The eye-catching view of different Open-Source Intelligence (OSINT) tools that are available in the market.
In our daily lives, we search for a lot of information on the internet. If we don’t find the expected results, we usually quit!
But have you ever imagined what lies in those hundreds of page results? “Information”!
This can be possible only by using different tools. Tools play a significant role in searching for information but, without knowing the importance and usage of tools, it will not be helpful for the users.
Criminal IP
Criminal IP is a prominent OSINT search engine for cybersecurity, designed to collect and analyze threat intelligence by gathering real-time data on over 4.2 billion IP addresses and cyber assets. Through Criminal IP’s Asset Search and Domain Search, users can easily and quickly access desired asset information.

This includes a comprehensive range of data for pentesting, such as a 5-level risk score, current open port information and vulnerabilities (CVE codes), probability of phishing URLs, abuse records, fake favicon usage, connected IPs, and subdomain information.
Additionally, various search filters allow users to effectively extract the desired assets.

The search is not limited to phishing sites or malicious IPs, as it can also search for all assets connected to the internet, including IoT devices and certificates.
NexVision
NexVision is an advanced A.I.-powered OSINT solution that provides real-time intelligence from the Whole Web (Clear Web, Dark Web, and Social Media). It provides unprecedented access to Dark web searches through regular browsers like Chrome and Safari, without the use of anonymizing browser Tor.
If you’re looking to conduct background checks, due diligence, customer on-boarding compliance (KYC/AML/CFT), gather organization intelligence, third party intelligence, cyber threat intelligence, or even research on cryptocurrency addresses from a ransomware threat, NexVision provides accurate real-time answers.

NexVision is primarily used by the military and governments, but has since 2020, been commercially available and relied on by Fortune 500 companies and small-medium businesses (SMBs) alike for their intelligence and investigative needs. Their service includes a direct subscription to their SaaS solution and purchasing intelligence reports.
How it works:
In the first step, its A.I. powered engine continually collects data, analyzes it, and categorizes them, providing the largest commercially available data lake. In the second step, the engine uses machine learning to reduce false positives to provide highly accurate and contextualized results. This greatly reduces the man-hours and time required in investigations and the alert fatigue that analysts face when met with large amounts of irrelevant data. In the final step, all the results are reflected on the dashboard, where users can easily visualize and make informed decisions.
The dashboard allows users to set keyword alerts to monitor targets in real-time, conduct investigations, and analyze results whilst staying anonymous.
The software has a simple interface that is designed for entry-level analysts. Analysts can access and use military-grade and comprehensive intelligence without relying on scripts or writing a single line of code.
Its social media module monitors data from Meta (previously Facebook), Instagram, LinkedIn, Discord, Twitter, YouTube, Telegram, etc, and comes equipped with geolocation technology to determine the source and location of information dissemination.
Social Links is a software company that develops AI-driven solutions that extract, analyze and visualize data from open sources including social media, messengers, blockchains, and the Dark Web. Their flagship product SL Professional empowers investigators and data security professionals to reach their work objectives quicker and more effectively.

SL Professional offers a suite of custom-designed search methods spanning more than 500 open sources. The product’s advanced search queries, many of which rely on machine learning, allow users to filter the data as it is being gathered in a range of sophisticated ways.
However, Social Links OSINT solutions do more than just gather information; they also offer advanced analysis tools for refining data as you progress through investigations, returning accurate results for an ever more comprehensible picture of the investigation.
Features
- A professional bundle of 1000+ original search methods for over 500 open data sources including all major platforms across social media, messengers, blockchains, and the Dark Web
- Advanced automation features which leverage machine learning to deliver an expansive range of information retrieval, showing accurate results at remarkable speeds.
- Bespoke analysis tools enable data to be significantly enriched and molded to the user’s particular purposes.
- Seamless integration within your IT infrastructure
- Social Links offer training and support as part of their product packages.
For organizations who need the ultimate OSINT solution, Social Links also has an enterprise-grade platform SL Private Platform – an on-premise OSINT solution offering their widest range of search methods, full customization according to the users’ needs, and private data storage.
Shodan
Google is the most used search engine for all, whereas Shodan is a fantastic and goldmine search engine for hackers to see exposed assets.
When compared to other search engines, Shodan provides you the results that make more sense and related to security professionals. It mainly includes information related to assets that are being connected to the network. The devices may vary from laptops, traffic signals, computers, and various other IoT devices. This open-source tool mainly helps the security analyst in identifying the target and testing it for different vulnerabilities, passwords, services, ports, and so on.

Moreover, it provides users with topmost flexible searches by the community.
For example, let us consider the situation in which the single user can see the connected net cams, webcams, traffic lights, and so on. We will take a look at some use cases of Shodan:
- Testing “default Passwords”
- Assets with VNC viewer
- Using the RDP port open to testing the available assets
Google Dorks
Google Dorks came into existence in 2002, and it gives effective results with excellent performance. This query-based open-source intelligence tool is mainly developed and created to help users in targeting the index or search results appropriately and effectively.
Google Dorks provides a flexible way of searching for information by using some operators, and perhaps it is also called Google Hacking. These operators make the search easier to extract information. Below are some operators or indexing options provided by Google Docker, and they are:

- Filetype: This operator is mainly used to find the file types or to search for a particular string
- Intext: This indexing option is used to search for a specific text on a specific page.
- Ext: This is used to search for a specific extension in a file.
- Inurl: Used to search for the specific string or word in the URL
- Intitle: To search for the title or words mentioned above in the URL
Maltego
Maltego is designed and developed by Paterva, and it is one of the inbuilt tools in Kali Linux. This open-source intelligence tool is mainly used to perform a significant exploration against various targets with the help of several in-built transforms (and also provides the capability to write custom ones).
A programming language that you use in Maltego is written in Java and displays as a built-in pre-packaged in the Kali Linux. Once the registration process is done, then the users can use this tool to create and develop effective digital footprints of the particular target on the internet.

The expected results may happen to IP conversion, AS number is identified, Netblock is also identified, even the phrases and locations are also identified. These are all the icons in Maltego that provides a detailed view and information about all the icons.
You can even know more information about the target by digging more into the process. Finally, I can say that it is an excellent tool to track the footprints of each and every single entity over the internet. Maltego is available across all popular operating systems.
Harvester
Harvester is an outstanding tool for finding emails, subdomains, IPs, etc. from various public data.
Below example to find the subdomains using DNSdumpster.
[root@geekflare theHarvester]# python theHarvester.py -d geekflare.com -v -b dnsdumpster
*******************************************************************
* _ _ _ *
* | |_| |__ ___ /\ /\__ _ _ ____ _____ ___| |_ ___ _ __ *
* | __| _ \ / _ \ / /_/ / _` | '__\ \ / / _ \/ __| __/ _ \ '__| *
* | |_| | | | __/ / __ / (_| | | \ V / __/\__ \ || __/ | *
* \__|_| |_|\___| \/ /_/ \__,_|_| \_/ \___||___/\__\___|_| *
* *
* theHarvester 3.1.0.dev1 *
* Coded by Christian Martorella *
* Edge-Security Research *
* [email protected] *
* *
*******************************************************************
[*] Target: geekflare.com
[*] Searching DNSdumpster.
[*] No IPs found.
[*] No emails found.
[*] Hosts found: 3
---------------------
lab.geekflare.com:104.25.134.107
tools.geekflare.com:104.25.134.107
www.geekflare.com:104.25.134.107
[*] Virtual hosts:
------------------
[root@geekflare theHarvester]#TheHarvester is also available on Kali Linux. You can check the Kali Linux installation guide if you need it.
BTW, there are more tools to find subdomains.
Recon-Ng
Recon-ng is an effective tool to perform reconnaissance on the target.
The entire power of this tool lies completely in the modular approach. The power of modular tools can be understood for those used Metasploit. Recon-ng has various built-in modules that are used to target mainly while extracting information as per user needs. We can use the Recon-ng modules just by adding the domains in the workspace.
Workspaces are mainly created to carry out the operations inside it. The users will be redirected to the workspace as soon as it is created. Inside the workspace, the domain can be particularly specified using add domain <domainname>. Modules of Recon-ng are used to fetch information about the specific domain after they (domains) are added into the recon-ng.
Some of the excellent modules, such as google-site-web and bing-domain-web, are used to find further domains related to the first initial target domain. The result of these domains will be all the indexed domains to the search engines. Another catchy module is bing_linkedin_cache which is mainly used to fetch the details of the email addresses related to the domain. This module can also be used to leverage in performing social engineering.
Moreover, using other modules, we can get fetch the extra or additional information about targets. So finally, this open-source intelligence tool is a fantastic tool and also must be included in the toolkit of researchers.
TinEye
TinyEye helps you with reverse image search so you can find where the images appear online. Apart from reverse image search, its capabilities like computer vision, recognition of products, etc. can power your applications to make the images searchable on the web.
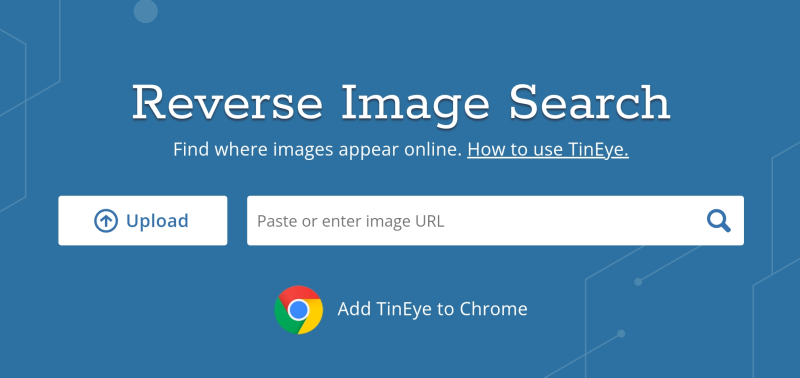
Utilize TinEye’s advanced image recognition feature to detect fraud and moderate content for your business.
Track how and where the images appear to verify the images online, and find the location of the image that is appearing on the web to check its compliance with copyright. In addition, TinEye’s MobileEngine enables you to connect the physical world with the digital through image recognition.
| ✅ Pros | ❌ Cons |
|---|---|
| Simple and easy-to-use tool | Pixel-support must be more to recognize images more clearly |
| Offers some free services and handy options | Not all the results are accurate |
| User-friendly and fast engine |
Upload your image or paste a URL for free to recognize the images.
AlienVault
AlienVault is an open-source intelligence platform that gives you free access to more than 20 million threat indicators. This helps you extract Indicators of Compromise (IoCs) from emails, threat reports, PCAPs, blogs, and more.

Utilize Alien Labs OTX sandbox to analyze malware in your files or URLs. Just submit the file and URL and let AlienVault handle the rest. It allows you to create special groups and join to investigate the threats.
Connect AlienVault with other security tools via STIX/TAXII, SDK, DirectConnect API, and more. You can get the latest information about the threats, attacks, malicious actors, and other necessary information from the global intelligence community.
| ✅ Pros | ❌ Cons |
|---|---|
| Offers unified threat detection | UI could have been better |
| Connects with other security tools to give extra layer of security | Dashboards are a little tricky to navigate |
| Reporting feature is great | |
| Opportunity to connect with global threat intelligence community |
Download and install the agent on your device for free and start analyzing all the threats.
What is Open-Source Intelligence?
Open-Source Intelligence, in short, called OSINT, refers to the collection of information from public sources to use it in the context of intelligence. As of today, we are living in the “world of the internet” its impact on our lives will have both pros and cons.
The advantages of using the internet are, provides lots of information and easily accessible by everyone. Whereas, the disadvantages are misusing the information and spending a lot of time on it.
Now, here comes the existence of OSINT tools, which are mainly used to collect and correlate information on the web. Information can be available in various forms; it can be text format, file, image, and so on. According to the CSR Report for Congress, it has been said that Open-Source Intelligence has been produced from the public information that is correctly disseminated, collected, and exploited effectively. And makes this information available for the users to address a specific intelligence requirement.
Why do we require OSINT tools?
Let us consider one situation or scenario in which we need to find information related to some topics on the web. For this, you need first to search and do analysis until you get the exact results, this consumes a lot of time. This is the main reason why we require intelligence tools because the process mentioned above can be done within seconds using these tools.
We can even run multiple tools to collect all the information related to the target, which can be correlated and used later.
Conclusion
Penetration testing or cybersecurity investigation is challenging, and it requires information from various sources. I hope the above ONIST tools help you with that.


