Development Operations (often shortened for DevOps) entails combining cultural practices, philosophies, and tools that increase the capability of an organization to deliver software apps and services faster.
Unlike organizations that use traditional infrastructure management and software development practices, it involves evolving and improving products more quickly. Because of its operational efficiency, many organizations are adopting DevOps techniques to streamline their workflow and achieve better results.
As of this writing, DevOps is proliferating due to modern software’s changing demands and complexity as it evolves across many fronts.
As a developer, I have seen an ever-growing interest in DevOps. In this post, I’ll focus on the top trending DevOps areas backed with some statistics. While I haven’t ranked them in any particular order, reading through them will give you some insights into what rooms you can explore and stay ahead in the technology space; it steadily moves fast. I’ll also include some DevOps tools gaining traction as well.
DevSecOps
Today, security is one of the significant areas of concern in the digital era that you can’t shed off. However, the traditional software delivery approach makes security an after-sought commodity. DevOps is a game changer and has helped software engineers release code 60% faster. But with speed, there’s an introduction of insecurities, and that’s where DevSecOps comes into aid.
Many enterprises have integrated DevSecOps into their software lifecycle. It means that right from the conceptualization of the software, security is prioritized, eradicating all the chances for vulnerability. More benefits include streamlined software governance and observability.
According to a report by Infosec, 96% of the respondents claimed that DevSecOps has been advantageous to their firms. DevSecOps is all about a blend (collaboration) of development, operations, and security concerns by IT teams when automating processes and enacting speedy deployments.
Serverless Computing
Serverless computing refers to developing and running services or applications without a server. Right from the development stage, the apps are tactically designed to run without managing servers.
The last few decades have ramped up the adoption of this operation model based on benefits like facilitating the migration of computing infrastructure to the cloud, streamlining and optimizing the development processes.
A report by Global Market Insights shows that the serverless market exceeded $9 billion in 2022 and is set to expand by a 25% compound annual growth rate (CAGR) between 2023 and 2032.
Microservice Architecture
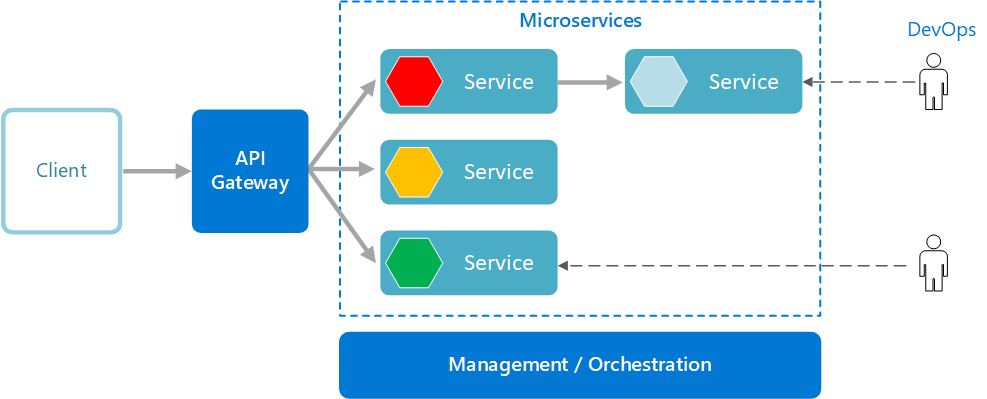
You’ll often find it referred to as microservice. In this case, DevOps entails breaking large-sized applications into small manageable pieces that fit together (a bundle of loosely coupled services). This criterion decreases complexity, expands scalability, and eases the development process.
Besides that, microservices simplify software development, testing, and deployment leading to fast application delivery without sacrificing product quality.
A research report by IBM indicates that microservice architecture is currently applied in many fields, including data analytics, database applications, customer relationship management, customer services, finance, and HR applications.
The core benefits highlighted are self-sufficiency, easy implementation of changes, simplified onboarding, broad scope for technical variety, and continuous delivery. The report shows that 30% of the key benefit of this approach is customer retention.
AIOPs/MLOPs
Artificial Intelligence for IT Operations (AIOps) uses AI capabilities like natural language processing to automate and streamline workflows.
Machine learning operations (MLOps) entail streamlining the process of using machine learning models under production while monitoring them. With AIOps, it is easy to identify problems hindering operational productivity. MLOps plays the role of enhancing productivity.
Webinarcare published their research stating that AIOps usage should rise from 5% to 30% by the end of this year based on its impact on improving data-driven collaboration.
Low Code Applications
As you can presume, from the name, low-code applications are a new DevOps approach to building software. In this case, complete applications are created with small code efforts. Many developers and organizations are adopting this approach as it facilitates easy and fast development.
This approach sets many organizations in the competition for fast-paced software. That aside, it allows non-technical staff to participate in product development through an interface that handles the whole process. Low-code applications are one of the DevOps future trends aimed at speeding up development and deployment through simple, user-friendly applications.
At the time of writing, many tools are used to automate application deployment through a readily available interface that helps with other DevOps processes like version control, build validation, and quality assurance.
Colorwhistle’s statistics depict that low-code applications are imperative and reduce development time by 90%. They further predict that 70% of oncoming business applications will rely on low code as of 2025.
GitOps

GitOps is a relatively new trend in the DevOps workflow. It is a new approach to software development and deployment combining the Git version control with container orchestration technologies like Kubernetes.
The main focus is monitoring, controlling, and automating infrastructure through a Git-encompassed workflow. Based on its capabilities, developers and IT operations managers use Git to collect and deploy applications.
GitOps combines the best DevOps practices like version control AI, compliance, collaboration, and the CI/CD applying them to the automation infrastructure. And to pile on these benefits, GitOps encourages increased releases, continuous delivery on creation, testing, and seamless deployments with high efficiency.
Humanitec’s statistical analysis report showcases the benefits of the GitOps approach to software development, providing developers more control over YAML files while offering freedom for application configuration.
Expect increased traction on GitOps following the ability to minimize human errors when working with YAML files. Statista’s report features GitOps in the leading 40% of DevOps techniques.
Kubernetes
Kubernetes, often called K8s, is an open-source container orchestration platform – the tool automates the deployment, scaling, and management of containerized applications.
K8s avails of a continuous and autonomous container-based environment for integration where developers can scale (either up or down) application resources. This is why K8s has hit the top list for DevOps this year.
According to a survey by Dynatrace, K8s has become a key platform where you can move workloads to the cloud. And that being the case, there’s been an annual growth rate of 127%, where the number of Kubernetes clusters grew five times that of on-premise hosted clusters.
The survey also highlights strongly growing areas in K8s technology: security, databases, and the CI/CD domains. Don’t be surprised to hear K8s being called the operating system of the cloud.
Infrastructure as Code

Infrastructure as Code (IaC) in DevOps is about managing and provisioning infrastructure through configuration files instead of manual processes. The configuration files define and arrange computing resources like storage, networks, and virtual machines. This technology allows organizations to provide and run infrastructure by improving accuracy and consistency.
Infrastructure management has moved from data centers’ physical hardware and taken new forms through virtualization, containerization, and cloud computing. The key benefits are cost reduction, increased deployment speeds, minimalization of errors, improved infrastructure consistency, and reduced configuration drift.
GlobeNewswire’s report states that the infrastructure as code (IaC) market space experiences a 24% compound annual growth rate (CAGR). The key aspects driving this space are the eradication of annual methods and the liberty that comes with automation for DevOps teams.
Site Reliability Engineering (SRE)
SRE in DevOps is a software engineering and operations collaboration to build high-quality software products and services. At its core, the main focus is to create, measure and operate resilient systems designed to handle high traffic while giving the best user experience.
Simply put, SRE is all about using software engineering as the pivot to automate IT operations like incident and emergency response, product system management, and change management (all of which would’ve been done manually by system administrators).
A survey by Sumo Logic indicates ever-growing traction on the dependence on SRE to bring forth reliable and digital products through harnessing cloud-native tools and their new processes.
The survey highlights that 62% of organizations are using SRE, 19% through the entire IT process, 55% are using it with specific IT teams, 23% are piloting SRE, and the remaining 2% on others, while 1% claim that SRE didn’t work for them.
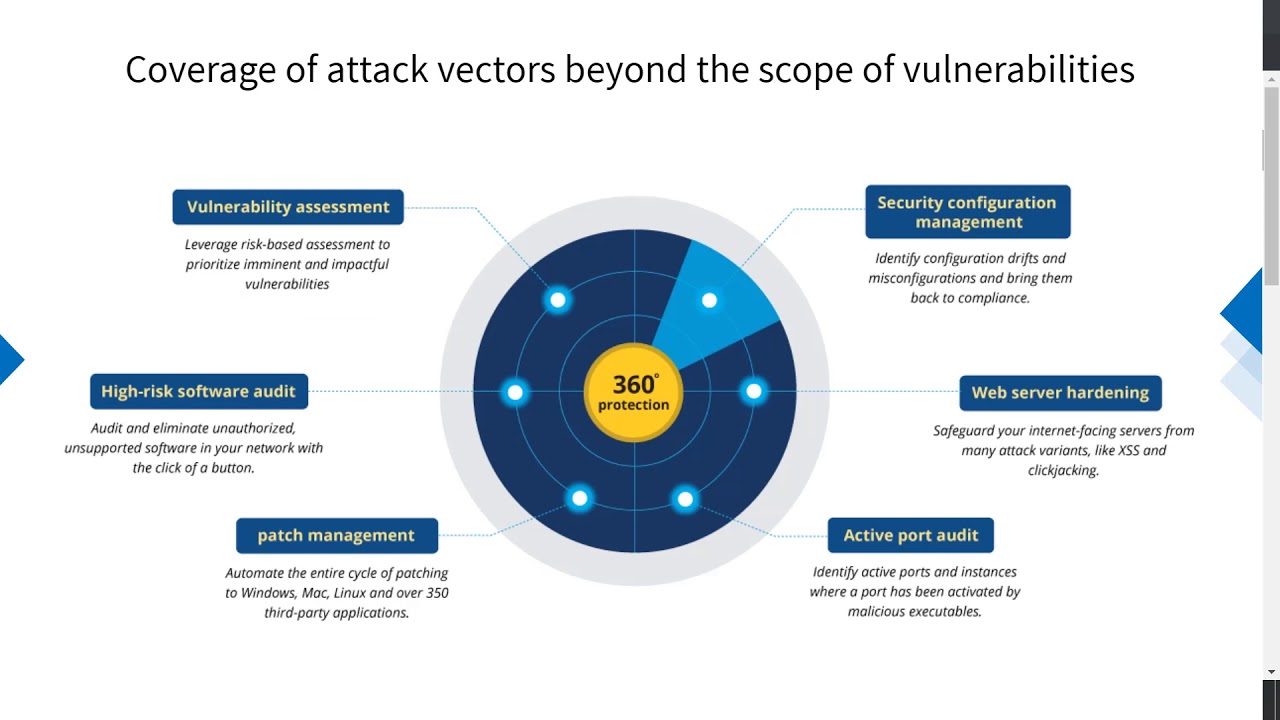
Vulnerability Management
If you’re a security enthusiast, this is your field. It entails managing and mitigating security vulnerabilities. This tech aims to spot, categorize and mitigate potential security threats before attackers exploit them.
So, it is a continuous, proactive, and automated process to keep your networks, computer systems, and applications from data breaches and cyber-attacks. The process involves discovering assets and nailing an inventory, enacting vulnerability scans, managing patches (keeping systems updated with the latest security patches), security incident and event management (SIEM), penetration testing, threat intelligence, and remediation of vulnerabilities.
Astra’s report on vulnerabilities highlights that logging libraries for applications can endanger devices, and lack of input validation (like in Chrome browser-based applications) puts over 3 billion devices at risk. The report also advises on software updates to reduce vulnerabilities by at least half.
Platform Engineering
Platform engineering is a crucial arm in the DevOps space. It involves building and operating applications in cloud-native platforms. Platform engineering is about quickly building, deploying, and troubleshooting software while leveraging the latest technology innovations.
At its core, it’s a discipline that designs and builds workflows and toolchains that prompt self-service capabilities in a cloud-native era for software engineering organizations. Platform engineers avail integrated products, Internal Developer Platform (IDP), that covers all operation requirements for an entire application life cycle.
Humanitec’s blog post shows that platform engineering growth is quite shocking, with the Platform Engineering Slack community growing from a thousand to 8k practitioners in 2022.
The post also predicts that you’d expect more case studies to emerge in the domain, unique approaches to how platforms as products address unique developer needs, and a rise in DevOps and platform engineering roles.
Hybrid Deployment
DevOps combines on-premises and cloud-based resources in a hybrid deployment to enact agile and flexible software development and deployment. This technology aids organizations in scaling the cloud’s ability and saving costs while providing effective control over the application and its data.
This approach allows organizations that have already invested in on-premise infrastructure to augment them and create alternative paths to AWS (as an example) or Microsoft Azure instead of a full migration of their services.
The key benefits of this model include reduced costs, better support for remote workforces, improved scalability and control, innovation agility, business continuity, and improved security risk management.
Statista’s report on hybrid cloud states that 72% of enterprises have deployed hybrid cloud for their organizations. And with the help of hybrid deployments, there’s an expanded focus on cloud strategies, security, and improved data management.
Data Observability
Data observability is gaining traction in DevOps because its techniques can provide a profound understanding and analysis of application performance, thus driving reliability, availability, and scalability.
It’s a criterion for DevOps teams to acquire comprehensive insights into an application, identify problems and influence their decision-making. Through data observability, organizations can use tools to automate monitoring, perform root cause analysis, track data lineage, and acquire data health insights. These insights make it easy to detect, resolve and safeguard apps from data anomalies.
According to CDInsights, 90% of IT experts believe that data observability is crucial at every stage of the software development life cycle (SDLC), with the most concerned areas as planning and operational stages.
In modern business, observability cascades plenty of benefits like improved collaboration and productivity while saving on costs by up to 90%, among others.
Docker
Docker is a software platform where you can build, test and deploy applications seamlessly. You can use Docker to package your software into standard units called containers. Containers house all your software requirements needed to run it, including libraries, code, system tools, and runtime.
Dockers guarantee an easy deployment that scales your application on any environment while your code runs. In simple words, Docker simplifies your development and workflow by allowing you to innovate with the choice of tools for your application stack with deployment environments for each project.
Based on DMR’s report, Docker has onboarded over 4 million developers with over 1000 commercial customers. The docker hub has over 5.8 million dockerized applications plus 100k apps using it as a third party.
Ansible
Ansible, primarily targeted at IT professionals, is a powerful automation software for application deployment, updating workstations and servers, configuration management, and performing all system administrator tasks.
While it’s useful for automation, system administration, and popular DevOps procedures, you can configure a computer network without in-depth programming skills. Ansible plays a key role in version control, infrastructure as code (IaC), and all other executable operations paramount to running and organization.
Daffodil’s report on infrastructure as code (IaC) tools show that Ansible is the world’s number two preferred configuration tool after Terraform. The tool is popular for configuration, cloud provisioning, and intra-service orchestration automation.
Terraform
Terraform, as infrastructure as code (IaC), allows you to define both on-premise and cloud resources in version-able, reusable, and sharable human-readable configuration files.
The platform allows you to have a consistent workflow that you can use to manage your infrastructure throughout its entire life cycle. With Terraform, you can manage high-level components like SaaS features and DNS entries, as well as low-level ones like computation, storage, and network resources.
Statista’s report on DevOps tools depicts that Terraform takes 35% after AWS cloud formation templates which lead by 47%. It’s preferred by the DevOps team for its high security in building, changing, and version infrastructure.
Final Words
DevOps is an interesting field in the software engineering space. As you have seen, there are multiple domains for you to choose from. Whether you’re an expert in the area or just an enthusiast looking to start your career, the DevOps space has a chance for you.
If you want to reinforce your knowledge in the area, I recommend equipping yourself with great resources. The more you acquire profound knowledge, the closer you reach your dream career.
If, on the other hand, you’re an organization’s decision maker, you’ve learned about the technology trends that you’d opt to adapt as the DevOps evolves across many fronts. If there’s a good place to start learning DevOps, it’s our list of the best DevOps courses you can take.