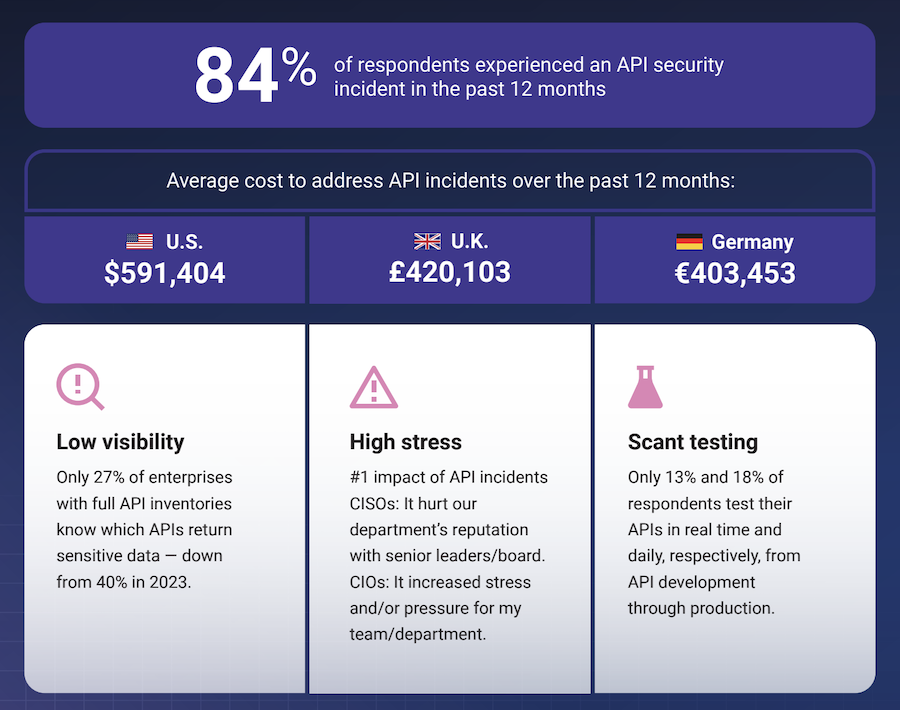
Application and API attacks have surged recently. According to the API Security Impact Study 2024, 84% of enterprises have experienced API security incidents in 2024. So, you must find and fix vulnerabilities in your App or API to prevent hackers from exploiting them.
Of course, using a DAST scanner is a proven way to detect security issues in your running App or API. However, finding the right DAST scanner can be tricky, especially when you’re new to scanning tools. These tools tend to have different features for various use cases, which can be confusing if you’re a beginner.
To make it easier, I have prepared a list of the best DAST tools based on my thorough research, participation in trials and demos, and reading of product documents. I’ve also verified vendors’ claims using multiple data sources, including independent B2B review sites like G2, TrustRadius, and Capterra.
Check out the list below! 👇🏼
- 1. Probely
- 2. Invicti
- 3. Indusface WAS
- 4. Rapid7 InsightAppSec
- 5. StackHawk
- 6. SOOS DAST
- 7. Veracode Dynamic Analysis
- 8. Acunetix
- 9. Detectify
- 10. Intruder
- 11. Burp
- 12. Checkmarx DAST
- Show less
You can trust Geekflare
At Geekflare, trust and transparency are paramount. Our team of experts, with over 185 years of combined experience in business and technology, tests and reviews software, ensuring our ratings and awards are unbiased and reliable. Learn how we test.
Top DAST Scanners Comparison
For a brief overview, I’ve created a comparison table below for the DAST scanners on this list based on key features, availability of a free trial, and pricing.
| DAST Scanner | Key Features | Free Trial | Pricing |
|---|---|---|---|
| Probely | Noise-free scanning, low false positives, compliance support, customizable scanning, API scanning, integration with CI/CD pipelines | ✅ | On-request |
| Invicti | DAST + IAST approach, open-source component detection, broad vulnerability coverage | ❌ | On-request |
| Indusface WAS | Malware scanning, penetration testing, zero false positives, public asset inventory, defacement detection, VAPT | ✅ | $59/app/month |
| Rapid7 InsightAppSec | Protection from 95+ attack types, attack replay, scan scheduling, misconfiguration scanning | ✅ | $175/app/month |
| StackHawk | API testing for REST, SOAP, GraphQL, custom test scripts, prioritized scan results, CI/CD integration | ✅ | $42 per code contributor/month |
| SOOS DAST | Open-source ZAP scanner, unlimited domain scanning, CI/CD integrations, OSS vulnerability scanning, security misconfiguration detection | ✅ | $90/month |
| Veracode Dynamic Analysis | Cloud-native scanning, firewall-protected scanning, scan parameter customization, API security scanning, remediation guidance | ✅ | On-request |
| Acunetix | Scans script-heavy sites, 12,000+ vulnerabilities, combines DAST + IAST, open-source component analysis, CI/CD integration | ❌ | On-request |
| Detectify | SPA and JavaScript-heavy site scanning, tailored security tests, authenticated scanning, frequent security test updates | ✅ | On-request |
| Intruder | Emerging threat scans, flexible scheduling, remediation scans, API scanning, integration with compliance tools | ✅ | $99/month |
| Burp Suite | Unlimited automated DAST scanning, API scanning, browser-powered scanning, custom configurations, OAST integration | ✅ | On-request |
| Checkmarx DAST | SAST + DAST correlation, live API scanning, security risk assessment, SDLC integration, unified AppSec platform | ❌ | On-request |
In the sections below, I’ve discussed 12 of the shortlisted DAST scanners in detail, including their features, my testing experience, and pricing.
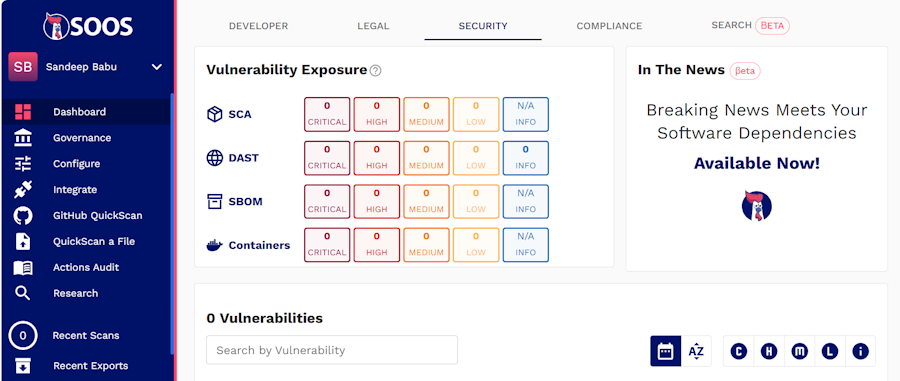
1. Probely
You can use it to fulfill web security compliance requirements by generating detailed compliance reports and showing those reports as evidence of compliance. You can easily integrate Probely with CI/CD tools, issue trackers, and messaging apps.
Probely Features
I accessed the Probely free trial to explore its features and liked how it informs you about vulnerabilities. It categorizes vulnerabilities into three categories of severity—Low, Medium, and High, with CVSS (Common Vulnerability Scoring System) score. As a result, you can quickly prioritize vulnerability management.
Probely also provides tips and tricks on fixing vulnerabilities it detects in your app or application, as shown in the screenshot below.
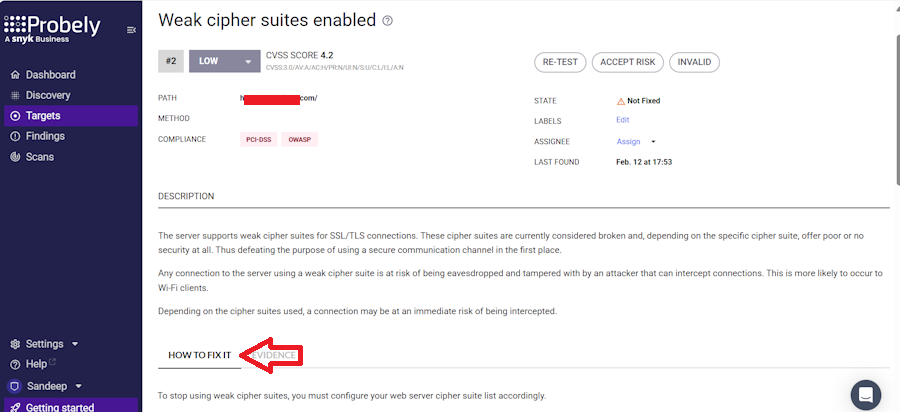
I also found the dashboard informative and easy to navigate.
Probely Pricing
It offers a forever-free plan with 5 free scan hours/month. The Enterprise plan follows custom pricing. Probely provides a free 14-day, fully-featured trial. You can also request a demo to have a guided product tour.
2. Invicti
Invicti can be integrated with 50+ tools, including CI/CD, issue trackers, collaboration tools, and more.
Invicti Features
During my research and use of the demo, I noted that Invicti helps fix vulnerabilities faster by automatically locating them. The IAST sensor connects to the application runtime while the DAST engine scans for vulnerabilities.
When DAST finds an issue, IAST provides detailed insights, like file names and line numbers. It is a good feature for fast vulnerability remediation. Also, its proof-based scanning minimizes false positives.
Invicti Pricing
Invicti pricing is available on request. A free demo is available to explore its features.
3. Indusface WAS
Indusface WAS Features
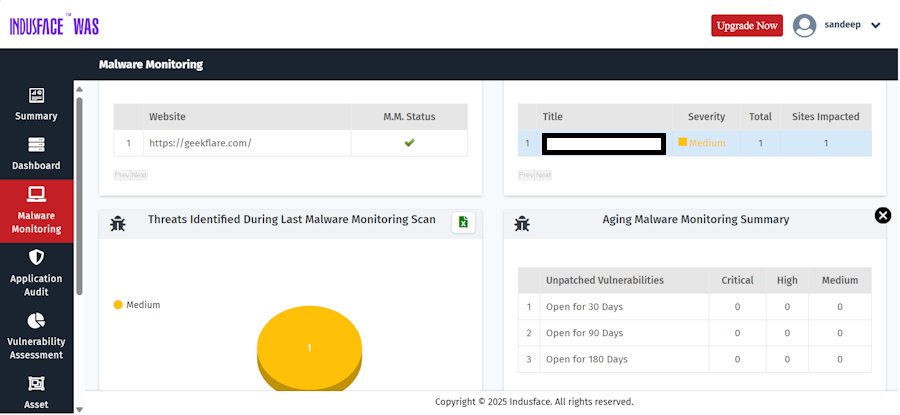
Indusface WAS Pricing
Indusface WAS pricing starts at $59/app/month. It offers a 14-day free trial.
4. Rapid7 InsightAppSec
I liked that InsightAppSec enables you to collaborate at speed. Its rich reporting and integrations make informing compliance and development stakeholders seamless. You can easily tailor reports to several compliance regulations, such as HIPAA, PCI-DSS, and more.
InsightAppSec’s scan engines support both on-prem and cloud-based deployment. You can easily integrate InsightAppSec into your dev workflows.
Rapid7 InsightAppSec Features
To explore InsightAppSecc thoroughly, I subscribed to its free trial and scanned a website I control. It delivered the report in 29 minutes. It tested my site for more than 95+ attacks, including OWASP Top 10, misconfiguration, and more. I found its dashboard intuitive and liked its ability to schedule and blackout scans.
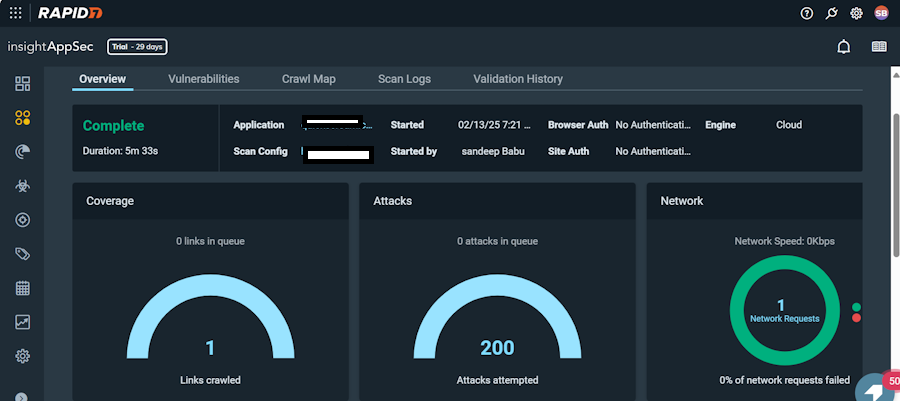
InsightAppSec Pricing
InsightAppSec pricing starts at $175/month per app. The company offers a generous 30-day free trial. You can also watch an online demo to understand the product better.
5. StackHawk
The platform offers detailed App Request & Response data, developer-friendly explanations, and resources to investigate issues quickly and efficiently. It offers 4 packages for users: Free, Pro, Enterprise, and Custom.
You also get to run technology-specific API Scan Configs.
StackHawk Features
StackHawk Pricing
StackHawk pricing starts at $42 per code per contributor (5 contributors minimum). It offers a 14-day free trial.
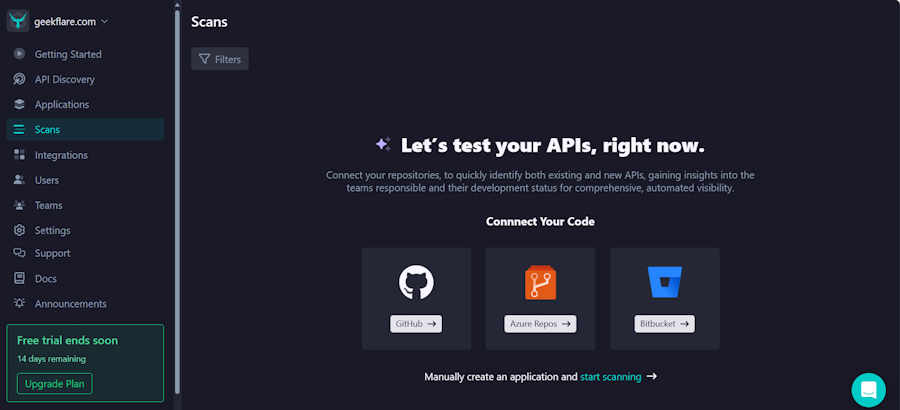
6. SOOS DAST
The platform leverages Industry-Standard Open Source ZAP Scanner with added features to offer your application broad security coverage. It can also push issues to GitHub’s Security Panel.
With the solution, you can scan your app and API for security issues, such as SQLi, security misconfigs, XSS, missing security headers, and more.
SOOS DAST Features
SOOS DAST Pricing
SOOS DAST pricing starts at $90 per month. A free trial is available.
7. Veracode Dynamic Analysis
Veracode DAST Features
I chose Veracode Dynamic Analysis because it provides instant, accurate results that can help you quickly identify security issues. Plus, the remediation guidance is informative. As a result, you can fix vulnerabilities efficiently, while on-demand expertise offers support when needed.
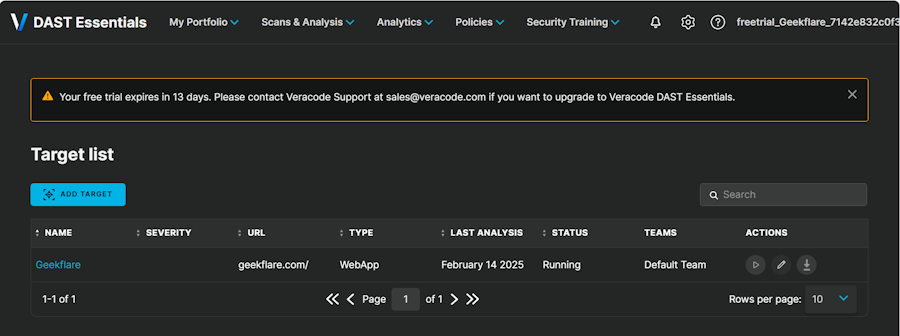
Veracode DAST Pricing
Veracode DAST pricing is available on request. The company offers a 14-day trial and product demo.
8. Acunetix
Acunetix comes with a powerful application security solution that identifies security vulnerabilities in your websites, applications, and APIs. It can automate scanning in hard-to-reach, password-protected areas.
The platform offers an accurate view of your attack surface and assigns a score to vulnerabilities it detects. This helps you prioritize vulnerability management. Also, it allows you to scan multiple environments simultaneously.
Acunetix comes with SCA to scan open-source components of your web application. It reduces false positives with proof of exploit and lets you know the exact location of vulnerabilities to save time on vulnerability fixing. Easy scan scheduling allows you to automate scanning.
You can integrate it with your CI/CD, issue tracker, WAF, and other tools.
Acunetix Features
- Scans script-heavy websites, single-page applications (SPAs), and applications built with HTML5 and JavaScript
- Identifies over 12,000 web vulnerabilities, including SQL injection and XSS
- Merges results from Dynamic (DAST) and Interactive (IAST) security testing for deeper insights
- Analyzes open-source components for security risks, licensing issues, and outdated dependencies
- Checks hard-to-find unlinked files and API endpoints that other scanners can easily miss
I like that you can integrate Acunetix easily with your web application firewall to stay secure while you fix security issues.
Acunetix also lets you know if your application security is improving over time with visual trends, helping you tweak your application security strategy to improve it.
Acunetix Pricing
Acunetix pricing is available on request. The company offers a free demo.
9. Detectify
Detectify automatically scans custom-built applications, finds business-critical security vulnerabilities, and strengthens your web app security with Application Scanning.
The solution offers you a complete overview of vulnerabilities. You will have expert remediation tips to address detected security issues. You can filter and tag findings to initiate the remediation process faster.
The Detectify application scanner easily integrates with OpsGenie, Splunk, Jira, Slack, PagerDuty, and more for better collaboration.
You can export results in PDF, XML, JSON, and more, and share scan profiles with your team members.
Detectify Features
- Scans complex web apps, including SPAs and JavaScript-heavy sites, for deep insights
- Finds diverse vulnerabilities with an evolving fuzzing engine
- Tailors security testing by mapping your tech stack and applying the most relevant tests
- Scans authenticated areas like admin panels and user settings for hidden risks
My favorite feature of Detectify is that it updates the scanner with new security tests every week. So you will have an up-to-date scanner to scan your application.
Detectify Pricing
Detectify’s application scanning pricing is quote-based. It offers a 14-day free trial and a free demo to explore the product.
10. Intruder
Intruder web application vulnerability scanner helps you detect and fix vulnerabilities in your web application and its underlying infrastructure.
Its DAST scanner is powered by ZAP and performs over 75+ checks on your application, including security misconfiguration, injection flaws, and more.
The platform allows you to schedule recurring scans at flexible intervals. It automatically detects new vulnerabilities with proactive emerging threat scans.
The system prioritizes security risks intelligently and provides remediation advice, helping you focus on the most critical issues. This ensures continuous scanning for vulnerability detection and remediation for your web applications with minimal manual effort.
Additionally, Intruder lets you run remediation scans, so you don’t have to run full scans to verify if your remediation efforts were fruitful.
It can also scan your API for security vulnerabilities. For compliance support, you can easily integrate Inrtuder with Drata.
Intruder Features
- Quick setup in under 10 minutes
- API to integrate with your CI/CD pipeline
- Add-on penetration testing
- Easy integration with Jira, GitLab, GitHub, and more
I chose Intruder for its Emerging Threat Scans, which automatically detect and scan for new critical vulnerabilities as they arise. I’ve also verified from Intruder’s product documents that it supports unlimited users and unlimited ad-hoc scans.
Intruder Pricing
Intruder application scanner pricing starts at $99/month. A free 14-day trial is available to explore its features.
11. Burp
Burp Suite’s Enterprise plan offers unlimited automated DAST scanning. It provides you with complete visibility into the attack surface of your application or API.
A major advantage is that it integrates with CI/CD pipelines, vulnerability management platforms, and issue-tracking tools like Jira and Trello. It also supports custom Burp extensions, GraphQL API, and SSO for easy access.
Burp Suite Enterprise scans your web portfolio for vulnerabilities aligned with PCI DSS standards, OWASP Top 10, and more to help you meet various compliance.
You can also track security changes over time by visually comparing deltas and updates. This helps you understand how your attack surface evolves. Another great feature is that it supports Role Based Access Control (RBAC).
Burp Suite Enterprise Features
- Out-of-box configurations for preset scan modes
- API scanning to detect vulnerabilities in API endpoints
- Authenticated scanning for restricted areas
- Browser-powered scanning to analyze and navigate complex SPAs
- Custom and scalable configurations to control scan depth, vulnerability reports, and speed
I liked that Burp Suite Enterprise allows you to add Out-of-band Application Security Testing (OAST) to DAST, improving scanning accuracy and efficiency.
Burp Scanner provides clear remediation advice for every detected issue. PortSwigger Research and the Web Security Academy offer expert guidance, helping you fix vulnerabilities effectively.
Burp Pricing
You can deploy Burp Suite Enterprise in two ways: self-hosted or through PortSwigger’s secure cloud. The pricing is available on request. A free trial is available to explore features.
12. Checkmarx DAST
A single platform enables you to run SAST and DAST scans, offering a seamless AppSec experience. Additionally, it supports various languages and integrations.
As Dynamic Application Security Testing (DAST) is an add-on to Checkmarx One, you can use other Application Security (AppSec) programs available with it.
These include Static Application Security Testing (SAST), Software Composition Analysis (SCA), Supply Chain Security (SCS), API Security, Container Security, and Infrastructure as Code (IaC) Security.
Checkmax DAST Features
- Correlation of SAST and DAST findings in a single platform for better vulnerability remediation
- Integrate seamlessly with the software development lifecycle
- Scan live APIs to detect real-time vulnerabilities
- See API vulnerabilities discovered by both SAST and DAST in a single location
Checkmarx DAST Pricing
Checkmarx DAST is available as an add-on with Checkmarx One and follows custom pricing. You need to contact the company to get pricing details. A free demo is available.
What Is DAST and How Does It Work?
Scanning the Application
Carrying Out Simulated Attacks
Identifying Vulnerabilities
Sending Report
5 Key Features Your DAST Tool Should Have
Here are key features you should look for when shopping for a DAST scanner.
1. Vulnerability Coverage
Vulnerability coverage is the most critical feature of a DAST scanner. So, you should make sure that the DAST scanner you pick covers a wide range of vulnerabilities, such as:
- Injection attacks
- Authentication & authorization flaws
- Security misconfiguration
- Sensitive data exposure
- Cross-site request forgery
- API security issues.
I recommend booking a demo with multiple dynamic application security testing tools to see which tool covers a wide range of vulnerabilities.
2. Automated Scan
A good DAST tool offers automated scanning, which reduces the hassle of manually initiating security scans. So, make sure the DAST scanner you are considering allows you to schedule scans.
3. Integrations
The tool must support standard integrations like CI/CD pipelines, issue trackers, and security platforms. Broad and seamless integration support helps you enforce a secure app development culture.
4. Real-time Insights
Detailed reports and real-time alerts help your security teams respond quickly. The DAST tool should also provide actionable insights through continuous and automated security checks for faster remediation.
5. Compliance Support
Meeting security standards like OWASP, GDPR, and PCI DSS is important to avoid legal liabilities. These standards will also depend on the nature and location of your business.
So, pick a DAST tool that helps you meet various compliances applicable to your business.
5 Benefits of DAST Scanners
How DAST Is Different Than SAST
Conclusion
-
 EditorAnirban Choudhury is as an editor at Geekflare, bringing over 7 years of experience in content creation related to VPNs, Proxies, Hosting, Antivirus, Gaming, and B2B2C technologies.
EditorAnirban Choudhury is as an editor at Geekflare, bringing over 7 years of experience in content creation related to VPNs, Proxies, Hosting, Antivirus, Gaming, and B2B2C technologies.



