Ever experienced slow-loading websites or errors when trying to visit websites? The culprit might be an outdated DNS cache. In this article, we’ll guide you through clearing your DNS cache on Windows and popular browsers.
Computer operating system like Windows, Mac and browsers like Chrome, Firefox, Safari store DNS query results for faster website loading. While useful, this cache can become outdated, leading to website errors or potential privacy concerns. Clearing just your browser cache may not be enough, you would need to specifically flush the DNS cache, as explained below.
How to Clear DNS Cache on Windows
On Windows, you’ll need to open Command Prompt either from the Start menu and search for it or by pressing Ctrl + r and typing cmd and clicking OK. Once inside the prompt, you can issue the below command to flush the DNS cache:
C:\>ipconfig /flushdnsYou’ll get output showing Successfully flushed the DNS Resolver Cache. as shown below:
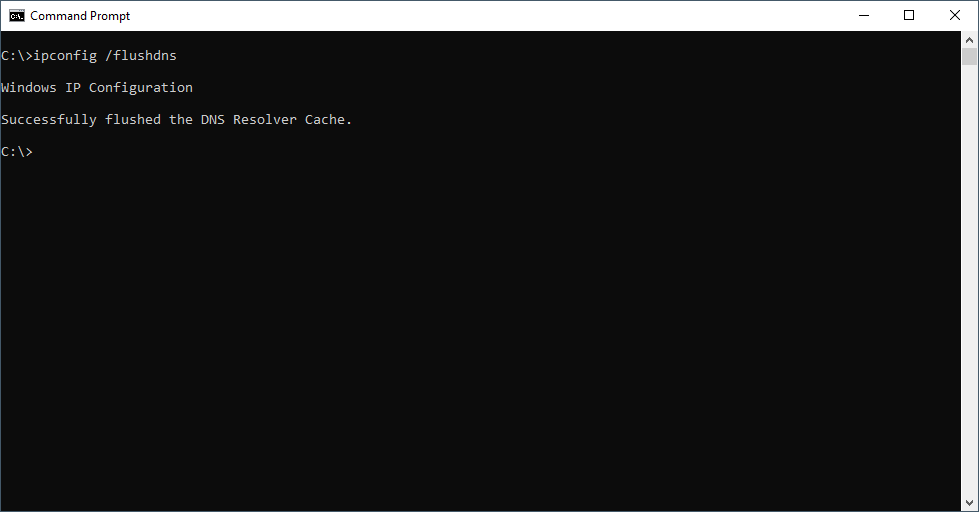
C:\>ipconfig /flushdns
Windows IP Configuration
Successfully flushed the DNS Resolver Cache.
C:\>This command works on Windows XP, 7, 8, 10 and 11 and is fairly simple to use.
How to Clear DNS Cache on Mac
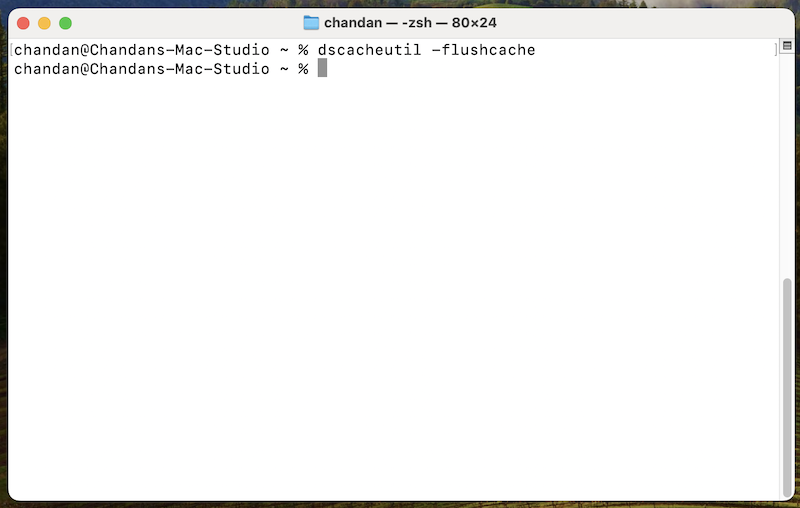
To clear DNS cache on macOS, open Terminal and type the below command and press Enter.
dscacheutil -flushcacheIf you are not logged into your Mac using admin or root permission, you can use the dscacheutil command with sudo. It will prompt you to enter the admin password.
sudo dscacheutil -flushcacheThe command execution will silently return to the prompt.
How to Clear DNS Cache on Chrome
DNS cache, as discussed, is not only cached by an operating system like Windows; the browser you’re using may also be caching DNS records.
To flush the DNS cache on Chrome, open a new tab and enter chrome://net-internals/#dns in the address bar and press Enter.
You should get a page like the following:
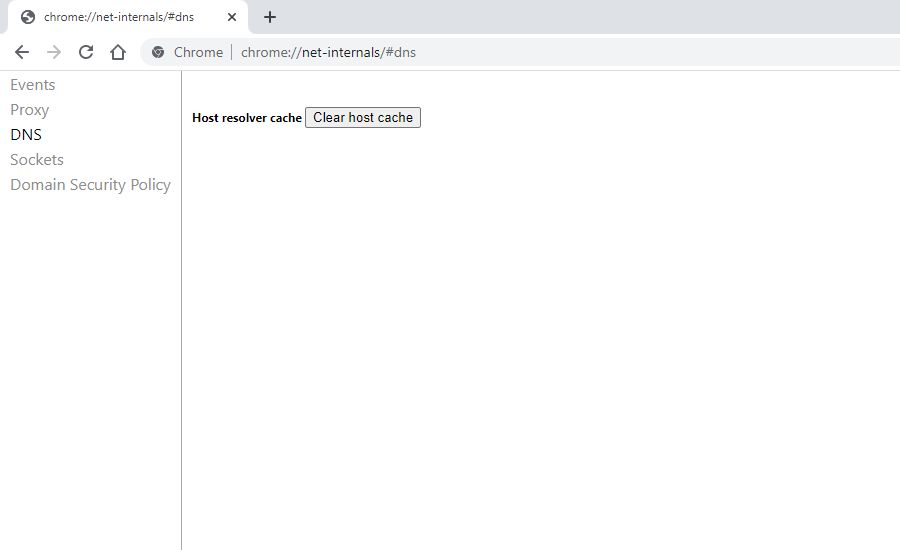
Click on Clear host cache button to clear the browser’s DNS cache. No prompts or confirmation messages will be shown, but this simple action should flush Chrome’s DNS cache for you.
How to Clear DNS Cache on Firefox
Clearing the DNS cache in Firefox can be done by simply restarting the browser, as the cache is not maintained on the disk. However, there is a way that you can follow to clear just the DNS cache in memory without needing to restart your browser.
For this, open a new tab in Firefox and enter this in the address bar, and press enter: about:networking#dns
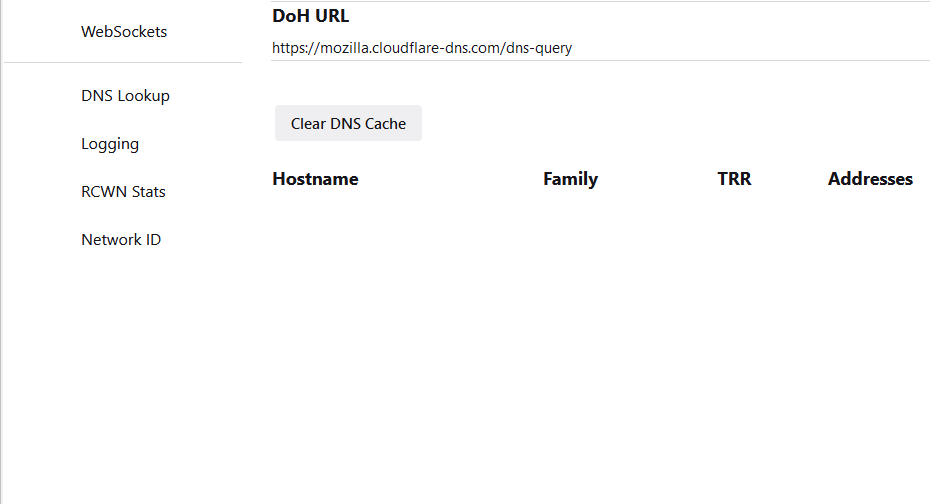
This page should show you DNS cache details and offers a button Clear DNS Cache — click on it to clear the browser’s DNS cache.
To be thorough, it’s also a good idea to clear cache and cookies from Firefox settings if you’re still experiencing issues.
How to Clear DNS Cache Safari
Safari has a hidden option to clear different caches, including DNS, from its menu bar. But first, you would need to enable Develop menu.
- To do that, go to
Safarimenu and then openPreferences. - Then click on the
Advancedtab and then checkShow Develop menu in menu bar. - Now you should see a new option,
Developin Safari’s menu bar. - In that menu, select
Empty Cachesoption to clear the browser’s cache, including any caches related to DNS.
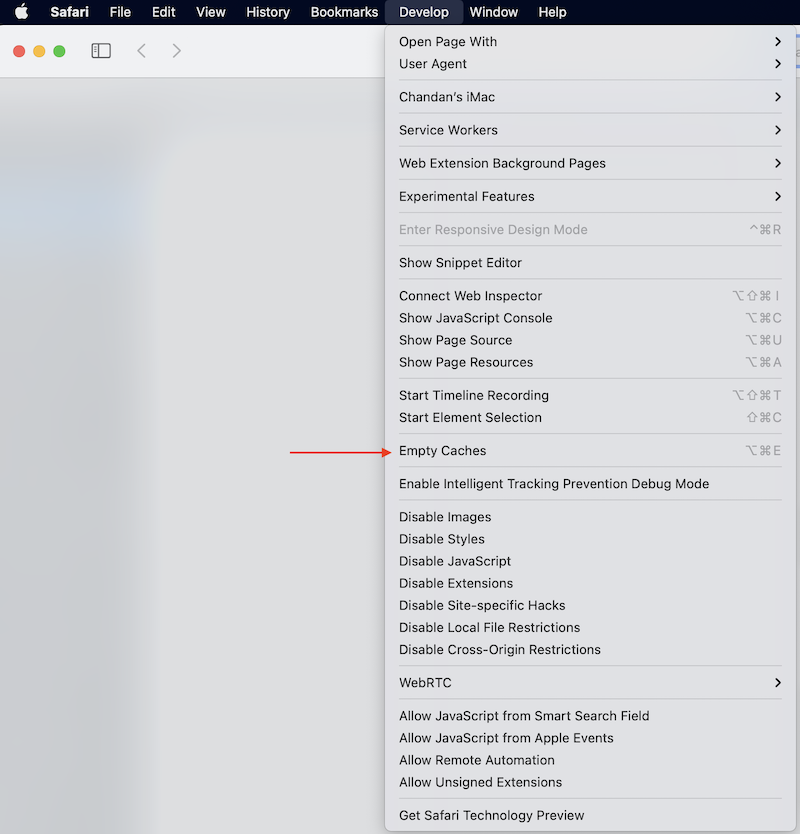
Ideally, you should restart the browser after clearing the cache for the best results.
Conclusion
I’ve covered simple steps that allow you to clear DNS caches on your computers. This can be helpful in troubleshooting issues related to connectivity and DNS resolution. Flushing DNS will also help if you are using a VPN service and having frequent website connectivity issues.


