Subdomain finder is used to identify subdomains associated with a domain name for various purposes, such as security audits, SEO research, and penetration testing.
Subdomains are extensions of a domain name that allow website owners to create separate sections of their site for different purposes, such as a blog, online store, or support portal.
Hackers can use unmonitored subdomains to steal data and engage in malicious activities, potentially harming a website’s reputation. Monitoring all subdomains linked to a website is crucial to prevent these risks.
A subdomain finder can help uncover hidden web pages, test for vulnerabilities, and improve website performance. It is used by cybersecurity professionals, digital marketers, and website administrators.
Geekflare has researched and compiled the best domain finders based on ease of use, domain scoring, and comprehensive scanning capabilities.
- WhoisXML Subdomain Lookup – Best for Developers
- Cyber Asset Finder by Attaxion – Best for Security Analysis
- Criminal IP – Best for Domain Scoring
- DNSDumpster – Best for Visualizing Subdomains
- NMMapper – Best for Simple Online Lookups
- Sublist3r – Best for Python Users
- Netcraft – Best for Historical Subdomain Data
- Knock Subdomain Scan – Best for Fast Permutation-Based Scans
- DnsRecon – Best for Kali Linux DNS Recon
- Pentest-Tools Subdomain Finder – Best for Pentesters
- MassDNS – Best for Bulk Lookups
- OWASP Amass – Best for Asset Discovery
- Show less
You can trust Geekflare
At Geekflare, trust and transparency are paramount. Our team of experts, with over 185 years of combined experience in business and technology, tests and reviews software, ensuring our ratings and awards are unbiased and reliable. Learn how we test.
WhoisXML Subdomain Lookup
Best for Developers
WhoisXML Subdomain Lookup is a part of the Domain Research Suite (DRS). It helps you discover a comprehensive list of subdomains associated with your main domain in just one click.
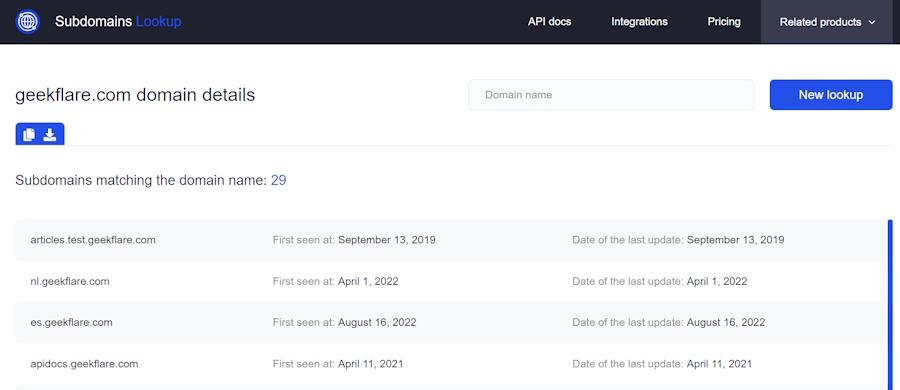
With its extensive database that is updated daily, WhoisXML Subdomain Lookup offers up-to-date information about subdomains.
Subdomain records include three data points: subdomains, date first seen, and date last seen.
You can access subdomain intelligence through GUI tools, API calls, or batch feeds. When you use API, query results are in XML and JSON formats for easy integration.
WhoisXML Subdomain Lookup offers three payment plans, including a one-time purchase starting at $23, a monthly subscription starting at $19, and a yearly subscription starting at $190. It offers 500 DRS for free credit to try it. Each request costs one DRS credit.
Cyber Asset Finder by Attaxion
Best for Security Analysis
Cyber Asset Finder by Attaxion helps to find the subdomains of any target domain, displaying up to 1000 subdomains. Scans are performed in real time and can be refreshed as needed. I like as it is free, and I don’t need to create any account to use it.
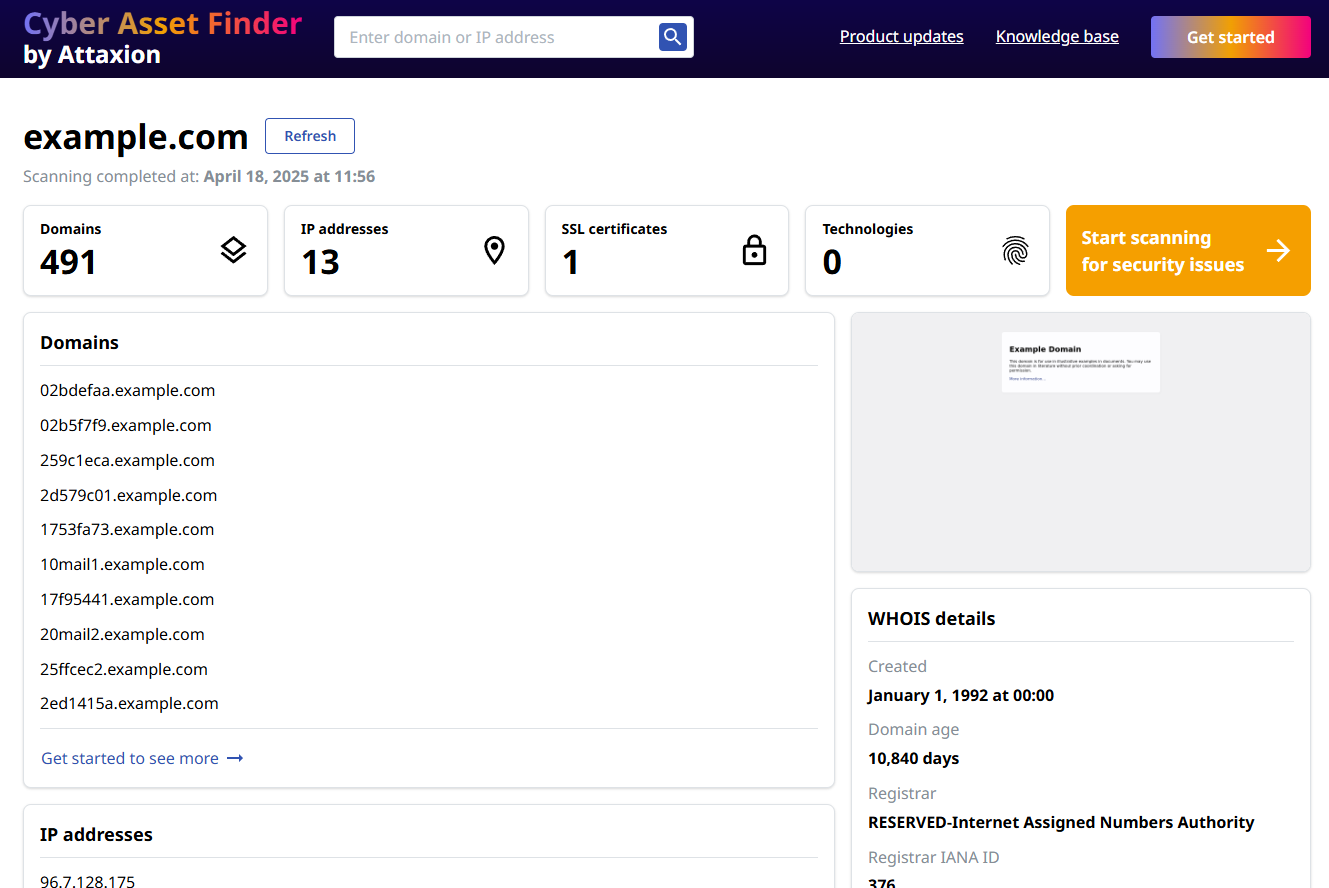
Along with subdomains, Cyber Asset Finder also shows other related crucial information like IP addresses, SSL certificates, web technologies, DNS records and WHOIS details.
It helps to support security analysts in gaining better visibility into external assets and potential unintended exposures, while uncovering shadow IT. It also serves as a preview of Attaxion’s advanced External Attack Surface Management (EASM) platform, which includes additional capabilities such as vulnerability scanning and deeper asset discovery.
Criminal IP
Best for Domain Scoring
Criminal IP is an open-source intelligence (OSINT) search engine that focuses on assessing attack surfaces and hunting for threats. Its domain research toolkit analyzes domain vulnerabilities and provides a score.
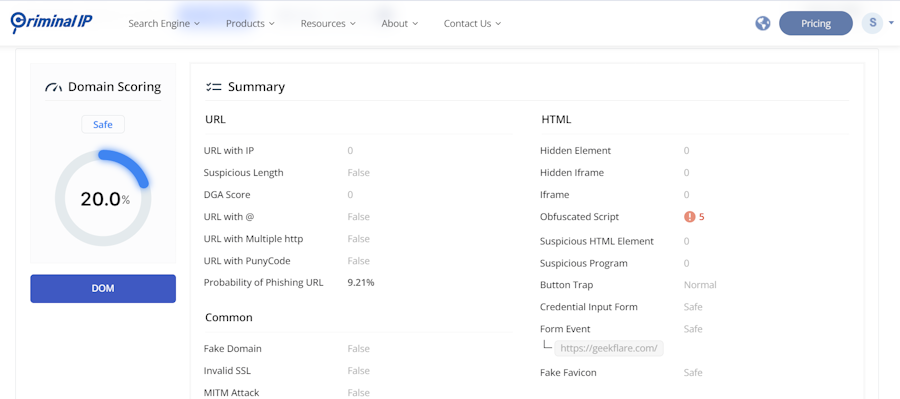
The domain search feature of Criminal IP allows you to find all connected domains and subdomains, as well as tons of other security insights, including:
- History of communication during page loading.
- Technical stack used in a page
- Information about certificates used on the page.
- Inspection of connected IPs to discover malicious IPs
You have an option to export the report in the PDF format.
When the free plan is not sufficient, you can go for premium one which starts at $58.5/month on an annual plan.
DNSDumpster
Best for Visualizing Subdomains
DNSDumpster is a free domain research tool that provides information on domain host records, DNS records, and TXT records and offers a domain map feature. It is managed by hackertarget.com.
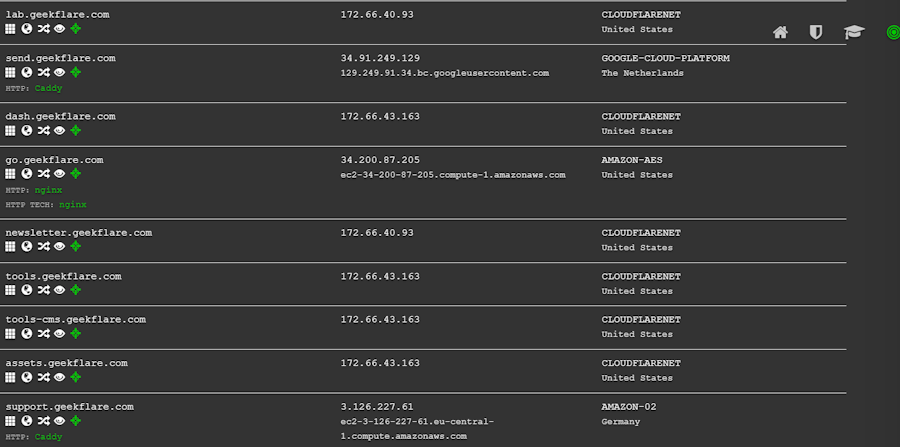
The search utilizes data from various sources, such as search engines, web archives, security information databases, SSL certificate logs, and internet scans, to conduct a comprehensive search for hidden subdomains and web hosts, enhancing vulnerability assessment and attack surface discovery.
NMMapper
Best for Simple Online Lookups
NMMapper is a useful tool for finding subdomains associated with your website. It utilizes eight popular subdomain finders to gather all hosts of your domain, making it an effective domain availability checker.
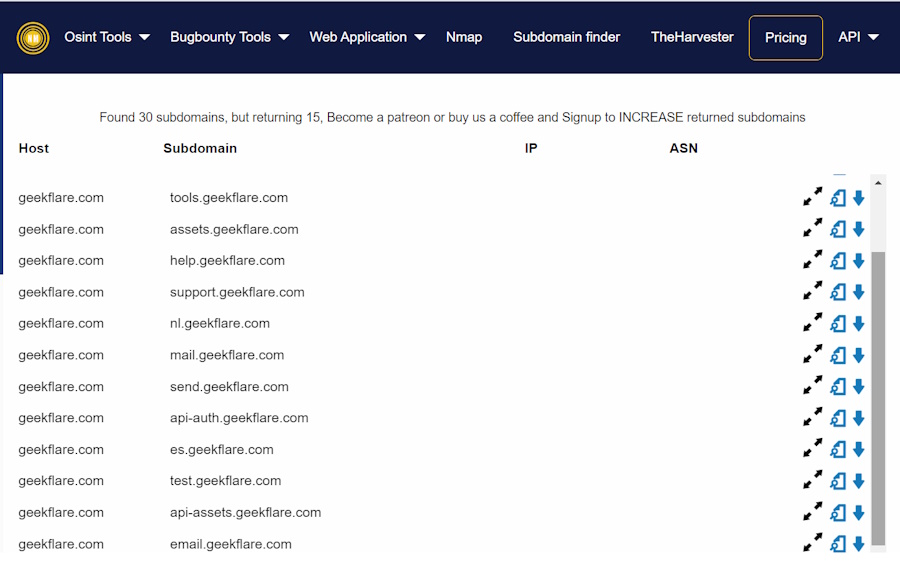
And the best part is you can perform concurrent target scans on all these subdomain finders. This feature helps you compare and inspect results provided by these tools to get better insights into the subdomains associated with your main domain.
NMMapper also allows you to scan each of the subdomain names you have discovered to identify servers, technology, and DNS A records. If you run multiple domains, it can also help you visually inspect and compare which domain has the largest sub-domain.
NMMapper offers three pricing plans:
- Standard- $5 per month with limited features
- Premium- $10 per month with the ability to export records JSON/Excel
- Professional- $15 per month with full API access and other advanced features
Sublist3r
Best for Python Users
Sublist3r is a powerful Python tool designed for subdomain enumeration using open-source intelligence (OSINT).
Well-suited for penetration testers, Python users, and bug hunters, Sublist3r finds subdomains using Ask, Baidu, Bing, Yahoo, Google, ReverseDNS, DNSDumpster, VirusTotal, and Netcraft.
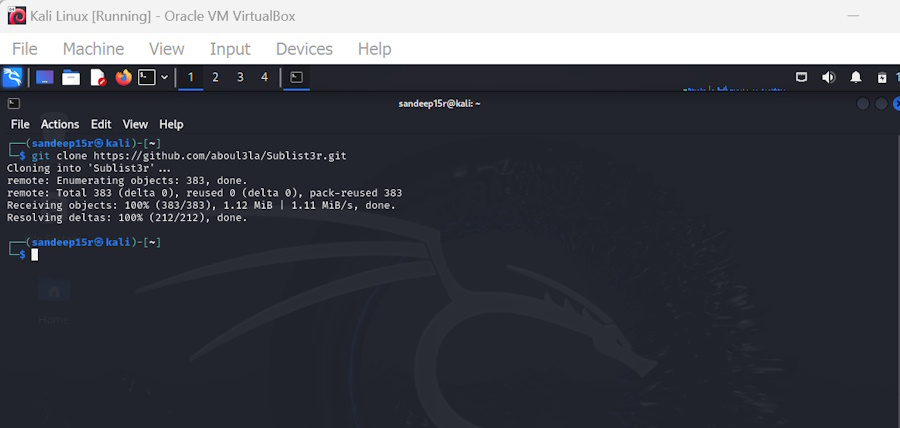
What’s more, the integration of Sublist3r with SubBrute enables you to discover more subdomains through brute forcing using an improved wordlist. Sublist3r is free to use.
Sublist3r can scan found subdomains against specific TCP ports. Moreover, you can enable verbose mode to display results in real-time. It also has an option to save the results to a text file.
Sublist3r supports Python 2 and 3 and requires Python modules like requests, dnspython, and argparse to work.
Netcraft
Best for Historical Subdomain Data
Netcraft is a leading cybersecurity company offering a family of apps and extensions for email clients, browsers, and phones to enhance cybersecurity.
Netcraft offers a free tool to discover unmonitored subdomains linked with your main website. It is an easy-to-use tool; you just have to paste your website in the search box and press the enter button on your keyboard to see subdomains.

However, Nercraft has a limitation. The search results will only show websites visited by Netcraft Extensions users at least five times in the last six months.
Netcraft’s SearchDNS tool is intuitive, and you will not encounter any difficulties using it. If you cannot use the tool optimally, explore the Search Tips section.
Knock Subdomain Scan
Best for Fast Permutation-Based Scans
Knock Subdomain Scan is a modular and portable Python3 tool designed for fast subdomain enumeration on the target domain using passive reconnaissance and dictionary scan.
With Knock Knock Subdomain Scan, you have the power to tailor your subdomain reconnaissance and brute-force attacks. You can leverage a range of customized options, including DNS servers, user agents, timeouts, and thread counts, to suit your specific needs.
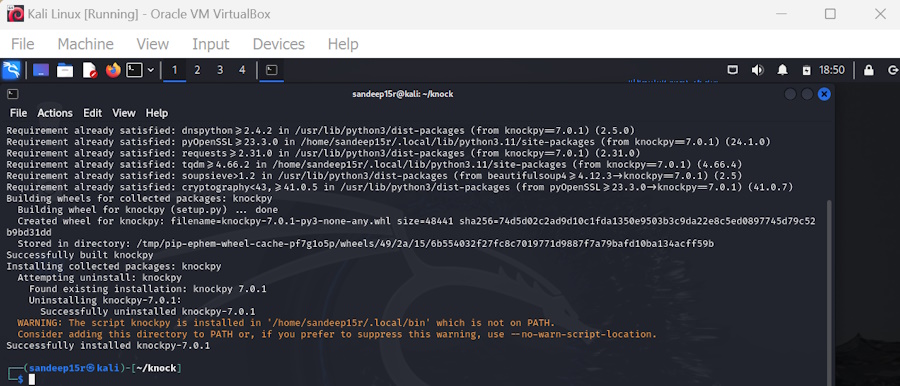
Knock Subdomain Scan can integrate with VirusTotal and Shodan for enhanced scanning capabilities by setting the respective API keys.
Knock Subdomain Scan supports JSON output and the report-saving feature for better data management. Guelfoweb developed the tool, which is in version 7.0.1. It is free and offers various installation options, including via pip or git.
DnsRecon
Best for Kali Linux DNS Recon
DnsRecon is a powerful Python tool designed to explore DNS functionalities and enhance network security assessments. Created as a Ruby script in 2007, it has since been rewritten in Python to extend its capabilities.
DnsRecon offers various features to perform comprehensive DNS checks. It can verify Name Server (NS) records for zone transfers and enumerate general DNS records such as Mail Exchange (MX), Start of Authority (SOA), NS, Address (A), AAAA, Sender Policy Framework (SPF), and Text (TXT) for a given domain.
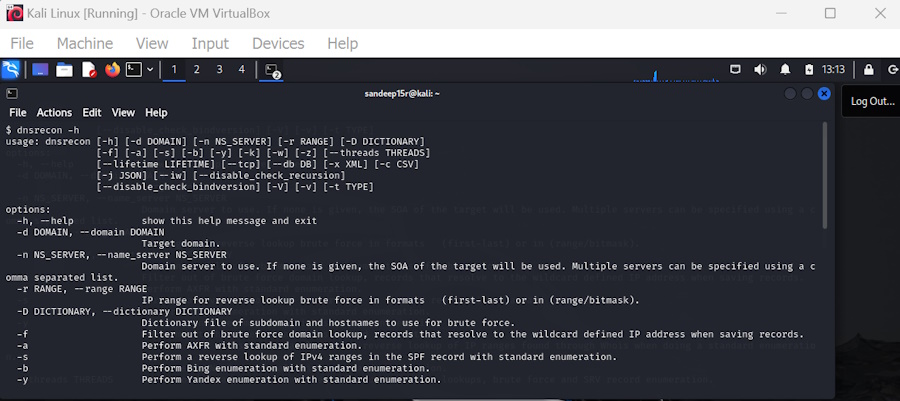
Additionally, it can perform common Service (SRV) record enumeration and expand top-level domains (TLDs). DNSRecon also includes functionality to check for wildcard resolution and brute force subdomains and host A and AAAA records using a specified domain and wordlist. These insights can help you enhance your web security to prevent subdomain takeover attacks.
DnsRecon can perform Pointer (PTR) record lookups for given IP ranges or Classless Inter-Domain Routing (CIDR), making it valuable for network mapping and reconnaissance. It can also check DNS server cached records for A, AAAA, and CNAME records using a list of host records provided in a text file.
To use DnsRecon, you need Python 3.6 or newer, which ensures compatibility with modern Python environments. It is a free tool that comes preinstalled on Kali.
Pentest-Tools Subdomain Finder
Best for Pentesters
Pentest-Tools Subdomain Finder helps you identify subdomains of an internet domain to understand your organization’s attack surface. It combines multiple discovery methods to return valid results for extensive reconnaissance.
Subdomain Finder validates each scan result, providing IP addresses, WHOIS details, server information, and more.
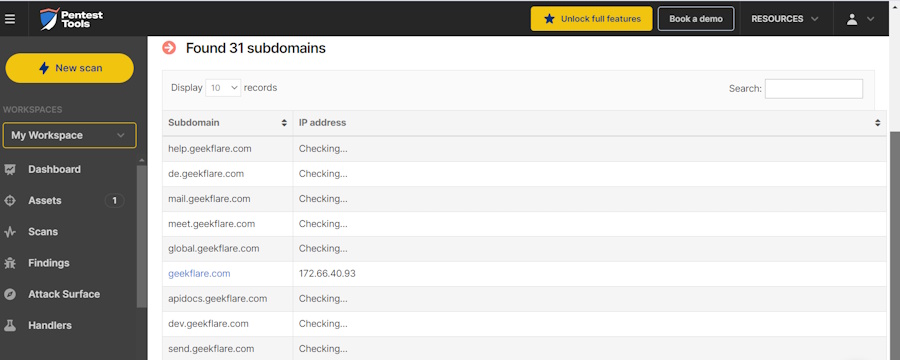
It identifies subdomains behind firewalls and supports wide-scope engagements, which makes it essential for vulnerability scanning and ethical hacking.
Subdomain Finder offers various tools for security scanning, including vulnerability scanning, WAF detection, and port scanning. It has both free and paid plans, with the paid plans offering access to 20+ security tools and features. The free plan allows for basic subdomain extraction, while the paid plan offers deeper scans and customizable options.
Here is the pricing plan for Pentest-Tools:
| Plan | Pricing | Number of Assets | Parallel Scan |
|---|---|---|---|
| Basic | $84/month | 5 | 2 |
| Advanced | $190/month | 50 | 5 |
| Teams | $395/month | 500 | 10 |
It also offers a free plan that allows you to scan up to 5 assets and run 2 parallel scans with limited features.
MassDNS
Best for Bulk Lookups
MassDNS is a high-performance DNS stub resolver that can resolve millions or billions of domain names. It can handle over 350,000 names per second with public resolvers without any particular configuration.
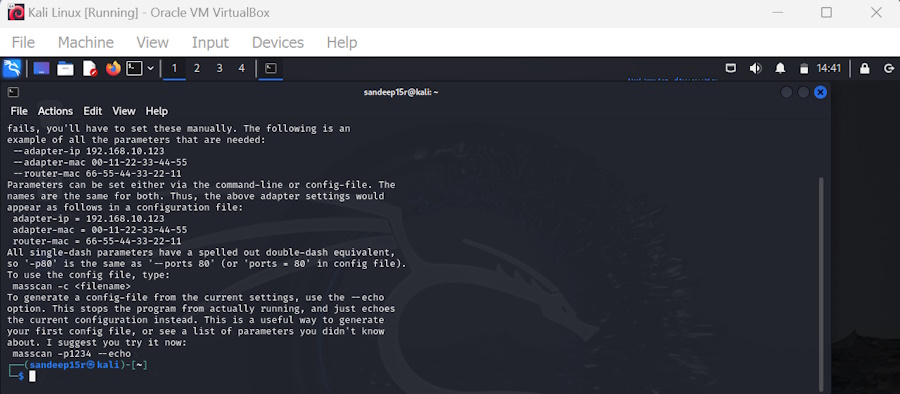
MassDNS supports various options for DNS queries, including custom resolver files and output formats to offer data from your chosen list of domain names. It also includes scripts for advanced tasks like subdomain brute-forcing and extracting data from certificate transparency logs.
Ideal for users who need to process a vast amount of domain names efficiently, MassDNS offers a simple yet powerful solution for large-scale DNS resolution tasks.
MassDNS is free to use. However, to use the tool optimally, you need some technical know-how.
OWASP Amass
Best for Asset Discovery
OWASP Amass is ideal for security researchers due to its ability to perform thorough network mapping of attack surfaces and external asset discovery.
OWASP Amass uses open-source intelligence gathering and reconnaissance techniques to find subdomains associated with a domain, and it is free to use.
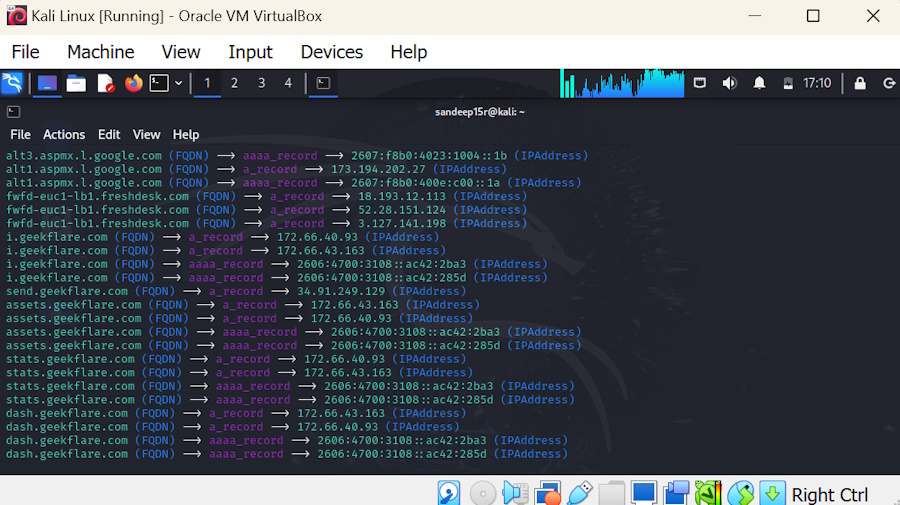
The OWASP Amass framework comes with:
- A collection engine for asset discovery
- An asset database for storage of findings
- The Open Asset Model
For DNS-related search queries, OWASP Amass uses Brute forcing, Reverse DNS sweeping, NSEC zone walking, Zone transfers, Fully Qualified Domain Name (FQDN) alterations/permutations, and FQDN similarity-based Guessing to provide results.
If you use a fully functional Kali Linux, OWASP Amass is already there. Go to “Application,” search for Amass, and click on it to run.
Benefits of a Subdomain Finder Tool
A subdomain finder tool is critical for efficient domain management and security, as it uncovers hidden subdomains and provides you with valuable insights.
Here are the key benefits a subdomain finder tool offers:
- Enhancing Security: By identifying hidden subdomains, a subdomain finder tool can help strengthen your website’s security defenses.
- Comprehensive Reconnaissance: Mapping out domains using a subdomain finder tool enables you to conduct thorough research and analysis.
- Time-Saving Automation: Automating the process of discovering subdomains with a finder tool helps save valuable time and resources.
- Prioritizing Vulnerability Scans: A subdomain finder tool can assist in determining which subdomains should be prioritized for vulnerability scans to prevent potential security breaches.
- Improving Incident Response: By uncovering unauthorized subdomains, a finder tool can enhance your incident response strategies and prevent potential threats.
- Brand Protection: Detecting rogue subdomains with a finder tool can safeguard your brand reputation and prevent any unauthorized usage.
- Detailed Information: Subdomain finder tools provide in-depth information such as IP addresses and WHOIS details, allowing you to assess and manage your domains effectively.
Use Cases of a Subdomain Finder Tool
Subdomain finders are essential tools in cybersecurity and IT management, offering a range of applications.
Here are some common use cases where subdomain search tools prove to be invaluable:
- Identify all subdomains for comprehensive security audits and discover hidden vulnerabilities
- Conduct thorough reconnaissance to map out the attack surface and test subdomains for security weaknesses.
- Locate subdomains to uncover hidden vulnerabilities and increase the chances of finding exploitable issues.
- Continuously monitor subdomains for new vulnerabilities and prioritize them based on risk level.
- Investigate subdomains to understand the scope of security incidents and identify unauthorized subdomains.
- Detect and manage subdomains to prevent misuse and impersonation and protect brand reputation.
- Ensure all subdomains comply with security policies and generate reports for audits and regulatory requirements.
What Are Popular Penetration Testing Tools Available?
Metasploit, Nmap, and Burp Suite are popular penetration tools. These pentest tools help identify vulnerabilities and ensure robust security measures.
#1. Metasploit
Metasploit is a widely used penetration tool created by the open-source community and Rapid7. It comes in two versions, Metasploit Framework (free) and Metasploit Pro (paid), and is based on the use of modules to perform specific functions in penetration testing.
#2. Nmap
Nmap is a free, open-source network scanning tool used for network discovery and security auditing. It helps identify available network hosts, services, operating systems, packet filters/firewalls, and other network characteristics.
#3. Burp Suite Professional
Burp Suite Professional is an advanced web vulnerability scanner that helps with manual testing, automatic discovery, and fixing security issues in web applications.


