Managed Detection and Response (MDR) solution is a combination of advanced security technologies, tools, and expertise that vendors offer to their customers in a security-as-a-service delivery model.
Instead of investing in a costly multi-product in-house solution, the organization outsources its IT security to a third-party MDR provider.
In this case, the provider monitors the customer’s infrastructure while proactively detecting and remediating current and emerging threats.
An MDR service provides advanced protection and is ideal for all organizations and especially those without adequate tools and skills to secure today’s complex IT environments.
It extends the in-house security systems with advanced tools and highly skilled experts to provide 24/7 monitoring and advanced threat detection and response – better than other cybersecurity solutions.
Consequently, organizations can access the latest and most effective security technologies and expertise without investing in costly in-house solutions.
Benefits of MDR Service

One of the main benefits of an MDR solution is improving the overall security posture of an organization. It also provides actionable threat intelligence and reports containing information that helps identify and address vulnerabilities and gaps in security systems and practices.
Other benefits of a managed detection and response solution include the following;
- 24/7 monitoring and fast, real-time detection and remediation of all threats, hence minimizing the number of successful attacks and damage.
- Enables organizations to gain better visibility into their IT infrastructure hence tracking user activity and detecting suspicious or malicious activities.
- Reduced costs -Eliminates the need to invest in costly in-house security systems and teams
- Helps organizations to comply with various industry and regulatory standards
How MDR Differs from Other Cybersecurity Solutions

An MDR service differs from other cybersecurity solutions in that it is run by a third-party provider. Although there might be an in-house solution, the MDR service complements the client’s existing security solutions, such as antivirus programs, firewalls, intrusion detection systems, and other tools.
However, the clients do not have to invest heavily to purchase costly in-house technologies and employ experts. Instead, the MDR service provider offers security tools and expertise as a service at a lower cost.
The provider proactively monitors an organization’s infrastructure, endpoints, network traffic, applications, log files, user activity, and other data points.
Upon detecting any threat or suspicious activities, the provider quickly investigates and mitigates the incident without necessarily having to consult the client. Consequently, this stops the attack before it damages or compromises the systems.
Key Features of an MDR Service

The key features of a managed detection and response service include the following;
- Advanced threat hunting using the latest and advanced tools and highly skilled experts. This enables the MDR solutions to detect evolving threats that bypass other security solutions.
- Uses advanced security analytics, artificial intelligence, machine learning, predictive analysis, behavioral modeling, network forensics, user and entity behavior analytics (UBEA), cloud security posture management (CSPM), and others to understand how attackers compromise IT systems.
- Provides real-time 24/7 protection by continuously monitoring the systems for current and emerging threats and any suspicious activities. This allows them to quickly detect and respond to any threats before they cause any damage.
- Upon detecting a threat or suspicious activity, the MDR service provider experts investigate the issues and take immediate action to stop the attack. Unless for new emerging threats, some outsourced solutions perform automatic remediation by quarantining suspicious files or blocking access to an IT resource when there is suspicious activity.
- Automated continuous monitoring of an organization’s IT infrastructure, networks, endpoints, applications, and other resources and activities to identify and resolve any threat. It also notifies the security teams of any attempted attacks and potential threats.
Why Organizations Choose MDR Services

With the evolving computing landscape, traditional security solutions are insufficient to protect the complex IT infrastructure. MDR helps to fill critical IT security gaps due to inadequate technologies, expertise, and monitoring capabilities. Most providers invest in highly skilled staff with advanced threat-hunting expertise.
Additionally, they deploy highly effective EDR tools and other technologies. Consequently, organizations without adequate skills, time, and budgets to invest in a robust security solution can outsource the security services from the MDR providers.
The service provides organizations with the technologies and expertise to effectively detect and stop all the threats that bypass in-house cybersecurity solutions. Ideally, the outsourced services provide continuous monitoring and in-depth analytics to gain full visibility into an organization’s infrastructure and reliably detect and respond to threats beyond what in-house solutions and teams can handle.
Managed Detection and Response Use Cases
Below are some of the organizations that can use managed detection and response services.
Small businesses
These can get the comprehensive protection of their assets without investing so much in in-house tools and skills. Usually, small businesses lack adequate resources to buy a stack of security solutions and employ highly skilled staff. As such, outsourcing security provides them with the latest technologies and resources at a fraction of the cost.
Big Organizations
As organizations and businesses continue to grow in size, staff, and infrastructure, the security teams may be overwhelmed due to the complexity of the systems. Additionally, a large organization may have offices distributed across several regions with a diverse user base, including remote workers and a variety of devices.
An MDR helps to monitor and protect the cloud environment, endpoints, in-house systems, workloads, data, and identities.
Government entities
Most government institutions run large and complex IT systems with sensitive and private data. Additionally, the systems must run without interruption to ensure efficient and prompt service delivery. As such, they need to protect the internal and external-facing applications and systems.
Financial institutions
Financial organizations hold a wide range of sensitive and private data that requires high security to prevent attacks, fraud, and theft. An MDR solution can provide an additional layer of security and round-the-clock monitoring and analysis to quickly detect and respond to suspicious activities.
Healthcare providers
Healthcare providers handle sensitive patient data that should not be accessed by unauthorized people. Additionally, they must comply with various regulatory standards, such as HIPPA, in regard to how they manage private data. An MDR solution enables them to quickly identify and mitigate threats while helping to comply with the various regulations.
To help you choose the right solution, here are the best MDR services.
Cybereason MDR
Cybereason MDR is a fast and effective detection, response, and prevention solution that helps organizations identify and stop all types of threats. It protects IT systems from even the most sophisticated attacks that in-house solutions cannot detect. The MDR solution provides fast detection and quick remediation of a threat.
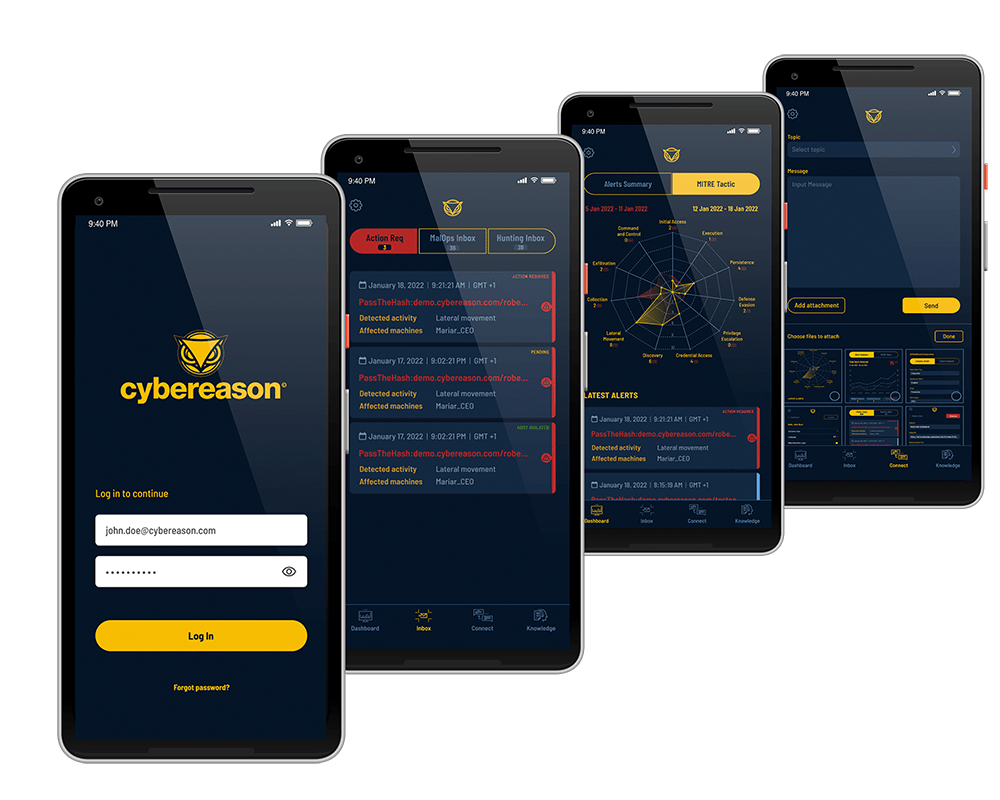
Key Features:
- Provides comprehensive and effective protection for all your IT systems externally, thereby covering all your security needs and enabling your IT staff to focus on other issues.
- Enables organizations to improve their security posture and protect all endpoints regardless of location.
- Uses an intelligent Cyberreason Severity Score feature to filter and reduce alert fatigue.
- Seamless and fast deployment, enabling you to secure your assets in only a few minutes
- Has a Cybereason MDR Mobile App to empower security teams with up-to-date information and allows them to access dashboards and respond to threats from anywhere.
Heimdal
Heimdal’s Managed Extended Detection and Response (MXDR) solution offers a 24×7 managed security service with an expert team of experienced professionals.
The award-winning platform, with more than 15k customers, provides event monitoring, threat investigations, and forensics to perform proactive analysis on threats, and its action-oriented incident response team neutralizes attacks quickly.
Its AI-powered and integrated solutions deliver optimal operational efficiency for SecOps teams to decrease alert fatigue to work proactively.
It offers a comprehensive suite of 10+ fully integrated services purposely built from empowerment onsite or remote workforce for enabling the CISOs, Security Teams, and IT admins – anywhere.
At a fraction of the cost, users are assured of enterprise-level security, which offers maximum value from your investment due to its cost-effective solutions and is maintained without additional teams or infrastructure costs.
Key Features
- Its advanced automated responses would decrease both the time it took to detect the attacks (Mean Time To Detect – MTTD) and, once detected, decrease the necessary time for resolution (MTTR), thereby ensuring the protection of networks, endpoints, emails, access points, and identities.
- Delivers advanced and comprehensive machine learning results, behavioral pattern analysis, and threat visualization with the extended power of Heimdal’s suite across threat intelligence, telemetry data, and detection rulesets, delivering evidence-based securities.
- With an experienced team of investigators and defenders at your disposal, advanced security solutions are implemented quickly with gap skills identified, swift investigations provided, and measures taken to ensure the least downtime or interruptions in productivity.
- Its advanced cybersecurity solution with Extended Threat Protection employs Predictive AI and MITRE ATT&CK techniques to give real-time visibility across your network, endpoints, and email vulnerabilities.
- The intuitive design allows quick response or action under manual and automatic options to take the initiative for security compliance.
- Its user-friendly interface evidently provides a solution to staying informed of potential threats while still being in control of any remedy and required response.
The platform is powered by Heimdal XDR – Unified Security Platform and offers the broadest range coverage against advanced tactics, including reconnaissance, exfiltration credential abuse, and ransomware encryption.
Sophos MDR

Sophos MDR is a superior and cost-effective MDR service that provides 24/7 advanced protection against breaches and ransomware.
The SaaS-based managed detection and response solutions help to free up your security teams’ time and let them focus on other issues. Sophos offers organizations the latest cybersecurity tools and expertise without investing in costly in-house systems.
Key Features:
- Tailor-defined solutions that allow security teams to customize the level of service based on the organization’s unique needs and existing security gaps.
- Provides complete incident response, hence ensuring minimal downtime and damage. While enabling you to quickly recover from the threat and continue operations.
- A centralized dashboard and reports system that provides insights into your security posture, security incidences, and action taken on a weekly and monthly basis.
- Seamlessly integrates and works in conjunction with the existing security solutions
- Provides 24/7 monitoring and immediate incident response service upon detecting a threat. It then sends you a notification about the threat and action taken.
Rapid7 MDR
Rapid7 MDR is a powerful service that helps to detect and mitigate threats using the latest and most effective technologies. It also provides monitoring and threat hunting to stop attackers before they strike.
The managed detection and response solution relies on multiple advanced detection technologies such as behavioral analytics, threat intelligence, network traffic analysis, and others to detect and respond to threats.
Key Features:
- Provides a cost-effective and complete 24/7 end-to-end security operation center (SOC) with instant response to the endpoint and user threats.
- Excellent reporting and alerting features. It provides comprehensive reports, analysis, and a wide range of metrics.
- Enables organizations to extend their security teams with Digital Forensic and Incident Response (DFIR) and threat analysis experts.
- Combines multiple advanced technologies such as InsightIDR’s XDR, forensic tools, external and internal threat intelligence, and hunting solutions. Consequently, Rapid 7 can quickly detect and mitigate all existing and emerging threats.
- Unlimited and customizable rules and alerts tuning to meet your organization’s needs.
Crowdstrike Falcon Complete MDR
CrowdStrike Falcon Complete MDR is a powerful, advanced cloud-native MDR platform that protects servers, workstations, cloud workloads, endpoints, users, data, and identity.
It uses real-time indicators such as threat intelligence, cyberattacks, telemetry, and others to accurately detect threats and gain visibility into vulnerabilities. Additionally, it provides automated threat hunting and protection mitigation.
Key Features:
- A lightweight, scalable, and fast tool with high detection coverage, advanced performance, and protection.
- Provides rapid detection and elimination of threats while quarantining suspicious files and alerting the organization’s teams to investigate further.
- Protects critical assets, including cloud workloads, endpoints, user accounts, and data, with the highest efficiency.
- Besides detection and response, it provides a free cleanup and restoration in case the attack has compromised the systems.
- Provides real-time visibility and advanced threat intelligence.
Cynet 360 AutoXDR
Cynet 360 AutoXDR is a comprehensive MDR that provides effective 24/7 protection by improving visibility, threat detection, response, and prevention. It is a cost-effective solution that eliminates the need to invest in costly multi-product solutions and large skilled security teams.
The automated end-to-end outsourced security platform helps organizations protect their systems using lean in-house teams.
Key Features:
- Enhanced protection of the organizations’ assets, network, endpoints, users, in-house and third-party applications, and systems
- Combines signals from networks, endpoints, decoy beacons, users, and other sources to provide real-time visibility into potential threats.
- Uses preset behavior tools and dynamic behavior profiling to detect suspicious user activities
- It provides multi-layer protection against Man-In-The-Middle (MITM), data exfiltration, scanning attacks, file attacks, malware, ransomware, and other exploits.
- Gain insights into the detection, response, and investigation services provided.
Alert Logic
Alert Logic is a comprehensive threat detection, response, and prevention platform. The solution is customizable to meet the specific security need of any organization.
It helps to detect, investigate and stop active threats across endpoint devices, applications, and networks. Alert Logic has advanced capabilities such as user behavior tracking, PCI scanning, web log analytics, and real-time reporting.
Key Features:
- Minimizes attacks by detecting and addressing potential threats, configuration issues, and any other vulnerability that could result in a compromise.
- For successful attacks, the solution provides quick detection and remediation, thus reducing the impact or damage of an attack.
- Provides an easy-to-use dashboard that provides in-depth insights, including all the alerts, analysis, and other reports generated by highly skilled Alert Logic security experts.
- 24/7 real-time SaaS threat detection and remediation, remediation guidance, and alerting backed by a team of security experts
- It helps organizations detect and prevent threats and data breaches and comply with GDPR, HIPAA, COBIT, ISO, and other regulatory standards.
Secureworks Taegis
Secureworks Taegis managed XDR is a powerful security platform that offers superior threat detection and response. It combines advanced threat detection with enhanced security expertise to provide 24/7 protection.
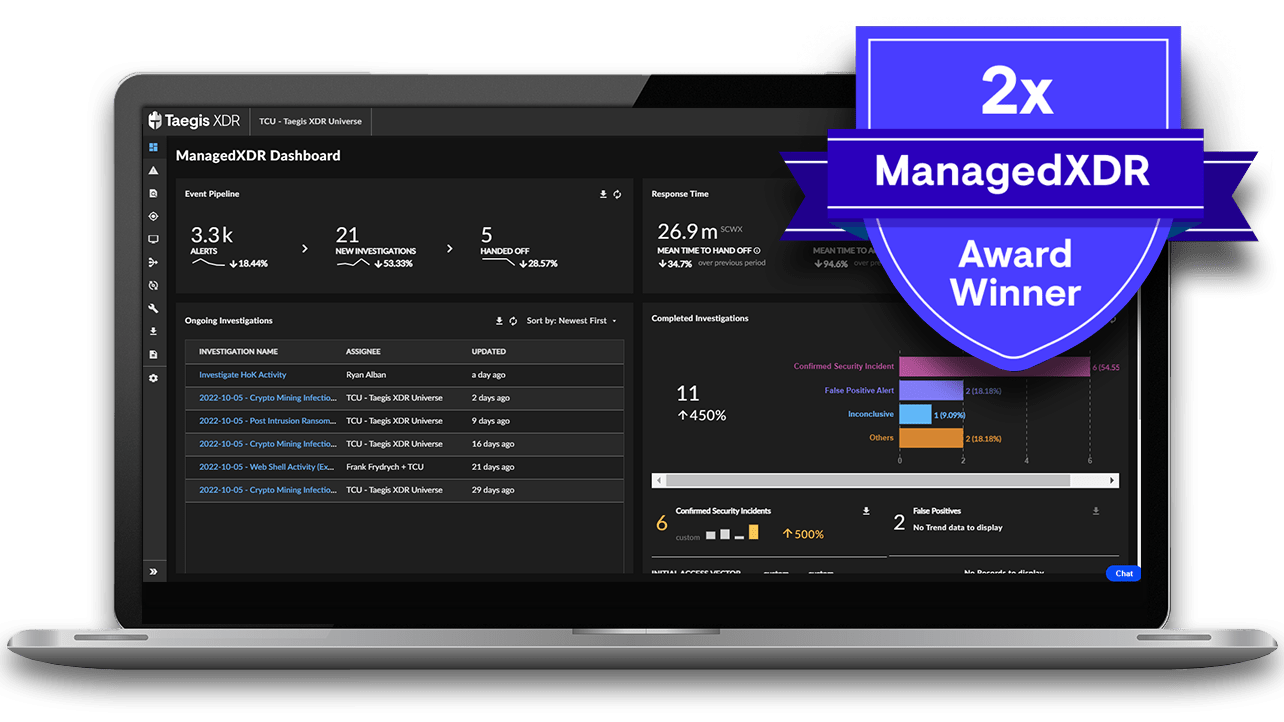
Key Features
- It provides holistic monitoring of the cloud, endpoint, network, identity, and other data points to provide you with useful insights, threat intelligence, and incident response, enabling you to reduce security risks.
- Gain access to highly trained security experts to address skills shortages in your organization.
- Maximize your security solutions investments.
- Uses comprehensive threat intelligence to protect your assets against the latest exploits and attacks.
Atos
Atos is an effective MDR solution that offers advanced and fast incident detection and response while providing continuous protection against all threats. The MDR service uses advanced security analytics on user behavior, applications, endpoints, and network to provide deeper detection.
It also uses artificial intelligence and machine learning to automatically detect, investigate and respond to threats.
Key Features:
- Use customized AI models to correspond to your organization’s security posture and potential threats.
- Has a real-time threat intelligence library to help security experts detect and respond to older and emerging threats?
- Advanced security monitoring that checks the networks, applications, user behavior, and endpoints and provides enhanced threat detection and protection
- Fast and effective incidence response to stop all attacks before they cause damage
- Enables you to detect, respond and protect your IT infrastructure without investing in in-house additional tools and security experts
- Automated threat remediation in real-time before it causes damages or compromises your systems.
Red Canary
Red Canary is a leading MDR solution with superior 24/7 threat detection and protection of networks, clouds, endpoints, SaaS applications, workloads, and identities. It provides 27/7 monitoring while investigating and reporting on threats and alerts.

The platform uses multiple threat detection technologies, highly skilled security analysts, and threat hunters to perform in-depth malware analysis, threat research, and investigations – providing maximum security.
Key Features:
- Advanced threat hunting using terabytes of security telemetry, over 3000 analytics, and over 20000 tests to detect hard-to-identify threats.
- Detect and respond to suspicious activity by a hacker or malware on an endpoint.
- Simple and predictable pricing plans with a flat rate for each endpoint
- Advanced alert filters to minimize false positives and prevent alerts and analysts’ fatigue.
- Provides comprehensive monitoring and threat and alert investigation. It also alerts the users with more accurate threat information with minimal false positives.
Conclusion
A managed detection and response service is one of the most cost-effective and reliable security for any organization. As cyber-attacks continue to evolve, most organizations cannot address all the threats due to a lack of tools, technology, and skills.
On the other hand, the MDR service providers invest in the latest technologies and expertise that enable them to address current and emerging threats. By offering advanced security-as-a-service, MDR providers allow organizations to access highly reliable, effective, and budget-friendly security.
Besides protecting the organization against threats in real-time, most MDR solutions have in-depth analytics and comprehensive reports that help organizations gain visibility into their security posture, identify and address the gaps, and prevent repeat issues.
Next, you may also read Information Security Management System (ISMS).






