Want to be an expert in identifying scam crypto tokens? If yes, check out these simple methods mentioned in this article to safeguard yourself from scammers.
Wherever there’s enormous demand and money inflow, there exists the possibility for scams. With over $1 trillion market capitalization, the crypto sector has had a huge involvement of scammers in recent years.
According to Chainalysis, 2022 witnessed the biggest-ever crypto hacking since the inception of cryptocurrencies. Furthermore, the hackers stole a whopping $3.8 billion from various platforms.
As an informed investor, it is essential to understand and spot scams around the crypto space. As a result, you can avoid falling into a scammer’s trap and create awareness among the people you know.
First, let’s understand what crypto scams are, but if you already know and want to dive right into the tools that help identify them, check the table below! However, don’t forget to read the post that follows to learn how you can identify a scam crypto token/coin yourself!
| Tool | Notable Features |
|---|---|
| Token Sniffer | Real-time monitoring for security threats on tokens |
| Honeypot.is | Identifies potential honeypot scam tokens |
| CoinMarketCap | Real-time token data, community activities, exchanges |
| Etherscan | Detects sell-offs, founder activities, reputation |
What is a Crypto Scam?
So, what are crypto scams? Basically, a crypto scam involves fraudulent activities or schemes to generate financial benefits. Also, in most cases, the victims of such scams lose their valuable crypto assets to scammers.

The increase in popularity of crypto projects and their tokens attracts millions of new users to this space. For this reason, fraudsters find it easy to trap beginners with less knowledge about the crypto space. Thus, it pays to know the best crypto platforms and use safe crypto wallets.
Also, there are a variety of ways scammers try to trap the unsuspecting, from crypto faucets, to even fake crypto apps! The key is to be vigilant!
Notably, fake or scam crypto tokens are among the most commonly used methods to misguide beginners and run away with their money. Here, the fraudsters convince users to invest by guaranteeing enormous returns.
But how do they pull out such scams? Let’s dive into it now.
How do Scam Tokens Work?
The main motive of the scammers is to convince users to buy a large number of scam tokens. To do so, the major tactics used include the rug pull method.
So, what’s a rug pull? Let’s understand that right away!

Rug pull is a crypto scam where the developers or team drops the projects and runs away with investors’ funds. Finally, after this process, investors are left with invaluable crypto tokens☹️.
The scammers initially pump the token price to create fear of missing out (FOMO) among investors. Therefore, the token price surges massively in a few hours.
Finally, once that token reaches a particular price, the developers sell out all their tokens. As a result, the price of the token crashes to almost zero, losing the money of all other investors in a few seconds.
One of the most prominent examples of rug pull was the Squid Game (SQUID) token in 2021. This crypto token inspired by a popular Netflix series crashed after the developers ran off with the user’s investments.
⚠️Overall, this rug pull wiped out $3.3 million of the user’s fund!
All things considered, it is important to recognize such scam crypto tokens and stay away from them.
How to Identify a Scam Token?
You can follow these methods to spot scam tokens from the crypto space:
#1. Research About the Project
The actual value of a crypto token lies in the future potential of the crypto project. Therefore, research the mission and goal put forward by the developers.

Moreover, check the use case of the token that the project issues. Genuine projects come with practical and clear use cases. If you find cryptos that offer logicless missions, avoiding such tokens is the better option.
Furthermore, check the details about the major investors of a project. If an established investor or investment firm is a major investor, it’s less likely to be a scam.
#2. Check the Team and their History
The core team is the central pillar of any crypto project that succeeds in the future. Most of the crypto crimes are conducted by anonymous founders and team members.
Ensure that the team members have work experience in the crypto sector. Moreover, check their active profiles on LinkedIn, X, or Discord platforms.
Suppose you’re a beginner in the crypto space. In that case, I recommend not being involved with projects that don’t provide information about their founders and team. However, note that this factor alone doesn’t guarantee the credibility of a project.
#3. Read the Whitepaper
The whitepaper provides in-depth details about a particular crypto project. You can read the whitepaper from the project’s website or platforms like CoinMarketCap or CoinGecko.

A typical whitepaper covers a project’s goal, timelines, and other important aspects. You can have a basic check on the whitepaper without having any technical expertise. Projects without a whitepaper can be considered as a red flag.
Other signs of the fishy whitepaper include:
- Grammatical errors
- Spelling mistakes
- Plagiarism
- Unprofessional design and layout
- Overuse of jargons
Creating a well-crafted whitepaper takes time, effort, and technical expertise. Therefore, you can easily find flaws in a fake project’s whitepaper.
#4. Check Exchange Listings
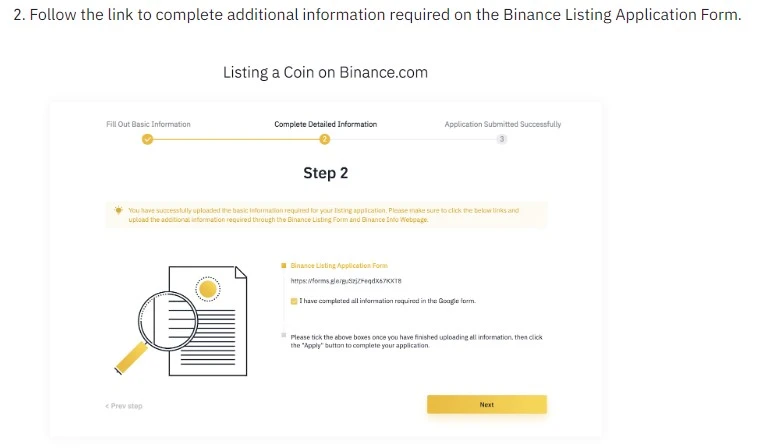
Most prominent exchanges undergo strict inspection before listing a new token. For example, to list a new token in Binance, the project’s founder or CEO must fill out a detailed form.
Once this form is submitted, a team of experts thoroughly reviews the project. Finally, after all conditions are met, Binance lists the token. This verification process itself eliminated a large number of scam crypto tokens.
With this in mind, you can check if a new token is listed on prominent exchanges such as Binance, Coinbase Exchange, and Kraken, to name a few. Overall, it’s better for a beginner to choose tokens listed on all the top 5 centralized crypto exchanges(CEXs).
#5. Check Token Liquidity
Simply put, token liquidity refers to the ease of conversion of crypto to another token or cash without impacting the market price. Suppose you sell a substantial number of a token; the overall price shouldn’t drop significantly.
You can check for a token’s liquidity on Uniswap or other decentralized exchanges (DEXs). This data will give you an exact idea of the liquidity of a crypto token.
Let’s consider the Ape In token as an example. If you try to buy this token, it’ll show “Insufficient liquidity.” It’s always better to stay away from such illiquid tokens.
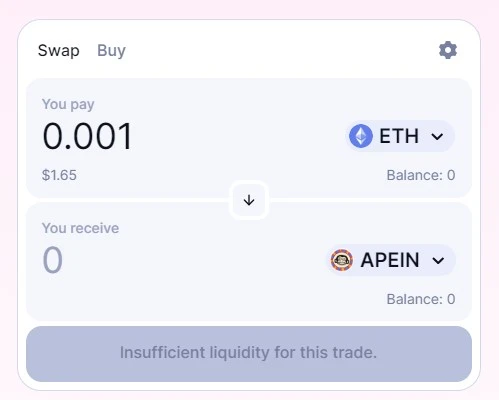
Illiquid cryptos are difficult to sell when a need arises. As a result, even if you place a sell order, the order stays unexecuted.
#6. Look into Social Media Activities
Social media platforms are the primary tool used to promote scam crypto tokens. Examine the marketing strategies that they offer.
Most scam projects focus on monetary aspects rather than technology and vision. For example, their pages highlight huge fundraisings and potential growth.
You can also check if they have verified accounts on major social media platforms. Most rug pull scammers don’t spend much time, money, and effort verifying their online accounts.

In addition, accounts with a large number of fake followers are also a sign of scam tokens. The best way to identify the genuineness of followers is to check the engagement for their latest posts. For example, an account with a million followers and few engagements can be considered a red flag.
Freebies are other major marketing tricks scammers implement to attract new users. Therefore, it’s better to avoid a project offering lots of free rewards, gift cards, or tokens.
#7. Consider Crypto’s Price and Trading Volume
If you observe the price patterns of a scam crypto token, there will be massive spikes. Moreover, you can also find irregular trading volumes at certain times.
You can easily spot these massive spikes in price and volume using simple charting platforms. For instance, you can search the token chart at TradingView to get historical price and volume movements.
For example, the price of Squid Game (SQUID) token surged from 1 cent to over $2,800 in a few days. Finally, this scam token’s price crashed to almost zero in a few seconds.

In short, avoid tokens that show sudden and extreme price and volume movements.
#8. Check Tokenomics
Tokenomics is basically the economics of a crypto token. As a result, you can understand the key components such as token supply, utility, distribution, and more.
If the founder and the team members hold the majority of the token supply, there exists a huge risk. Suppose they sell all their holdings; the token’s price will crash to zero.
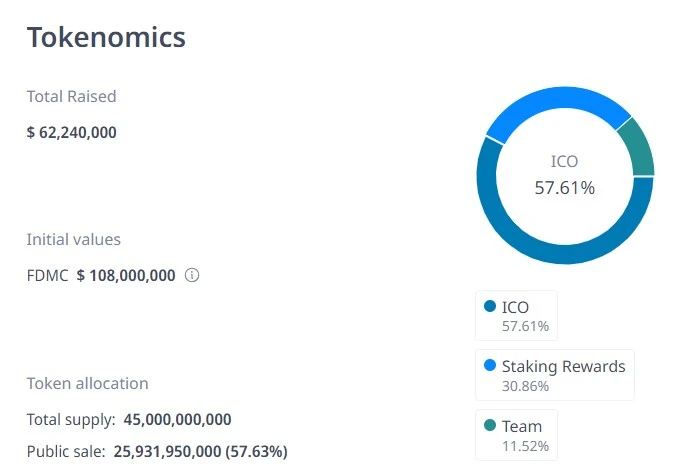
You can quickly check the simple tokenomics of a crypto token using platforms like CoinGecko or CoinMarketCap. Moreover, if you want to look at the detailed tokenomics, you can explore the whitepaper.
Tools to Identify Scam Tokens
Furthermore, you can also use some tools to find out scam crypto tokens. Stay tuned!
#1. Token Sniffer
Token Sniffer allows you to monitor the real-time activities of crypto tokens. This active monitoring helps to detect potential security threats around the selected token.

In addition, you can have a detailed inspection of the smart contracts of an underlying blockchain. At the time of writing, Token Sniffer supports 13 prominent blockchain networks.
The major data consists of:
- Holder Analysis: Details about all holders and their holding percentages.
- Liquidity Analysis: Includes the token liquidity in major crypto exchanges.
- Contract Analysis: Provides the verification details of the token’s contract source.
- Swap Analysis: Mentions if the token is sellable or not at marketplaces.
Token Sniffer is easy to use, as you can check the details about a token by entering its name or contract address. After a few seconds, you’ll get all the important information about that token.
#2. Honeypot.is
Honeypot.is helps you to identify potential tokens that function as a honeypot scam. Simply put, this scam involves scammers reaching out to people to provide their crypto wallet access in exchange for rewards. Thus, just having a secure crypto wallet isn’t enough!

Honeypot.is provides information on the following:
- Illiquidity in major exchanges such as Uniswap and SushiSwap.
- Source code of the token.
- Buy and sell limits.
You can use Honeypot.is to check if a token address is a honeypot🍯 or not. Here, you simply need to paste the contract address. Moreover, this tool helps you to detect scam possibilities of Ethereum and Binance Smart Chain (BSC) networks.
#3. CoinMarketCap
Acquired by Binance in 2020, CoinMarketCap is one of the trusted names in the crypto space. It is a must-have platform that helps you to research projects and cryptocurrencies.
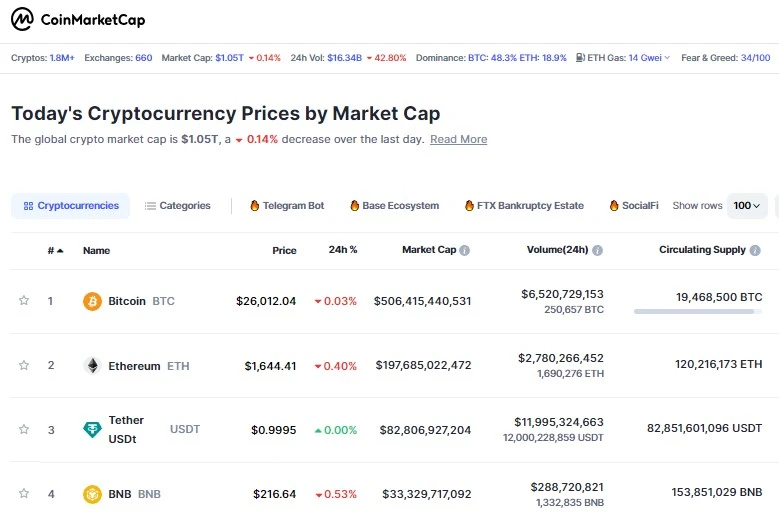
This platform provides real-time data about a token’s price, market cap, and trading volume. Moreover, you can also check the total, maximum, and circulating supply of tokens.
In addition, you can also check the activities of the community to spot any suspicious activities around the project. Also, you can find the token’s contract address, website, whitepaper, audit report, and more.
CoinMarketCap also provides the names of exchanges that list a particular token. This list includes the trading volume and liquidity score of the token.
#4. Etherscan
Powered by Ethereum, Etherscan is a reliable blockchain explorer. You can use this tool to check in-depth information about a token.
You can use this tool to detect large sell-offs in a cryptocurrency. Moreover, you can also spot the founder’s activities related to that token’s project. This data helps you to spot potential scams like rug pulls.
In addition, you can go through the comment section to check the possibilities for scams. Also, Etherscan helps you to identify the wallet where the hackers send the stolen assets.
Most importantly, this tool has a reputation option to inform the users of the credibility of a token. The type of reputation include:
- Unknown
- Neutral
- OK
- Suspicious
- Unsafe
- Spam
Unknown and neutral reputation tokens qualify for some credible requirements and don’t have significant red flags. In contrast, OK reputation satisfies most of the factors of a genuine token. However, it doesn’t provide a 100% guarantee to trust that token unquestioningly.
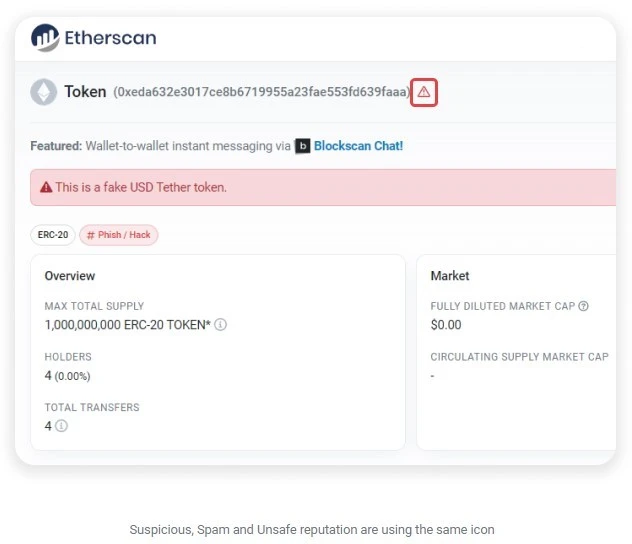
Tokens with suspicious, unsafe, and spam reputations come with reports of fraud, scam, spam, or phishing. It would be best to avoid tokens that fall under this reputation.
Final Words
There is no single factor that helps you to find a scam crypto token. However, you can combine all the methods discussed in this article to identify scam projects and their tokens.
In conclusion, avoid projects that sound too good to be true. Ultimately, don’t let the fear of missing out (FOMO) ruin your mental and financial peace.
Next up, the best Crypto lending platforms with tips on how to choose the right cryptocurrency lending platform.


