It can be annoying to see your computer prompting the error – “the requested operation requires elevation” . If you’re experiencing this issue, do not worry, as you’ve come to the right place.
In this article, we’ll be guiding you with suitable solutions to fix this error. But before stepping into the solution, let’s see what the error is about and why this error occurs.
What does “the requested operation requires elevation” mean?
When you try to access a file or install a program on your computer, you may encounter the error message, “the requested operation requires elevation”. This error indicates that the task you are trying to perform on your computer requires additional permission or authentication from the administrator.
To put it simply, your current user account on Windows doesn’t have the privilege to carry out the specific operation.
What causes the error “the requested operation requires elevation”?
While there are countless reasons behind this Windows error “the requested operation requires elevation”, this part lists the most common ones.
Corrupted user account: A corrupted Windows user account is more liable to lose data or access controls, resulting in a malfunction. This objects the user to perform certain tasks and shows the error “the requested operation requires elevation”.
Access privilege: The Windows account you are using might not have enough permissions to execute certain activities or access protected data. As a result, the error “the requested operation requires elevation” shows up.
User account control settings(UAC): When the user account control feature in Windows is turned on, it adds an extra layer of security by limiting the tasks that a non-administrative account can perform. However, these limitations could cause the error “the requested operation requires elevation” when you try performing certain tasks.
Malware or Virus: At times, a compromised system due to malware attacks results in the error “the requested operation requires elevation”. This is because the virus prevents your system from recognizing the authority of your Windows user account.
Here are some free PC Antivirus software to get rid of malware.
The majority of the fixes lie in repairing the causes we covered earlier. However, a few simple fixes are entirely new.
You don’t necessarily have to apply all the proposed workarounds. Try the fixes in order, until you find the one that works for you.
Fixes to “The requested operation requires elevation” error
Run the Program as an Administrator
When you run the program or file as an administrator, it gains administrative-level permission to perform a majority of the tasks that are typically restricted for regular user accounts on Windows.
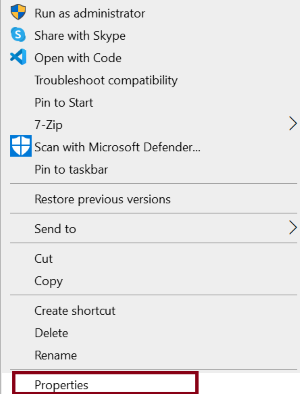
Step 1: Right-click on the application or program you want to open, then select Properties.
Step 2: Head to the compatibility tab; under the settings section, check the option Run this program as an administrator.
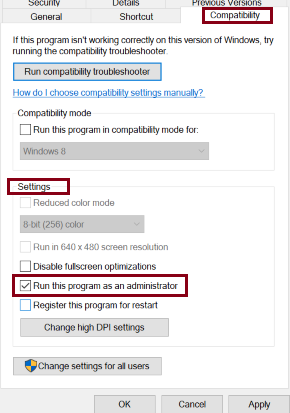
Step 3: Press Apply button to save the changes and then click on OK.
Check if this method worked by repeating the tasks that caused this error.
Extend Folder Privileges
If you encounter the error message, “the requested operation requires elevation” when attempting to access a folder, it means that the folder you want to access demands elevated permissions to use it. So, let’s extend the control privileges for this folder to all user accounts.
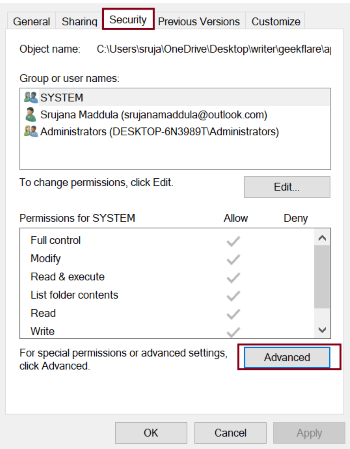
Step 1: Right-click on the folder you want to access and choose Properties.
Step 2: Switch to the security tab and click on the Advanced button.
Step 3: Check the option Replace all child object permission entries with inheritable permission entries from this object
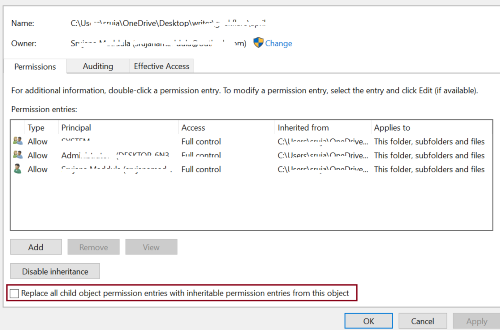
Step 4: Click Apply and OK to save the changes.
Try the following fix if this method didn’t help you.
Disable UAC
As mentioned earlier, UAC is a security feature in Windows that restricts you from performing certain tasks using a regular account. Disabling this feature can help you land on an error-free screen.
But I suggest you do this temporarily, as it exposes your system to vulnerabilities.
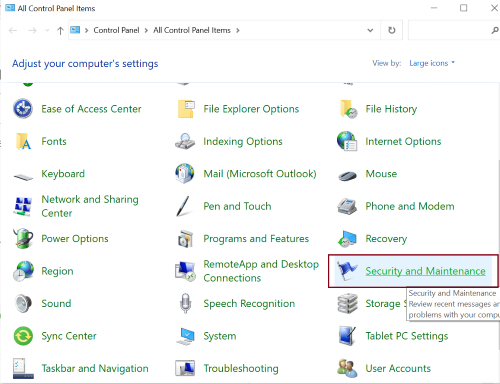
Step 1: Launch the control panel by searching it on the Windows search bar.
Step 2: Scroll for Security and Maintenance and click on it.
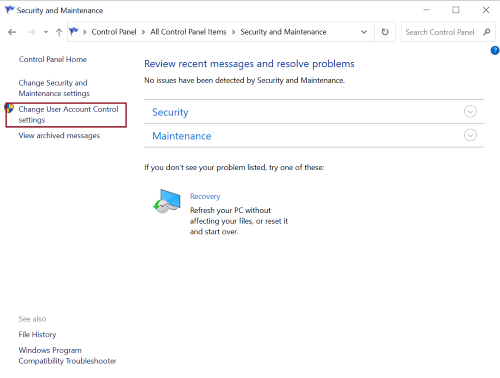
Step 3: You should see Change Users Account Control Settings in the left pane. Click on it.
Step 4: Drag the slider to the bottom end and press OK to save the changes.
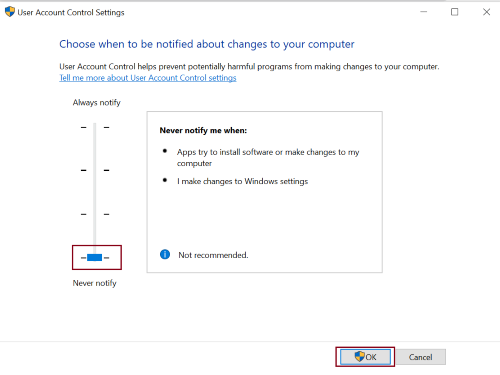
Restart your system and see if the error is gone.
Run SFC Scan
Corrupted or damaged files in your system can prompt the error the requested operation requited elevated permissions. Let’s fix it with the SFC scan.
Step 1: Search for command prompt by typing cmd in the Windows search bar.
Step 2: Right-click on the result to run as administrator.
Step 3: Input the command sfc /scannow and press enter.
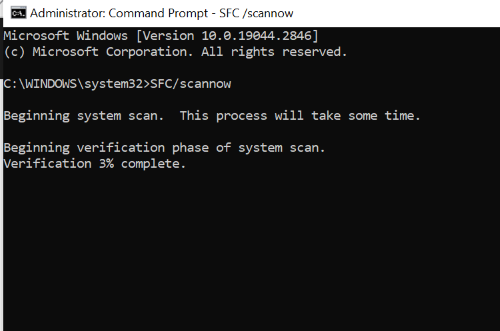
The scan runs and repairs any corrupted files.
How UAC (User Account Control) affects elevation in Windows 11?
Windows shows the error the requested operation requires elevation when you try performing certain actions, including accessing a file or folder, installing or modifying an application, or changing account settings.
“Elevation” in this context is simply granting administrative rights to a Windows user account or program to process tasks. UAC settings in Windows allow you to configure these access rights.
If the UAC feature is enabled in Windows, it prompts the user to approve the required elevation permissions before performing certain actions. This extends the security of your system by preventing unauthorized access. So, I recommend leaving this enabled by default and only disabling it temporarily to overcome the error.
Tips to prevent “The requested operation requires elevation” error in the future
- If you want to modify data or install software, use the administrator account.
- Run the command prompt as an administrator if you want to access or modify files or folders using Windows commands.
- You can also run the specific program you wish to use as an administrator, as shown in the first fix.
Final Words
I’m sure that for many of you, running a program in administrator mode will clear up the error “the requested operation requires elevation”.
In case the error popping up again, you can also try generic fixes like virus check, cleaning up cache and temporary files, and DISM scans that repairs system images to get rid of the error.


