Security, Orchestration, Automation, and Response (SOAR) tools are software products that enable IT teams to define, standardize and automate the organization’s incident response activities. Most organizations use these tools to automate security operations and processes, respond to incidents, and manage vulnerabilities and threats.
Generally, the SOAR solutions enable teams to collect valuable security data, identify, analyze, and address existing and potential threats and vulnerabilities from different sources. Consequently, the tools provide more visibility that allows organizations to respond to security incidents faster, efficiently, and consistently.
An ideal SOAR tool should;
- Ingest and analyze information and alerts from various security systems.
- Have the ability to define, build and automate workflows that the teams require to identify, prioritize, investigate and respond to the security alerts.
- Orchestrate and integrate with a broad range of tools to improve operations.
- Have forensic capabilities to perform post-incident analysis and enable teams to improve their processes and prevent similar issues.
- Automates most of the security operations hence eliminating repetitive tasks and allowing teams to save time and concentrate on more complex tasks that require human input
The tools rely on artificial intelligence, machine learning, and other technologies to automate repetitive tasks such as gathering information, enriching and correlating data, and more. Such an approach helps the teams to respond to a wide range of security issues faster and at scale.
Additionally, most of the SOAR solutions have playbooks that provide instructions based on proven practices and procedures. Using the playbooks ensures consistency, compliance, faster and reliable identification, and remediation of incidents.
With so many security products in the market, we have compiled a list of some of the best SOAR solutions to help you select the right solution to address your unique needs.
Let’s explore them. 👨💻
Splunk Phantom
Splunk Phantom is a SOAR solution that integrates with a broad range of security tools to give teams better insights and the ability to detect and respond to external and internal threats. It comes with a visual playbook editor (VPE) that enables security and development teams to use the inbuilt drag and drop feature to construct comprehensive playbooks.
Key features;
- Design custom automation processes for specific workflows.
- Filter data and define custom security actions
- Enables teams to collaborate and make critical security decisions in real-time.
- A fast SOAR solution for enhancing security within your organization and quickly address incidents
- Centralized visualization
- Event per day (EPD) feature that shows the security events the tool has managed.
IBM Resilient
The IBM Resilient is a machine learning-based SOAR platform with enhanced threat detection and incident response capabilities. The SOAR solution is available for on-premise installation, as an MSSP service, or as a Security as a Service (SaaS) deployment model. It provides teams with a single platform and the ability to automate operations, add intelligence, enhance collaboration and address the threats faster and efficiently.
Key features;
- Enables teams to access detailed threat intelligence and actionable security alerts hence quickly respond and manage any incident.
- Flexible deployment, automation, and orchestration options to meet unique business needs
- Gain visibility into security incidents, understand and prioritize them, then take the appropriate remedial actions.
- Built-in cyberattacks simulation feature to test the security systems and validity of the playbooks. The feature helps the teams to perform compliance audits and addressing any issues.
- Dynamic and additive playbooks to empower teams with the relevant knowledge and guidance to resolve security incidents effectively.
Insightconnect
Rapid7 Insightconnect is a SOAR solution that integrates, streamlines, and accelerates the security processes with little or no coding. The platform connects the security tools and teams to provide complete integration and clear communication across different technologies.
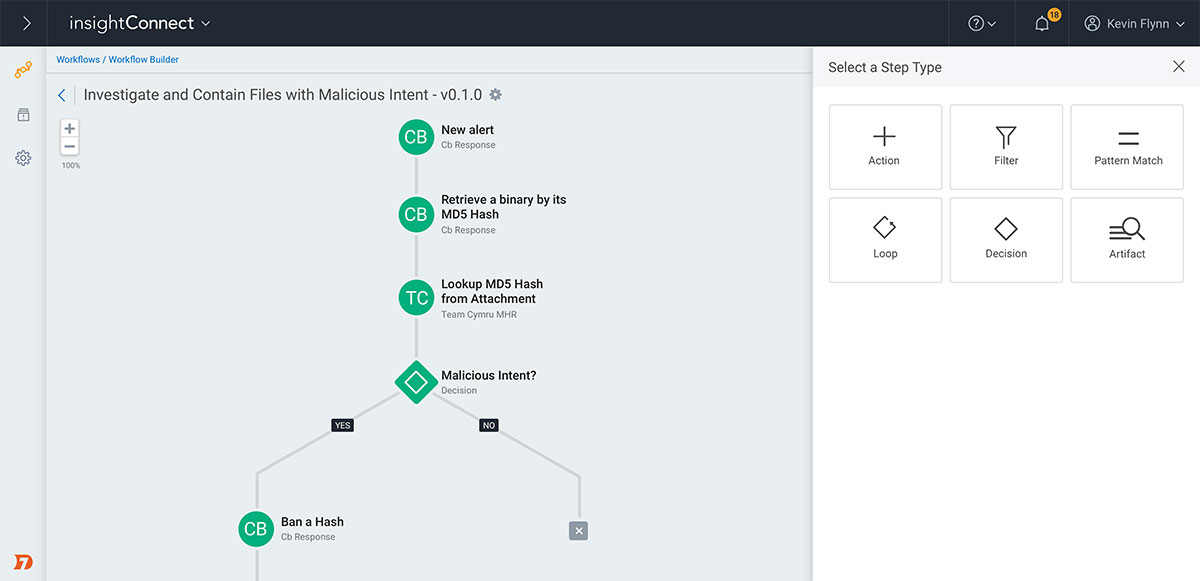
Key features;
- Detect, block, and respond to attacks, malware, phishing attacks, compromised user accounts, vulnerable network ports, etc.
- Automate the threat hunting and other processes to quickly identify malware, compromised URLs and domains, and suspicious activities.
- Automate the detection, blocking, and investigating viruses, malware and email phishing attacks, and other malicious programs
- Provides real-time visibility and ability to respond faster and smarter to security incidences
- Execute automated playbooks hence speed up the incidence response processes.
RespondX
LogRhythm RespondX is a simple SOAR solution that provides reliable real-time advanced threat detection that enables organizations to improve their security. The SmartResponse feature helps to automate the workflows and accelerate the threat investigation and response processes.
Key features;
- A comprehensive tool that supports end-to-end security incident response processes from collecting data and quarantine endpoints to blocking compromised network assets and ports.
- Automate incident response processes to efficiently mitigate all risks, identify and address the vulnerabilities to prevent similar attacks in the future.
- Track the mitigation and recovery when investigating an incident
- A user interface that can update cases to include log data, alerts, and other information.
- Automatically suspend risky or compromised user accounts, processes, and network access.
Exabeam
Exabeam incident responder is a powerful, cost-effective, fast, and security platform for detecting, investigating, and responding to security threats. The easy-to-use automated tool with a simple UI eliminates the manual investigations and mitigation tasks while providing a solution to deal with threats, distributed attacks, and more.
Key features;
- Provides a single, simple to use security management platform that does not require high levels of expertise
- Simple to use and fast data lake search
- Advanced end-to-end incident detection for both insider and external threats.
- Prebuilt, customizable, and automated incident playbooks to streamline and standardize response practices and procedures to ensure swift and repeatable, error-free actions.
- Use inbuilt tools to score an asset or user timeline and trigger an alert or require further investigation when the score reaches a specified threshold.
ServiceNow
ServiceNow Security Operations is a powerful enterprise security solution for managing incidents and vulnerabilities and enhancing security threat intelligence and configuration compliance. Generally, the SOAR tool enables you to analyze, identify, eradicate and recover from attacks and threats. As such, it provides you with a comprehensive solution to manage the full life cycle of security incidents.
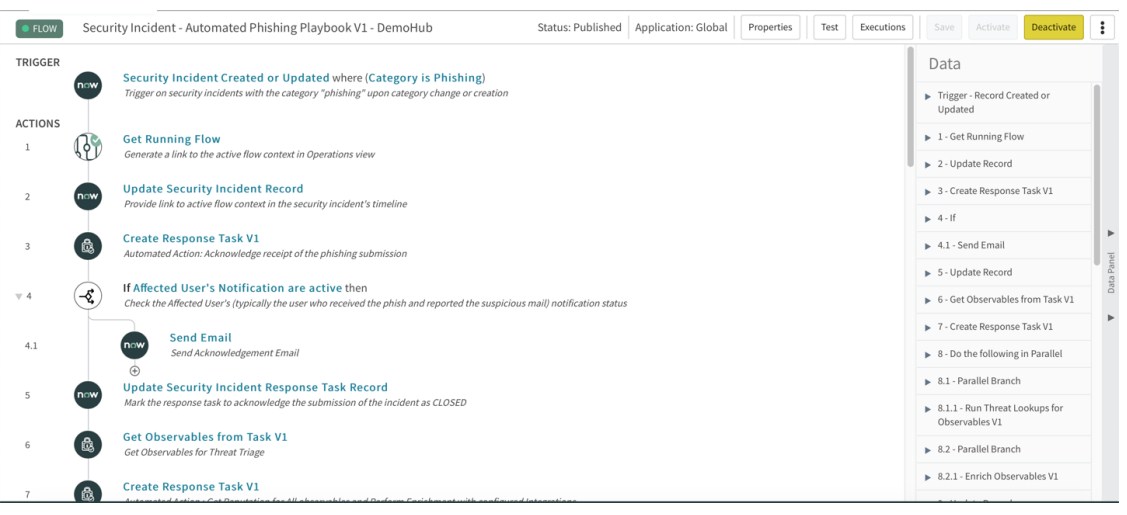
Key features;
- Automate your security tools, processes and activities, and tools
- Provides a summary of vulnerabilities, hence allowing teams to identify and address the weaknesses and prevent attacks in good time.
- Get the latest security incidents and vulnerabilities together with affected business processes.
- Identify, prioritize and respond to security incidents, vulnerabilities, misconfigured assets, and other risks much faster.
- Enables you to understand your security posture, bottlenecks, and trends through analytics-driven reports and dashboards.
Also Read: Best Web Vulnerability Scanner
SIRP
SIRP is a reliable, all-rounder SOAR solution that integrates with most out-of-box security technologies and functions to provide teams with a single point of control, automation, complete visibility, and incident management platform. The security solution collects data from several different sources across the infrastructure.
It then enriches the data with threat intelligence and analysis, after which it organizes it into vulnerabilities, incidents, and other classifications for easy understanding and response.

Key features;
- Provides valuable intelligence, enhanced visibility, and actionable security data
- Assigns security scoring to each incident, vulnerability, and alert hence enabling teams to prioritize.
- Integrates with over 70 security tools while allowing you to complete more than 350 actions from a single platform
- Provides full visibility into the security posture of the systems through an intuitive dashboard, in-depth reports, and incident audits
- A simple, drag-and-drop automated playbook helps to streamline workflows and enable efficient incident responses based on proven processes.
Conclusion
The security, orchestration, automation, and response tools help optimize vulnerability management, and threat response processes improve efficiency, reduce resolution time, and save costs.
Although there are many SOAR solutions, there is probably none that excels across all the security challenges businesses face. As such, when looking for a solution, consider the core features that are most important to your organization and choose one that best matches your requirements.


