
Proton VPN
Proton VPN is a highly secure and reliable VPN service known for its robust encryption, user-friendly interface, and extensive server network, catering to users seeking enhanced online privacy and versatile browsing capabilities.
Pros
-
6,300+ servers in 100 countries, 10Gbps, and Tor over VPN servers.
-
Offers a kill switch, DNS leak protection, split tunneling, and Secure Core.
-
Comes with unique features like VPN Accelerator, NetShield Adblocker, and VPN Profiles.
Cons
-
The free plan has limitations compared to the premium plans in terms of server access and features.
-
The interface lacks customization, and there is no flexibility with certain options.
You can trust Geekflare
Imagine the satisfaction of finding just what you needed. We understand that feeling, too, so we go to great lengths to evaluate freemium, subscribe to the premium plan if required, have a cup of coffee, and test the products to provide unbiased reviews! While we may earn affiliate commissions, our primary focus remains steadfast: delivering unbiased editorial insights, and in-depth reviews. See how we test.
Technology has made accessing the web easier, yet it has also magnified risks to users’ privacy and security. As a result, safeguarding yourself and maintaining anonymity online has become essential.
While there are plenty of solutions to address this, none are as simple and reliable as a VPN. With the blooming cybersecurity risks, these numbers are expected to grow significantly in the coming years.
As a mainstream consumer, you have a sea of service providers to choose from, but picking the right one can be tricky. If you’re considering Proton VPN as your savior when browsing the web, check out this review before deciding.
Getting started with Proton VPN
It is compatible with various devices and operating systems, including Windows, macOS, Linux, iOS, and Android. The installation is straightforward regardless of the platform, and the company claims to offer both free and paid users a strong privacy and user experience.
In this review, I will examine multiple aspects closely to test its potential and determine whether it lives up to the expectations and is a worthy choice compared to other leading VPNs.
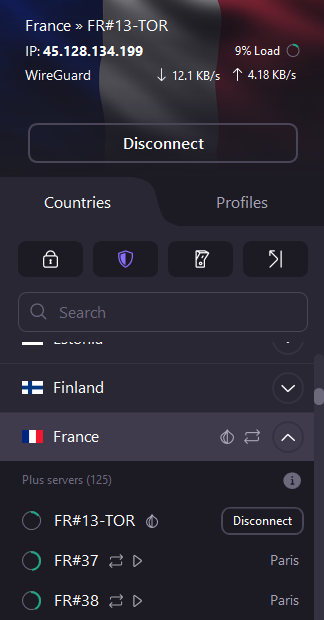
Proton VPN’s Interface
Proton VPN follows in the footsteps of the most prominent VPNs by offering a single-screen interface, more like a dashboard, featuring all options. While this might take a few minutes to get used to, navigating around the interface is buttery smooth.

When I tested Proton VPN for the first time, the futuristic theme and the speed graph were particularly impressive. Moreover, the subtle animations when connecting to a server, along with the minor details like the country flag displayed in the background, certainly added to the overall user experience.

Above all, the quick access to multiple features right from the connection screen is noteworthy, along with different user profiles that significantly increase usability. However, Proton VPN lacks customization, and making the settings easily available with the symbolic Gear icon on the dashboard would have seemed like the right way to go. If you do want to access the settings, it can be found tucked away with the other options inside the menu.
Proton VPN’s Encryption
Encryption is crucial to secure the data transmitted between a user’s device and the VPN server, ensuring privacy, confidentiality, and protection against potential eavesdropping or cyber threats.
Proton VPN ensures that you are always covered, thanks to the multiple VPN protocols it offers. While the absence of an option to change the encryption can be a letdown for a few, the AES-256 or ChaCha20 is arguably the best encryption standard a VPN could offer.
Considering the necessity of encryption, I have tested Proton VPN with Wireshark, a free and open-source packet analyzer, and here are the results below:
Capturing Packets with and without Proton VPN
I started visiting unsecured HTTP webpages on my browser and have captured the packets with and without the Proton VPN. Starting without VPN, the results were predictable, where Wireshark detected the HTTP webpage as unsecured and highlighted it in light green.
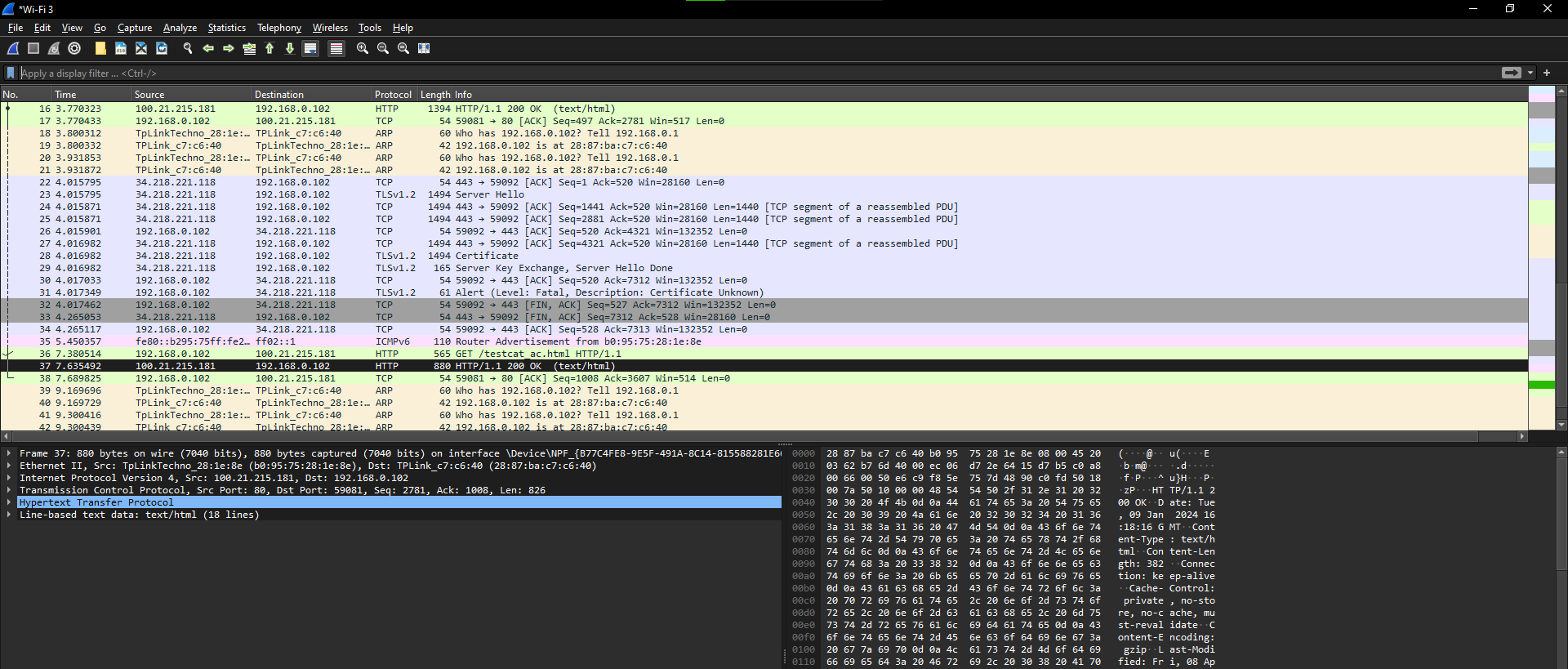
Next, I turned on the Proton VPN, left the defaults as is, and started recapturing the packets. To my surprise, HTTP webpages were detected by Wireshark. However, on the bright side, they aren’t highlighted in green and are detected secure and considered part of an existing conversation.
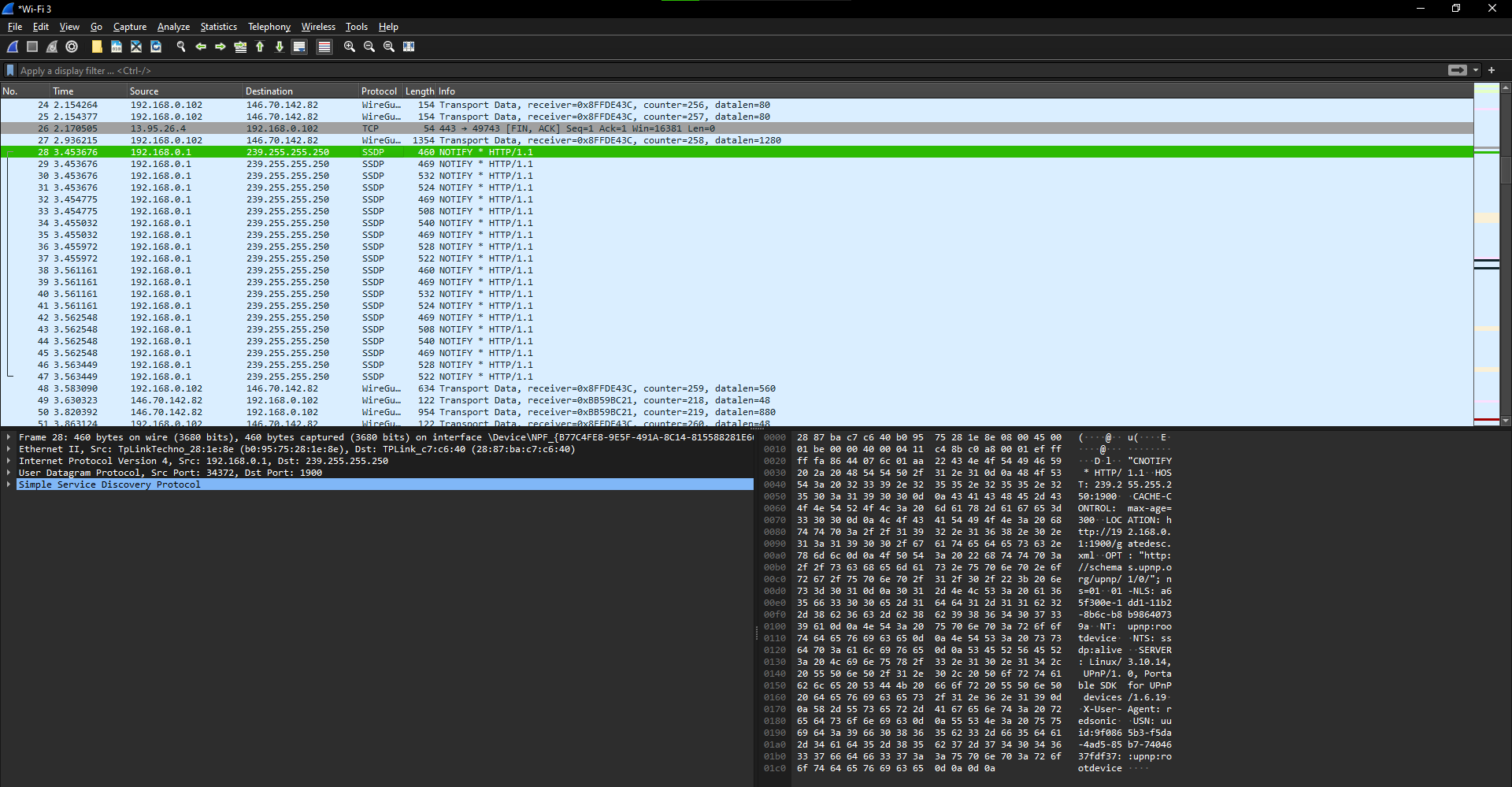
To cross-verify, I changed the Proton VPN protocol to OpenVPN, set the transport as UDP, and started recapturing the packets visiting unsecure webpages. Now, the results state otherwise, and the packets aren’t displayed as HTTP or SSDP protocols.
Following Packets with and without Proton VPN
With the packets displayed and everything seems promising, I followed the packets as a precautionary measure to find data leaks that happen when the encryption is poor.
The goal of this test is to follow a packet and find out if the conversation is readable. For this purpose, I performed recaptures with different scenarios, and here are the results:
Starting with the capture done without connecting to the VPN, I followed the packet highlighted in green and noticed the conversation was readable. However, the conversation also contains personal information, which is undesirable.
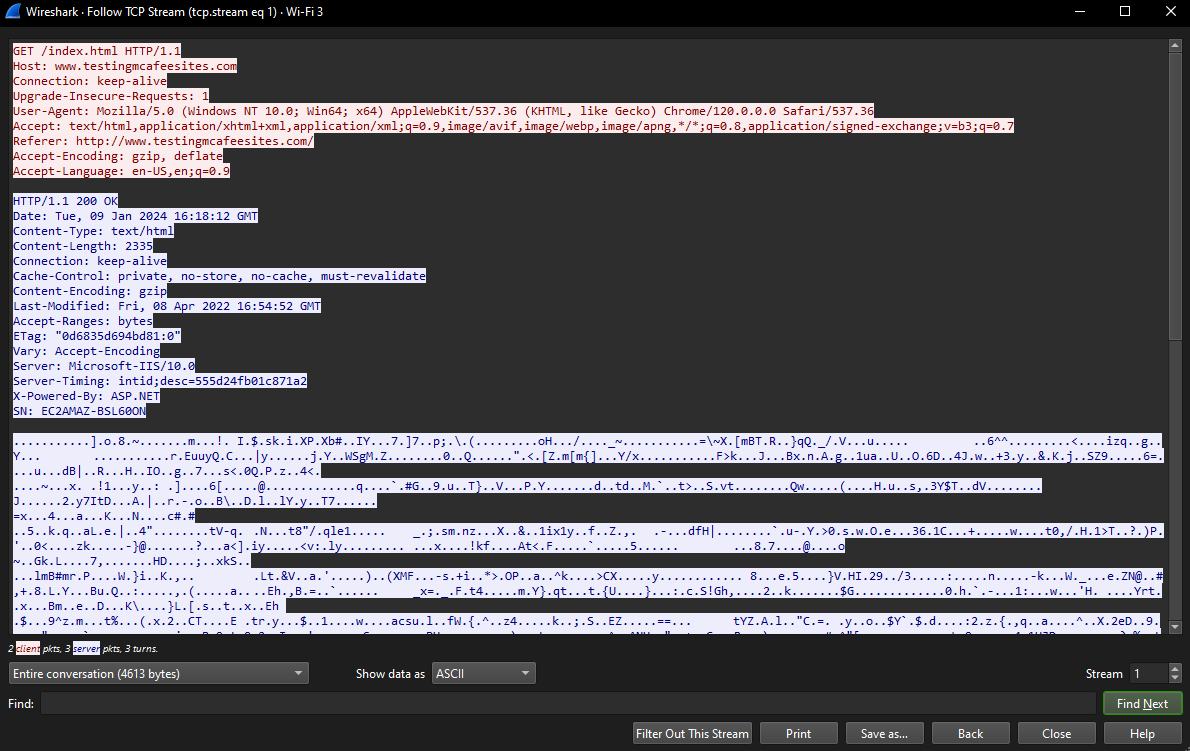
Considering the conversation readable and containing personal information, I turned on Proton VPN and recaptured the packets. While Wireshark hasn’t highlighted any packet in green, the conversation turned out to be readable, and even though it doesn’t feature any personal information, it wasn’t a good sign for Proton VPN.
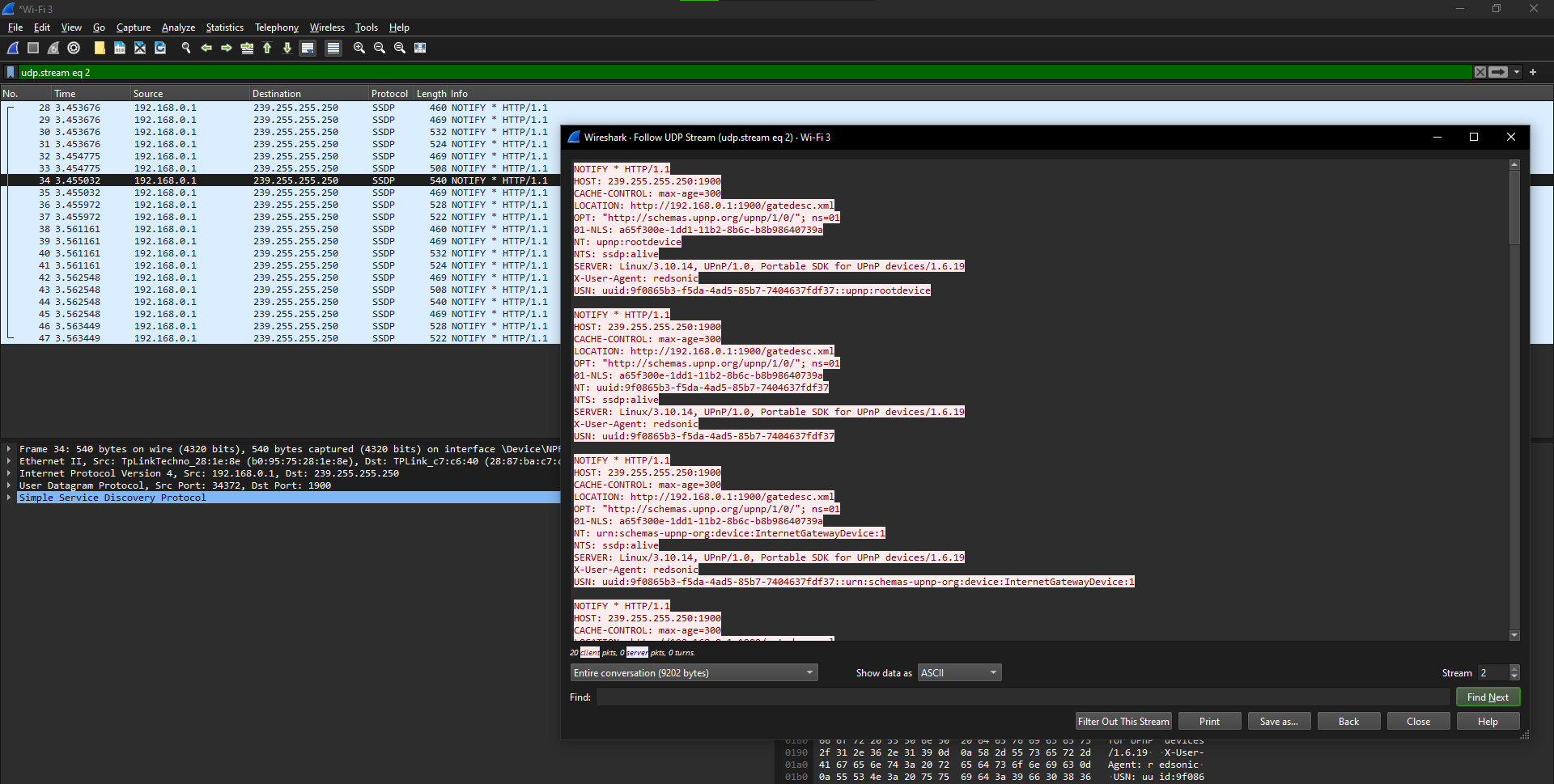
At this stage, I wouldn’t have proceeded further in most cases, but I decided to try changing the VPN protocol to OpenVPN-UDP and performed a capture. In this scenario, none of my activities that involved visiting the HTTP website were displayed. Also, the conversation was completely encrypted.
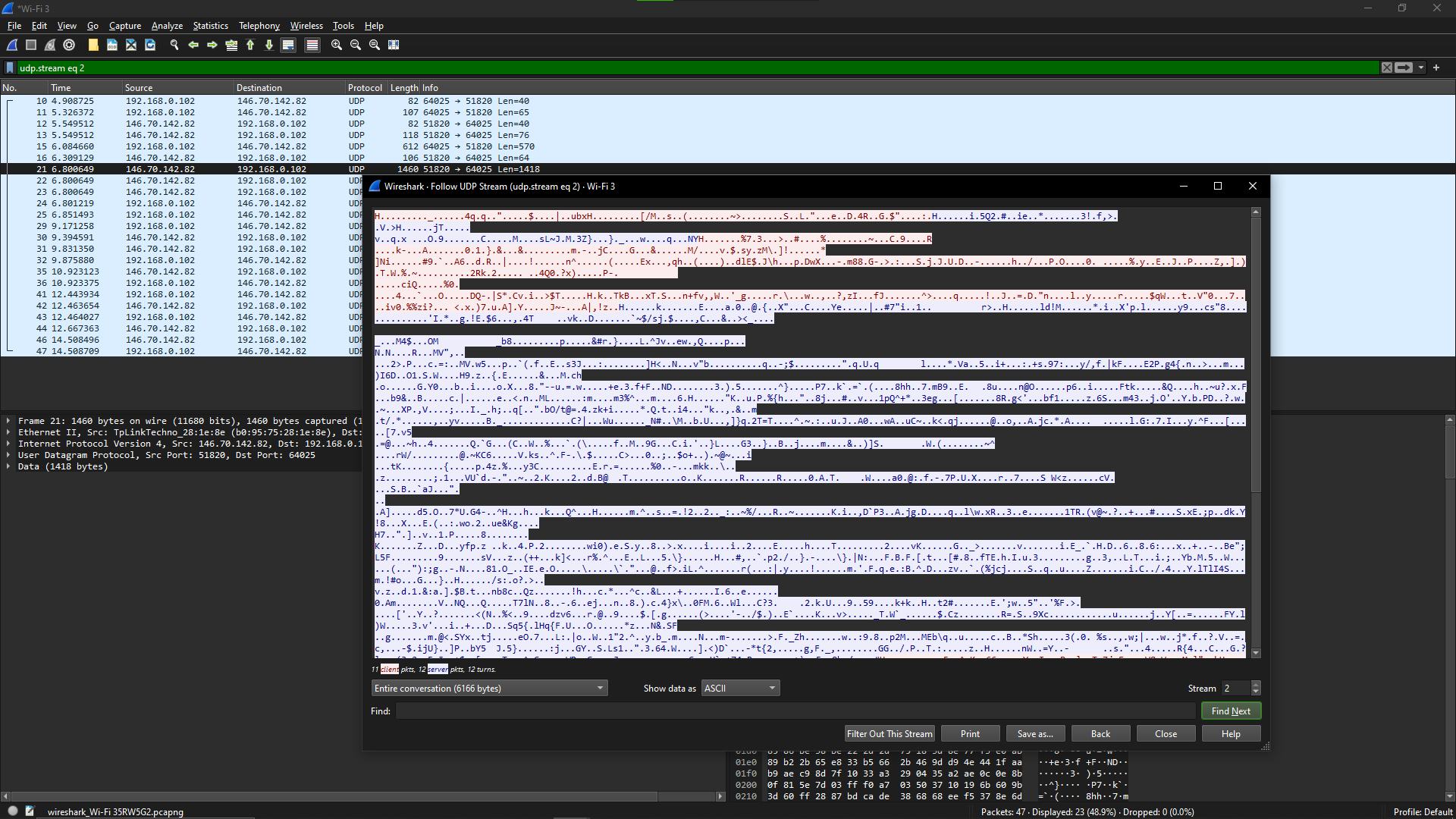
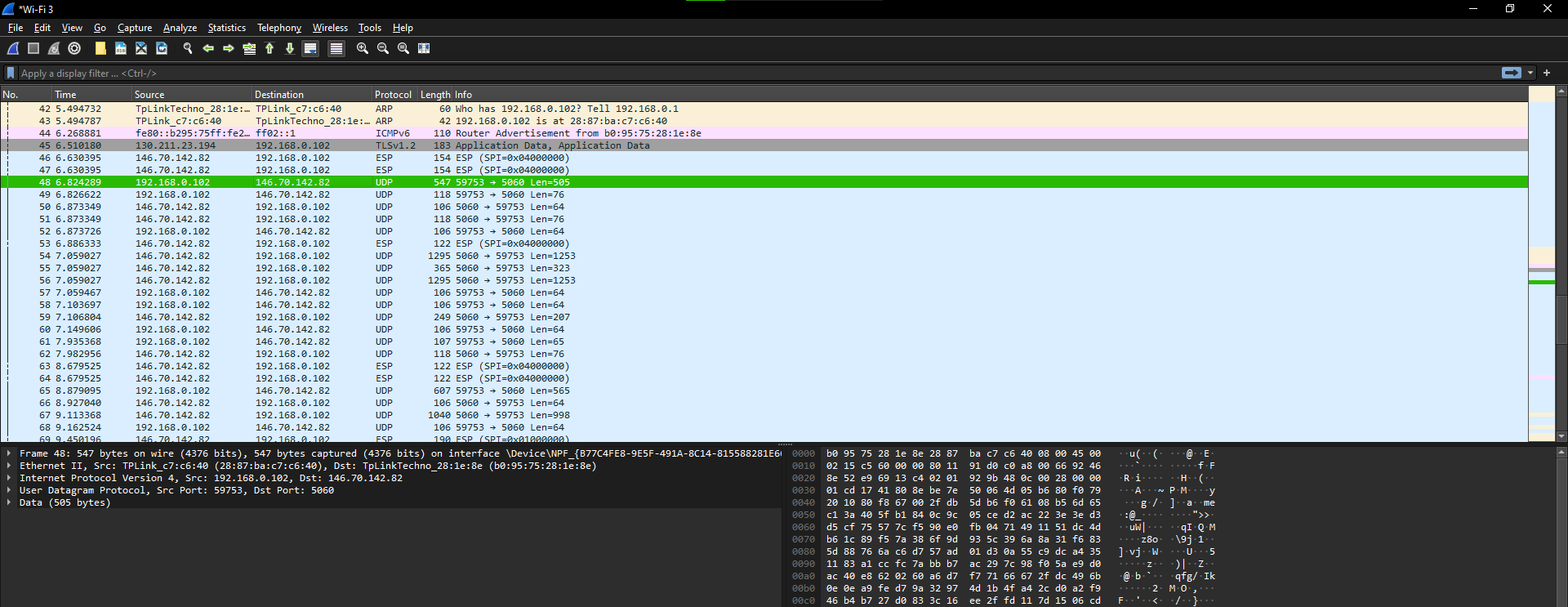
Does Proton VPN encryption matter?
The above results are testaments to why using a VPN is crucial. While the above tests are conducted by visiting an unsecured HTTP webpage for better testing and transparent results, I have browsed the web casually after turning on Proton VPNs WireGuard.
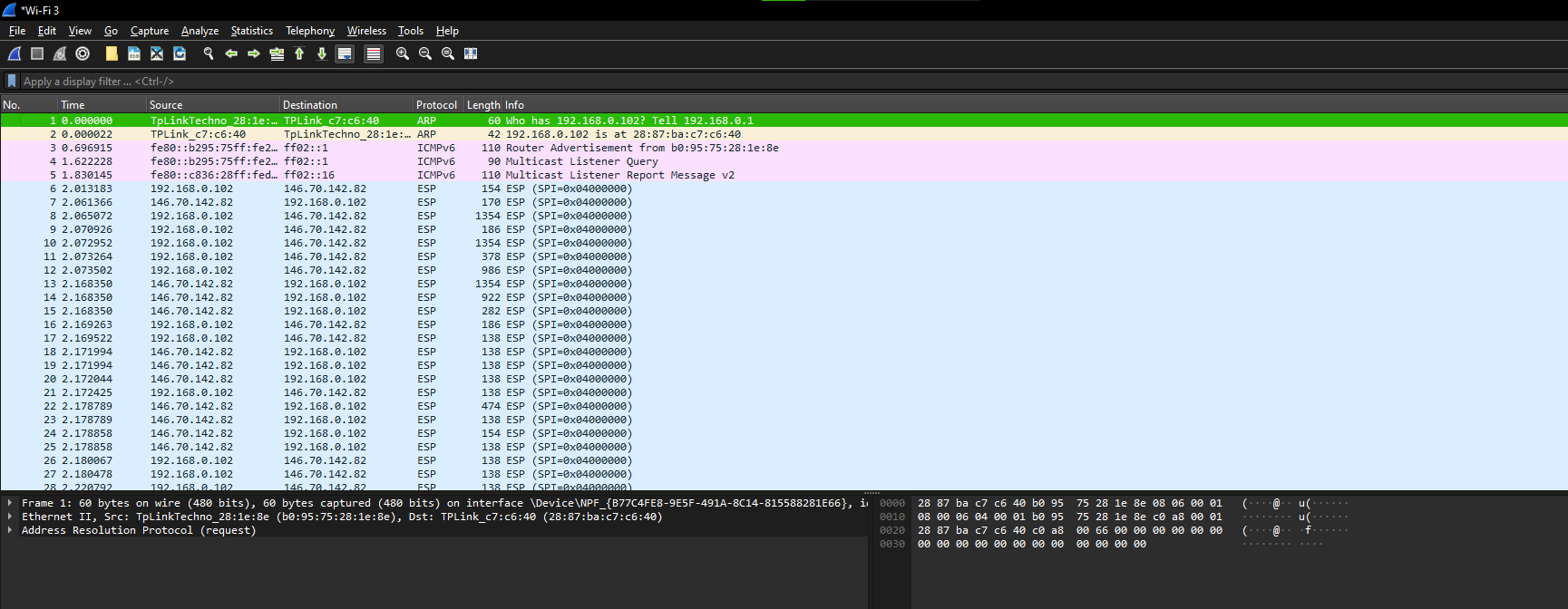
From the results, I have noticed that the WireGuard protocol of Proton VPN has done a good job of encrypting the traffic. While it might have left a few unsecure packets like ICMPv6, there were no other unsecured protocols captured.
Note: Unsecure protocols like MDNS, SSDP, IGMPv3, LLMNR, MADCAP, ARP, and UDPENCAP, including ICMPv6, feature unencrypted data. However, rest assured, as they typically operate within the local subnet and are not routed over the internet.
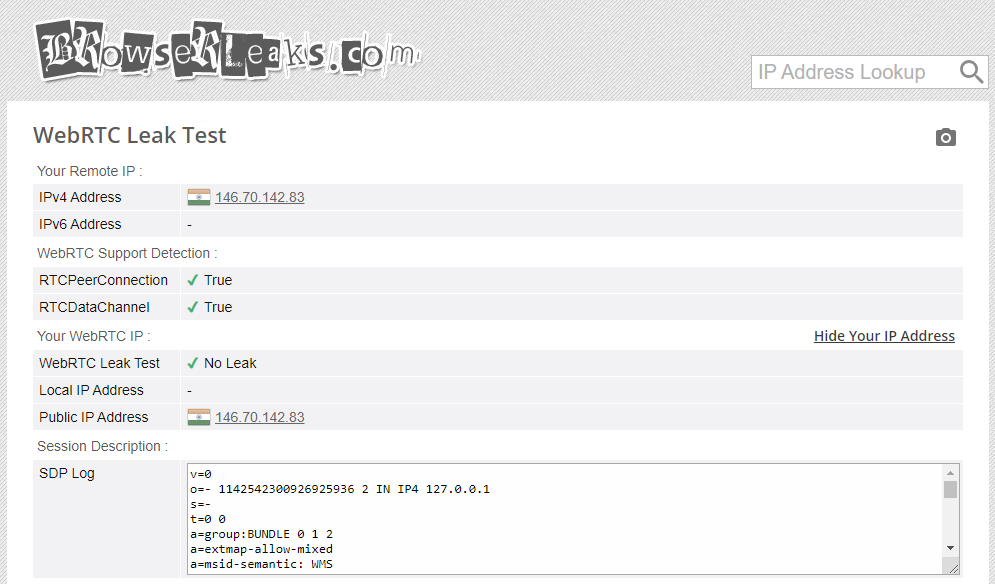
IP/DNS/WebRTC Leak Test
Ensuring that there are no IP and DNS leaks is crucial when utilizing a VPN, as such leaks can compromise security and privacy. An IP leak happens if websites or services you access can see your actual IP address, given by your Internet Service Provider (ISP), even though you are using a VPN.
In the same way, a DNS leak occurs if your device sends DNS queries to your ISP’s DNS servers instead of the secure DNS servers provided by the VPN, which could reveal the websites you’re accessing.
With these tests having a significant impact on privacy, I connected to a server on Proton VPN and put it to the test:

In the DNS leak test, multiple queries are performed, and none of the IPs and ISPs listed provided are mine. This confirmed that Proton VPN successfully masked my VPN and replaced it with the one it assigned, enhancing my privacy on the web.
While Proton VPN performed significantly well with the DNS and IP leak test, I opted for the WebRTC leak test just to be sure that my IP information wasn’t being revealed via STUN requests.
Once the results were out, I was relieved, considering there was no leak, and Proton VPN does stand strong to its claim of enhancing privacy on the web.
Speed Test
After considering the results from the tests made above, it seems clear that Proton VPN can enhance privacy on the web, but is it good for speed?
Regardless of the VPN you consider, the speeds offered by the servers are one of the key factors that define how well it performs. So, I have put Proton VPN to the test by connecting it to the closest server near me, and here are the results:

Next, I turned off the VPN and performed the speed test again. To my surprise, the speeds were slightly higher than the speeds recorded when the VPN was turned on.

Usually, this isn’t the case with most VPNs, as they struggle to offer good speeds, and the drop is significant. Through this test, it is clear that Proton VPN servers offer decent speeds and can be relied on. However, keep in mind that it isn’t for gaming, considering the latency is high.
Pro Tip: Try out various configurations of VPN protocols and conduct a speed test after each adjustment to determine the optimal setup for enhanced speed. Additionally, for improved speed and reduced latency, choose a server closer to your location.
Where does Proton VPN stand out?
After trying and testing Proton VPN, I noticed that it falls short in terms of features. While it might lack the features/tools a prominent VPN comes with, Proton VPN has implemented a few features well, which makes it stand out in its segment.
Note: The features/tools below might be common, and you might have seen them in multiple VPNs. However, it’s the implementation that makes Proton VPN a considerable choice among other VPNs.
Proton VPN’s Security and Privacy Enhancements
Proton VPN sets the bar high for online security and privacy. This section goes deeper into the advanced security measures Proton VPN employs to protect user data.
Secure Core Network: The secure core network of Proton VPN reroutes traffic through privacy-friendly countries. This feature can come in handy if you’re looking for enhanced privacy while surfing the web.
While this is a great feature, the rerouting decreases the speeds. Hence, use this when needed and ensure you turn it off while streaming and gaming.

Perfect Forward Secrecy: While this isn’t a feature that can be turned manually on and off, it remains turned on at all times. Even though it cannot be interacted with, it is a great addition as it employs ciphers to ensure past sessions’ data remains secure, even if future keys are compromised.
Proton VPN’s TOR servers: Your good old Google Chrome may just be scratching the surface of the internet, but you can go beyond it using the TOR browser. The best part about Proton VPN is its servers are dedicated specifically for this purpose. While this is a great addition to enhance anonymity, I suggest using it only while visiting onion websites.
Proton VPN’s User Experience and Accessibility
Proton VPN has paid great attention to detail in providing the best user experience and accessibility. While there aren’t many, the ones mentioned below work exclusively well and stand up to the tall claims.
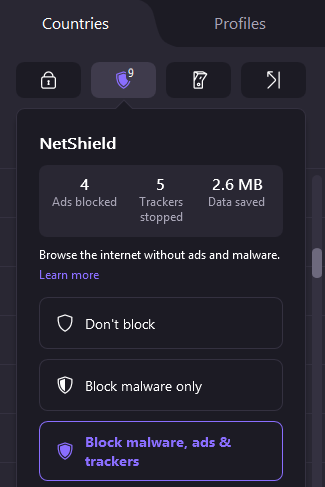
NetShield Adblocker: The Netshield Adblocker gives the user peace of mind while being on the web as it can effectively block malware, ads, and trackers through its DNS filtering capabilities.
There are no major complaints I have over these features, apart from the fact that you might get blocked by a few websites when they recognize you’re using an ad blocker.
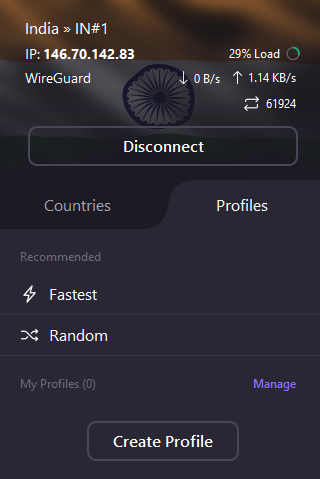
Proton VPN Profiles: The Profiles tab listed on the home screen deserves special attention, as it significantly enhances usability.
Through this feature, you can create custom connection settings and save them as a VPN connection. Later, you can use the profile to connect instantly to the server of your choice using those settings.
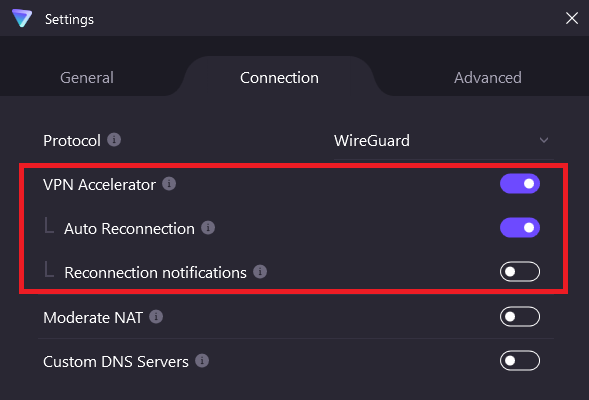
VPN Accelerator: While the VPN accelerator isn’t a significant feature to begin with, it can be a great addition if you want to enhance accessibility. The main purpose of this feature is to let you increase connection speeds significantly, which is especially useful for activities like torrenting.
Also, the additional perks like Auto Reconnection and Reconnection notification are added advantages.
Privacy Policy of Proton VPN
Proton VPN features over 6,300 servers in 100 countries, including specialized Secure Core servers. The best part of Proton VPN is its servers are located in Switzerland or Germany, which benefits from Switzerland’s strong privacy laws, outside EU/US jurisdiction, and 14 eyes surveillance.
Regarding its no-logs policy, Proton VPN is transparent and does not track or store users’ internet activity, ensuring privacy. Also, the source code is open for review and has been independently audited for added trust.
In addition to the privacy policy, Proton VPN ensures the best privacy by offering features like DNS Leak Protection, Kill Switch, Split Tunneling, and Ad and Malware Blocking (NetShield).
Proton VPN Pricing
Proton VPN offers different subscription plans with varying features, and here is a quick look at its Proton VPN Plus plan.
Free Plan:
- Offers basic privacy protection
- Access to 100+ servers in 3 countries
- No cost involved
1-Month Plan ($9.99/month):
- Full feature access
- 30-day money-back guarantee
- Protects up to 10 devices
1-Year Plan ($4.99/month):
- The same benefits as the monthly plan but at a reduced annual rate
2-Year Plan ($4.49/month):
- Best value with the lowest monthly rate
- All features included
Each paid plan comes with a 30-day money-back guarantee and allows protection for up to 10 devices simultaneously. However, if you aren’t happy and want to go further, consider the Proton Unlimited plan, which gives you access to all premium Proton services at an extra cost.
Wrapping Up
Proton VPN turns out to be an effective VPN, and it does stand on its promises. While you might find it short on features, consider this VPN as a solution to stay secure and anonymous on the web.
Proton VPN receives the Geekflare Value Award as it is one of the most efficient and reliable VPNs that you can get your hands on for the price. You might find better alternatives at the expense of a higher price tag, but if you’re looking for a VPN that sticks to providing well-rounded privacy and offers a suite of tools that get the job done, look no further.
After thorough testing, I believe there is some room for improvement as well. It can be underwhelming in certain situations, with the lack of customization and unpredictable protocol behavior. However, it is certainly a great choice for those looking for a VPN that is ideal for basic surfing and extensive torrenting.


