There is no rest for the webmaster. There is always something to do to keep websites healthy and to work in optimal conditions.
For example, monitor the SSL certificates to check if they are working properly and not expired.

The X.509 Public Key Certificates –or, as we all call them, SSL/TLS certificates– have an expiration date. After that date, the websites or applications they work for will simply stop sending and receiving data through a Secure Sockets Layer (or SSL for short), showing a security warning to your visitors or users.
Therefore, as a webmaster, you need to be sure that your certificates don’t expire. That could be an annoying task if you have many sites or web applications to maintain, so it is a good idea to have someone (or something) check the expiration dates for you, and warn you when those dates approach.
You may think that you’re not that lazy. I mean, if you have a whiteboard hanging on your office’s wall, you may just jot down the expiration dates with a red marker and add a couple of exclamation marks when the time to renew the certificates approaches, right?
The fact is, there’s more to certificate monitoring than just periodically checking expiration dates. There are more certificates than you may think — not just the one you purchased for your site — and it’s not just the expiration date that needs to be checked, because certificates can be revoked without your notification. Additionally, your site could be blocked if your certificate is not sufficiently secure or altered due to a potential malware attack.
So let’s take a look at all the things related to certificate monitoring.
Introducing the chain of trust
To be trusted, an SSL certificate needs to be traceable back to the trusted root it was signed off. That is to say, it has to be linked to a trusted certificate authority (CA) through a chain of trust. The chain of trust comprises three parts: the root certificate, the intermediate certificate, and the server certificate.
* The root certificate belongs to a CA, which carefully keeps it in a trust store.
* The intermediate certificates stay between the root certificate and the server certificate, acting as a middle-man between them. There can be many intermediate certificates in a trust chain, but there has to be at least one.
* The server certificate is issued for the specific domain that needs to be included in the trust chain.
When you buy an SSL certificate, you also get a bundle, including an intermediate root certificate. When someone arrives at your website, their browser downloads your certificate and follows the trust chain back to the trusted root certificate. If the browser can’t follow the chain, it will warn the user about a possible security threat.
Your certificate’s chain of trust can cause errors if something has not been correctly configured. Common problems include that a trusted CA didn’t issue the certificate, that the intermediate certificates aren’t properly installed, or that your server is not correctly configured with your SSL certificate. These are some of the issues that certificate monitoring tools can check for you.
Below we list some of the most popular certificate monitoring tools that could free you from the task of monitoring your SSL/TLS certificates.
Dotcom-Monitor
Whether you’re one person managing a few websites, or an enterprise company managing thousands, Dotcom-Monitor’s SSL monitoring service can notify you before certificates expire and ensure that you avoid costly downtime and error messages.
Dotcom-Monitor has everything you need to monitor SSL certificates in one, easy-to-use dashboard. You can set expiration reminders, check certificate authority, monitor common name verification, track SSL certificate usage, and prevent SSL revocation with just a few clicks in minutes!
StatusCake
If you’re looking for an SSL monitoring solution that does all the hard work for you, then StatusCake is the perfect tool.
It’ll monitor your SSL certificate for you, alerting you when it’s due to expire, or has expired, and help you to make sure it’s set up correctly. Better still, StatusCake integrates with 18 different platforms allowing you to choose how you receive your alerts, and who in your team should be getting them.

Unsure how SSL monitoring would have an effect on your website?
StatusCake’s tool eliminates the risk of your transaction process breaking, your search rankings dropping in Google and your customer satisfaction taking a hit, all with their SSL monitoring.
That’s not all. StatusCake has an intelligent SSL algorithm that calculates your SSL score, based on your certificate set-up. They’ll send you a detailed SSL report so you can easily identify any issues in the backend that could be affecting your website and, ultimately, your bottom line.
Sematext
Sematext offers SSL certificate expiry checks as part of their Synthetics Monitoring. Not just validity but monitor certificate chain, tracking changes, and a lot more.

You can get notified before the certificate expires and also in the event of any errors through multiple channels like Slack, Twilio, Zapier, VictorOps, custom hooks, and many others. It will help you avoid your website downtime due to certificate issues. In addition to that, you will get a detailed report whenever the tracked certificate changes.
Along with SSL/TLS certificate, you can monitor the complete website for performance, and the pricing starts from $2 per HTTP monitor. The best part is you pay as you go.
Better Uptime
Better Uptime is a modern monitoring service that combines SSL and synthetic monitoring options, incident management, and status pages into one product.

The setup takes 3 minutes. After that, you get a call, email, or Slack alert, whenever your SSL certificate is about to expire or is not working properly. The main features are:
- Unlimited phone call alerts
- HTTP(s), Ping, SSL & TLD expiration, Cron jobs checks
- Easy on-call scheduling
- Screenshots & error logs of incidents
- Slack, Teams, Heroku, AWS, and 100+ other integrations
Sucuri
SSL certificate monitoring is just one of the many options that Sucuri offers within its suite of services for scanning websites to detect possible malware problems.

When the service detects that changes were made to your website’s SSL certificate, it will immediately send you an alert so you can take the necessary actions. Sucuri’s complete malware detection service is fee-based, with plans starting at $ 199.99 per year.
Besides SSL certificates, it also scans for malware, SEO spam, blacklist status, DNS, and uptime monitoring.
Updown
Updown offers a simple and inexpensive website monitoring service, including SSL testing. Once you set up the service, you will begin receiving alerts in case of invalid or expiring certificates. Updown charges only for what you use, with no need to pay fixed monthly or yearly fees.

You buy credits and set up a monitor that operates until it consumes the credit. For example, if you want to check two websites every minute, it will cost you about € 1.17 a month. The alerting systems covered include SMS, Webhook, Zapier, Telegram, and Slack.
Oh Dear!
Oh Dear! does more than just monitor your domain certificate.

It performs a complete validation of your certificates’ chain of trust, checking all your intermediate certificates. If it detects a change in any of the certificates, it will present you with a clean report comparing the before & after situation to see if there was a change in any of the covered domains. This service also looks for old SHA-1, revoked, or distrusted root certificates, all of which can cause a site to be unavailable.
HTTPS Cop
Ashish Kumar offers a certificate expiry alert service for free, just because he wants to make the Web more secure and publicize his soon-to-be-released product HTTPS Cop, a complete set of tools to check all types of problems with a website’s SSL certificates.

Even though the full product is not yet released, the alert service is fully operational. You just have to type in your website’s URL, your email address, and you will begin getting notified two weeks before your certificates expire. You can add as many sites as you want to be monitored.
Keychest
Keychest business is all about digital certificates. Its service offers weekly email reports and dashboard summaries for all your certificates, with the ongoing discovery of new certificates thanks to its global database. It also offers renewal automation with third-party CAs and Let’s Encrypt management for businesses.

With Keychest, you can also purchase certificates with a unique 4-step purchasing process with price calculation. The purchase includes CSR generation and downloads for Linux and Windows and full automation of renewals.
CertsMonitor
CertsMonitor offers to fix all the problems with your certificates before they begin issuing embarrassing “insecure connection” warnings to you, visitors. The service includes keeping a tab on your Let’s Encrypt cron, fixing errors before the certificates expire, and seeing at a glance if your domain certificate is revoked or not configured properly.

You can receive reminders by email or through Slack. The service is free for monitoring up to 2 domains and has a cost of $ 29 per year for up to 30 domains.
Certificate Expiry Monitor
Certificate Expiry Monitor is an open-source utility that exposes the expiry date of TLS certificates as Prometheus metrics for those who prefer to build their own tools. The utility can be built on a Docker image or a Kubernetes cluster.
The project includes abundant documentation to access a Prometheus endpoint for monitoring, do a simple health check, and access many gauges and counters that show the certificates’ vital statistics.
Let’s Monitor
Whenever your certificates need renewal or aren’t working, Let’s Monitor will alert you for free. The service can send notifications to multiple contacts within a team through email messages or SMS. It also monitors uptime and performance to ensure the websites stay responsive and their data stays encrypted. To ensure worldwide access to your secured site, Let’s Monitor uses globally distributed servers.

Additionally, Let’s Monitor offers other advanced monitoring services, such as performance, availability, threats, and connectivity, among others. To get started with all these services, you just need to register with an email address and a password.
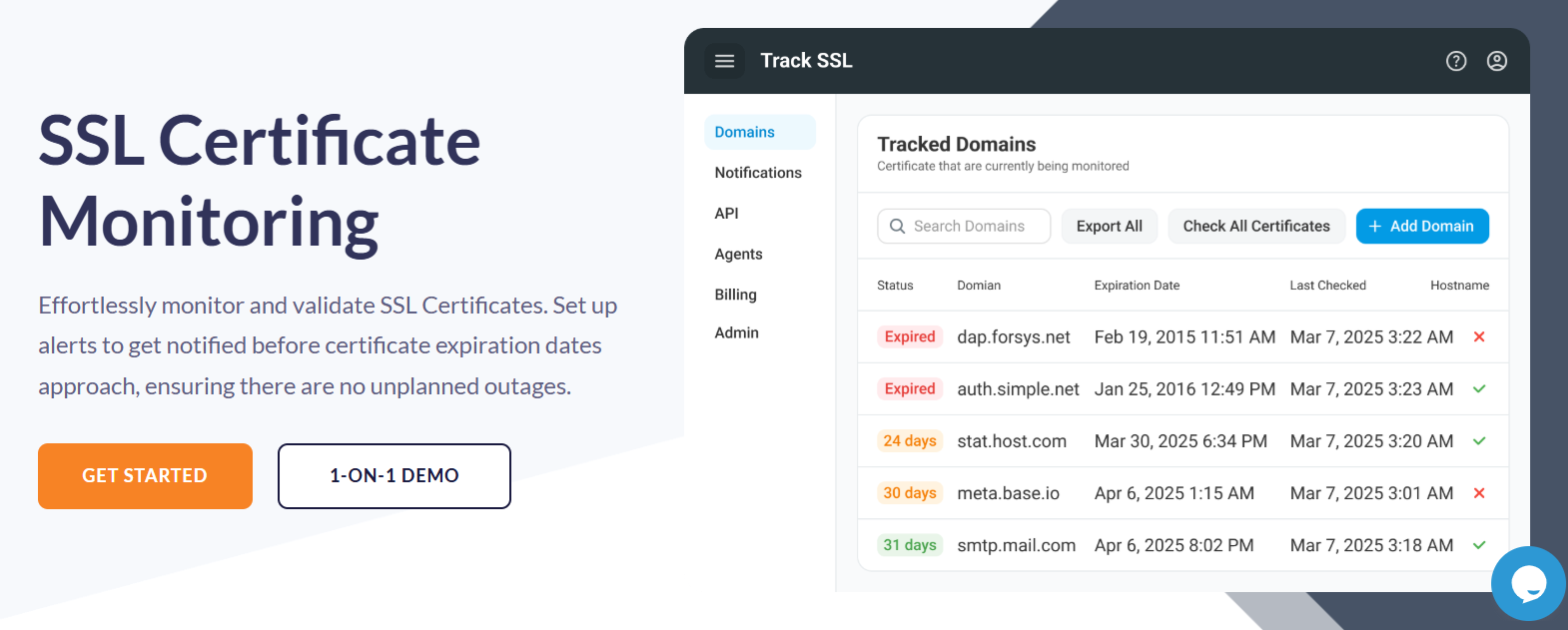
TrackSSL
TrackSSL is a web service that regularly checks your SSL certificates for common errors. To begin using it, you just need to create an account and add your certificates through the web interface. You will receive email notifications when the service detects problems with the certificates, such as pending expiry or misconfigured hosts.

TrackSSL will ensure that infrastructure changes don’t affect your certificates, sending you notifications whenever a change is detected. You can configure the notifications according to your needs, with the possibility of integrating with Slack and getting notifications into your #devops channel. Pricing plans start at $12 per year to cover up to 20 domains.
SSL Certification Expiration Checker
SSL-cert-check is a free and open-source shell script that you can run from cron to report on expiring SSL certificates. It can send a warning by email or log alerts through Nagios. The utility comes with several options that you can view with the “-h” option.
If you manage numerous certificates on a web server, SSL-cert-check can be used to print the expiration date for each of them. If you don’t have local access to the certificate files, you can use the utility’s network connectivity option to extract the certificates’ expiration dates from a live server.
In case you need to monitor a lot of servers, you can place their names and port numbers in a file and then run SSL-cert-check against that file.
Conclusion
If you don’t catch expired certificates early enough, the consequences could be really painful. The tools reviewed here offer notification features that can help you avoid problems, giving you peace of mind and freeing you from all the concerns associated with your website certificates.


