Hate someone stealing your WiFi? Let’s check how to use MAC address filters to put an end to this digital theft.
Emily found a few boys in their teens sitting just outside her apartment with their eyes glued to their smartphones.
Screens, she said to herself, rolled her eyes, and moved on.
The following day, she noticed a significant drop in internet speeds. Being a remote worker, this was particularly annoying since she was used to the blazing-fast 1 Gbps broadband.
This continued for a few days, and she avoided escalating to the ISP, expecting things to go back to normal on their own.
However, she noticed the repeated presence of those boys with their cellphones within a few meters of her apartment. Finally, she confronted a few of them and asked what this was about.
“The WiFi technician gave us the ‘connections’ for $10 a month”, one of them replied.
“Good for you”, responded Emily and returned to her computer table. She immediately opened the router console to see a few strange devices enjoying free internet.
Instead of reporting this to her provider, she used Mac address filtering as a fightback.
While Emily just sacrificed some data, WiFi stealing can have serious consequences. For instance, someone can use your WiFi to commit grave internet crimes, only to push law enforcement to knock on your door for an explanation and much more.
What Is a Mac Address?
A Media Access Control (MAC) address or a physical address is a 12-digit hexadecimal number designating each device on a local network. This puts an additional safety net other than a typical WiFi password.
MAC addresses are tied to the hardware and are very tough to spoof for the average internet user. In addition, it’s hassle-free to implement if you don’t bring in new devices every other day.
So, you can simply enter the MAC addresses of your devices and be assured that your WiFi bandwidth won’t be eaten up by others, even if they figured out the passwords somehow.
Notably, it’s different from IP addresses which are primarily used for global identification, can be shared among devices, and be changed with network configurations.
On the contrary, MAC addresses are permanent and remain fixed for a network.
How Does Mac Addresses Work?
Put simply, as a WiFi owner; you can search for MAC addresses for your devices and enter them in the MAC filtering section of your router console.
Once configured, the router blocks internet access for other devices.
So, there will be two steps in this process: finding MAC addresses and configuring the router.
Finding MAC Address
You need to have this information for each one of your devices.
And based on the device, there are different ways to find the MAC address. Besides, it also depends on your OS version, and the exact steps may differ.
However, these mentioned steps will be helpful.
Windows
You can either use the command prompt or the control panel to find the MAC address.
First, you can open the command prompt and type ipconfig/all.
This command will list all the connections, active or otherwise, with MAC addresses associated with each.
Alternatively, one can enter Control Panel>All Control Panel Items>Network and Sharing Center.
Subsequently, click the active connection and enter into the Details tab in the pop-up.
Finally, the relevant MAC address will be listed beside the Physical Address.
Mac
Enter the Apple menu and click System Preferences.
Next, enter into Network, select the connection, and click Advanced. Here, the MAC address will be listed under the Hardware tab.
Android
There are two ways to find the MAC address on any Android phone.
#1. WiFi MAC
Enter Settings and tap Network & internet. Next, tap the connection name and the gear icon beside it to configure specific connection settings.
The MAC address will be listed under the Advanced section.
#2. Device MAC
Navigate to Settings>About phone>Status information>Phone WiFi MAC address. These steps work for Samsung smartphones.
For stock Android phones, this is listed in Settings>About phone> WiFi MAC address.
So ultimately, it depends on the phone at hand. However, you can also simply use the Settings search box and type ‘mac’ to get the requisite.
Note: The WiFi MAC varies based on your choice: device MAC or randomized MAC. Using randomized MAC will assign one such address as per connection which won’t change even if you ‘forget network’. However, device MAC remains the same, irrespective of the WiFi you’re connected to.
iPhone
iPhone also has these options in multiple locations based on the MAC address you’re trying to find.
#1. WiFi MAC
Enter Settings> WiFi. Here, tap 🛈 beside the active connection. Now, locate the WiFi Address, which is actually the MAC address.
#2. Device MAC
Head over to Settings>General>About. Now scroll down and check the WiFi Address. Notably, this is different from the WiFi MAC and will be there even if not connected to any WiFi connection.
Enable MAC Address Filtering
After you’ve made a list of the MAC addresses to allowlist, it’s time to log in to the WiFi router console. Again, this heavily depends on your router.
Remember to have an active WiFi or ethernet connection with the same router before proceeding.
It starts with logging into the dashboard with the default gateway URL (typically 192.168.1.1)
Windows PC users can check this router login URL by typing in ipconfig/all in the command prompt and scrolling down to the Default Gateway of the active connection.
Mac people can navigate to the Apple menu>System Preferences>Network. Now, click the connection name and enter into the Advanced section. Here, click the TCP/IP tab to find the default gateway URL in the router section (Router: xx.xx.xx.x).
Next, log into the router dashboard with the username and password.
My router has this option in the Security section under MAC Filter, as shown below:
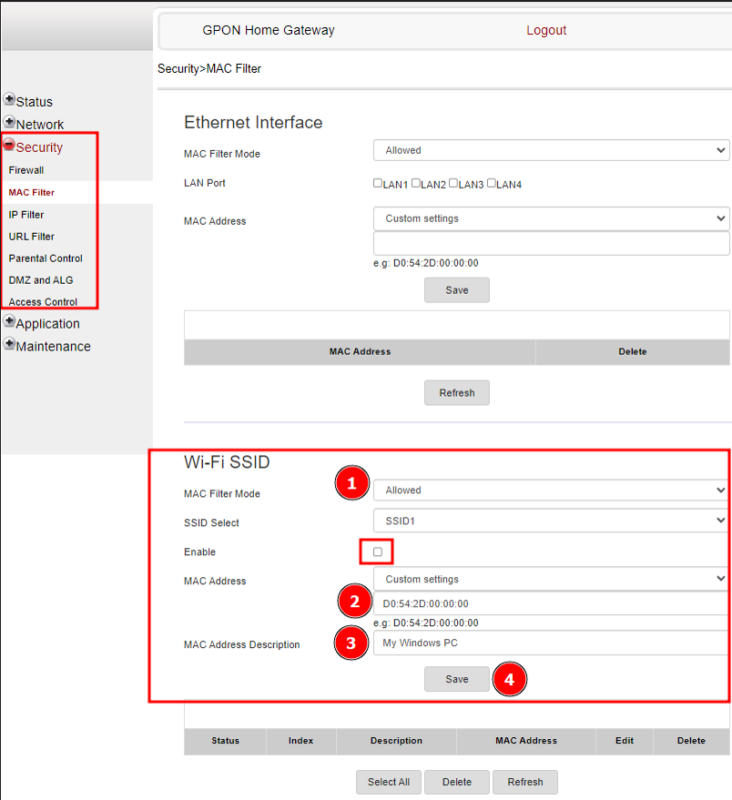
One can create separate filters for Ethernet and WiFi. But let’s go ahead with the WiFi since private WiFi owners have more control over ethernet connectivity.
Here, the first thing is selecting the filter mode: Allowed or Blocked. Because I’m setting this for a few of my personal devices, I’ll proceed with ‘Allowed’ to restrict connectivity to outsiders.
Next, one should enter the MAC address of the permitted devices, add a little description, and hit save. Finally, don’t forget to check Enable to allow this filtering to go live.
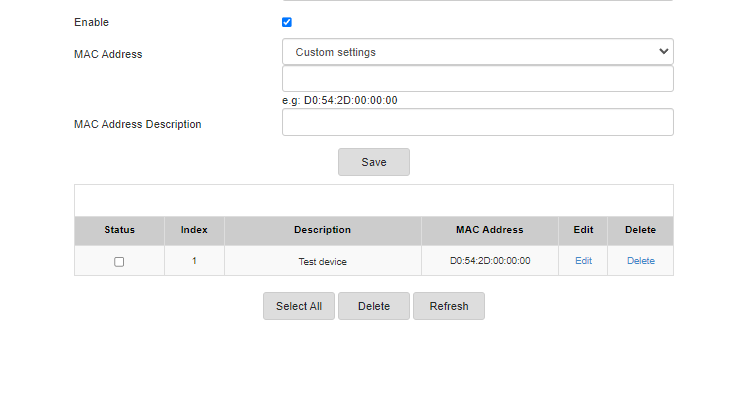
The added devices will show at the bottom for further modifications.
And that’s it. Now only the safelisted devices can access the router’s WiFi.
Alternatively, one could set it up with the Blocked mode, preventing internet access for the listed devices while allowing everyone else.
Benefits and Drawbacks of MAC Address Filtering
The obvious benefit of MAC address filtering is WiFi protection. It stops freeloaders from enjoying your data without your permission.
In addition to bandwidth loss, it averts the risk of any cybercrime organized with your IP address to its name.
Coming to demerits, you must add all new devices to the filtering database. While this isn’t a problem for your personal devices, it’s extremely annoying if you host guests or parties frequently.
Consequently, this is a devil you have to deal with to enjoy greater control over your data and security.
Stop the Theft!
MAC addresses identify all digital devices with internet connectivity. One can use them to prevent unauthorized internet access, even if the WiFi password is somehow leaked.
PS: ISP-supplied routers often lack advanced features like VPN. If you feel the same and are searching for a perfect alternative, look no further than this curated list of the best WiFi routers.


