Application attacks are increasing rapidly. In the financial industry alone, web application and API attacks have grown by approximately 65% year-over-year.[1] Organizations now face escalating threats while also needing to comply with stricter security regulations such as PCI-DSS, GDPR, and HIPAA. As a result, Web Application Firewalls (WAFs) have become an essential security tool.
WAFs protect your web applications and APIs by monitoring and filtering HTTP traffic to block attacks like SQL injection, cross-site scripting (XSS), and other OWASP Top 10 threats.[2] They use rules, machine learning, and threat intelligence to detect and mitigate malicious activities, ensuring legitimate traffic flows uninterrupted.
Here are 10 of the 18 best web application firewalls (WAFs) that I’ve researched and reviewed based on their features, pros/cons, and pricing.
- 1. Sucuri – Best for Small to Medium Business Sites
- 2. Cloudflare WAF – Best for Global Threat Intelligence with CDN Integration
- 3. Radware Cloud WAF Service – AI/ML-Powered Automation for Faster Security Deployment
- 4. SiteLock WAF – Best for Immediate Threat Mitigation
- 5. ModSecurity – Open-source WAF
- 6. Prophaze WAF – AI-powered Attack Detection Algorithms
- 7. AppTrana WAF from Indusface – Best for Risk-based Protection
- 8. AWS WAF – Best to Integrate with Applications Hosted on AWS
- 9. Akamai App & API Protector – Best for Enterprise
- 10. BIG-IP Advanced WAF from F5 – Best for Global Enterprise
- Show less
You can trust Geekflare
At Geekflare, trust and transparency are paramount. Our team of experts, with over 185 years of combined experience in business and technology, tests and reviews software, ensuring our ratings and awards are unbiased and reliable. Learn how we test.
TL;DR: Best WAFs
Here is a comparison table of the best WAFs for a quick overview. I’ve compared their starting price, key features, and deployment method.
| WAF | Key Features | Deployment | Starting Price |
|---|---|---|---|
| Sucuri | Blocks malware, DDoS, hacks, and brute force attacks, virtual patching, Malware removal by Sucuri experts. | Cloud | $9.99/month |
| Cloudflare WAF | Uptime SLA, sensitive data detection, industry-leading threat feeds, advanced rate limiting. | Cloud | Price on Request |
| Radware Cloud WAF | Auto traffic learning, application mapping, adaptive policies, auto cross-module correlation | On-prem, cloud | Price on Request |
| SiteLock WAF | Real-time traffic statistics and detailed reports, Daily scans of your code, database, and CMS, WAF reports for PCI submission, CDN. | Cloud | $24.99 per month |
| ModSecurity | Customizable rules for specific security needs, centralized logging, and pre-configured rule-set for protection against common attacks. | On-prem, Cloud | Free |
| Prophaze WAF | Behavioral analytics, machine learning for advanced threat detection and prevention. | Cloud, hybrid, on-prem, Kubernetes | Price on Request |
| AppTrana | SLA-based virtual patching, SLA guarantee for 100% availability of business-critical websites, DAST scanner and penetration testing add-on. | Cloud, on-prem | $99/month |
| AWS WAF | Account take-over fraud protection, account creation fraud prevention, Managed rules to protect your app from common threats | Cloud | Usage-based pricing |
| Akamai App & API Protector | Self-tuning capabilities, API discovery and protection, adaptive protection to mitigate evolving threats. | Cloud | Price on request |
| BIG-IP Advanced WAF | Behavioral analytics and machine learning to accurately detect layer 7 DoS attacks, API protocol security, and protection from brute force. | Cloud, hybrid, on-prem | Price on request |
1. Sucuri
Best for Small to Medium Business Sites
Sucuri is the best web application firewall option for SMBs. These businesses often operate with limited security budgets, and buying multiple security tools to protect their websites is not viable.
The solution is included in the Sucuri Website Security Platform, which offers complete website protection, though you can buy WAF separately. Sucuri claims that its WAF can improve your website speed by up to 60%.
After reviewing Sucuri’s product documentation and conducting in-depth research, I recommend choosing the Sucuri Website Security Platform over just the Sucuri WAF for comprehensive website protection.
This is because the Sucuri Website Security Platform offers a wide range of security features to protect your website, such as malware removals, frequent advanced security scans, block list monitoring/removal, and more.
Moreover, the Sucuri Website Security Platform can help you meet various PCI-DSS requirements by offering WAF and an intrusion detection system for your website.
Sucuri WAF Features
- Virtual patching/hardening to stop OSI layer attacks.
- Protection from advanced DDoS and brute force attacks.
- Load balancing feature to improve performance and availability.
- SSL support & monitoring.
- Diverse CMS & hosting compatibility.
Sucuri WAF Pros
Malware and hack removal by Sucuri experts
Advanced security scans
24/7 availability of security teams
Website uptime monitoring
Sucuri WAF Cons
No security for APIs
Customer support needs improvement
Sucuri Pricing
Sucuri WAF pricing starts at $9.99/month, and Sucuri website security platform pricing begins at $229 annually. Sucuri offers a 30-day free trial of its WAF.
2. Cloudflare WAF
Best for Global Threat Intelligence with CDN Integration
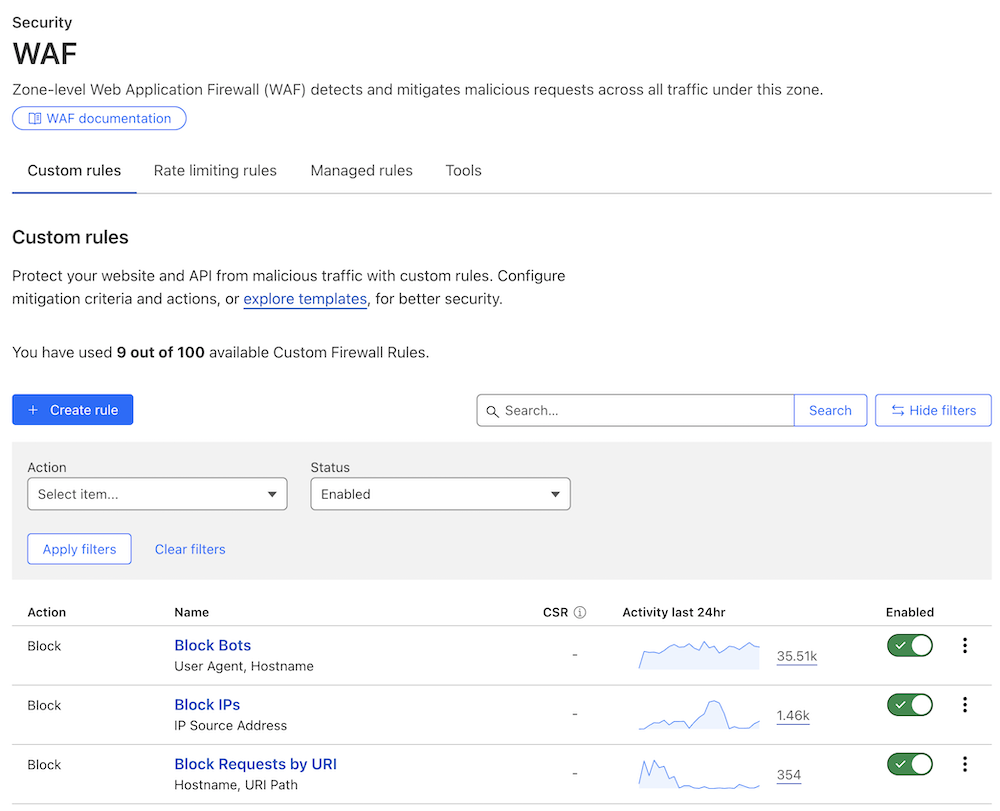
Cloudflare WAF leverages global threat intelligence and machine learning to protect your application from the latest threats, including zero-day attacks. It uses core OWASP TOP 10 rules to mitigate Layer 7 attacks, such as DDoS attacks, SQL injection attacks, cross-site scripting attacks, and more.
During my research and exploration of Cloudflare WAF, I noticed that the Cloudflare global network processes 93 million HTTP requests/second at peak. Thus, it offers best-in-class threat intelligence.
Cloudflare WAF scans your content as it’s uploaded to your application to find and block malware. Its machine learning-based detection can automatically detect and block emerging threats.
A user also highlighted its machine-learning capabilities on Reddit.
It can help your businesses meet certain PCI-DSS requirements, such as using a firewall or implementing the latest encryption.
Features of Cloudflare WAF
- Unmetered DDoS protection.
- Accelerated mobile pages.
- Bot blocking.
- Uptime SLA.
- Custom rule creation.
Note: The availability of the above features can vary based on your subscription plan.
Cloudflare WAF Pros
Advanced rate limiting
Sensitive data detection
Exposed credential checks
Best-in-class threat intelligence feed
Cloudflare WAF Cons
Occasional false negative
Costlier than other WAFs
Cloudflare WAF Pricing
Cloudflare WAF has custom pricing options. You’ll have to contact their sales team for a personalized quote based on your requirements.
Expert feedback on Cloudflare

Chandan Kumar
We at Geekflare have used Cloudflare since 2015 and are happy with the overall results. I like how everything works, and they are always innovative in implementing new security and performance features.
-
What do you dislike about Cloudflare?
It is not the product but customer support. When we migrated to Enterprise plan, had to follow up many times. Recently, we had another minor thing and had to chase their support many times.
3. Radware Cloud WAF Service
AI/ML-Powered Automation for Faster Security Deployment
Radware Cloud WAF Service offers advanced web application and API protection. Built on machine learning, it combines positive and negative security models to protect against OWASP Top 10 threats, zero-day attacks, and API abuse. It is a part of reputable Radware Cloud Application Protection services.
I have thoroughly checked its product documentation and third-party online reviews and found its adaptive AI-powered web application protection quite impressive. It can protect your web application from OWASP TOP 10 attacks and zero-day attacks.
Also, it automatically learns application behavior and continuously fine-tunes security policies for optimal protection.
Nishan on G2 also shared my view.
The auto policy generation and behavioral learning make it easy to maintain strong security with minimal manual tuning. I also appreciate the integrated bot management and DDoS protection, which provide a complete solution in one platform, along with clear dashboards that give great visibility into attacks and traffic patterns.
I like the fact that it leverages a global network of WAF points of presence (PoPs), so you can connect to a server closer to your location for low latency.
With PCI DSS, HIPAA, and multiple ISO certifications, Radware Cloud WAF stands out for compliance and reliability. This makes it an ideal solution for enterprises seeking robust, cloud-based application security with minimal operational overhead.
Features of Radware Cloud WAF Service
- Auto traffic learning to detect normal behavior and block malicious activity
- Application mapping to identify code changes and vulnerabilities
- Adaptive policies for maximum security and reduced false positives
- Managed service with expert emergency response
- Automated analytics to simplify security management
Pros
Automatically generates security policies to protect new applications
Fully complies with PCI standards
Integrates with Radware bot management to block advanced bots
Boosts performance with advanced load balancing
Cons
Some reviewers noticed slight latency during high traffic, which is normal for WAFs and shows it’s actively protecting.
It can feel complex for non-tech users at first, but Radware’s strong support helps you get started easily.
Pricing
Radware Cloud WAF pricing is not listed on its website. You need to contact the company to get pricing details.
4. SiteLock WAF
Best for Immediate Threat Mitigation
SiteLock WAF automatically protects your website from OWASP Top 10 attacks and various other cyber threats. It scans your code, database, and CMS daily to find vulnerabilities. If it detects any issues, it automatically patches them. Your website is also protected from malicious bots and backdoors.
The platform lets you customize firewall configurations to fine-tune your website traffic. You also get weekly reports highlighting usage and performance patterns and attacks blocked.
Its TrueShield Content Delivery Network (CDN) analyzes real traffic trends, website content, and usage patterns to identify content suitable for caching. Once identified, this content is duplicated, stored, and reused, reducing the need for repeated server requests. As a result, it boosts your website performance.
In my research, I have found that it offers a WAF activity report for PCI submissions. I like the fact that it provides the SiteLock Trust Seal that you can display on your website, stating that your website is secure and malware-free. This can help you build trust among website visitors.
Based on your plan, you will also get daily backups of your website.
SiteLock WAF Features
- Bot mitigation to block bad bots.
- Real-time traffic statistics and detailed reports.
- Premium content delivery network (CDN) to enhance website speed.
- Advanced caching for static and dynamic content.
- Search engine blacklisting prevention.
- Report on site health status.
Note: These features can vary based on your subscription plan.
SiteLock WAF Pros
Daily scans of your code, database, and CMS
Provides website backup
WAF reports for PCI submission
SiteLock Trust Seal to build trust among visitors
SiteLock WAF Cons
Expensive for small business owners
Lacks machine learning capabilities to block emerging attacks
No website uptime monitoring
SiteLock WAF Pricing
SiteLock WAF pricing starts at $24.99/month for a 12-month contract. It offers a risk-free 30-day refund policy. If you’re unsatisfied with the product, you can apply for a refund within 30 days.
5. ModSecurity
Open-source WAF
ModSecurity offers one of the most popular open-source WAFs. You can install it on Nginx, apache, or IIS web servers. It provides a continuous passive security assessment of your application by monitoring its internal aspects.
The platform is a classic web application firewall that offers decent coverage against OWASP Top 10. However, it lacks advanced features such as CDN, managed services, and DDoS protection.
Also, it is not an easy-to-implement solution like Sucuri or Cloudflare WAF. So, I wouldn’t consider it suitable for small business owners. To use ModSecurity, you need to be a cybersecurity expert or have a good knowledge of IT.
ModSecurity is under OWASP’s custodianship.
ModSecurity WAF Features
- Real-time application security monitoring and access control.
- HTTP traffic monitoring and real-time analysis.
- Customizable rules for specific security needs.
- Centralized logging with tools like mlogc and Syslog compatibility.
- ModSecurity Core Rule Set (CRS) for standard protection against vulnerabilities.
ModSecurity Pros
Open-source project
Extensive community support
Widely deployed firewall engine
ModSecurity Cons
Not a beginner-friendly solution
Lacks CDN, malware scanning, and compliance support
ModSecurity Pricing
ModSecurity is free to use. You can download it from GitHub.
6. Prophaze WAF
AI-powered Attack Detection Algorithms
Prophaze WAF leverages multiple attack detection algorithms with AI to detect malicious traffic. It can enhance the security of web apps, backend APIs, serverless and service meshes. In addition to OWASP Top 10, it can block bot and DDoS attacks.
It allows you to tailor rules to safeguard your web assets based on your specific security requirements. In my research, I noticed that its Health Check Monitoring feature oversees backend services, helping detect issues early before they escalate.
Prophaze WAF comes with a fast, secure CDN to improve your website speed, and it can be integrated with all popular CMS.
The platform is well-suited for eCommerce, healthcare, education, and financial services. By offering protection to your API and web application, it can help you meet various compliance requirements, such as GDPR, HIPAA, CCPA, PCI-DSS and SOC2.
Prophaze WAF Features
- Uses behavioral analytics to monitor and analyze user behavior.
- Machine learning for advanced threat detection and prevention.
- Distributed Denial-of-service (DDoS) protection to prevent service disruption.
- Offers virtual patching for vulnerabilities.
- Blocks new malware variants and malicious requests.
Prophaze WAF Pros
Fast deployment in just six clicks
24/7/365 support
Free SSL Certificate
Multiple deployment options
Prophaze WAF Cons
Lacks website uptime monitoring
No uptime SLA
No malware removal service
Prophaze WAF Pricing
Prophaze’s website has not published pricing information. You need to contact the company for the pricing details. It offers a 14-day free trial.
7. AppTrana WAF from Indusface
Best for Risk-based Protection
AppTrana from Indusface is an excellent choice for a WAF offering risk-based protection. With its managed, unlimited security scanning and expert pen-testing add-on, AppTrana identifies and resolves critical vulnerabilities before hackers exploit them.
In his review on G2, Dileep D. also highlighted its pen-testing feature.
Extremely satisfied with the VAPT testing services provided by Indusface. The team was always accessible via whats app and MS teams for addressing the queries and offering assistance.
It operates as a 24/7 SOC, capable of testing false positives, monitoring latency, fine-tuning WAF rules, and protecting against bot and DDoS attacks, among other functions.
I also observed that it virtually patches all vulnerabilities autonomously within 72 hours and provides a clean, zero-vulnerability report. It can help you meet application security audit requirements for PCI, HIPAA, SOC2, and more.
Moreover, it offers client-side protection against supply chain attacks, such as form jacking, skimming, and Magecart.
As it is hosted on the cloud, AppTrana WAF supports various combinations of deployments, including on-premises, public cloud, private cloud, and custom port applications.
AppTrana WAF Features
- Day zero protection with a guided onboarding process.
- SLA-based virtual patching.
- SLA guarantee ensures 100% availability of business-critical websites.
- Origin server protection defends servers from direct-to-origin DDoS, bot, and vulnerability attacks.
- DAST scanner and penetration testing add-on offer risk-based protection.
AppTrana WAF Pros
Zero false positives
Pentesting by experts add-on
Expertly written custom rules
SwyftComply to meet compliance requirements
AppTrana Cons
High cost as compared to other WAFs
User interface can be confusing for beginners
The starting plan lacks key features like SIEM integration and false positive monitoring
AppTrana WAF Pricing
AppTrana WAF pricing starts at $99/app/month. It offers a free 14-day trial.
8. AWS WAF
Best to Integrate with Applications Hosted on AWS
Amazon Web Services WAF lets you monitor your web traffic with precise control over how metrics are generated, collected, and analyzed. You can easily monitor, block, and rate-limit bots. With its managed rules, you can save tons of time through the quick implementation of pre-configured security measures.
It’s the best WAF to be integrated with apps hosted on AWS because it offers seamless compatibility and scalability tailored to the AWS ecosystem.
In my research, I noted that you can configure rules to filter web traffic based on HTTP headers and body, IP addresses, or custom URLs.
It allows you to create firewall rules for blocking SQL injection, cross-site scripting, and other types of cyberattacks. And the best thing is it lets you create a centralized set of rules that you can deploy across multiple websites.
AWS WAF gives real-time metrics, including details about IP addresses, URLs, geo locations, user-agent and referrers.
AWS WAF Features
- Web traffic filtering.
- Bot control to block, or rate-limit, pervasive bots.
- Account take-over fraud protection.
- Account creation fraud prevention.
AWS WAF Pros
Custom security rules to control bot traffic
Easy integration with apps hosted on AWS
Managed rules to protect your app from common threats
Advanced fraud prevention features
AWS WAF Cons
Costly bot protection
No virtual patching
Steep learning curve and only ideal for those with technical expertise in the AWS ecosystem
AWS WAF Pricing
AWS WAF pricing depends on the number of web access control lists (ACLs), rules per ACL, and web requests, with no upfront commitments. It offers a free trial.
9. Akamai App & API Protector
Best for Enterprise
Akamai App & API Protector offers web application firewall, API security, bot mitigation, and DDoS protection in a single solution. It evolves with your threat landscape and offers reliable attack detection and protection from sophisticated attacks, such as injection attacks, botnets, and various other application and API threats.
Its comprehensive protection for websites, applications, and APIs, with tailored defenses against the latest threats, makes it the ideal WAF choice for enterprises.
I like its ability to automate updates and self-tune using machine learning to improve security. You can easily deploy it in your CI/CD pipeline to ensure security throughout the software development lifecycle. DevOps integration is possible through various options, such as GUI, its Terraform provider, APIs, and the Akamai CLI.
I also found the onboarding easy. You can apply security configurations to your new applications and APIs without much hassle, and it sends you real-time alerts.
You can quickly integrate it with leading SIEM solutions to investigate security vulnerabilities and triage attacks. It also supports access controls for advanced AppSec management.
Akamai App & API Protector Features
- Automatic updates protect apps and APIs from the latest threats.
- API discovery and protection manage risks from new and unknown APIs.
- Self-tuning capabilities eliminate the need for manual configurations.
- DDoS protection blocks network attacks at the edge.
- Learning attack patterns by using both local and global data to make customer-specific protection adjustments.
Akamai App & API Protector Pros
Requires less manual intervention
Adaptable protection to mitigate evolving threats
Easy deployment in CI/CD pipeline
Akamai App & API Protector Cons
Occasional false positives
No VAPT for compliance support
Akamai App & API Protector Pricing
Akamai doesn’t provide any pricing information for App & API Protector on its website. You need to contact the company to get pricing details. It offers a 30-day free trial.
10. BIG-IP Advanced WAF from F5
Best for Global Enterprise
BIG-IP Advanced WAF combines machine learning, threat intelligence, and deep application expertise to protect your apps, APIs, and data from various attacks. These include app-layer DoS attacks, threat application takeover, threat campaigns, bots, OWASP Top 10, and zero-day vulnerabilities.
I noticed that it leverages behavioral analytics and machine learning to accurately detect layer 7 DoS attacks and successfully mitigate them. I also liked its ability to encrypt data at the application layer to protect against data-extracting malware and man-in-the-browser attacks.
With BIG-IP Advanced WAF, you can amp up API protocol security by deploying tools to secure GWT APIs, GraphQL, XML, and REST/JSON.
It offers flexible deployments, letting you deploy it on leading private cloud, public cloud, and high-performance hardware. Its built-in security protection, logging, and reporting can help your organization comply with leading compliances, including PCI DSS, HIPAA, SOX, and more.
BIG-IP Advanced WAF Features
- Enables declarative API-based deployment and configuration to deliver security as “code”.
- Defends critical applications from major security risks, including OWASP Top 10 vulnerabilities.
- Protects against brute-force attacks leveraging stolen credentials.
- Shields applications from automated bot attacks and malicious tools.
BIG-IP Advanced WAF Pros
API protocol security
CI/CD integration
Works seamlessly with other F5 services
Variety of deployment options, including on-premises, cloud, and hybrid settings
BIG-IP Advanced WAF Cons
Not a beginner-friendly solution
Prone to false positives
BIG-IP Advanced WAF Pricing
BIG-IP Advanced WAF pricing information is not available on the F5 website. You need to contact the sales team to get a pricing quote. The company offers a 30-day free trial.
More WAF Options for You
In addition to the above-mentioned WAFs, I’ve also listed more web application firewall options for you to take a look.
| WAF | Ideal for |
|---|---|
| 11. Fastly WAF | Medium to Large Organization |
| 12. Imperva WAF | Global Threat Intelligence Management |
| 13. Fortinet FortiWeb | Machine Learning Threat Detection |
| 14. Reblaze WAF | AI-Powered Bot Protection |
| 15. Wallarm WAAP | 24/7 Vulnerabilities Monitoring |
| 16. Radware AppWall | Unique Auto Policy Generation Technology |
| 17. Aikido Zen | Privacy-focused WAF Solution for Developers |
| 18. Barracuda WAF | Mid-Sized Organizations |
What Is Web Application Firewall Software?
Web application firewall (WAF) software protects your application, website, or API by filtering, monitoring, and blocking malicious traffic and application layer (OSI Layer 7) attacks, such as XSS, DDoS, SQLi, cross-site forgery, and others listed in OWASP Top 10.
The main functions of a web application firewall include but are not limited to:
- Monitoring and filtering incoming and outgoing application traffic.
- Blocking unauthorized access based on predefined security rules.
- Protecting against malware and viruses by inspecting traffic.
- Preventing data breaches by controlling access to sensitive resources.
- Managing and limiting network traffic to prevent application layer attacks.
A web application firewall sits in front of a website or application. It analyzes the traffic pattern and applies predefined security rules to allow or block web traffic. If it finds malicious traffic, it blocks it, protecting your website or application from application layer attacks.
You’ll also find web application firewalls with advanced features such as CDN, uptime monitoring, virtual patching, and compliance support.
I recommend exploring the WAFs mentioned on this list to find a solution that aligns with your requirements.
4 Benefits of Using Web Application Firewall (WAF) Software
WAFs protect your website or application from various Layer 7 and OWASP Top 10 attacks. They are a must-have security solution to improve website, application, and API security.
Below, I’ve highlighted 4 major benefits of using WAF software.
1. Enhanced Security
A web application firewall acts as a protective barrier between your website, application, or API and potential threats. It blocks malicious traffic and various application layer attacks, such as XSS, SQLi, and more.
2. DDoS Attack Mitigation
In a DDoS attack, a malicious actor tries to overwhelm your website, application, or API by flooding it with massive traffic generated from a network of compromised computers.
A WAF offers protection from DDoS attacks. It can identify and block unusual traffic, enforce limits on the number of requests made by an IP within a specific timeframe, detect and block bots, and restrict access to regions known to launch these attacks. It also notifies you in real-time about these attacks so that you can take proactive mitigation measures.
3. Zero-day Attack Prevention
Managed web application firewalls continuously update rules to protect against zero-day vulnerabilities and exploits before patches/updates are available, offering zero-day attack prevention.
4. Integration and Scalability
You can integrate a WAF with public and private clouds, CDNs (many WAFs even include built-in CDN services), APIs, on-prem applications, CI/CD pipelines, SIEM tools, web application vulnerability scanners, and more.
With flexible deployments and the ability to support new apps, APIs, and services, WAFs enable you to scale operations quickly as your security needs change.
Use Cases for Web Application Firewalls
Different industries rely on web applications for various purposes. Here are some common use cases across different industries.
E-commerce
E-commerce platforms process sensitive customer data, such as credit card details and customers’ addresses, making them a lucrative target for hackers.
WAFs can help e-commerce business owners prevent hackers from accessing customer information by blocking malicious attacks. They also aid E-commerce business owners in meeting PCI DSS and other regulatory compliances.
Financial Services
WAFs secure online transactions and protect sensitive financial data. By detecting and blocking unauthorized access attempts, they help organizations comply with strict regulations such as GDPR, SOX, and PCI DSS.
WAFs also mitigate risks from DDoS attacks, ensuring continuous availability of banking and financial services.
Healthcare
WAFs protect sensitive information, including medical records and insurance details, from cyber threats. They also support health organizations in meeting compliance with HIPAA and other regulations and maintaining data integrity.
SaaS Applications
Web Application Firewalls (WAFs) prevent downtime for cloud-based applications by detecting and blocking threats like DDoS attacks, API abuse, and malicious bots. They use real-time threat detection and behavioral analytics to filter out harmful traffic while allowing legitimate requests, ensuring continuous availability.
What’s Next
After learning about the best web application firewalls (WAFs), I suggest you take as many trials and demos as possible to find the right WAF to address your security requirements.
You can also check out the following posts to learn more about security solutions.


