Data has turned out to be the most crucial aspect of a business. Moreover, it plays a predominant role in personal life as well.
If you want to keep your data safe and secure against data loss, corruption, and theft, you must have a comprehensive data backup strategy in place for your organization.
This article will discuss the importance of data backup and what business users can do to develop a foolproof data backup policy. Fortunately, you can implement these approaches for personal data as well.
What Is Data Backup?
Data backup is a common term used in the domain of information technology. It means making a copy of the existing data and storing it somewhere else. The primary purpose of backing up data is to use it if the original data is inaccessible, lost, deleted, corrupted, or stolen.

You can have a duplicate copy of your data anywhere for backup purposes. You might want to store it in an external data storage device like an external HDD, SSD, and USB. Else, data backup on a cloud storage platform is another viable option.
The objective of the data backup is not to stop data loss but to restore the backup copy if it happens. Hence, it is the most critical step during any large-scale edit to a database, computer, or website.
What is the importance of Data Backup?
You can lose your precious data due to numerous reasons, and without backup data, data recovery will be expensive, time-taking, and at times, impossible. Following are some of the reasons why every company should back up its data.
Data Loss Prevention
One of the primary reasons behind data loss is accidental or intentional deletion, and a backup copy can save your back in such situations. Any employee may accidentally delete any crucial data without knowing its importance or requirement in the future.
Besides, some hostile employees might intentionally delete organizational data. You can prevent losing such data permanently by having data backup.
Protection Against Physical Disasters
Contrary to popular belief, you can lose your business-critical data due to different physical disasters such as fire, floods, earthquakes, or tornados. Such disasters can completely wipe out your data and make data recovery practically impossible.
Another less severe but more frequent example would be a system crash of your computer or someone stealing your hard drive or laptop with no data backup. You also need data backup to tackle these situations.
Answer to Hacking Attacks
Even with the most advanced protection against hacking, your business can become a victim of hacking and ransomware attacks. These prevalent outbreaks can cause heavy financial damage to your business if you do not have the data backed up somewhere else.
Companies also need to remember that old-school methods like viruses, malware, and spyware, are still the leading causes of data loss and theft. Even if you do not fall prey to ransomware, regular virus attacks can also cause you loss. You can be sure of data security only with data backup.
Useful for Audits and Archives
Business companies need to go through audits, and not having necessary documents and information at the end of the financial year will not look good. Regardless of your business country, you must backup your financial records to avoid issues with national regulatory commissions.
Data backup also serves archival purposes. If your business belongs to the financial sector, keeping a copy will come in handy if your clients lose the data from their end due to a virus attack or system crash.
Quickly Resume Operation
In any event of data loss, the ability to recover quickly and resume operations is crucial to an organization’s success. If your clients are made to wait for several hours while you rebuild the database from scratch, they might turn away from your business and opt for your competitors. If you have a data backup and a smooth data recovery policy, it will take less time to get back on track.
It also makes sense to back up the data in a different location, probably in another state or country, your company could start functioning immediately.
A disaster recovery plan is essential, especially if you live in a natural disaster-prone area. A plan for IT disaster recovery is critical for your business.
Once you have a data backup strategy for your business, you can have a good night’s sleep without having to worry about the security of customer and organizational data. Whether there is a system crash, natural disaster, or cyberattack—nothing can stop you when you have backup data.
As you are familiar with the importance of data backup, it is time to learn data backup best practices. In this time of cyberthreat, random data backup is not enough. You must have a solid and consistent data backup policy. The following are the best practices.
Regular and Frequent Data Backup
When it comes to data backup, the rule of thumb is to perform it regularly, without having lengthy intervals between the instances. The standard practice is to perform a data backup daily, or if not possible, at least once a week.
Businesses that involve mission-critical data should back up such data in real-time. For that, you can use tools that will automatically backup your data on a regular frequency. Else, you can also perform backups manually if you own a small or medium business.
Use Multiple Methods

As a business organization, it is not wise to rely on a single data backup method. Instead, follow the popular 3-2-1 rule. It means making 3 copies of data and storing the backup copies on 2 different devices/platforms, one of which should be offsite storage.
If there is any budget constrain, companies should consider backups on an external drive and a cloud platform.
Prioritize Offsite Storage
Even if you do not follow the 3-2-1 method and backup data in a single site, make sure to go for offsite storage. It can be a physical server located somewhere away from your office or any cloud-based platform.
This will offer you a great advantage if your central server gets compromised in any way. For example, a natural disaster can be devastating for your on-site server, but an offsite backup will stay safe.
Consider Endpoints

If your focus is solely on your database for backup, it will be a mistake. You have to consider the endpoints such as desktops, laptops, tablets, and phones your employees and colleagues use to perform their duties.
If you do not back up the data of these devices, you might lose them forever in case the devices get lost or stolen. Hence, you should include individual device backup in your data backup policy.
Encrypt Backup Data
Apart from the data backup platform, you must be careful about data encryption. Keeping the backup data in an encrypted format will ensure an added layer of security. Encrypted backup copies will stay protected against data theft and corruption.
Moreover, there will be no issue when the business needs to recover it. Your IT admin or data backup service providers can confirm if your backup data is getting encrypted or not.
Perform Regular Tests
Backing up your data does not mean the end of your responsibility. Whenever you get an opportunity, perform test backup and recovery. It will help you become aware of the shortcomings in your policy and methods.
By discovering the errors, you can make necessary corrections that will benefit you in the long run. Usually, organizations perform these tests annually or bi-annually. However, companies dealing with constantly changing data should perform the test more often.
Decide on the Retention Span
Since there is always a fixed amount of storage space, an organization can’t save every backup forever. Usually, backup solution providers offer different retention schedules for various types of backup up data.
You must perform thorough research about the standards and requirements of data retention in your industry. However, data backup best practices include keeping monthly and bi-annual backups as long as possible.
Learn About the Popular Data Backup Tools
Manually backing up business data can be time-consuming and hectic. Also, regular cloud-based data storage is not the safest option for crucial and sensitive data backup. Therefore, dedicated data backup tools are getting popular among business organizations.
#1. Acronis
Whether it comes to backing up your valuable files or expensive tools, Acronis Cyber Protect Home Office is the right solution. It creates a mirror image of selected files and folders or your complete system that you can restore in a flash when needed.
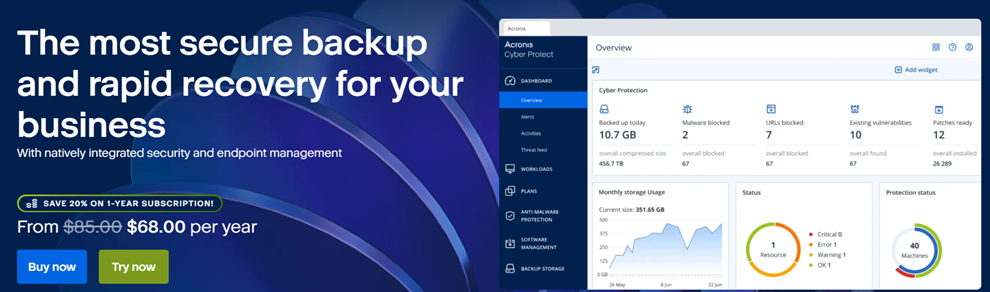
The anti-ransomware feature of this utility can detect and reverse the unauthorized encryption of an HDD. As a result, your business data stays safe from growing ransomware attacks.
Acronis also comes with features such as quick backup validation, incremental and differential backup, file synchronization, active disk cloning, resumable backup, version control, memory card and mobile backup, web filter, and real-time protection. All these make it a dependable and powerful choice of business data backup.
#2. EaseUS
EaseUS Todo Backup protects your data with disk imaging technology. It offers solutions for organizations of all sizes and environments. Once you schedule backup at your preferred time, the software will run automatically and make backup copies.

Users can also choose from full, scheduled, incremental, and differential backups to cover every bit of data. Its real-time backup report provides you with the latest update on every backup stage and alerts you if anything unexpected happens.
#3. Uranium Backup
Uranium Backup is powerful and versatile backup software. The Free version offers the ability to perform full, incremental, or differential backups of files and folders. Among the free features offered, there is the Zip64 compression of files which allows you to encrypt data archived. In addition, the backup scheduler allows users to plan the execution of every single backup set.

The software has a user-friendly interface and to start using the free version just need to visit the dedicated page and simply click on Download without any registration or credit card required.
#4. Genie9
Genie9 offers cost-effective backup solutions for home users and organizations. Using its Timeline view, users can recover their data from any point in time. Also, it shows the backup health through protection level.
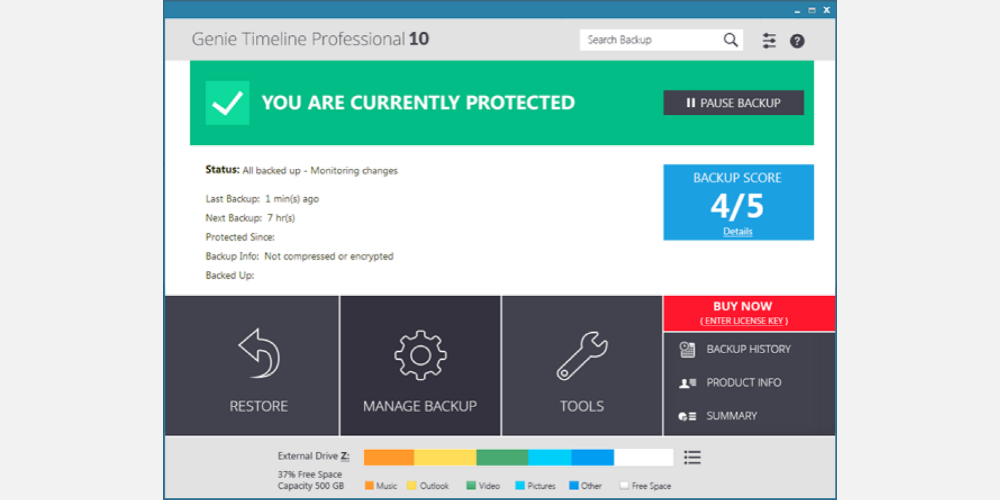
As a user, you can use Turbo mode to backup data at high speed or use Smart Mode to adjust the speed depending on available system resources. By enabling Game/Movie mode, users can hide annoying pop-ups automatically and ensure interruption-free gaming or viewing experience.
#5. Backblaze
Backblaze offers seamless and secure data backup in the cloud. It supports automatic backup of all files, including documents, images, audio files, and videos. At the same time, there is no restriction in terms of file size or file count on this platform.
It encrypts your file in transit and in storage to ensure maximum security. However, users can opt for additional protection by using a private encryption key for backup restoration.
What’s more, Backblaze comes with intelligent throttle and threading technology that makes data backup blazing fast. The backup data gets stored in its dedicated data centers with biometric security, 24/7 staff, and power backup.
#6. R-Drive
R-Drive Image is a robust disaster recovery solution that protects your business from fatal data loss after a system failure, hardware crash, and virus attack. It creates disk image files for backup purposes and lets you restore backup data quickly and completely to your system.
You can use it to backup only selected items instead of all disk objects. Using its advanced file filter feature, users can easily find and mark files. The user interface of this utility is available in all major languages, including English, French, German, Japanese, and Spanish.
Final Thoughts 👩🏫
The digital world is going through a constant transformation. Hackers are adapting to new techniques to get hold of your data. For these reasons, companies must perform data backup best practices to reduce data loss threats and increase data recovery chances.
Now that you have learned the need for having your data backed up and different data backup techniques, you can choose the one according to your business requirements.
If your business is medium or enterprise-level, you can consider the best data backup solution for it.


