Antivirus software is a type of program that detects and removes malicious files and unwanted programs, such as viruses, ransomware, worms, and spyware, from a device. Without robust antivirus software, a user’s system and data are vulnerable, and a cyberattack from these unwanted programs can lead to data loss and system malfunctioning. Antivirus software scans every file on your device and monitors any suspicious activity to detect and remove threats from the system.
The Geekflare team has researched and listed the best antivirus software available today based on factors such as performance, protection, ease of use, and malware detection rates.
You can trust Geekflare
At Geekflare, trust and transparency are paramount. Our team of experts, with over 185 years of combined experience in business and technology, tests and reviews software, ensuring our ratings and awards are unbiased and reliable. Learn how we test.
1. Avast One
Best for Comprehensive Digital Protection
Avast One offers an all-in-one service that combines security tools, antivirus with VPN, and speed-up tools to keep users safe and their data private. Alongside the paid versions, Avast One provides a free software tool for Windows, iOS, and macOS.
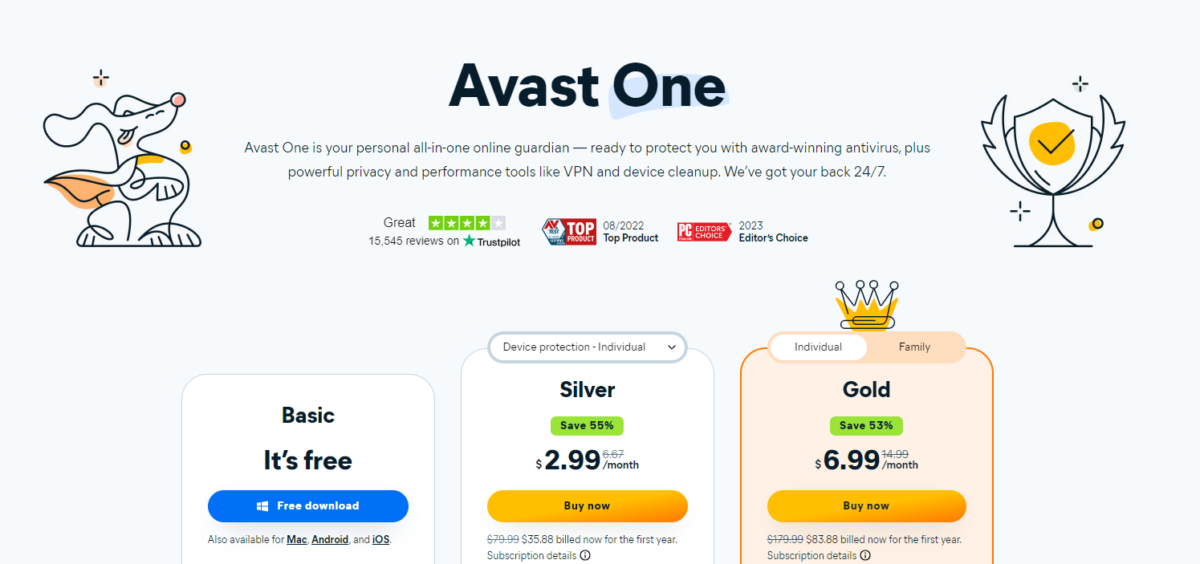
Using the Web Hijack Guard feature, users can block dangerous and fake websites. Furthermore, Considering the rise of ransomware attacks, Avast has taken action to offer Ransomware and Sensitive Data Shields.
Avast One’s Webcam Shield provides notifications when someone tries to access your webcam. Using VPN Secure Connection, you can Secure your personal information and identity from cybercriminals, stay private, and go online with military-grade security. For a detailed look at this antivirus, you can check our Avast One review.
Avast One Pros
Strong comprehensive protection.
Free version available.
Various features like Data Breach Monitoring and Web Hijack Guard for additional security.
Avast One Cons
Most advanced features are restricted to PC.
Recourse intensive operation.
Avast One Pricing
Avast One is available at a starting price of $79.99 for the first year, and protects up to 3 devices in the starter plan.
2. Malwarebytes
Best for Removing and Preventing Malware
Malwarebytes provides multiple-layered antiviruses that offer real-time protection from various emerging and existing threats, including phishing, zero-day exploits, ransomware, viruses, and other malware.
Additionally, it provides a browser extension for a safer, more private, and faster browsing experience. The browser extension removes ads and creates a safe online experience by blocking online scams, unwanted programs, and malicious websites.
Based on your chosen package, you will get features like anti-spyware, anti-malware, brute protection, and Wi-Fi security. It supports MacOS, iOS, Windows, Chrome, and Android.
For more information, you can check out how it performed in our detailed Malwarebytes antivirus review.
Malwarebytes Pros
Excellent capability at detecting and removing malware.
Minimal impact on system performance.
Simple and easy to use.
Malwarebytes Cons
Lack of real-time protection in the free version.
Lack of additional features compared to other options.
Malwarebytes Pricing Plans
Malwarebytes’ starter plan, the Basic Security plan, is available at $3.75/month, when billed annually.
3. Kaspersky
Best for High-Level Threat Detection
Kaspersky provides various anti-malware products for individuals and businesses. With Kaspersky Premium, you get multiple products under a single subscription. This packs its antivirus, a VPN, a password manager, identity theft protection, performance optimization, and more. However, while Kaspersky offers robust customer support for its features, it’s limited in some regions.
With Kaspersky, you get 360-degree privacy protection covering online browsing, smart home monitoring, and webcam and mic security. Additionally, this redirects every transaction through a secure browser to ensure financial detail secrecy. You also get protection from phishing scams at malicious websites and emails hosting rogue links.
Kaspersky password manager safely stores all passwords, credit card numbers, etc., and syncs them across platforms. Moreover, it is coupled with a dark web scanner, which notifies you if your credentials ever get leaked. Its virtual private network boasts over 2,000 global servers and has advanced features such as a kill switch, suspending internet connectivity if your VPN encryption drops accidentally.
This tool’s performance optimization involves a hard disk cleaner and health monitor, which helps identify duplicates and redundant applications, schedule backups, and alert you in case your hard disk is nearing the end of its life cycle. It also deletes invalid Windows registry entries, boosts loading times, and features an app updater. A few more utilities in the performance segment include entertainment mode, battery saver, and activity manager.
Kaspersky Pros
High-level malware detection rates.
Great security features like VPN and password manager.
Minimal impact on system performance.
Kaspersky Cons
Limited customer support in some regions.
Uses more system resources than other products.
Kaspersky Pricing Plans
Kaspersky is available at a starting price of $59.99/year for 1 device.
4. Bitdefender
Best for Multi-Device Protection
Bitdefender offers malware protection for all kinds of devices without impacting performance. This tool offers threat detection technologies, multiple-layer ransomware protection, secure VPN, and advanced parental controls.
With Bitdefender antivirus services, you can protect your devices with features like real-time data protection, network threat prevention, advanced threat defense, vulnerability assessment, web attack prevention, anti-fraud, and anti-spam.
Apart from this, Bitdefender offers extra features like Bitdefender Photon, Autopilot, Bitdefender VPN, Anti-Theft Feature, Global Protective Network, and Battery Mode.
Moreover, for online privacy, you will get an anti-tracker, microphone monitor, webcam protection, Wi-Fi security advisor, social network protection, file shredder, firewall, and safe online banking.
Bitdefender Pros
Fantastic multi-device coverage.
Multi-layer ransomware protection.
Robust free version with great protection.
Bitdefender Cons
Some features are not user-friendly.
VPN access is hidden behind separate paywall.
Bitdefender Pricing Plans
Bitdefender offers a 30-day free trial. The starter plan is available at $34.99 for the first year, and protects 1 device.
5. AVG Ultimate
Best for Enhanced Internet Security and System Performance
AVG provides a free antivirus program to users on many devices and operating systems. However, with AVG Ultimate, users can access a wide range of features such as TuneUp, real-time threat detection, webcam protection, ransomware protection, an enhanced firewall, and Remote Access Shield.
AVG offers user-friendly features without compromising on performance and security. The software can optimize the device with TuneUp, clean out the junk and unnecessary files, boost the battery life, and provide an unlimited VPN with 50+ server locations.
The powerful VPN keeps your online experience private and safe and enables you to hide your IP addresses, access your favorite online content, and secure a Wi-Fi network. You can also access over 50 server locations, secured with 256-bit encryption.
Furthermore, AVG offers advanced features like automatic maintenance, startup optimizer, software updater, sensitive data shield, webcam protection, payments protection, app lock, and email protection. AVG Ultimate supports various languages in Windows, Android, and iOS, but only English is supported on Mac devices.
AVG Ultimate Pros
Tools for performance enhancement and privacy protection.
User-friendly interface.
Competitive pricing for 10-device coverage.
AVG Ultimate Cons
Malware-detection rate could be better.
Limited features in the free version.
AVG Ultimate Pricing Plans
AVG Ultimate is available at $59.88 for the first year, and covers 10 devices.
6. Webroot
Best for Fast Scan
Webroot is a reliable protection service known for its fast scans. It does a decent job of providing advanced protection against online threats like identity theft and phishing. This tool offers real-time threat intelligence, automatic protection over any network and unsecured WiFi, and advanced web filtering.
One aspect of Webroot that stands out is that it not only wipes out any malware or ransomware but also greenlights good programs installed in the system. It gives you a detailed analytic report to help you identify suspicious behavior and rectify device health within minutes. Furthermore, you get real-time cloud-based protection for your device.
Webroot SecureAnyWhere Pros
It easily fixes ransomware damage.
Feature-rich plans.
Webroot SecureAnyWhere Cons
Old and outdated interface.
The firewall settings can be confusing.
Webroot SecureAnyWhere Pricing Plans
Webroot SecureAnyWhere is available at a starting price of $24.99/year and covers 1 device.
7. Avira
Best for Privacy and Performance Optimization
Avira provides security features by detecting online threats and malware in real time, speeding up mobile phones and computers, generating and remembering passwords, and encrypting web browsing. The features include system optimization tools like PC Cleaner, unlimited VPN, identity protection, browser safety and anti-phishing, and email protection.

One of Avira’s main focuses is providing anonymity to its customers. The company offers various features to keep your online presence anonymous, such as the unlimited VPN that secures your web browsing while buying products and sharing your location or personal information. You can benefit from the PC Cleaner feature to remove junk files, speed up your device performance, and reduce lags.
A single subscription can secure up to 25 devices, including Macs, web browsers, Android, iOS, and PCs. Avira Prime will scan your system for weak passwords, malware, vulnerable networks, and outdated apps.
Avira Pros
Minimal impact on system performance.
Strong focus on privacy.
Basic plan covers up to 5 devices.
Avira Cons
Lackluster customer support.
Free version includes ads.
Avira Pricing Plans
Avira’s starter plan is available at $9.99/month and covers 5 devices.
8. Norton 360
Best for Identity Theft Protection and Secure VPN
Norton 360 includes a wide range of security tools, making it a suitable option for comprehensive protection in one tool.

The introductory plan includes antivirus, spyware and ransomware protection, cloud backup, firewall, personal password manager, VPN, privacy monitor, ID theft protection, and other tools, making it a total cybersecurity package.
Higher-tier subscriptions also provide advanced features like credit monitoring, social media monitoring, credit card and data breach alerts, and insurance policies to shield you against stolen funds.
Norton 360 Pros
Strong, comprehensive protection.
Great malware detection rate.
Light on system resources.
Norton 360 Cons
More expensive than some competitors.
No free plans provided.
Norton Pricing Plans
Norton 360’s starter plan, Deluxe, is available at $49.99 in the first year, and covers 5 devices.
9. McAfee
Best for Comprehensive Cybersecurity with Identity Monitoring
McAfee is simple to use and continuously operates in the background to monitor identity thefts. It also updates you with alerts to keep your device safe. The software provides regular updates and automated scans to ensure that all the security filters applied are on and effective against any emerging threats.
McAfee is known for its firewall protection, which helps control and monitor outgoing network traffic. It aims to safeguard personal information, such as usernames, passwords, and other sensitive details, from falling into the wrong hands.
It automatically blocks browser extensions, URLs, or downloads that may seem fishy and harmful to your system. Another underrated feature is the LiveSafe, which focuses solely on your mobile and desktop health and security.
McAfee Pros
Password manager to keep all passwords in one place.
Special tools for online protection.
A comprehensive security suite that offers a broad range of features.
McAfee Cons
Slows down device when in use.
Flags incorrectly for some files.
McAfee Pricing Plans
McAfee’s services are available at a starting price of $44.99/year, and covers unlimited devices.
10. Trend Micro Maximum Security
Best for Web Threat Protection and Fraud Prevention
With Trend Micro, you can protect up to 5 devices of any operating system, be it Mac, Chromebook, Windows, iOS, or Android. It extends its services to the latest Windows 11 and provides protection against the latest fraud, malware, and scams.
The software supports mobile phones, computers, and tablets. It shields your privacy and blocks websites that can potentially steal your personal data. It also automatically flags any scam URLs or phishing emails. An optimization feature is also provided to remove unwanted files, clear cache, and free up system memory for enhanced device performance.
Trend Micro allows you to create and manage complex passwords with their credentials on your most visited websites. It also integrates with AI to deliver an effective and smooth protection system that evolves faster than scams.
Trend Micro Pros
A diverse set of robust security features.
Parental control that helps limit content and screen time.
Multifaceted browser extension.
Trend Micro Cons
It might cause lags on your device.
Limited licensing options.
Trend Micro Pricing Plans
Trend Micro’s starting price is $49.95/year, and covers 5 devices.
11. Sophos Home
Best for Advanced Real-time Malware Protection
Sophos Home is an affordable option that provides advanced real-time malware protection. The feature-rich solution includes remote app control, threat analysis, and scanning. It provides different layers of security and fast virus scans for smooth operation.

With real-time threat protection, Sophos Home ensures immediate defense against real-time and evolving online dangers. The advanced features of Sophos Home include AI threat detection, malware scan and cleaning, ransomware security, security management, and web protection.
Many features are available for free, so you can test them before opting for the paid version.
Sophos Home Pros
The knowledge base support is available 24/7.
No email is required to sign up for the free trial.
Parental web filtering.
Sophos Home Cons
The content filter in parental controls is ineffective.
Advanced features have a steep learning curve.
Sophos Home Pricing Plans
Sophos Home offers a single plan for $44.99/year, and covers 10 devices.
12. ESET NOD32 Antivirus
Best for Multilayered Protection
ESET NOD32 primarily focuses on providing efficient malware protection and is well-regarded for its multilayered protection approach. It combines multiple security technologies to offer comprehensive protection. This includes traditional signature-based detection, cloud-based scanning, machine learning measures, Ransomware Shield, and Exploit Blocker.
Exploit Blocker, one of this tool’s main features, protects against attacks targeting web browsers and other apps. Thanks to the Real-time Antivirus, this tool can protect your device against viruses, worms, Trojans, and ransomware.
The UEFI Scanner can scan for threats hidden in the firmware. Its anti-phishing feature also protects users against fraudulent websites. Another advantage of ESET NOD32 is Cloud-powered scanning. This feature Uses LiveGrid technology, a cloud-based reputation system that improves detection capabilities.
ESET NOD32 Antivirus Pros
Excellent multilayered protection technologies.
Lightweight and efficient.
Advanced features such as UEFI scanner and exploit blocker.
ESET NOD32 Antivirus Cons
Lacks some common features, such as a VPN.
No free version.
ESET NOD32 Pricing Plans
ESET NOD32 has a starting price of $39.99/year for 1 device protection.
Comparison of Best Antivirus Software
The table below compares the best antivirus software on this list, based on factors such as Malware Detection Rate, System Performance Impact, and Security Features.
| Antivirus | Malware Detection Rate | System Performance Impact | Security Features |
|---|---|---|---|
| Avast One | 98.8% | Medium | Firewall, password manager, real-time protection, ransomware protection |
| Avira | 98.9% | Low | Password manager, parental control, anti-phishing, system optimization tools, VPN |
| Kaspersky | 91.8% | Medium | Real-time protection, anti-phishing, ransomware protection, password manager |
| Bitdefender | 96.1% | Low | Real-time protection, firewall, parental controls, password manager |
| AVG Ultimate | 98.8% | Medium | VPN, system optimization tools, webcam protection, anti-phishing |
| Malwarebytes | 95% | Low | Ransomware protection, anti-phishing, browser guard, VPN |
| Norton 360 | 98.9% | Medium | Real-time protection, firewall, VPN, password manager, ransomware protection |
| McAfee | 98.7% | Medium | Real-time protection, password manager, VPN, firewall, identity theft protection |
| Trend Micro Maximum Security | 84.5% | Medium | Anti-phishing, privacy protection, parental controls, system optimization tools |
| Sophos Home | 98% | Low | Ransomware protection, remote management, web filtering |
| Webroot SecureAnywhere | 98% | Very Low | Real-time protection, ransomware protection, identity theft protection |
| ESET NOD32 Antivirus | 96.3% | Low | Real-time protection, anti-phishing, UEFI scanner, ransomware protection |
What is Antivirus Software?
Antivirus software is a program or set of programs designed to detect and remove malicious files and programs from computers, networks, and other digital devices. Malware includes viruses, worms, Trojan horses, ransomware, spyware, adware, and other types of harmful programs that can compromise a system’s security, privacy, and functionality.
Antivirus software utilizes various detection and protection methods and technologies, including comparing the files against a database of known malware signatures, examining code behavior patterns, and monitoring programs for suspicious patterns.
Impact of Antivirus Software on System Performance
The impact of antivirus software on your system performance will differ depending on your chosen software. Moreover, it depends on the power of your system’s hardware. However, robust antivirus software usually comes with optimization tools that can minimize the impact on system performance.
Antivirus software uses system resources in 3 different ways:
- CPU: During scans and real-time protection, the software is actively monitoring files and processes that consume CPU resources and can slow down the system.
- Memory: Antivirus programs usually run background processes that consume RAM and limit the available resources for other programs.
- Disk I/O: Antivirus software reads and writes multiple files during scans, which increases disk activity and can slow down the hard drive’s performance.
As a result, when using demanding antivirus software, you may experience slowdowns in OS operations, application performance, and network performance for antivirus software, including network protection features like web shields and firewalls. Additionally, running an antivirus program increases the power consumption of your system. So, if you’re using a laptop on battery, you must charge the device more often.
However, since the long-term goal of using antivirus software is to remove malicious and unnecessary programs, the performance of your system will be optimized after the scan is completed.
Benefits of Antivirus Software
Malware protection, data privacy protection, online protection, and performance optimization are the main benefits of using antivirus software.
- Protection Against Malware: The most important reason to use an antivirus program is its protection against all kinds of malware. Antivirus software prevents malicious programs from infecting the system, which leads to data corruption, system slowdowns, unauthorized access, and more.
- Online Protection: Most modern devices are constantly connected online. Antivirus programs provide safe internet browsing with anti-phishing measures and firewalls for malicious websites.
- Data Privacy Protection: One of the goals of malicious programs is to steal private data and sensitive information, such as passwords. Antivirus programs can protect the users against these attacks. Moreover, some antivirus services offer anti-tracking software that blocks the tracking of websites’ cookies.
- Performance Optimization: Antivirus software scans the user’s system and deletes malicious programs. Most malware programs consume system resources and slow down the device. Installing a lightweight and efficient antivirus can improve your system’s performance.
Role of Antivirus Software in Modern Security
Antivirus software plays a key role in modern cybersecurity. Many companies and businesses utilize antivirus software alongside other security tools, such as firewalls and encryption technologies, to create a comprehensive defense system. Thanks to the advanced threat protection of modern antivirus software, companies can keep their data and servers safe against advanced persistent threats and zero-day exploits.
For organizations, business antivirus software offer real-time monitoring and management tools. The best antivirus programs provide cloud security and data backup solutions, which benefit all kinds of businesses. Additionally, these antivirus software are compatible with different devices and can be used on multiple systems.
Free vs. Paid Antivirus Software
Free and paid antivirus software differ in malware detection rates, ransomware protection, system optimization, customer support, and advanced features. The differences between free and paid antivirus software are detailed below.
- Malware Detection Rates: Paid antivirus provides more robust malware detection technologies. The free versions offer basic malware detection, and the rates are considerably lower than those of paid antivirus software.
- Real-time Protection: Free antivirus rarely provides real-time protection. However, real-time protection is the main draw of most paid antivirus software. With this feature, your system can detect malware before it executes and damages your system.
- Ransomware Protection: Free antivirus programs lack specific anti-ransomware features. It is advised to use a robust paid antivirus to block unauthorized encryption attempts.
- Firewall: Operating systems offer a firewall feature, such as Windows Defender Firewall. However, antivirus programs provide advanced firewalls in the paid version.
- Web Protection: Free antivirus offers limited web protection, but with most paid antivirus programs, you can access advanced anti-phishing, anti-spam, and safe browsing features.
- Parental Controls: Paid antivirus software offer parental control options and allow parents to monitor, restrict internet usage, and set time limits. This feature is rarely provided in free antivirus software.
- System Optimization Tools: Free antiviruses usually don’t offer optimization tools. Some paid options provide optimization tools, such as disk cleanup and performance-boosting features.
- VPN: A VPN service is only available in premium versions of most antivirus software. In some cases, the feature is available with unlimited data.
- Password Manager: If you want to access a full-featured password manager, opt into paid versions of the best antivirus software.
- Customer Support: Free antivirus software has an option to contact support, but users need to pay for a premium customer support experience that includes live chat, phone support, and fast response time.
- Supplemental Security: The premium versions offer additional security features, such as identity theft protection, online storage, and web monitoring.
Antivirus Security Trends for 2025
AI and Machine Learning are the main antivirus security trends for 2025, as they are beneficial in identifying patterns in malware behavior. Considering that 58% of malware attack victims are small businesses, artificial intelligence can protect many small companies that don’t have access to big security teams.
Moreover, ransomware attacks increased by 715% in 2020, leading to the rise of anti-ransomware features in antivirus software. Remote businesses have also increased since 2020. As a result, cloud-based antivirus solutions are quickly becoming the norm, as this helps businesses protect their data regardless of the location of their employees.
AI models are trained to identify different kinds of online threats and are bundled with a cloud service to protect multiple devices worldwide. This reduces the cost and workload for businesses. Larger businesses can redirect their security teams to work on more immediate projects. At the same time, smaller firms don’t have to invest in a security team, thanks to cloud-based protection through antivirus software.
OS Built-In vs. Third-Party Antivirus
The table below highlights the differences between OS built-in antivirus software and third-party antivirus software.
| Performance and Features | OS Built-In Antivirus Software | Third-Party Antivirus Software |
|---|---|---|
| Malware Detection Rates | Good rates against common threats | Superior rates against all kinds of threats |
| Ransomware Protection | Limited protection | More comprehensive protection with specialized tools |
| Web Protection | Basic URL filtering and anti-phishing measures | Advanced web protection |
| Firewall | Basic firewall without many customization options | Advanced firewall with many customization options |
| VPN | Not included | Included in premium options, unlimited usage in some software |
| Parental Controls | Not included | Advanced parental controls with monitoring features |
| Password Manager | Not included | Included in some programs with secure storage and auto-fill capability |
| Customer Support | No specialized customer support for antivirus | Live chat, phone, and email |
| System Optimization Tools | Not included | Included in many premium options, with disk cleanup and performance booster |
How Antivirus Software Protects You from Online Threats
The section below discusses multiple online threats, such as viruses and adware, and how antivirus software protects your system against them.
- Viruses: Viruses are the most well-known malware that can hurt the system. Antivirus programs have a database of known virus signatures, and after scanning files, they can find viruses and quarantine or delete them.
- Potentially Unwanted Programs: These programs bundle with other software, change browser settings, or display excessive ads. Antivirus software identifies these programs based on their patterns and asks users if they want to delete them.
- Adware: Adware is malicious software that displays unwanted ads. Antivirus software can detect and block adware during installation by identifying ad-related code.
- Spyware: Antivirus software can detect unauthorized access to webcams or microphones, sending data without the user’s consent, and keylogging.
- Trojans: Trojans are disguised as legitimate software. Antiviruses utilize heuristic analysis and behavior monitoring to detect Trojans that are trying to open the backdoor or steal data.
- Worms: Antivirus programs can detect worms through unusual network activity, such as rapid file transfers or repeated attempts to access multiple devices.
- Ransomware: Sudden encryption of large numbers of files or repeated attempts to alter file extensions are signs of ransomware. Antivirus detects signatures and analyzes the behavior of these files to safely quarantine and remove ransomware.
- Rootkits: Rootkits hide deep in the OS, but antiviruses can perform deep scans, such as scanning at boot time to detect rootkits.
- Browser Exploits: Brower extensions of antivirus software can easily detect threats in web pages by scanning scripts or analyzing unauthorized attempts to access the browser.
- Phishing Attempts: Most antivirus software scan emails, websites, and messages to find suspicious attachments or misleading URLs.
How Does an Antivirus Work?
Antivirus software utilizes multiple methods to find any kind of threat to your devices. Android antivirus software and MacOS antivirus software work differently compared to Windows antivirus because the threats are varying, and malware can hide in different directories based on the operating system.
Regardless of the operating system and brand, there are standard functionalities spanning across all antivirus software. These functionalities are listed below.
- Scanning the files and comparing them to a database of known malware signatures.
- Real-time detection for instances when a suspicious program runs in the background.
- System scans that analyze system files at boot time and after it to find different threats, such as ransomware.
- Using specialized tools such as anti-spyware software to detect certain kinds of malware in the files.
- Using website malware scanners that can detect online threats immediately and block them before they infect your device.
Frequently Asked Questions
To decide what is the best antivirus software, you need to consider the level of protection your device needs. For instance, if you are constantly browsing, the best antivirus is the one with the best web protection features. Overall, an antivirus that can quickly detect most threats and doesn’t slow down the system is considered the best option.
If you keep sensitive information on your device, it’s better to use paid antivirus services. However, if the device is not your primary system and you don’t use it for important tasks, using the best free software will suffice.
Yes, you need antivirus software even if you use a Mac or a smartphone. Various threats and malware are not exclusive to a specific OS or device. Therefore, antivirus services are available for many devices and operating systems. You should choose the best virus protection for your PC or mobile, regardless of your operating system.
No antivirus software can provide 100% protection, and there is always a chance that a malware program will damage your system and privacy. However, using the best virus protection software will drastically reduce the chances of your system getting infected.
Yes, you can use more than 1 antivirus on a single system, but it’s not recommended. This can cause unnecessary simultaneous scans that can lead to crashes. You should compare the best security software and choose one based on your system.
Antivirus services are available through different pricing plans. For the most affordable plans, choose one that is only for 1 device and has the basic features. Kaspersky, Avira, and Bitdefender are some antivirus software that offer affordable services.


