How are you securing your API?
It’s the age of the digital economy explosion, and massive data loads are being piped through APIs. Business, gaming, education, weather, science, arts. You name it, everything works on APIs. For a world so fundamentally reliant on APIs, there’s surprisingly little focus on security.
For developers, the defaults of their frameworks are enough; or even worse, when no frameworks are being used, they think they’re following security practices. For system admins, the default security offered by their infrastructure or service provider is what they rely on.
Not a pretty sight at all, if you ask me.

Needless to say, there’s a lot at stake, which we realize only when something truly terrible happens.
Tools for Increasing API Protection
There are several tools that can help us scan vulnerability, or even better, offer the first line of defense when it comes to securing APIs. But be cautioned that at the end of the day, no security strategy is perfect. The below API protection tools can increase your API security manyfold, so they are recommended.
AppTrana
AppTrana’s dedicated API Protection features offer a comprehensive risk-based solution to protect against a wide range of API threats, including OWASP API top 10, API-based DDoS and bot attacks, embedded threats, data leakage, etc. With unlimited automated API scanning backed with manual pen-testing, it continuously monitors your risk score to strengthen the security posture.
AppTrana’s API protection ensures the most comprehensive solution with the combination of Risk detection, API Threat detection, API Positive Security policies, API-Specific DDoS policies, API-Specific Bot modules, and API Discovery features.

Its API discovery ensures complete visibility into API calls, including undocumented and shadow APIs, to understand your API attack surface. This dedicated API protection collects information about user details, API usage behavior, threat activity, API call maps, and more to showcase the protection status with real-time analytics.
Using Indusface AppTrana, you can generate tailored API-specific policies to block API-focused abuse in real time.
Cloudflare
Cloudflare’s advanced web application firewall (WAF) is crucial for ensuring secure and efficient applications and APIs. It defends against DDoS attacks, blocks unauthorized bot access, detects malicious data, and scans for browser supply chain attacks.

Cloudflare’s extensive worldwide network facilitates the transmission of vast amounts of traffic through its API gateway. To ensure the security of its APIs, Cloudflare employs a comprehensive framework encompassing API discovery, integrated API management and analytics, and layered API defenses.
API Gateway provides secure and efficient API management, including discovery, Layer 7 security, Mutual TLS, positive API security, abuse detection, and sensitive data detection. It facilitates endpoint identification and monitoring, protects against attacks, implements authentication, verifies OpenAPI schemas, and prevents data leaks.
Cloudflare API Gateway protects against OWASP API risks.
Graylog API Security
Graylog API Security provides real-time API monitoring, threat detection, and streamlined actionable remediation insights to meet the evolving security needs of organizations where traditional solutions such as WAFs and API gateways are failing.
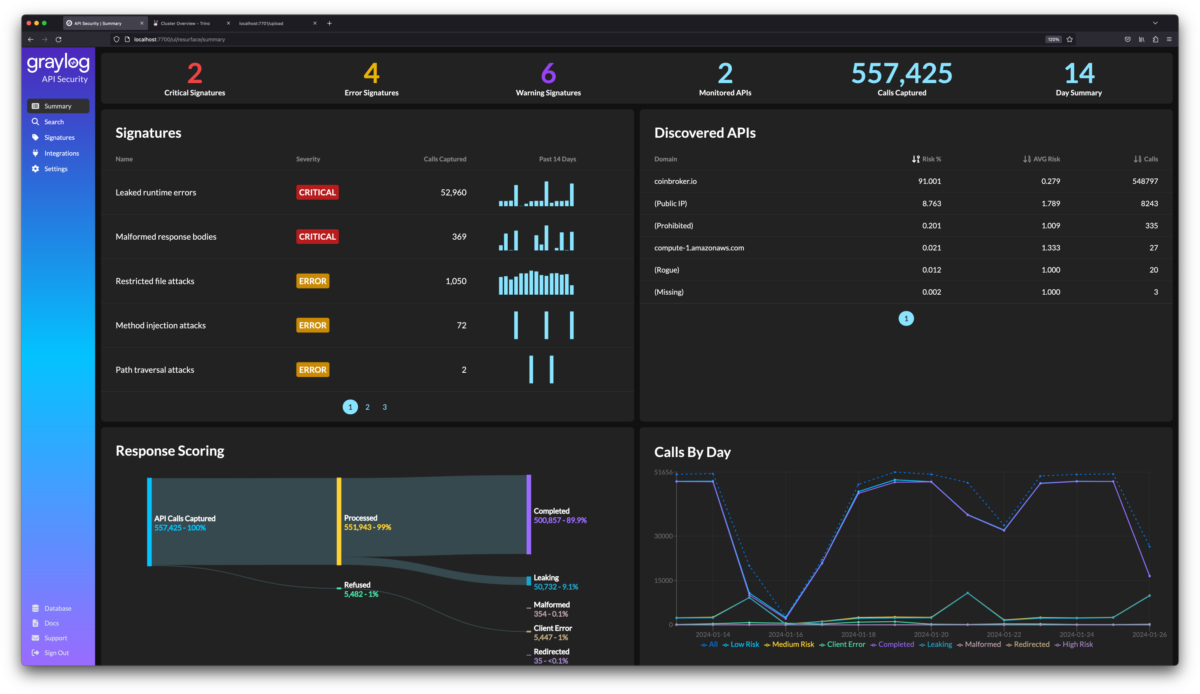
Graylog API Security is a cloud-native architecture for self-managed private cloud or on-prem implementations to ensure the detection of data leakage via APIs. It is the only self-managed API solution that captures the full payload of both API requests and responses.
With Graylog API Security, practitioners gain:
- API Discovery: Automatically discover and categorize APIs for focused monitoring
- Risk Scoring: Prioritize alerts based on their relative risk to the organization
- Full-Fidelity Capture: Capture the complete API request and response payload, creating a readily accessible datastore for both real-time attack detection and forensic search
- Real-Time Threat Intelligence: Stay ahead of emerging threats with continuous monitoring of APIs and out-of-the-box threat signatures
- Guided Remediation: Once a threat is detected, Graylog API Security automatically provides helpful, straightforward remediation information
- High-Level Insights: Presented on a summary dashboard, it can facilitate productive discussions across the company since API often sits at the intersection of DevOps, Network, Security, and Application teams
Graylog API Security operates inside the perimeter to protect against insiders and authenticated attackers masquerading as legitimate customers and partners to access sensitive data.
Invicti
Invicti comes with a USP of “proof-based scanning”. In simpler terms, it’s often possible that irregular network conditions or some lesser-known API behaviors are construed as security loopholes, which are later found to be wrong.
This wastes resources, as all the vulnerabilities reported, need to be scanned again manually to confirm that they aren’t false positives. Invicti says the tool is able to provide you with a strong enough proof of concept for the reports, removing doubts about the weak links found.

With companies like Sony, Religare, Coca-Cola, Huawei, etc., on their client list, you can be sure that these folks are doing something right. 🙂
Okta

Try Okta to enable your developers to concentrate on enhancing the user experience as well as secure your enterprise data efficiently. It offers OAuth 2.0 authorization and is designed for both mobile and web applications. It is also compatible with third-party API management services.
Use Okta to create, audit, and maintain all the policies for API access through user-friendly and purpose-built consoles without needing custom codes. It offers you extra flexibility so that you don’t have to secure your APIs using extra gateway instances.
Okta encompasses identity-driven policy to control different types of users and services under one roof. Define access depending upon user profiles, networks, groups, consent, and clients. Extend tokens using dynamic data from your internal systems to enjoy faster integration and seamless migration.
It facilitates a centralized administration for APIs and lets you protect API resources. Okta focuses on security by allowing you to safeguard access between different micro-services.
42crunch
42Crunch is an API security platform for developers to seamlessly integrate security measures into the API development pipeline, ensuring proactive testing, fixing, and protection from development to runtime.
The platform is trusted by top brands like Verizon, Ford, Bridgestone, Allianz, etc.
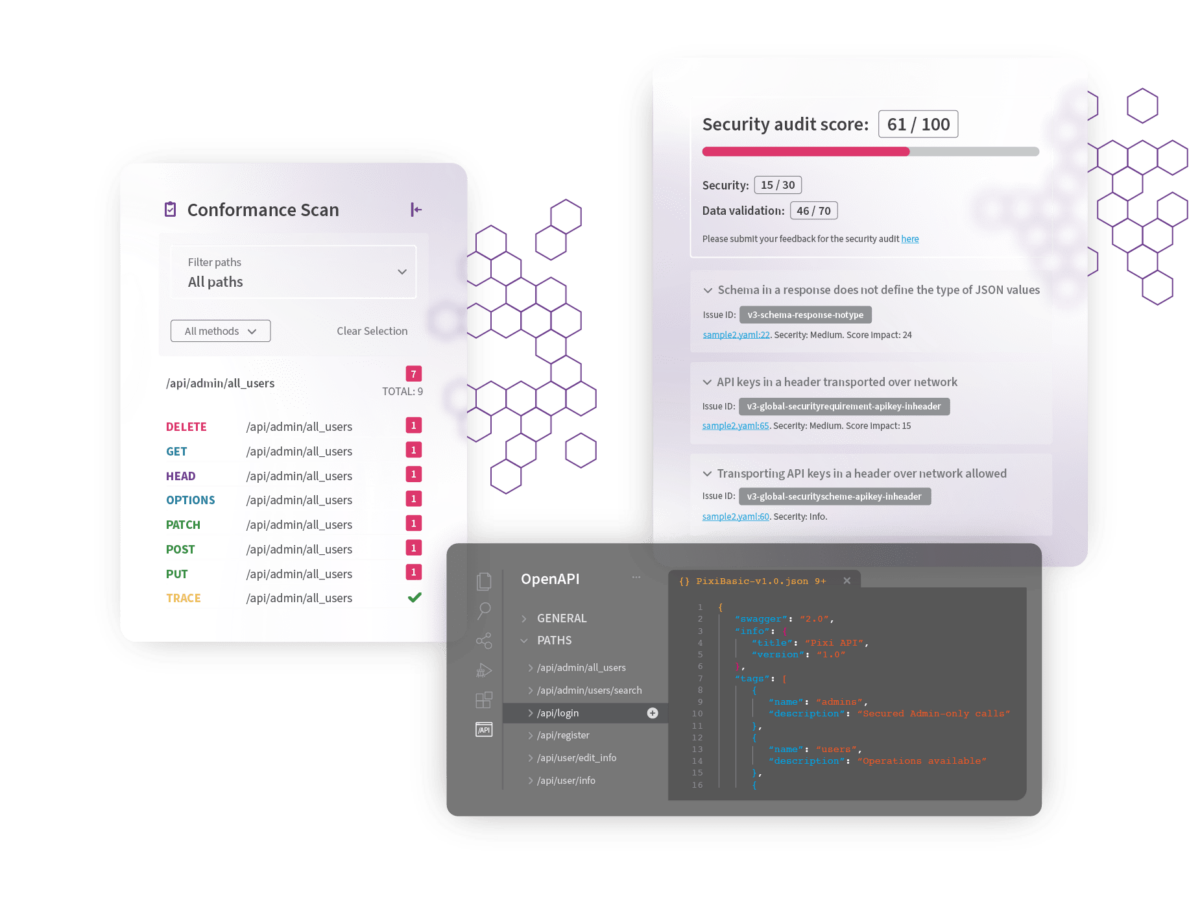
The company claims to be the only platform that ensures security governance and compliance from design to runtime.
It does this through API Audit, which performs 300 security checks; API Scan, which detects vulnerabilities in testing and runtime; and API Protect, which enforces runtime API security policies with a small, containerized micro-API firewall.
42Crunch’s API Security Testing tools help uncover API security weaknesses, while API Protection ensures runtime security with content validation, threat detection, traffic control, and an API micro-firewall. More than 800k developers adopt 42crunch API tools.
Probely
Probely is a vulnerability scanner used by SaaS businesses, developers, security teams, DevOps, and compliance professionals. It scans web apps and APIs, finds vulnerabilities, and offers detailed reports on how to resolve them.

Some top companies like Olx, Trend Micro, and Entertainment Partners trust this platform, which supports various web applications and APIs, including microservices and standalone APIs following an OpenAPI (Swagger) Specification or Postman Collection.
Probely provides a documented API and adapts vulnerability severity according to context. It integrates with CI/CD pipelines, automates security testing for web apps and APIs, and syncs with issue-tracking platforms.
It ensures compliance with standards like PCI-DSS, OWASP TOP 10, ISO27001, HIPAA, and GDPR. Try it free for 14 days.
APIsec
APIsec provides an automated platform for proactive and continuous API security testing. It builds client trust by thoroughly testing updates and releases to ensure a secure production environment.
The platform automates comprehensive security testing for APIs throughout the software development lifecycle (SDLC). It enables API discovery, analysis, and execution of customized attack scenarios before production.
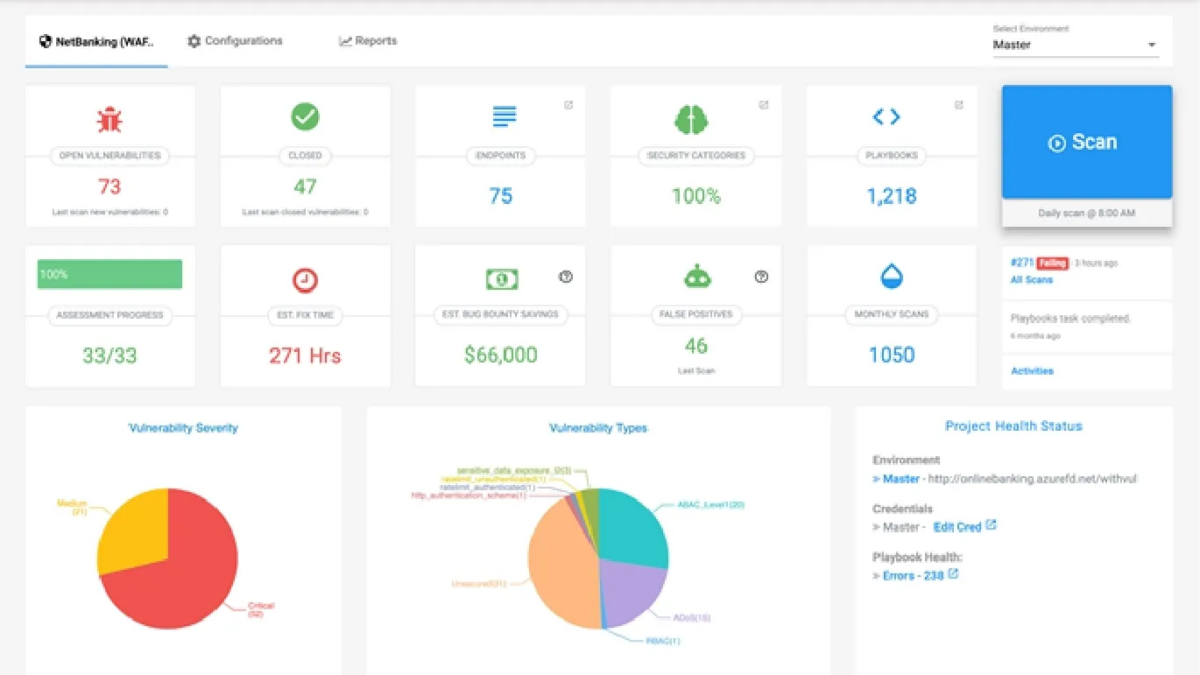
APIsec helps to get rid of repetitive manual third-party testing by automating the API security testing.
APIsec seamlessly integrates with CI/CD, ticketing, and communication platforms, ensuring a smooth workflow. Aligning API penetration tests with risk assessment enables the detection of security issues early on, reducing technical debt in application development.
The platform offers an unauthenticated API scanner, free of charge, to identify misconfigurations and other basic security flaws. It also offers free courses like API security fundamentals and expert API pen testing; if interested, you can visit APIsec University.
Cequence
Cequence is a multi-award-winning platform for API discovery, inventory, compliance, and dynamic testing. The platform aids in the identification and prevention of fraud, attacks, exploits, and data leaks in real-time.

It offers a comprehensive solution for identifying API attack surfaces in order to ensure threat protection as well as compliance and regulations. The platform can be easily integrated with your existing API and security infrastructure.
Cequence claims to have saved millions of dollars and billions of users while also ensuring the security of transactions. Some top companies that use this platform include RBS, American Express, Ulta Beauty, PoshMark, T-mobile, Telstra, etc.
API Discovery and Risk Assessment, Remediation of Sensitive Data Exposure, Account Takeover Prevention, and API Risk Assessment are some of its key features. The platform offers free API security assessment.
Why should we secure API endpoints?
We need to secure endpoints because, that’s what the business depends on. Not securing the API endpoints leads to the below undesirable consequences for the business.
Business loss 📉
This is the obvious one. If someone succeeds in messing with your API endpoints, it will bring everything to a screeching halt. Security breaches can also take a lot of time to recover from, which translates to suicide in business terms. While it’s true that most businesses probably won’t be affected by an hour or two of downtime, for some, it’s not permissible.
Imagine a currency exchange being down for a few minutes!
Compliance issues
Not securing your APIs properly can land you in serious trouble, depending on which geographies or industries you’re dealing with. For instance, if you’re serving the banking industry (in the EU, especially), the cost of being discovered serving with insecure APIs will result in massive legal and compliance troubles. So much so that it might even spell the end of your business.
Reputation loss
Being hacked is painful enough in itself, but if news gets out in public, there’s going to be an irrecoverable loss to your brand image. For instance, Sony has been hacked a few times very badly by now, and in security circles, the company is a laughing stock of sorts.
Even if no actual loss of data or money is incurred, good luck trying to convince your scuttling customers. 🙂
Inflated infrastructure bills 💰
When your API runs on infrastructure, it consumes resources (bandwidth, CPU, and memory, mostly). For instance, where the API is not secured properly, and malicious outsiders are able to interact with it, it’s possible for them to force the API to keep doing a lot of pointless work (running heavy database queries, for example), which can shoot up your bills for on reasons.
On platforms where automatic scaling of resources is enabled (like AWS), the outcomes can be shocking (off-topic, but if you ever get caught in a soup like this on AWS, they’re quite understanding of the situation and promptly waive off the inflated bill — as of writing, at least!).
Team morale
So, you might be thinking, that the team that let these compromises happen will lose morale over them. Well, not quite. It’s possible that the compromises were due to weak infrastructure security, which will dishearten the developers or vice versa.
Should this happen enough time, you’ll have a culture on your hands that you’ll regret letting develop.
Competitor’s gains
So let’s say there was a breach, but there was no actual loss. However, your competitors will use the incident to drum up their own API and assert how much more secure theirs is (even if it’s not!). Once again, good luck trying to convince the market. 🙂
All in all, there are consequences to security breaches that go beyond losing money.
Best Practices for Securing API endpoints
Thankfully, there are certain easy-to-implement and well-understood practices that you can apply to your API endpoints for securing them. Here’s what most security experts recommend.
HTTPS always 🔒
If your API endpoints allow API consumers to talk over http or other non-secure protocols, you’re putting them at a big risk. Passwords, secret keys, and credit card information can easily get stolen as any man-in-the-middle attack, or packet sniffer tool can read them as plain text.
So, always make https the only option available. No matter how trivial an endpoint might seem, connecting over http shouldn’t even be an option. TLS certificate doesn’t cost much; you can buy for as low as $20 from the SSL store.

One-way password hashing
Passwords should never be stored as plain text, as in the event that a security breach occurs, all the user accounts will be compromised. At the same time, symmetric encryption should be strictly avoided, as any attacker ingenious and persistent enough will be able to break them.
The only suggested option is asymmetric (or “one-way”) encryption algorithms for storing passwords. That way, neither an attacker nor any developer or sysadmin within the company will get to read customer passwords.
Strong authentication 💪
Now, almost every API has a form of authentication, but in my opinion, the OAuth2 system works the best. As opposed to other authentication methods, it divides your account into resources and allows only limited access to the auth token bearer.
At the same time, another very good practice to set tokens to expire every, say, 24 hours, so that they need to be refreshed. This way, even if your token gets leaked, there’s a chance that the 24-hour deadline will reduce the impact of the breach.
Apply rate limiting
Unless you have an API that’s used by millions of people every minute, it’s a very good idea to enforce a limit of how many calls a client can make to the API in a given time window.
This is mostly to discourage bots, which can keep sending hundreds of simultaneous requests every second and make your API eat up system resources for no good reason. All web development frameworks come with a rate-limiting middleware (and if not, it’s fairly easy to add it via a library) that takes just a minute or so to set up.
Validate input
This sounds like a no-brainer, but you’ll be surprised how many APIs fall for this. Validating input not just means checking that the incoming data is in a correct format, but also that no surprises are possible. A simple example is SQL injection, which can wipe out your databases if you let the query strings go by with little or no checking.
Another example is to validate the POST request size and return a proper error code and message to the client. Trying to accept and parse ridiculously large inputs will only serve to blow up the API.
Enforce IP address filtering, if applicable
If you’re into B2B services and your APIs are used by businesses from set locations, consider adding an extra layer of security that restricts IP addresses that can access your API. For every new location and new client, the IP address will need to be checked against the incoming request.
Yes, it adds nuisance to onboarding, but the end result is much tighter security than can be otherwise achieved.
Conclusion
There’s no shortage of API security tools available in the market, whether it is open source, free or commercial, or any combination of these.
Try a few of them from the list and see what works best for your requirements.


