Network scanners or IP scanners are software applications or tools that are used to discover as well as scan devices, services and open-ports in a computer network that is IP-based. Network scanners send network packets also known as probes to gather information on the services and devices present through IP addresses that are within a specified range.
Network scanners are helpful in:
- Discovering devices
- Scanning ports and vulnerabilities
- Identifying services
- Mapping networks
- Auditing security
- Managing inventory, etc.
One of the challenging tasks for network administrators is to manage the IP addresses. It becomes complex when you are working in a large organization where hundreds of networks are connected.
Managing IP addresses in the spreadsheet is not fancy. It gets messy when you have thousands of IPs. Thanks to the following IP scanner, which helps you to scan IP, port, manage IP, and much more.
OpUtils
OpUtils is a switch port and IP address management software that helps engineers diagnose, troubleshoot, and monitor IT resources efficiently. It scans IPv6 and IPv4 subnets to identify the utilized and available IP addresses.
OpUtils also scans the switches available in your network, maps devices to switch ports, and views details like the users, locations, etc. This will help identify device intrusions and acts as a barrier to their access.
It allows you to track your network’s bandwidth usage and create bandwidth utilization reports for many parameters. It also schedules CISCO config file backups for downloading or uploading and compares other versions of the running and startup configuration files.

Using LAN tools, you can automatically or manually boot up idle machines present in your network. You can generate a graphical representation of SNMP IP nodes with the help of SNMP tools by viewing the snapshot of MIBs (Management Information Base) and query SNMP (Simple Network Management Protocol) devices.
To get this snapshot, you need to search the subnet for getting particulars of CISCO devices, and after that, you can collect some details like IOS details, flash memory, device snapshot, etc. It also scans TCP ports and SNMP devices and restores details of IP address, system, and more related to the MIB OID (Object Identifier).
You can also have access to manage, inspect, and resolve your MAC addresses, IP addresses, and DNS names with monitoring tools like MAC addresses and a DNS resolver. It will alert you on network issues that require your attention immediately by monitoring the servers in your network.
Learn how to Find IP Address of Windows, Linux, Mac, and Website.
Try either their free or professional version and manage your network with these tools.
PRTG Network Monitor
Scan IP addresses and multiple devices on LAN or WLAN and monitor your network. If there are any disruptions in the network, you would receive alarms to take action quickly. In addition to network devices, you can easily monitor network traffic.
With this IP scanner, view the number of devices available in your network. This tool comes handy to scan open ports to mitigate the possibilities of an online attack.
PRTG includes Sunburst along with other dashboards that you can access on your PC, tablet, or smartphone to customize it according to your priorities and network requirements. It offers real-time reporting and sensors for customized monitoring. Additionally, it provides a REST API sensor to monitor JSON and XML files.
Setting up of remote probes is possible with PRTG to regulate your decentralized network.
Fing
Fing is a free network scanner for home and small offices that catalogs and secures your devices.
Fing apps, available on both mobile and desktop, help users create their network device inventory, track network events, and protect from intrusions.
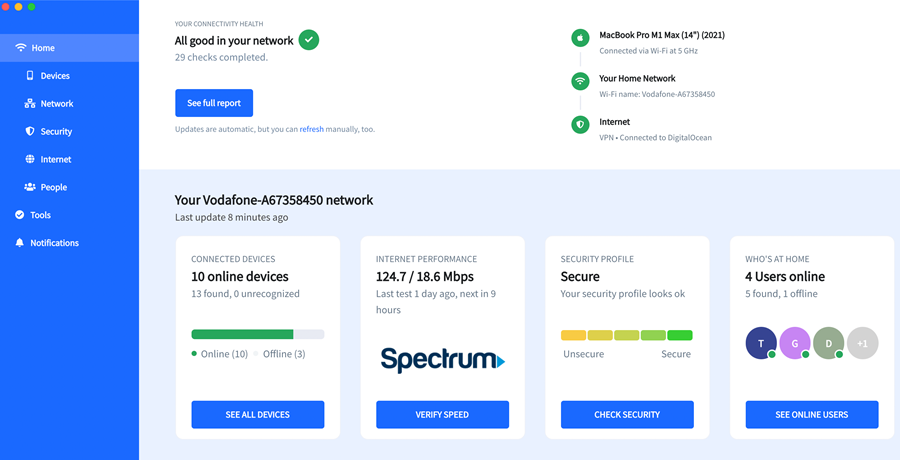
With Fing you can:
- Scan
- Identify all devices connected to your network
- View detailed information about each device, including IP and MAC addresses
- Monitor
- Create user profiles and track user presence over time
- Receive alerts when unknown devices join the network
- Run Internet speed tests and compare Internet Service Providers
- Secure
- Block unwanted devices permanently
- Autoblock unknown devices joining the network
- Run security and vulnerability checks
- Find hidden cameras in the network
- Control
- Limit internet time for specific users
- Schedule offline times for parental control
- Troubleshoot your network
Fing is free to download for Windows, macOS, Android, and iOS. Subscriptions plans for advanced features start at $2.99/month.
IP Address Manager
An advanced IP manager by SolarWinds is packed with tons of features. Managing DHCP, DNS, and IP with SolarWinds software is easy.
Some of the features:
- IP detail and history tracking
- Track IP address automatically
- Schedule a scan to ensure up-to-date data
- Capable of managing IPv4 and IPv6 addresses
- Be alerted when IP conflicts or mismatched DNS entries
- Monitor multi-vendor devices such as Cisco, Microsoft, ISC DHCP servers, BIND and Microsoft DNS servers from a single platform
- vRealize Orchestrator plugin to automate VM IP management
- Discover and track subnet and associated blocks
- Find IP address
- Delegate IP administration

It offers API, which makes integration with third-party software easy.
You can get it started with a FREE trial to see if it suits your requirements.
Angry IP Scanner
One of the famous IP scanners with more than 23 million downloads lets you scan local and internet-facing IP addresses.
Angry IP scanner is open-source software that works on Windows, MAC, and Linux.

Not just IP, but it’s capable of scanning ports. You have an option to save the scan results in multiple formats (TXT, XML, IP-port list files, CSV).
If you know Java, you can extend the functionality by writing a plugin.
As you can guess, it has a dependency on Java to run, so ensure you have installed it on your PC.
Free IP Scanner
Seeking the best IP tracker? Look no further than Free IP Scanner, a powerhouse lightweight scanner that conquers networks with lightning speed.

It works on Windows OS and powered by multi-thread scan technology.
This tool is capable of showing NetBIOS information such as hostname, workgroup, etc. You have an option to export the results in a file.
IP Scanner by Spiceworks
Automatically discover the devices in LAN (local area network).
Spiceworks IP scanner is available for Windows, OSX, and Linux. If you are looking to find out all network-connected devices for inventory quickly, then this would be handy.

Network Scanner
Lizard System’s network scanner lets you analyze your personal, corporate network. It uses a multi-threaded scanning technique that enables us to scan thousands of network-connected devices per minute.
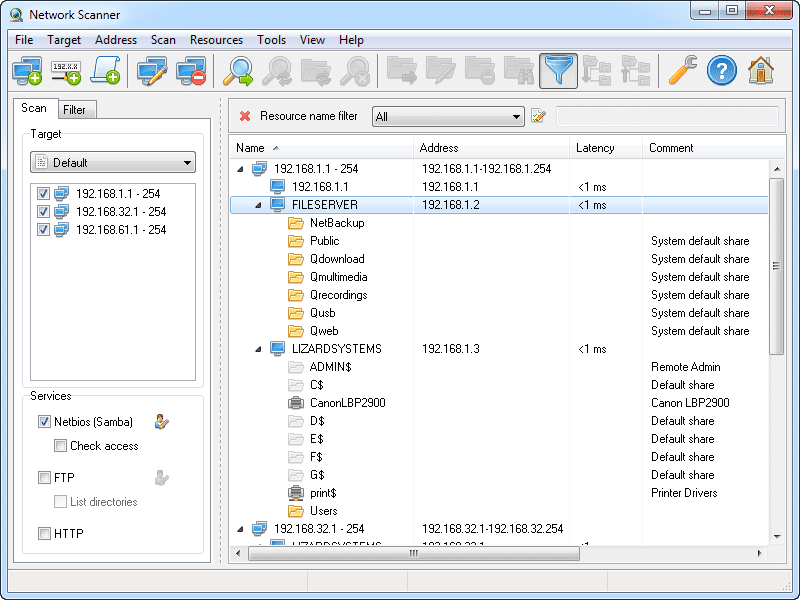
As you can see in the above screenshot, you get NetBIOS information, web server, FTP, and much more.
Results can be exported in HTML, TXT or XML format.
You can download a full-features trial for ten days to see if this works for you.
Advanced IP Scanner
One of the popular scanners downloaded more than 30 million times offer you to analyze your LAN in a minute.
Advanced IP Scanner is a portable executable, that you can use to access network shares, remote control via RDP, MAC address detection, etc.

It’s FREE, so give it a try to see how it goes.
Take a look at this detailed Advanced IP Scanner guide.
IP Range Scanner
A free software by Lansweeper is capable of scanning your network and providing network-connected device information.
You can schedule a network scan or run on demand whenever you want.

Some of the key features are:
- Execute custom commands
- Discover subnets
- Import network IP using CSV files
- Detect internal and external IP addresses
NMAP
This list won’t be complete without including NMAP. NMAP is usually known as a network security finder tool, but this can also be used to find IP address usage in a network.

Ex: if you want to find out what all IP is connected/online in the 10.0.0.1 network. You can just execute the below Nmap command.
nmap -sP 10.0.0.*Intruder
Not exactly IP Scanner but known as a network vulnerability scanner.
When it comes to security, a basic solution will not cut it. Intruder’s network vulnerability scanner is a powerful tool that is trusted by over 1,500 companies across the world. It’s able to find 10,000+ vulnerabilities, but its biggest USP is that it also helps you to reduce your external attack surface.
What this means is that as well as running continuous and thorough checks of your network, and discovering vulnerabilities as soon as they are released, it prioritizes exposures on your internet-facing systems to help you to tackle the biggest threats first.

It’s impossible to list all the vulnerabilities that Intruder could find lurking in your systems, they include configuration issues, missing patches, application bugs, encryption weaknesses, and more, but thanks to its seamless integration with tools such as Jira, Zapier, Microsoft Teams, and Slack, you can ensure your developers get the info they need to resolve these issues quickly.
With AWS, GCP, and Azure cloud connectors, technical teams can automatically synchronize their cloud IPs and hostnames to stay on top of their infrastructure.
Intruder offers a 30-day free trial of its network vulnerability scanner.
Wireshark
Scan your whole network with Wireshark – one of the most popular network analyzers in the world. It supports dark mode on your Windows and includes packet list sorting to help you with quick network protocol scanning. You will find a display filter functionality while utilizing the app to filter raw bytes in your network usage.

Wireshark is a free to download and often used to troubleshoot network related problems like packet drop, request block, frequent disconnection, connection reset, etc.
Zenmap
Zenmap is an open-source, multi-platform tool that supports Linux, Mac OS X, Windows, BSD, and more. This official Nmap Security Scanner GUI comes for free. The application is suitable for both seasoned and beginner-level professionals to utilize its advanced functionalities.
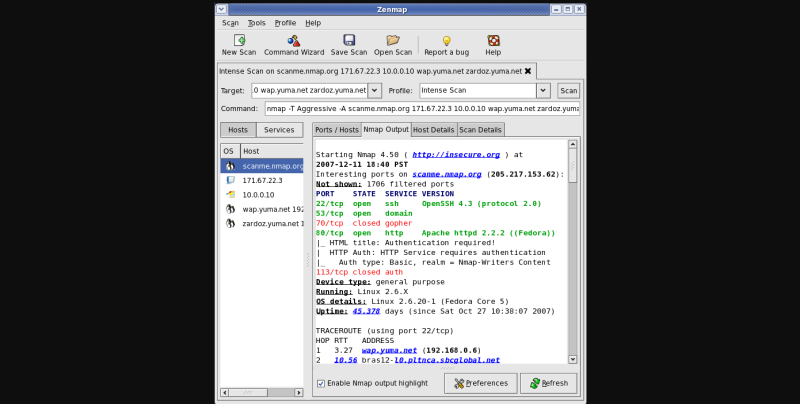
Nmap users can easily save the used scans in their systems as profiles to run them quickly when required without wasting time. With its command lines, you can create interactive sessions to run the scans flexibly. You can even save your scan results and view them later to discuss with your teams.
Zenmap enables you to compare the saved results with each other to know how they differ from time to time and make proper decisions at the right time. You can store the current scans in your searchable database to access them anytime easily.
These IP scanner tools should help you towards effective management of your network.
Conclusion
I hope the above gives you an idea about network IP scanner tools and helps you to manage them better.


