Controlled Folder Access is a built-in defensive mechanism for Windows 10 & 11.
Windows OS is a popular target for cybercriminals due to its widespread use and the variety of vulnerabilities that can be exploited. Malware and ransomware attacks can cause significant damage to data and systems, which results in financial loss, reputational damage, and other negative consequences.
In addition to installing antivirus software, the Controlled Folder Access feature in Windows 11/10 can provide an extra layer of protection against ransomware attacks.
Let’s see what this controlled folder access is all about and its importance.
What is Controlled Folder Access?
Controlled Folder Access is a feature in Windows 10 & 11 that provides an extra layer of security to protect important files and folders from unauthorized changes by malicious software or ransomware.
When this feature is enabled, it restricts the ability of applications to access and modify files and folders that are protected. Only trusted applications that are whitelisted by the user or system are allowed to access these files and folders.
Windows will monitor and alert the user whenever an untrusted app attempts to modify a protected file or folder with this Controlled Folder Access. This feature provides an additional layer of protection against ransomware attacks and other types of malicious software that attempt to encrypt or delete important files.
There are a few ways to enable Controlled Folder Access in Windows 10 & 11.
Using Windows Security Center
- Click on the Windows Start button and type “Windows Security” in the search bar.
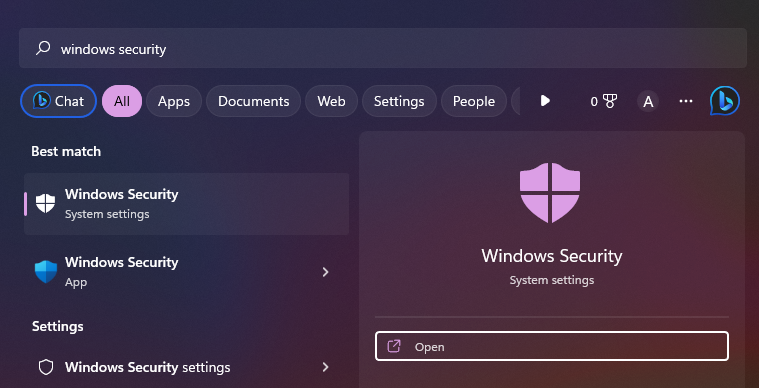
- Click on “Windows Security” to open the app.
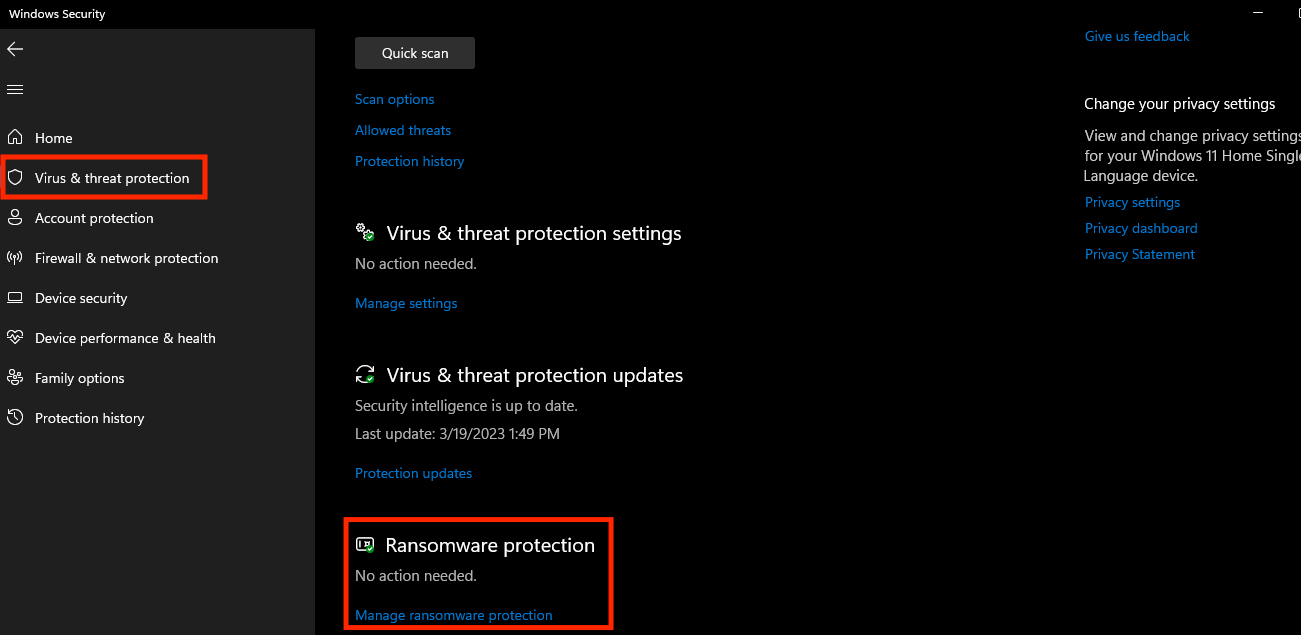
- Click on “Virus & threat protection” in the left-hand menu.
- Scroll down to “Ransomware protection” and click on “Manage ransomware protection.”
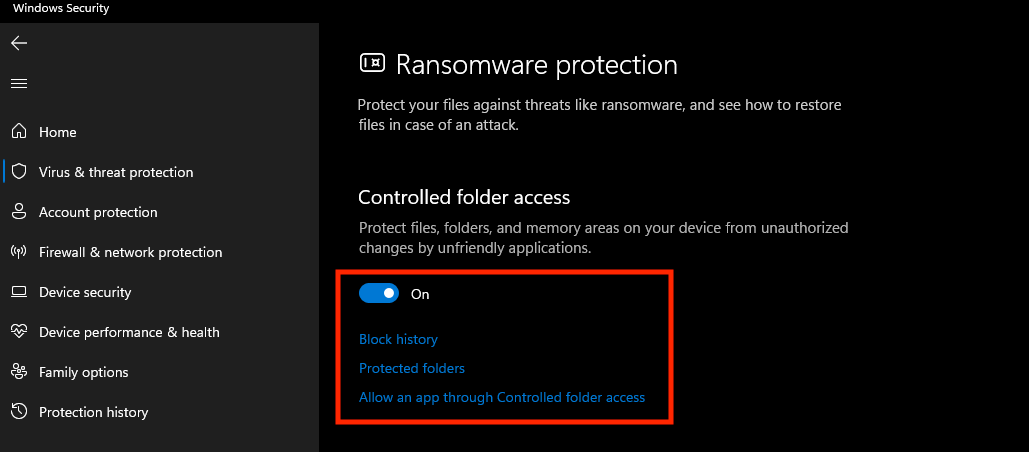
- Toggle the switch under “Controlled folder access” to the on position.
- Windows Security will now monitor protected folders and alert you whenever an untrusted app attempts to modify them.
- To add a protected folder, click on “Protected folders” and then “Add a protected folder.”
- Select the folder you want to protect and click “OK.”
- You can also add trusted apps to the whitelist by clicking on “Allow an app through Controlled folder access” and select the app you want to add.
Using Group Policy
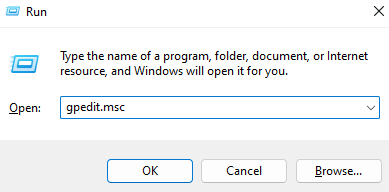
- Press the Windows key + R to open the Run dialog box.
- Type “gpedit.msc” and click OK to open the Local Group Policy Editor.
- In the left-hand panel, navigate to Computer Configuration > Administrative Templates > Windows Components > Windows Defender Antivirus > Windows Defender Exploit Guard > Controlled folder access.
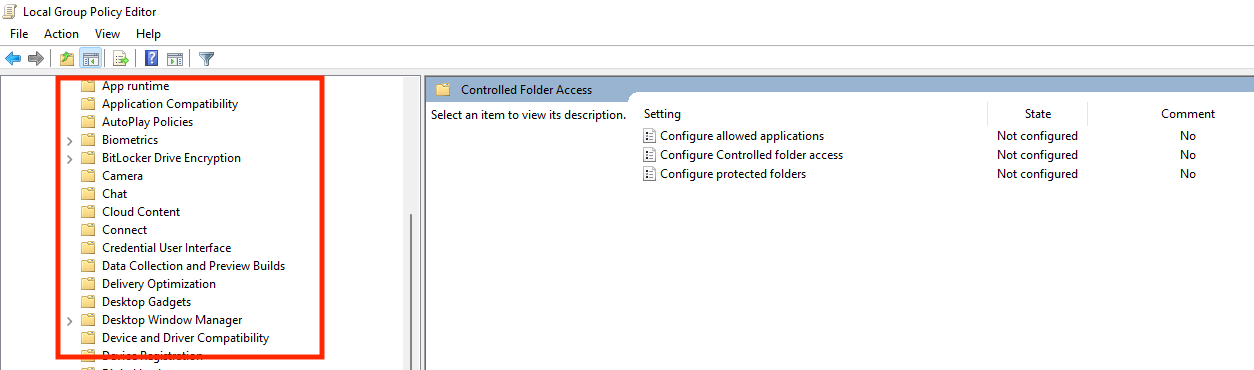
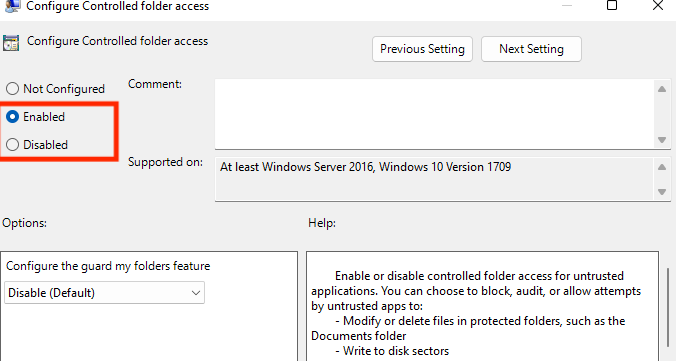
- Double-click on “Configure Controlled folder access” in the right-hand panel.
- Select the “Enabled” option and click OK.
- Under the “Options” section, select “Audit mode” to monitor changes to protected folders or “Block mode” to prevent changes to protected folders.
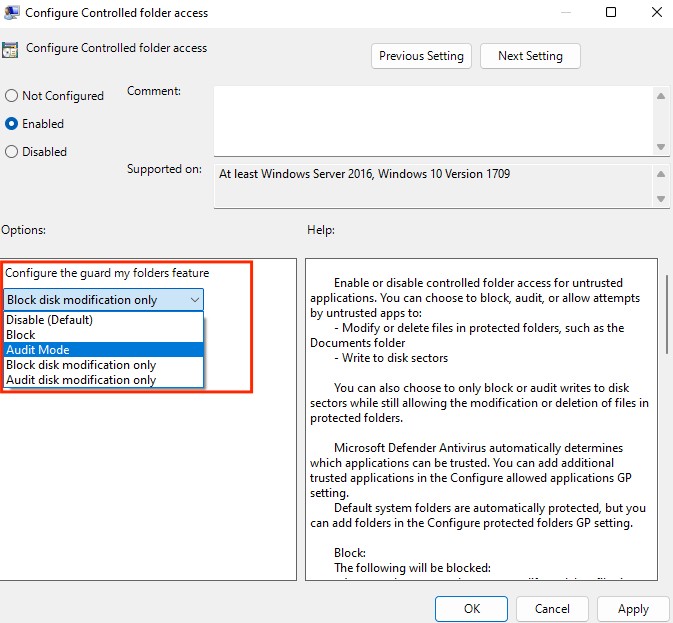
- Click the “Apply” button and then click “OK” to save the changes.
- And finally to add a folder to the list of protected folders, open Windows Security and go to “Virus & threat protection” > “Manage ransomware protection” > “Protected folders” > “Add a protected folder.” Select the folder you want to protect and click “OK.”
Using PowerShell
- Open PowerShell as an administrator. To do this, right-click on the Windows Start button and select “Windows PowerShell (Admin).”
- Type the following command and press Enter.
Set-MpPreference -EnableControlledFolderAccess Enabled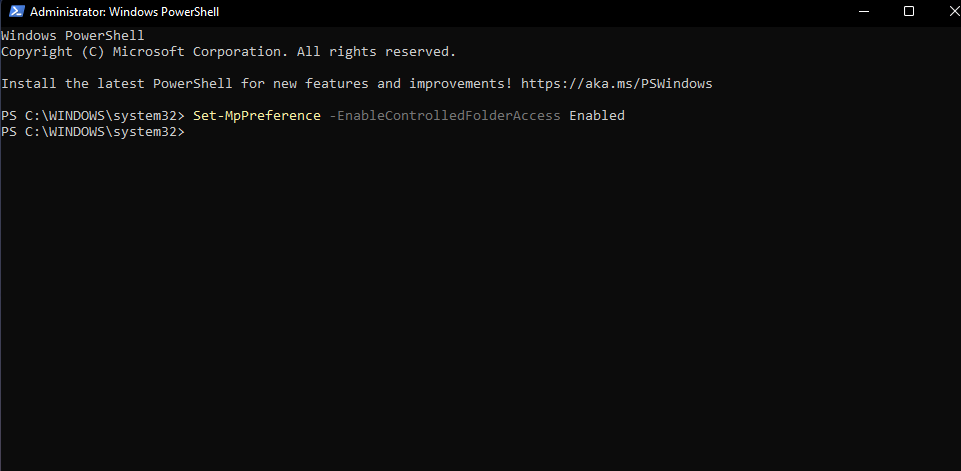
- Once you run the command, Controlled Folder Access will be enabled on your device.
- Similarly to disable the Controlled Folder Access, you need to replace “Enabled” with “Disabled”.
Set-MpPreference -EnableControlledFolderAccess Disabled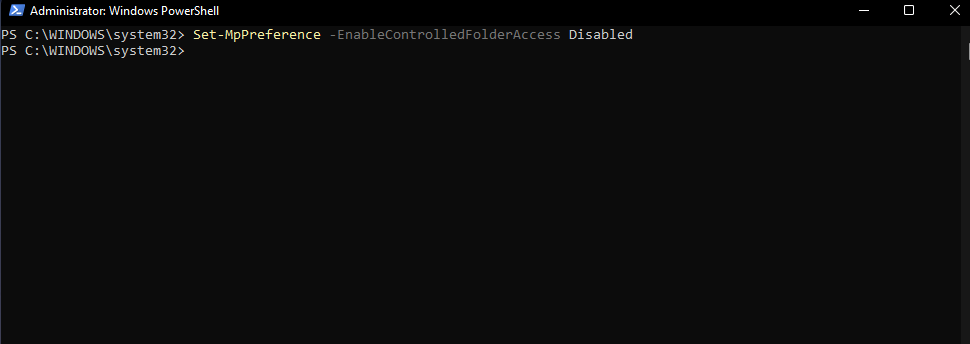
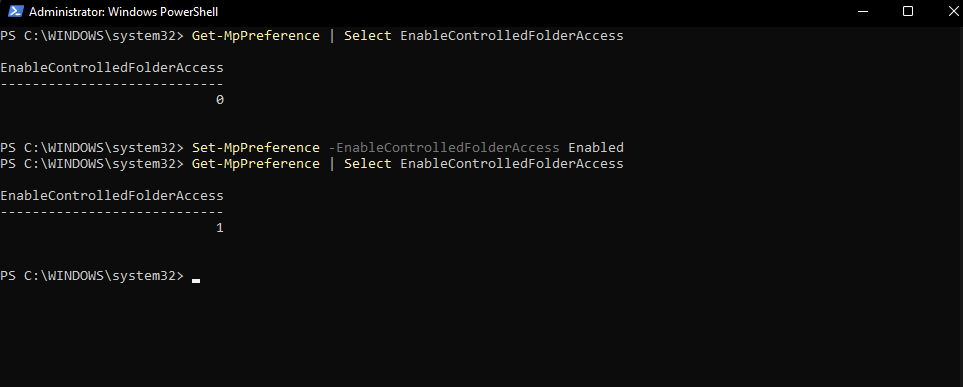
- You can verify the status of Controlled Folder Access by running the following command.
Get-MpPreference | Select EnableControlledFolderAccess- If the output shows “1”, then Controlled Folder Access is enabled. If the output shows “0”, that means the Controlled Folder Access has been disabled.
Note: You may need to restart your computer after making changes to the Controlled Folder Access settings.
Why do the data need to be secured?

Protection from cyberattacks
With the increasing number of cyberattacks, securing your data is essential to protect your sensitive information from being accessed by unauthorized individuals. Cybercriminals can use your personal information for fraudulent activities or sell it on the dark web.
Avoiding identity theft
Identity theft occurs when someone steals your personal information and uses it to commit fraud or other criminal activities. By safeguarding your data, you can prevent identity theft and avoid the legal and financial consequences that come with it.
Compliance with regulations
Depending on your industry, there may be specific regulations that require you to protect your data. Legal & financial penalties may be imposed for not complying with these rules and regulations.
Maintaining trust with customers
If you are a business owner, protecting your customer’s data is essential to maintain their trust. A data breach can damage your reputation and cause customers to lose faith in your ability to protect their information.
Peace of mind
Knowing that your data is secure can provide peace of mind and reduce stress. You can focus on other tasks and activities without worrying about the potential consequences of a data breach.
How to choose folders to protect?
These are the various factors to consider when selecting certain files and folders to secure.
Importance
Check the folders which contain important files, such as personal or financial information, that could be dangerous if accessed or modified without permission.
Risk
Evaluate the level of risk for each folder based on factors such as the likelihood of a malware attack and the potential impact of a security breach.
Usage
Consider how frequently each folder is accessed or modified and whether it is a shared folder or only accessible to a specific user.
Location
Find out if the folder is accessible from outside the organization and whether it is stored on the local computer or a network drive.
Once you have identified the folders that require protection, you can add them to the Controlled folder access list by following any of the above-listed methods. It’s important to regularly examine & update the list of protected folders to make sure that any new or modified folders are also covered by the encryption.
Author’s Note ✍️
Controlled Folder Access is an important security feature in Windows 10 and 11, but it is not sufficient on its own to maintain a high level of security. It is just one layer of defense among many that should be implemented to secure your system
In addition to this Controlled Folder Access, you should also consider implementing other security measures such as Antivirus & anti-malware software, Firewall, Two-factor authentication, Strong passwords, and regular backups.
I hope you found this article helpful in learning about controlled folder access and its importance. You may also be interested in learning about how to recover deleted files from recycle bin after emptying them on Windows and Mac.


