Web vulnerability scanner identifies security vulnerabilities in web applications, including SQL injection, cross-site scripting (XSS), cross-site request forgery (CSRF), compliance gaps, configuration flaws, and many more.
Organizations of all sizes can use web vulnerability scanners to identify and mitigate potential threats in their web applications, enhancing their security posture.
Undetected vulnerabilities, if exploited by hackers, can compromise your application’s security, exposing your data, systems, and network to severe risks. So, proactively identifying and resolving these issues using a web vulnerability scanner can strengthen your application security and safeguard your most critical assets.
Geekflare has researched and compiled the best web application vulnerability scanners based on key features such as detection accuracy, scanning speed, ease of integration, customization options, reporting, and compliance checks.
- 1. Intruder – Best for Small to Medium Businesses
- 2. Acunetix – Best for Deep Scanning Capabilities
- 3. HostedScan – Best for Automated, Continuous Scanning
- 4. ManageEngine Vulnerability Manager Plus – Best for Built-in Remediation Flow
- 5. Burp Scanner – Popular Among Security Professionals
- 6. Tenable Web App Scanning – Simple and Scalable
- 7. Qualys WAS – Best for Integrating With Existing Qualys Products
- 8. Nikto – Best for Open-Source Needs
- 9. Invicti – Best for Enterprise
- 10. Detectify – Best for Simulating Hacker-like Attacks
- 11. Hacker Target – Hosted Open Source Vulnerability Scanners
- 12. Indusface WAS – Managed DAST Platform
- 13. Astra Pentest – Best to Perform Automated Pentest
- 14. Pentest Tools – Easy to Use
- 15. Google Web Security Scanner – Best to Scan App Hosted on GCP
- Show less
You can trust Geekflare
Imagine the satisfaction of finding just what you needed. We understand that feeling, too, so we go to great lengths to evaluate freemium, subscribe to the premium plan if required, have a cup of coffee, and test the products to provide unbiased reviews! While we may earn affiliate commissions, our primary focus remains steadfast: delivering unbiased editorial insights, and in-depth reviews. See how we test.
1. Intruder
Best for Small to Medium Businesses
Intruder is a robust web application vulnerability scanner that identifies and remedies vulnerabilities in web applications and their supporting infrastructure. It also offers manual testing of your web application for critical vulnerabilities that automated scans might miss.
Intruder can detect various vulnerabilities, including SQL injection, cross-site scripting, server-side code injection, and buffer and integer overflows. It offers integrations with Amazon Web Services (AWS), Zapier, and Slack to streamline your workflow.
Depending on your license type, the Intruder employs scanning engines such as OpenVAS, Tenable Nessus, and Nuclei. Its dynamic application security testing (DAST) scanner is powered by Zed Attack Proxy ( ZAP), an open-source web application security scanner.

Intruder Features
- Automate external vulnerability scanning to identify web-layer security issues and over 140,000 infrastructure weaknesses, including remote code execution flaws.
- Deploy an agent-based internal scanner that supports Windows, Linux, and macOS.
- Integrate easily with AWS, Azure, Cloudflare, and Google Cloud Platform (GCP).
- Generate audit-ready reports that are easy to share with customers, stakeholders, and auditors with a single click.
- Gain complete security posture visibility through reports with quick tips to improve your cyber hygiene score.
Intruder Pricing
Intruder offers three subscription plans: Essential, Pro, and Premium, with pricing based on the number of application and infrastructure licenses you choose. All plans include a 14-day free trial.
2. Acunetix
Best for Deep Scanning Capabilities
Acunetix is an automated vulnerability scanner that scans web applications accessible for over 7,000 vulnerabilities, including SQL injections, XSS, misconfigurations, out-of-band vulnerabilities, OWASP Top 10, exposed databases, and more.
Acunetix offers API security, enabling you to identify and remediate API vulnerabilities. It features DeepScan technology for scanning malicious URLs, testing popular CMSs like WordPress and Drupal, and analyzing web services, including simple object access protocol (SOAP).
Acunetix combines scan results from DAST and Interactive Application Security Testing (IAST) for better coverage. You can open vulnerabilities as issues directly in GitHub, JIRA, or Microsoft Team Foundation Server (TFS) within the Acunetix interface, and it also allows you to verify fixes.

Acunetix Features
- Customizable scans to include and exclude specific areas of your web application.
- Generate compliance reports like PCI DSS, OWASP Top 10, HIPAA, and ISO 27001 to meet regulatory requirements.
- Analyze vulnerabilities in detail, including their impact, fixes, and related classifications (CWE, CVE, CVSSv3).
- Utilize AcuSensor for complete backend visibility and minimize false positives and false negatives.
Acunetix Pricing
Acunetix offers pricing on request. You can schedule a free demo to understand the product better.
3. HostedScan
Best for Automated, Continuous Scanning
HostedScan is an automated web vulnerability scanner that employs multiple scanners to detect a wide range of vulnerabilities. It conducts internal scanning from inside a local area network (LAN) or other private networks and external scanning from outside your network over the public Internet.
HostedScan can detect misconfigurations, WordPress and plug-in vulnerabilities, front-end and API vulnerabilities, vulnerable javascript libraries, bad certificates, XSS and other OWASP top 10 risks, and more. It is a cloud-based suite of scanners that doesn’t require local resources.
HostedScan offers a comprehensive suite of tools (which I discuss in detail in my HostedScan review), including the OpenVAS vulnerability scanner, Nmap port scanner, OWASP ZAP scanner, and SSLyze scanner. These tools enable the detection of vulnerabilities across servers, networks, web applications, and encryption protocols.

HostedScan Features
- Deliver quality scans with 100% open-source capabilities.
- Schedule scans easily for one-time, daily, weekly, or monthly execution.
- Categorize scan results by risk levels (high, medium, and low) for easy analysis.
- Generate audit-ready reports for SOC 2 and ISO27001 compliance.
HostedScan Pricing
HostedScan’s free plan includes all scan types for up to three targets. The Basic plan offers unlimited re-scans and scheduling at $39/month, while the Premium plan adds API access and integrations at $109/month. Annual plans save 25%, and all plans come with a 30-day refund guarantee.
4. ManageEngine Vulnerability Manager Plus
Best for Built-in Remediation Flow
ManageEngine Vulnerability Manager Plus helps you identify a range of vulnerabilities in your web infrastructure. This includes OS vulnerabilities, zero-day vulnerabilities, security misconfiguration, high-risk software, web-server misconfiguration, third-party vulnerabilities, and more.
Not only does Vulnerability Manager Plus help you detect vulnerabilities, but it also prioritizes them based on severity, exploitability, and the availability of fixes. As a result, you can plan remediation efforts strategically to fix severe issues first.
I like Vulnerability Manager Plus because of its built-in remediation workflow. You can leverage its 75+ CIS benchmarks to detect violations and get detailed insights on how to mitigate them.
It monitors your web servers and provides detailed information on server misconfigurations, including cause, impact, and remediation for each misconfiguration.
Plus, Vulnerability Manager Plus lets you optimize systems’ security in your organization by enforcing measures like strong passwords, memory protection, and the least privileges.
You can deploy ready-to-use, tested scripts to protect your network from zero-day vulnerabilities without waiting for official patches. The tools also identifies and patches network devices.
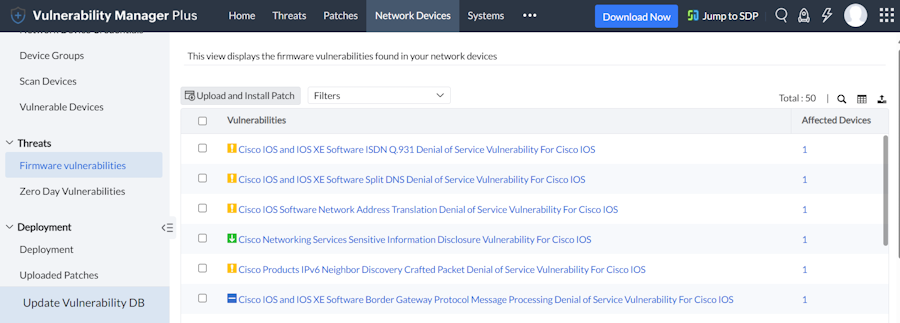
Vulnerability Manager Plus Features
- Vulnerability assessment and prioritization based on exploitability, severity, age, affected systems, and the availability of fixes.
- Compliance with 75+ CIS benchmarks by auditing systems, detecting violations, and providing remediation insights.
- Automation of patch deployment for Windows, Mac, Linux, and 500+ third-party applications at no extra cost.
- Enforcement of security best practices, including complex passwords, least privileges, and memory protection.
- Detection and remediation of web server vulnerabilities.
Vulnerability Manager Plus Pricing
ManageEngine Vulnerability Manager Plus offers three paid plans—Professional, Enterprise, and Custom.
The site doesn’t provide pricing details for the Professional plan. The Enterprise plan starts at US$1,195 per year for up to 100 workstations and a single-user license, while the perpetual license for the same requirement costs US$2,987, plus an annual maintenance and support fee of US$598. For a custom quote based on your requirements, you’ll have to contact the company.
The company offers a free personalized and online demo to help users explore the features of Vulnerability Manager Plus.
5. Burp Scanner
Popular Among Security Professionals
Burp Suite’s web vulnerability scanner is a powerful tool that can scan your web application for a wide range of vulnerabilities, including the OWASP Top 10, HTTP Desync attacks, blind server-side request forgery (SSRF), directory reversal, zero-day vulnerabilities, and more.
Burp Scanner provides DAST web application scanning with scalable, recurring, and easy-to-configure scans. It simplifies security management with bulk actions, such as launching quick scans. Its browser-powered scanner easily tests complex single-page applications (SPAs). Authenticated scanning tests are used to identify privileged areas of your target application.
Burp Scanner is available in three versions: Burp Enterprise, Burp Professional, and Burp Community Editions. It supports flexible setup options, including on-premise, Kubernetes deployment, and cloud-based instances.

Burp Scanner Features
- Option to add automated out-of-band application security testing (OAST) to dynamic scan for scanning vulnerabilities with high accuracy.
- Utilize out-of-the-box configurations with preset modes like Deep or Lightweight to save time.
- Graphical dashboards and comprehensive reporting, including scan history, remediation advice, and compliance checks for PCI DSS and OWASP Top 10.
- Easy integration with CI/CD platforms to see vulnerabilities in your development environment.
- Easy issue tracking platforms integration with Jira, GitLab, and Trello to help you track issues.
Burp Scanner Pricing
Burp Enterprise Edition offers custom pricing, while the Burp Professional Edition is available for $449 per user annually. The Burp Community Edition is free, and Burp Scanner provides a full-featured trial for feature evaluation.
6. Tenable Web App Scanning
Simple and Scalable
Tenable Web App Scanning, part of the AI-powered Tenable One product suite, is a DAST tool designed to scan your application for OWASP Top 10 vulnerabilities, including SQL injection and XSS in custom code and outdated third-party components.
Tenable Web App Scanning offers scalable deployment options, including SaaS-based scanning for modern web applications, on-premises deployment via the Security Center, and seamless integration with CI/CD environments. It also allows you to schedule automated scans weekly or monthly for all your applications.
Tenable constantly updates its vulnerability database to add new detection for custom code vulnerability detection and third-party components on your web application.

Tenable Web App Scanning Features
- Offers personalized dashboards and widget visualizations to combine IT, cloud, and web application vulnerability data into a single, cohesive view.
- Detect various cyber hygiene issues with predefined scan templates, including soon-to-expire SSL/TLS certificates and server-side misconfigurations.
- Enable administrators to create user groups and assign permissions to launch and view scans with role-based access control.
- Scan modern web applications, including single-page applications, effectively.
- Customized scanning reports and pre-configured executive-level reports to keep business stakeholders informed.
Tenable Web App Scanning
Tenable Web App Scanning costs US$7,434. A free trial is also available to assess its features.
7. Qualys WAS
Best for Integrating With Existing Qualys Products
Qualys Web Application Scanning (WAS) is an industry-leading cloud-based web vulnerability scanner that offers AI-powered scanning to detect various vulnerabilities, including OWASP Top 10, OWASP API Top 10, compliance issues, and more.
Qualys is powered by the Enterprise TruRisk™️ Platform, which helps you get an infield view of your cyber risk posture. It allows you to scan web apps and APIs across all environments, including on-premises, multi-cloud, API gateways, and containers.
Qualys has an easy-to-use dashboard that gives you complete visibility of scans and reports, simplifies vulnerability management, centralizes remediation, and allows you to customize reports for different audiences. It offers comprehensive scanning and monitoring to detect and manage PII vulnerabilities, ensuring compliance with GDPR, HIPAA, PCI DSS, and other regulations.
Qualys efficiently discovers and catalogs all web applications across the network, scaling from a few to thousands, with tagging for organized reporting and access control. It offers deep API scanning to identify vulnerabilities in Representational State Transfer (REST) and Simple Object Access Protocol (SOAP) APIs.

Qualys WAS Features
- Consolidate vulnerabilities from automated Qualys WAS scans and third-party manual penetration testing tools like Burp.
- Utilize AI-assisted clustering to scan critical areas in large applications for better detection rates and time-saving.
- Deploy XSS power mode to scan deeply and detect XSS vulnerabilities.
- Apply Path Fuzzing Rules to improve scan accuracy by allowing specific URL path components to be ignored.
- Detect malware threats, including zero-day attacks, with behavioral analysis and deep learning.
Qualys WAS Pricing
Qualys offers custom pricing, which depends on the number of IPs, web applications, and user licenses. Its features can be examined during a free 30-day trial.
8. Nikto
Best for Open-Source Needs
Nikto is an open-source web vulnerability scanner that scans web servers for multiple vulnerabilities, including potentially dangerous files/programs, outdated servers, and more. It is frequently updated to include the latest known vulnerabilities.
Nikto can scan various web servers, including Nginx, Apache, Litespeed, and more. It effectively reduces false positives by analyzing headers, page content, and content hashing.
Moreover, Nikto allows you to adjust scan settings to include or exclude entire classes of vulnerability checks. It saves reports in various formats, including plain text, SQL, HTML, XML, JSON, NBE, or CSV.
You can install the Nikto vulnerability scanner on both Windows and Linux systems. On Linux, it’s easily installable via package managers like apt or yum, and it’s also available on GitHub for direct installation or running from the source.

Nikto Features
- Check 7,000 potentially dangerous files/programs, over 1,250 outdated server versions, and over 270 version-specific problems.
- Test for configuration-related issues, such as open index directories.
- Analyze multiple ports on a server.
- Identify installed software via headers, favicons, and files.
Nikto Pricing
Nikto is a free-to-use, open-source vulnerability scanner.
9. Invicti
Best for Enterprise
Invicti offers a robust web application security scanner powered by Proof-Based Scanning™, significantly reducing false positives and eliminating manual verification. It utilizes a unique DAST + IAST approach to thoroughly scan websites, applications, and APIs for enhanced visibility and deeper analysis.
Invicti can detect thousands of vulnerabilities, including SQL injection, XSS, out-of-band vulnerabilities, server-side request forgery, and many more. Additionally, it provides a color-coded view of each app’s vulnerabilities, allowing you to easily track your progress and see how effectively you’re resolving issues.
Invicti can run tests simultaneously across multiple environments, eliminating scanning queues and speeding up your testing process. It automatically consolidates results from all environments into a single location, saving you the hassle of manual collation.
With flexible deployment options, Invicti adapts seamlessly to your cloud, on-premise, or hybrid infrastructure.
Invicti Features
- Leverage AI to automatically evaluate your web assets post-discovery and calculate a risk score based on up to 220 external features.
- Scan any web application, web service, or API, including first and third-party code.
- Utilize a manual scanning toolkit where automated scanning fails.
- Offer Proof-Based Scanning™ to reduce false positives, eliminating the need for manual verification.
- Provide developers with detailed documentation highlighting the exact locations of vulnerabilities for faster issue resolution.
Invicti Pricing
Invicti offers custom pricing. To learn more about its features, you can request a demo of the Invicti web application security scanner.
10. Detectify
Best for Simulating Hacker-like Attacks
Detectify Application Scanner is an automated web application vulnerability scanner that checks custom-built applications for a wide range of vulnerabilities, including OWASP Top 10, SQL injection vulnerabilities, input sanitation issues, SSL and encryption misconfigurations, vulnerabilities behind authentication, and more.
Detectify will scan your applications continuously to detect the latest vulnerabilities, and you will have recurring weekly scans in development, staging, and production environments.
You can also schedule scan frequency or trigger tests from Detecigy API. It offers a detailed overview of all vulnerabilities and remediation tips, allowing you to filter and tag results for better prioritization of fixes.
Detectify Features
- Discover many security-related bugs or unexpected behavior issues using the fuzzing engine.
- Perform effective authenticated testing with three options for scanning behind login: recorded login, basic authentication, and session cookies.
- Reduce scan time for large apps by allowing the Detectify crawler to identify common structures and filter similar pages.
- Customize and optimize vulnerability scans by fingerprinting your domains and their software and applying relevant, technology-specific tests.
Detectify Pricing
Detectify offers two pricing models: Full EASM and Small Attack Surface, each available in two modes—Surface Monitoring and Application Scanning.
The Full EASM model is priced based on custom quotes, while the Small Attack Surface model offers Surface Monitoring at €275 per month and application Scanning at €82 per month.
All plans come with a 2-week free trial.
11. Hacker Target
Hosted Open Source Vulnerability Scanners
Hacker Target provides a suite of vulnerability scanners designed to uncover your attack surface, identify weaknesses, and gather actionable network intelligence. It helps you identify vulnerabilities from the attackers’ perspective by simulating real-world security events, testing for vulnerabilities, and evaluating your incident response.
Hacker Target offers online scanners, including the Nmap Port Scanner, OpenVAS Vulnerability Scanner, Zmap Fast Network Scan, WhatWeb/Wappalyzer, SharePoint Security Scanner, WordPress Security Scanner, Joomla Security Scanner, Drupal Security Scanner, and SSL Scanner.
All online scanners offered by Hacker Target are hosted as a hosted service, so you don’t have to install or maintain any tool on your system.

Hacker Target Features
- Identify poorly maintained endpoints and forgotten assets.
- Discover a wide range of web application and network service vulnerabilities on any system exposed to the internet.
- Launch vulnerability scans easily with a simple interface.
- Monitor internet-facing services on a host or network.
- Schedule scans flexibly on a weekly or monthly basis.
- Leverage DNS data sets and Internet-wide scan data to identify organization-wide endpoints.
Hacker Target Pricing
Hacker Target offers two pricing tiers:
- Standard Plan: The Starter plan costs $10 per month, The Pro plan is $25 per month, and The Business plan costs $50.
- Enterprise Plan: The Enterprise One plan costs $100 monthly, and the Enterprise Two plan costs $200.
All plans come with a 7-day money-back guarantee.
12. Indusface WAS
Managed DAST Platform
Indusface Web Application Scanning (WAS) is an AI-powered DAST scanner that verifies all the discovered vulnerabilities using a combination of AI and human intervention to guarantee zero false positives.
Indusface WAS scans websites for OWASP’s top 10 vulnerabilities, SANS 25, SQL injection, XSS, zero-day threats, and other vulnerabilities. It provides you with detailed remediation guidelines for each open vulnerability discovered.
Indusface WAS also allows easy integration into your CI/CD pipeline to automatically trigger scans on new builds and create tickets for vulnerabilities.

Indusface WAS Features
- Offers unlimited automated app scans.
- Consolidate DAST, Malware, Infrastructure, and pen test results into a single dashboard.
- Receive website defacement alerts.
- Conduct deep and accurate authenticated scans
- Sending scan logs to major security information and event management (SIEM) providers.
Indusface WAS Pricing
Indusface WAS offers three pricing tiers with options to pay monthly or yearly. The Basic plan is free, while the Advanced plan costs $59 per app per month. The Premium plan is $199 per app per month. It offers a 14-day free trial to explore its paid features.
13. Astra Pentest
Best to Perform Automated Pentest
Astra offers an automated scanner that scans web applications, mobile apps, APIs, cloud infrastructure, and networks for various vulnerabilities, including SQL injections, logic errors, misconfigurations, SANS25, and OWASP Top 10.
Astra vulnerability scanner organizes all of your vulnerability data in one place and provides you with practical steps to fix the vulnerabilities it detects.
Astra allows your security team to discuss each security issue where it is listed, streamlining communication and collaboration among team members by eliminating the need for emails, calls, and messages. To improve collaboration, you can easily connect the Astra scanner with various tools, such as Slack, Jira, and GitLab.

Astra Features
- Gain a broad view of your security posture with its CXO dashboard.
- Prepare for compliance with various regulators, including ISO, SOC2, GDPR, and CIS, by covering all necessary tests.
- Utilize a continuous vulnerability scanner and expert human support to fix critical issues faster.
- Prioritize vulnerability fixing based on ROI.
- Secure an industry-recognized security certificate to build trust with your customers and partners.
Astra Pricing
Astra offers 3 pricing tiers:
- The Scanner plan ($1,999/year) offers unlimited vulnerability scans, CI/CD tool integrations, and AI-powered assistance.
- The Pentest plan ($5,999/year) adds an annual pentest, cloud security reviews, and compliance reporting.
- The Enterprise plan (starting at $9,999/year) includes multiple targets, a Customer Success Manager, and Slack Connect support.
14. Pentest Tools
Easy to Use
Pentest Tools offers a security testing suite that includes various vulnerability scanners to detect vulnerabilities in your web application. It comes with a website scanner, network scanner, subdomain finder, port scanner, URL Fuzzer, WordPress scanner, and many other reconnaissance and exploitation tools.
Pentest Tools’ vulnerability scanners can help you identify a wide range of vulnerabilities in classic and modern web applications, including SQLi, XSS, OS command injection, and more. These scanners also help you detect API vulnerabilities and security issues in popular CMSs like WordPress, Drupal, or Sharepoint.
Additionally, Pentest Tools allows you to send scan results to a Jira project, receive notifications via webhooks, and view a digest on Slack or Microsoft Teams.

Pentest Tools Features
- Create an attack surface based on your scan results to gain an in-depth view of your target’s exposure.
- Utilize a dedicated VPN agent to simulate an attacker with local network access.
- Scan behind login pages to identify vulnerabilities in your application.
- Combine scan results from multiple tools into an easy-to-read report in just 3 minutes, and export reports in HTML, PDF, DOCX, and other formats.
- Incorporate multiple tools in scan templates for wider coverage and take advantage of scheduling and bulk scanning options.
Pentest Tools Pricing
Pentest Tools offers a Free plan with basic tools. The Basic plan, at $85/month, includes all tools with light scans and supports up to 5 assets. The Advanced plan, priced at $190/month, adds features like scanning behind logins and supports up to 50 assets. At $395/month, the Teams plan includes all Advanced features, supports up to 500 assets, and provides additional capabilities like API access and premium support.
The Premium tier follows a pay-as-you-go model with variable pricing, while the Enterprise tier offers fixed-price or asset-based subscriptions tailored to organizational needs. Visit the pricing page for more details and a $300 credit to try the product.
15. Google Web Security Scanner
Best to Scan App Hosted on GCP
Google Web Security Scanner is an automated web security scanner that finds vulnerabilities in your APP engine, compute engine web applications, and Google Kubernetes Engine (GKE).
Google Web Security scanner tests your application by following all links from the starting URLs and analyzes as many user inputs and event handlers as possible. However, it only works with public URLs and IPs that aren’t protected by a firewall.
Google Web Security Scanner conducts weekly managed scans to identify and assess public web endpoints. These scans are configured and managed through the Security Command Center. However, managed scans are limited to applications using the default ports—80 for HTTP and 443 for HTTPS. Custom scans are required for applications utilizing other ports.
Google Web Security Scanner Features
- Conduct custom scans to gain detailed insights into application vulnerabilities, including mixed content, outdated libraries, XSS, etc.
- Display vulnerability types and their corresponding compliance standards.
- Control access to the security scanner with Identity and Access Management (IAM) controls.
- Validate scan configurations during creation and before each scan.
Google Web Security Pricing
Google Web Security Scanner is available in the Security Command Center’s Enterprise, Premium, and Standard tiers, but some functions may be limited in the Premium and Standard tiers.
Google Cloud’s Security Command Center offers three service tiers: Standard, Premium, and Enterprise. Only the Premium and Enterprise tiers incur charges, separate from the costs of other Google Cloud services.
The Premium tier uses a pay-as-you-go model, with pricing varying based on organizational or project-level activation. Visit the pricing page for more information. It offers a $300 credit to try the product.
Is There Any FREE Online Website Security Scanner?
Yes, there are some free online website security scanners, such as Sucuri and ImmuniWeb, that can help detect vulnerabilities on your website.
You should note that a free version of an online website security scanner might not have all the essential features to discover all your website’s vulnerabilities. So, it is always better to use one of the best premium website security scanners to scan your website comprehensively.
What Are the Popular Open-Source Security Scanners?
The popular open-source security scanners are Nikto, OWASP Zap, and OpenVAS. These tools are popular in the security community for their effectiveness and ability to customize and extend their capability. Using open-source security scanners offers various benefits, including cost-effectiveness, transparency, flexibility, customization, and no vendor lock-in.
Many of these tools also function as XSS scanning tools, helping to detect cross-site scripting vulnerabilities that can be exploited by attackers to inject malicious scripts into webpages. For instance, OWASP Zap includes automated XSS detection capabilities, making it a handy resource for developers and security testers alike.
More on Website Security


