Assess your data center security flaws before bad guys do!
One of the many news we hear in the current digital era is a cyber attack. It disturbs the business, damages the reputation, and panics end users.
How do you ensure your network infrastructure is capable of mitigating cyber attacks?

Those days are gone when you rely on annual or quarterly penetration test results. In the current era, you need an automated breach attack simulation (BAS), continuous assets scanning, and, of course, protection.
Thanks to the following tools, which let you simulate the real attack against your data center so you can review the results and take action. The best part is some of the tools that allow you to automate the action.
Ready to prepare for the worse?
- 1. Infection Monkey
- 2. TitanHQ SAT & Phishing Simulation
- 3. NeSSi2
- 4. CALDERA
- 5. AttackIQ
- 6. Scythe
- 7. XM Cyber
- 8. Randori
- 9. Picus
- Show less
You can trust Geekflare
At Geekflare, trust and transparency are paramount. Our team of experts, with over 185 years of combined experience in business and technology, tests and reviews software, ensuring our ratings and awards are unbiased and reliable. Learn how we test.
1. Infection Monkey
Are you running your application in the Cloud? Use Infection Monkey to test your infrastructure running on Google Cloud, AWS, Azure, or premises.
Infection Monkey is an open-source tool that can be installed on Windows, Debian, and Docker.
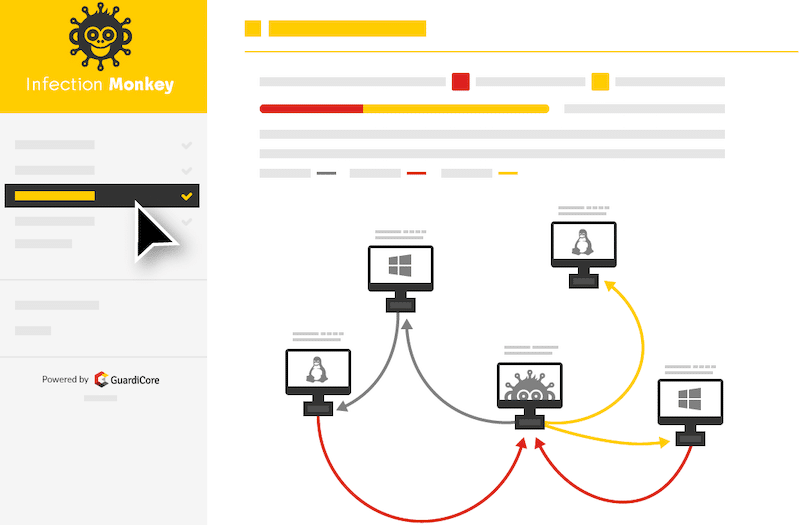
You can run an automatic attack simulation for credential theft, misconfiguration, compromised assets, etc. Some of the worth mentioning features.
- Non-intrusive attack simulation, so it doesn’t impact your network operations.
- Comprehensive audit report with an actionable recommendation to harden the web servers or other infrastructure
- Low CPU and Memory footprint
- Visualize network and attacker map
If you are a CISO or from the security team, then you will love the report. It is FREE, so give it a try today.
2. TitanHQ SAT & Phishing Simulation
TitanHQ offers human security awareness training. It automatically manages security training based on behavioral triggers. It provides real-time intervention awareness with proven effectiveness.
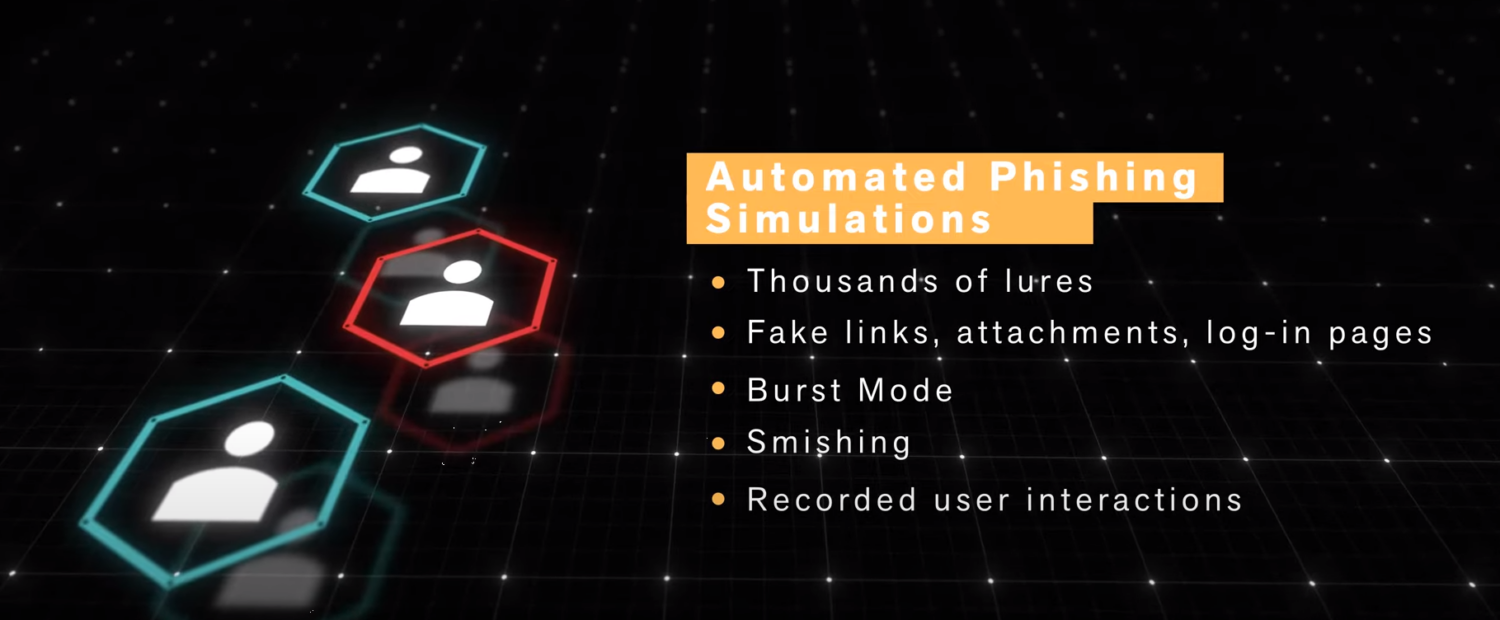
This SaaS product can be easily deployed. SafeTitan delivers behavioral training to individual employees in their exact moment of need that contributes to positive behavior change.
Key Features
- Delivers real-time contextual training
- Thousands of templates for automated phishing attack simulation
- Gamified and interactive training program with short testing
- Enterprise-level intelligent reporting for 360° organizational view
- Cyber knowledge assessment on security and compliance best practices
- Ensures compliance with ISO, GDPR, HIPAA, PCI, EU NIS, and Cyber Essentials
- Unlimited phishing simulations
- Unlimited Cyber Knowledge Assessment Quizzes
Get a free demo to see how it can maximize your ability to secure your business and employees, and minimize security incidents and related costs.
3. NeSSi2
NeSSi2 is an open-source, powered by JIAC framework. NeSSi stands for Network Security Simulator, so you can guess what it does. It focuses mainly on testing intrusion detection algorithms, network analysis, profile-based automated attacks, etc.

It requires Java SE 7 and MySQL to set up and runs.
4. CALDERA
An adversary emulation tool. CALDERA supports only the Windows Domain network.

It leverages the ATT&CK model to test and replicate the behavior.
Alternatively, you may also try Metta by Uber.
5. AttackIQ
AttackIQ is one of the popular security validation scalable platforms to strengthen your data center security. It is an offensive-defensive system to help security operation engineers exercise red team capabilities.
The platform is integrated with a vital framework – MITRE ATT&CK. Some of the other features are.
- Powered by AttackIQ research team and industry security leader
- Customize the attack scenario to mimic the real-world threats
- Automate the attacks and receive continuous security status reports
- Lightweight agents
- Works on a primary operating system and integrates well with existing infrastructure
They offer two weeks FREE trial to try their platform. Give a try to see how well is your infrastructure posture.
6. Scythe
Know where your organization stands in security risk exposure. Scythe platform got a powerful and easy-to-use workflow to create and launch a real-world cyber threat campaign. With the help of data, you can analyze your security endpoints in real time.
Scythe is offered as a SaaS model or on-premises. Whether you are a red, blue, or purple team – it fits all.
If you are interested in learning red team activity, then check out this online course.
7. XM Cyber
XM Cyber offers an automated advanced persistent threat (APT) simulation solution. Stay ahead of the attacker.
You can select the target to run and setup on-going attacks and receive a prioritized remediation report—some highlights about the tool.
- Customize the attack scenario based on needs
- Visualize attack path
- Up-to-date attack methods
- Best practices and policies recommendation
8. Randori
Randori is a reliable, automated red team cyber-attack platform for testing security systems’ effectiveness in preventing attacks. It can generate and launches real exploits and attacks the same way an attacker would do but in a safe way.
The platform has benefits such as;
- Assessing entire security solutions and identifying weaknesses.
- Provide insight into how an attack would see the organization’s assets.
- Allows teams to simulate real attacks safely toward the organization’s IT systems.
- Provides real-time attack target analysis
- It allows you to test defenses, identify weaknesses, and stop assuming you are secure.

9. Picus
Picus is a security and risk management solution that enables you to assess, measure, and mitigate vulnerabilities continuously, hence enabling your organization to stay ahead of cybercriminals. With an easy-to-configure and use dashboard, the Picus security breach and attack simulation platform provides real attacks to test your defenses and determine if they offer adequate protection.

It has benefits such as;
- Extensive threat database and corresponding protection measures
- Real-time identification of weak as well as strong security layers, – allowing teams to identify and address security gaps quickly.
- Fine-tune and maximize the complex security technologies
- Enables quick identification of vulnerabilities and suggests the optimum mitigation measures to reduce risks.
- Provides Real-time visibility into an organization’s security attacks preparedness and ability to address weaknesses.
Conclusion
Managing an organization’s IT security risk is challenging, and I hope the above tools help you implement world-class control to lower risk exposure. Most of the listed tools offer a free trial, so the best thing to do is to try to see how they work and go for the one you like.


