Smartphones have become an essential part of our daily lives, facilitating tasks such as shopping, banking, and making payments.
Safety is a primary concern while we store our personal and financial information on mobile devices, making us vulnerable to hacking and other online threats. These vulnerabilities mainly arise due to a lack of security updates.
Google announced in July 2023 that only Android version 10 and above will receive security patches going forward. Below is the distribution of Android versions used worldwide.
More than 25% of the Android versions will not receive security patches. There are more than 2.3 billion Android users in the world, which means at least half a million Android users are vulnerable.
The following apps will help you to protect your Android devices from online identity & security threats.
Avast Mobile Security
Avast is a great app to provide your Android phone protection against viruses coupled with many other threats.

Avast is one of the world’s most trusted free antivirus for Android, which alerts you when spyware, adware get installed and violate your privacy.
The detection rate of the latest Android malware is about 99.9% and is around 100% of malware detected in the last four weeks.
Verdict: If malware and safe browsing are your primary concern, this app is appropriate for you.
Malwarebytes Mobile Security
Safeguard your Android devices from ransomware, malware, and other threats using the advanced protection of Malwarebytes Mobile Security.

It can efficiently detect dangerous threats and remove them before your device gets compromised. Malwarebytes Mobile Security offers real-time shields and scans for even sophisticated phishing URLs while you use the Chrome browser. It also alerts you in case it detects anything suspicious to ensure a safe browsing experience.
The application conducts periodic privacy audits by identifying access permissions of your apps installed on your phone or tablet. You can track those apps by tracking your location, costing you hidden fees, or monitoring your calls. Malwarebytes can quickly search all your files for malware and potentially harmful programs, including adware, screen lockers, etc.
It supports Android versions 6.0 or higher and languages like English, French, Italian, Spanish, Russian, Dutch, German, Indonesian, Polish, and Portuguese.
You can also check out our detailed review of Malwarebytes for more information.
Want to try out?
Malwarebytes offers a 30-day free trial with all the premium features. You can buy its starting plan for $3.33/month for one device or choose a higher plan for more devices.
Kaspersky: VPN & Antivirus
For good reasons, Kaspersky is a well-known name in the cybersecurity space. This free-to-download app has excellent features to keep you safe in this ever-dangerous digital territory.

This has:
- Real-time malware protection
- Remote wipe & Find My Device
- Anti-phishing mechanisms
- Safe browsing and messaging
- Password manager
- Virtual private network, etc.
In addition, you get a breach alert to tell if your personally identifiable information is leaked. Besides, it also pings you when a new device connects to your WiFi network.
Overall, it provides Kaspersky 360-degree protection in a freemium package which is definitely worth considering.
Norton 360 Mobile Security
Norton 360 mobile security covers all bases to offer complete peace of mind. It helps you fight against online threats with its malware detection, advert blocker, WiFi analyzer, etc.
Following the trend, Norton mobile security also has a built-in VPN to encrypt all the network traffic.
Additionally, you get powerful phishing detectors indicating risky links in text messages, emails, and apps. Likewise, it identifies your personal information leaks over the dark web.
You can check this and more with its 14-day premium trial.
McAfee Security
McAfee security packs a capable cybersecurity suite to become the guardian of your smartphone.
It includes:
- Malware shield
- VPN
- Wi-Fi Scan
- Identity Protection
- Anti-phishing, etc.
The subscriptions of McAfee come in two flavors which basically differ in their identity protection module and a few advanced features you can check in their 7-day free trial.
AVG Antivirus & Security
AVG is another freemium mobile security solution with a decently powerful free version. Its paid subscription is frequently dubbed as ‘well worth’ by its enormous user base.
It offers:
- Malware scanner
- Phishing protection
- Media vault
- App lock
- VPN
- Performance booster
In addition to this long list of features, you also get an app usage tracker, breach alert, junk cleaner, etc.
You can expect similarities among Avast, Norton, and AVG mobile security, as all of these work under the same parent company.
Overall, it promises a lot to be ignored, and its powerful free subscription makes it a must-try security application.
ESET Mobile Security
ESET comes loaded with the best features to help you stay secure, and you can try its premium package for 30 days without paying a penny.
You’ll get:
- Antivirus
- USB scanner
- Online payment protection
- Powerful Anti-theft
- Remote wipe
- App lock
- Call filtering
- Scheduled scans, etc.
Among these, ESET antivirus, real-time scanning, security reports, activity logs, etc., are free features.
A paid subscription is clearly more potent with the advanced protection for 5-devices per plan.
Bitdefender Mobile Security
A critically acclaimed security product, Bitdefender offers a free premium trial for the first 14 days.

It boasts of:
- Malware detector
- Internet security
- Breach alert
- App locker
- VPN
- Anti-theft, etc.
In addition to your Android smartphone, Bitdefender also protects Android wear devices. Besides, its autopilot mode recommends security actions based on usage.
Overall, Bitdefender has a solid premium subscription and a capable free plan anyone can take benefit of.
Firefox Focus
There’s no better feeling than browsing without fear, and Firefox Focus helps you achieve just that. It’s an amazing browser that blocks a wide range of trackers while also erasing your history, passwords, and cookies.

As a result of blocking unwanted ads and trackers, you’ll be able to browse a lot faster. Since this app is powered by Mozilla, it’s completely free and gives you the basic right to browse privately. 🙂
Sophos Intercept X
Sophos Intercept X is one of the best antivirus apps one could have on Android at absolutely no cost.
Its user interface may not impress you much. However, its features will surely soothe your mind.
Features:
- Virus scanning of installed apps, existing apps, and storage media
- Loss and theft protection with the support of remote access which allows the user to wipe, lock, ring, and locate your device.
- Web-filtering
- Spam blocking
Sophos Intercept X boasts the latest malware detection rate of 100%, which helps it to stand out from the rest.
Secure Call
It ensures your calls in such a way that nobody can listen to them. Secure Call provides end-to-end encryption for your private calls, thus preventing them from being overheard by intruders.
It uses a default phone app to make and receive phone calls. Its Peer-to-peer architecture with a robust end-to-end encryption prevents your calls from being stolen by Third parties, including the developers of this app.
Verdict: If you want end-to-end encryption for phone calls, use Secure Call.
NoRoot Firewall
Many apps on your Android device might be using and eating up your mobile data unnecessarily.
NoRoot Firewall puts you in control of Internet access for apps without rooting your device. It allows us to choose whether a particular app can access the Internet only over wifi only over mobile data, or neither or both.
Orbot

Orbot is an Android application, a part of the Tor project, which allows you to route all of your traffic through the Tor network.
VPN uses a single server, whereas Tor routes your traffic through various tunnels making sure no traces are left behind. Orbot creates a genuinely private mobile data connection. Data gets encrypted and re-encrypted
Data gets encrypted and re-encrypted multiple numbers of times until it reaches the last network where it gets decrypted, thus preventing the sender from being traced.
F-Secure Total

Similarly to the products from Bitdefender and Norton, F-Secure Mobile Security is a part of a complete package (F-Secure SAFE) that protects you on any device of yours – i.e., mobile, laptop, desktop, etc. They offer a free trial and multiple paid options to choose from.
All paid plans are for a year, and you choose what you want to protect. You can also choose which features to purchase – i.e., total protection, VPN only, etc.
Read our review to learn more about F-Secure VPN.
As for features, these depend on the plan you want to purchase. Features include protection against viruses, spyware, and hacker attacks, as well as ID theft, call, and message blocking, safe online banking, and protection against malicious apps. For smartphones and tablets, you have the option to lock or locate the device remotely, or if it gets stolen, you can remotely erase your data.
If you need it, there is also a parental control option.
VIPRE Android Security
Protect your Android smartphones or tablets from 20,000+ malware and viruses by using VIPRE Android Security. This sophisticated antivirus can keep hackers at bay while helping you find your lost device and secure it.

With on-demand and on-install scanning features, this antivirus protects your devices along with its data from malicious applications. They constantly update the scanner with the latest security patches and offer automatic scanning for applications upon installation immediately.
It is endowed with web protection to identify malicious activities to provide a safer browsing experience on a majority of browsers. Anti-theft features can geo-locate, lock, and notify your device from internet-powered devices.
VIPRE has an autopilot feature that works like your security advisor. It provides you with complete information on the security status of your devices so you can stay alert. For email privacy, it is possible to check whether your email address or its details are safe or not.
With Smart unlock, you can access all your applications directly by disabling your PIN while using Wi-Fi from a trusted source. Add an extra layer of protection with fingerprint sensor support included in the app.
What’s more – the antivirus comes with a PIN timeout feature. When anyone tries to access any of your applications with PIN protection, it displays a 30-second timeout on five consecutive unsuccessful attempts. Also, if anyone tampers with your device without your knowledge, your smartphone will snap a picture of that person.
Its price is $15.99 for one year, one device.
Avira Antivirus Security

If you are a fan of things made in Germany, then you might want to start your search for an antivirus with Avira Antivirus Security for Android. Its free version offers protection against spyware, adware, and banking trojans, as well as ransomware. The antitheft module is also free. It includes standard functionality, such as pinpoint a lost phone on a map, remotely lock it and remotely wipe out its contents, if you believe it’s lost for good.
The premium features include the option to lock your camera and microphone, block phishing sites, and use a PIN code to lock sensitive apps.
Comodo Mobile Security
With its reported 1 Million + installs, Comodo Mobile Security isn’t as popular as Avast or AVG, but still, it has managed to get noticed by users. Comodo Mobile Security is more than an antivirus. In addition to its high-performance malware engine.
Chili Security
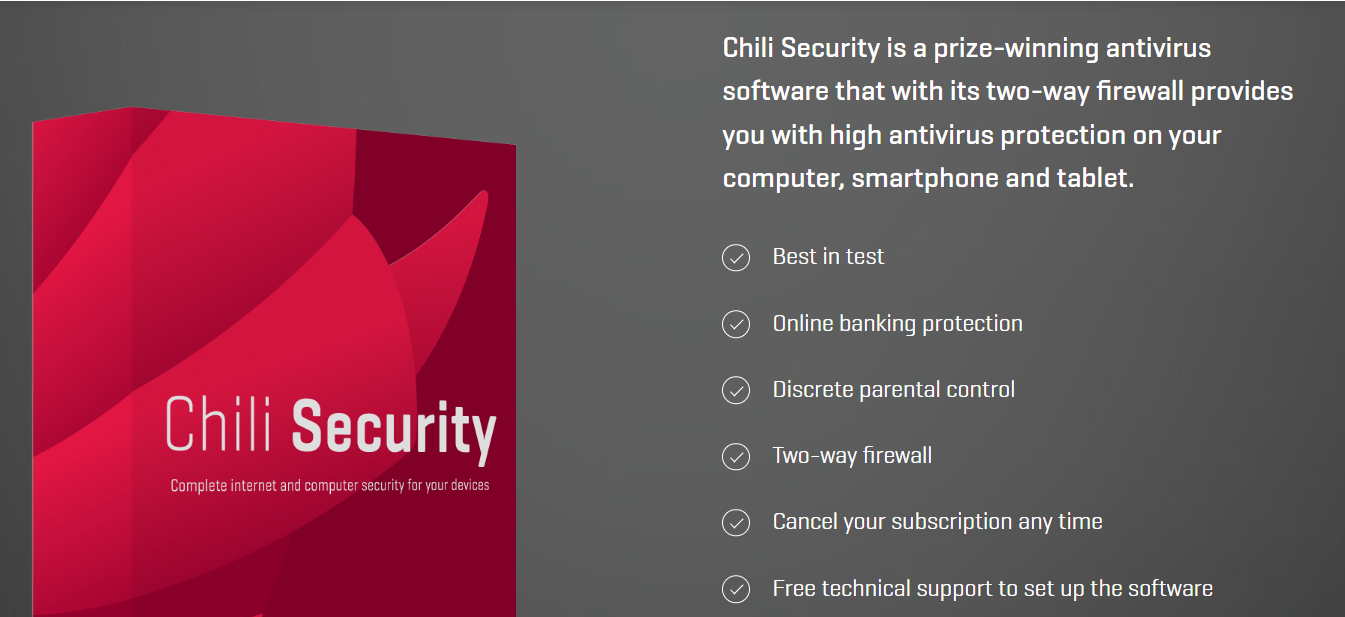
Chili Security isn’t as popular as some of the other names on this list, but their offer is good, and this is why it makes sense to include it. They offer two pricing plans: EUR 5.00 per month for one device or EUR 11.00 per month for an unlimited number of devices. This is a bargain if you have numerous devices because, in this case, the price per device is low. Fo one or two devices, the savings are unsubstantial to none.
In terms of features, Netbank protection (i.e., extra protection for your online banking activities) and the two-way firewall are worth mentioning. Needless to say, they do offer the standard features, such as antivirus scans and automatic updates, as well as parental control.
FAQs
A good antivirus not only gives on-device security but internet protection as well. This makes it better than the present status of built-in Android security protocols. So yes, having a dedicated antivirus solution is beneficial and more trustworthy.
Free antivirus is better than having no antivirus. That being said, free (security) products can be dangerous themselves. They might be making money from you in ways you wouldn’t approve of. Ultimately, getting a good paid antivirus has no equal.
It depends on the application at hand. But generally, yes. An antivirus runs real-time background scans and can feel like slowing your Android down a bit. However, it keeps your system free from malware, which can hurt performance and security more than anything.
There is no fixed number. And typically, modern antivirus programs with real-time protection are set and forget things. They alert you in case of need and don’t need your intervention otherwise. But if it matters to you much, run a full-scan scan weekly, if not daily.
Wrapping Up
On this list, I tried to include the best free and paid Android Antivirus. There is no need to try them all, though you might have to try a few before you pick the one to go with. Once you pick a service that’s good enough for you, stick with it and make sure it’s at all times updated to the latest database of threats because if it isn’t, you are not getting the adequate protection you need.


