to protect users’ privacy, prevent spam, and enable anonymous registration on websites that require email verification.
Below is a screenshot of TempMailo, the interface includes options to copy the email address, refresh the inbox, and change the temporary address.

Tempmailo Features
- Get an instant, ready-to-use temporary email.
- Store emails for 2 days with no long-term retention.
- Avoid spam and phishing with a throwaway email.
- Use it for free without registration.
- Access an upcoming API for email testing.
5. EmailOnDeck
EmailOnDeck is designed to provide disposable email addresses for online registrations, verifications, and privacy-focused interactions. It allows users to create an instant temporary email without requiring personal details, making it ideal for avoiding spam and protecting identity.
The screenshot below is from Email On Deck, showing a temporary email address and an inbox with a forwarded email from me. The interface includes options to refresh the inbox, delete messages, and send emails.

EmailOnDeck Features
- Generate a temporary email with one click; no registration is needed.
- Supports 10+ languages.
- Stay secure with a private, disposable email.
- Use Chrome and Firefox extensions for quick access.
- Use advanced features with the Pro version.
6. 10 Minute Mail
10 Minute Mail is a free, disposable email service that provides a temporary email address, valid for 10 minutes. It’s an ideal solution for quick sign-ups, protecting users from spam, phishing attacks, and unwanted promotional emails.
Here is a screenshot of 10 Minute Mail showing a temporary email address with a countdown timer showing its expiration in 9.20 minutes. The tool allows users to copy the email address, refresh the page, extend the time, or generate a new address.

The service ensures complete privacy by generating a unique, random email address that automatically expires. If needed, users can extend the duration or generate a new email instantly. It is useful for receiving verification emails without exposing personal email accounts to spam.
10 Minute Mail Features
- For privacy, emails are automatically expired after 10 minutes.
- Extend email lifespan up to 100 minutes when needed.
- Keep mailboxes private and inaccessible to others.
- Supports 40+ languages.
- Use a mobile-friendly design for easy access on any device.
- Rotate domains every 45 days to avoid website blocks.
7. YOPmail
YOPmail is a free disposable email service that provides instant, anonymous email addresses to protect your inbox from spam, phishing, and unwanted messages. Unlike traditional email services, YOPmail requires no registration, allowing users to generate a temporary inbox instantly for quick sign-ups and online activities.
Here is a screenshot of YOPmail showing an auto-generated anonymous email address. It provides instant access to received messages, helping users protect their personal email from spam and unwanted subscriptions.

YOPmail is a convenient solution for temporary communication, providing instant access to a disposable inbox without compromising security or privacy. Simply generate an email, use it, and forget it!
YOPmail
- Generate a temporary email instantly without registration.
- Store emails for up to 8 days before automatic deletion.
- Use alternate domains to bypass website blacklists.
- Reply to messages within the YOPmail system.
- Mask your inbox with an alias for added privacy.
8. MailTicking
MailTicking allows users to generate temporary email addresses instantly. It is designed for quick email verification, protecting privacy, and reducing spam in your primary inbox.
Here is a screenshot of MailTicking displaying a temporary email inbox. It automatically refreshes to display new emails, making it useful for quick registrations and avoiding spam.

With an auto-refreshing inbox, users can receive emails in real time without registration. It is ideal for signing up on websites, testing email functions, or accessing online services without exposing personal email addresses.
MailTicking Features
- Generate a random, disposable email address instantly without sign-up.
- Copy the generated email address with one click for quick use.
- Switch between multiple temporary email addresses anytime.
- Receive forwarded emails for testing and verification purposes.
- Use the service without registration, ensuring privacy.
9. AdGuard
AdGuard provides a secure, disposable email address that helps protect your privacy, prevent spam, and maintain online anonymity. With instant email generation and automatic inbox management, you can use a temporary email address for registrations, verifications, and testing without exposing your personal information.
The below screenshot shows the AdGuard Temp Mail service, which provides free temporary and disposable email addresses. The inbox showing received emails and includes options to refresh or change the email address.

Unlike traditional email services, AdGuard Temp Mail requires no sign-up, ensuring a hassle-free experience. This is useful for avoiding spam and protecting privacy when signing up for online services.
AdGuard Features
- Generate instant disposable emails to access temporary addresses quickly.
- Block spam and unwanted emails to keep your inbox clean.
- Hide your real email and IP address to stay private and avoid tracking.
- Automatically delete emails after seven days for better privacy.
- Test online services and apps with a developer-friendly setup.
10. Internxt
Internxt’s free temporary email service allows users to create disposable email addresses for anonymous and secure communication. This tool helps users avoid spam, protect their personal inboxes, and sign up for online services without sharing their real email.
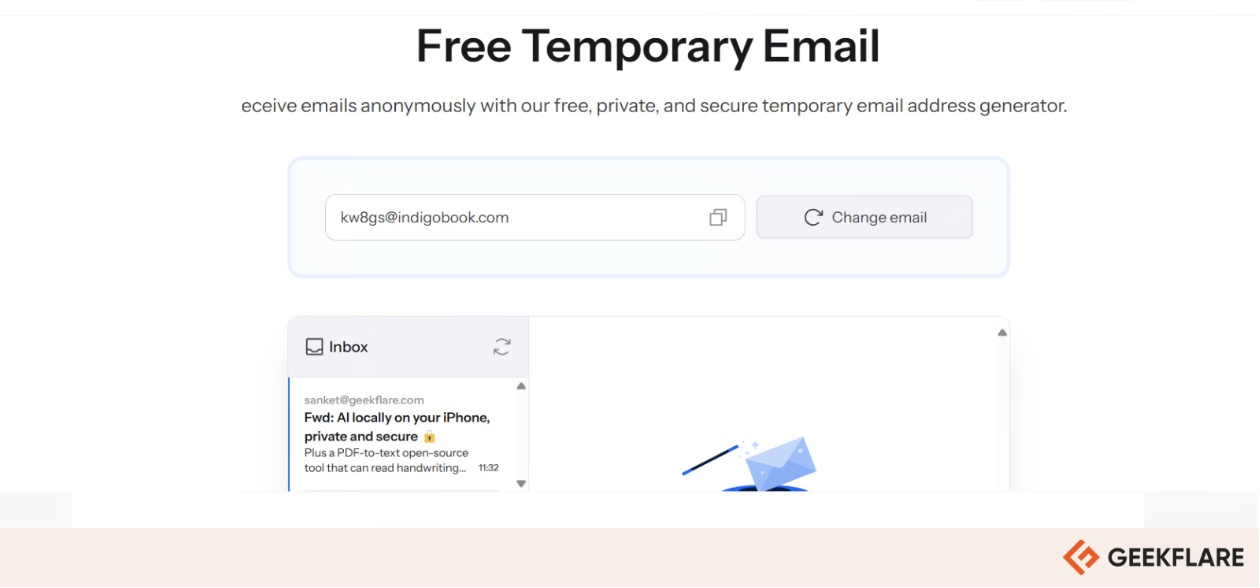
This screenshot shows Internxt’s Free Temporary Email Generator, which provides secure, disposable email addresses for anonymous use. It allows users to receive emails without revealing their personal addresses.
Unlike traditional email providers, Internxt does not store user data, ensuring complete privacy and security.
Internxt Features
- Use a random email address without revealing personal details.
- Avoid spam, ads, and phishing attempts with a clean inbox.
- Receive emails instantly for quick verification and sign-ups.
- Let emails expire automatically after three hours of inactivity.
- Stay private and anonymous with no data tracking or storage.
What Is a Temporary Email Address?
A temporary email address is a short-term, disposable email service that allows users to receive emails without revealing their primary email address. These emails are typically used for situations where privacy is a concern or when users want to avoid spam.
Here are some of the key benefits of a temporary email address:
- Spam Prevention: Helps users sign up for online services without receiving promotional emails.
- Privacy Protection: Prevents websites from collecting and selling personal email addresses.
- Quick Access: No registration required; users get an instant, disposable inbox.
But, there are some limitations, such as:
- Blocked by some websites that detect and reject disposable emails.
- No recovery option once the email expires, losing all messages.
- Not suitable for sensitive accounts like banking or legal services.
- Limited sending capabilities, as most temporary emails can only receive messages.
Beyond Temporary Email
While temporary email services are helpful for short-term needs, they are not ideal for long-term communication, security, or professional use. If you’re looking for a privacy-focused permanent email solution, consider using secure email providers like:
- Proton Mail: An encrypted email service that ensures end-to-end security and anonymity. Here is a detailed review of Proton Mail for you.
- StartMail: A private email provider offering PGP encryption and unlimited disposable email aliases.
Both options provide strong encryption, no ads, and protection against data tracking, making them excellent choices for users who value privacy and security in their everyday email communication.
Explore more on Email Management
-
 EditorRashmi Sharma is an editor at Geekflare. She is passionate about researching business resources and has an interest in data analysis.
EditorRashmi Sharma is an editor at Geekflare. She is passionate about researching business resources and has an interest in data analysis.



