WPScan is an open-source security scanner that scans WordPress websites for vulnerabilities in plugins, themes, and WordPress core.
WordPress is a popular content management system that is often targeted by hackers. Regularly scanning your WordPress website for vulnerabilities is crucial in order to prevent cyber threats such as data theft or malware infections.
WPScan is a powerful security tool that helps WordPress website owners and developers protect their sites from security threats by scanning and monitoring for vulnerabilities.
In this post, we will explore WPScan’s features and how to use it on Ubuntu, Kali Linux, and Docker.
What Is WPScan?
WPScan is an open-source security scanner for WordPress websites that identifies potential vulnerabilities such as outdated plugins, weak passwords, and configuration problems. It is owned by Automattic and uses a WordPress vulnerability database to scan for known vulnerabilities.
WPScan provides detailed reports on security scan results, identifying vulnerabilities and suggesting remediation steps such as updating software, removing insecure plugins/themes, and implementing security best practices.
WPScan is an open-source tool supported by a large community. Its database is regularly updated to stay effective in finding new threats. At present, WPScan has around 50,773 vulnerabilities in its database. It is available as a WordPress security plugin, command-line interface (CLI) scanner, and API.
WPScan Features
WPScan offers a comprehensive set of features to help users secure their WordPress websites and protect them from potential security risks. Here are the key features of WPScan:
- Vulnerability Scanning: WPScan conducts thorough scans on the core WordPress installation, installed themes, and plugins and identifies potential vulnerabilities such as outdated plugins or weak passwords.
- Configuration File Backup Detection: It helps identify exposed configuration file backups.
- Database Dump Detection: WPScan detects publicly accessible database dumps.
- Error Log Exposure: It identifies if any plugins expose error logs, which can provide valuable information to attackers looking for vulnerabilities to exploit.
- Custom Alerts: The WPScan WordPress plugin allows you to set custom alerts for specific security events.
WPScan has a low false rate (3%) and offers trustworthy and accurate security warnings. Consequently, you won’t spend much time on non-issues. It is constantly updated to keep up with new vulnerabilities and security threats.
Now that you know WPScan’s features, let’s learn how to install WPSan on different devices. For demonstration purposes, I have used an Oracle VM Virtual Box with Ubuntu and Kali Linux installed.
How To Install WPScan on Ubuntu
Installing and using WPScan on Ubuntu is straightforward. However, as WPScan is written in the Ruby programming language, you need to install Ruby first to make it work on Ubuntu.
Here is step-by-step process:
- Open “Terminal” and press Enter after pasting the following command to install Ruby on your Ubuntu device.
sudo apt install ruby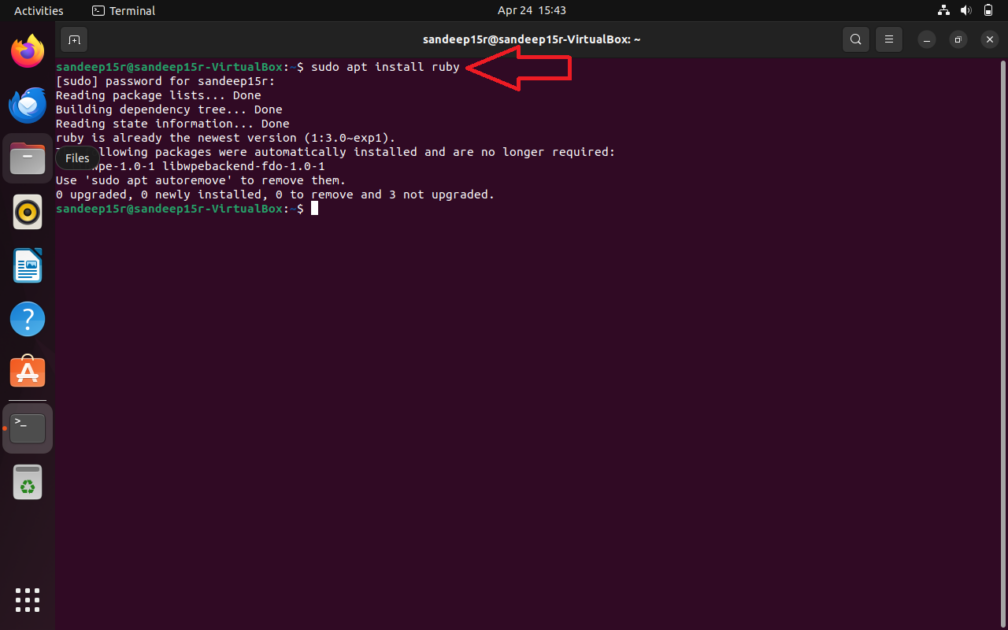
- Now, paste the following command and press Enter to install dependencies for building extensions.
sudo apt install build-essential libcurl4-openssl-dev libxml2 libxml2-dev libxslt1-dev ruby-dev libgmp-dev zlib1g-de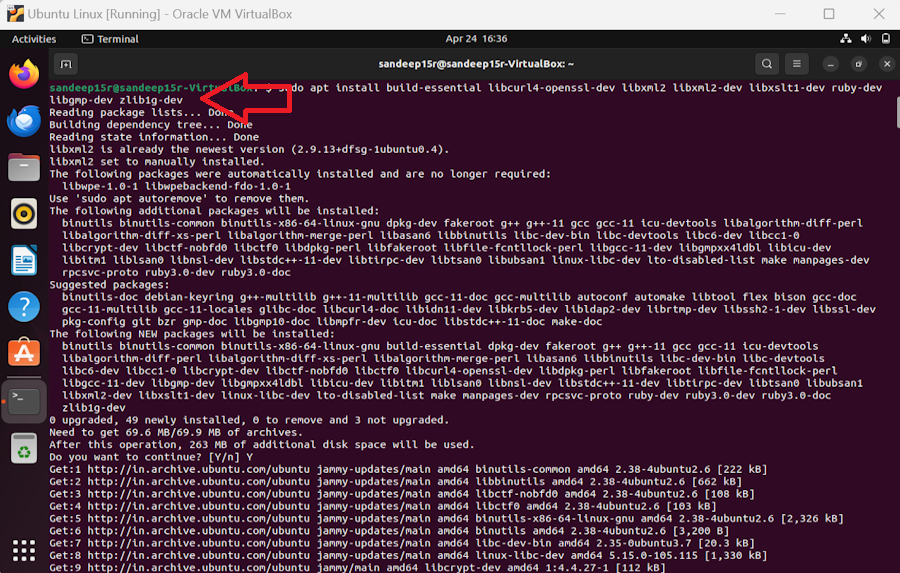
- Copy and paste the following command and press Enter to install WPScan on your Ubuntu device.
sudo gem install wpscan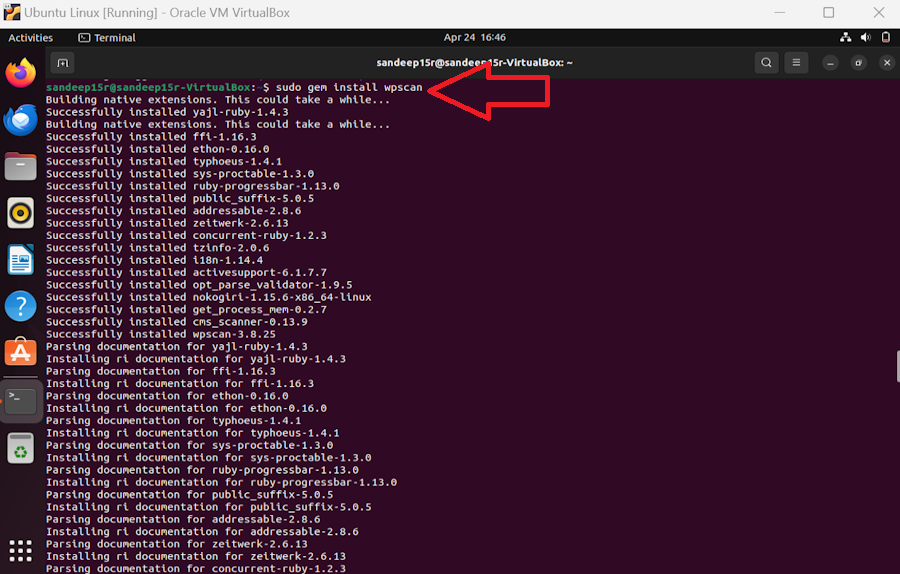
- Paste the following command and press Enter to update the database of WPScan.
wpscan --update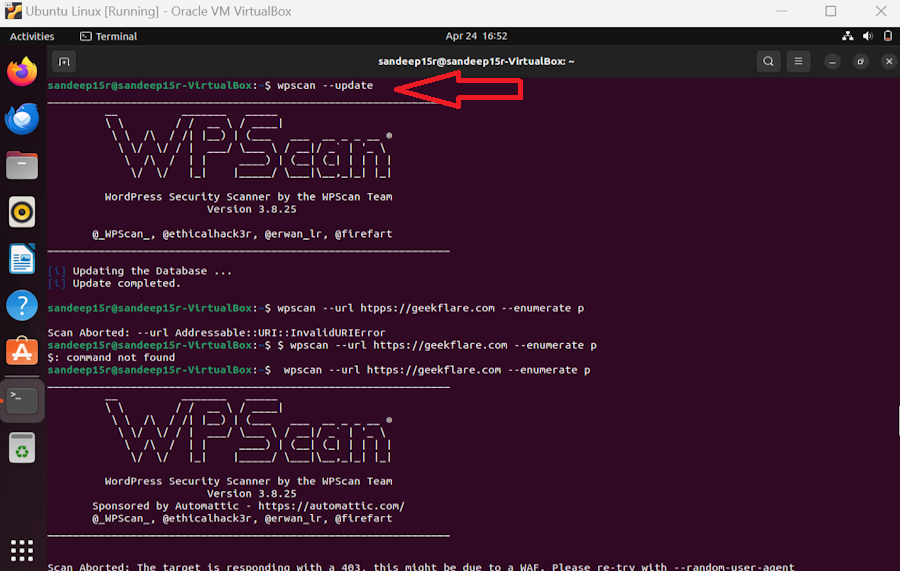
- You have up-to-date WPScan. Now, paste the following command and press Enter to start the scan. Replace http(s)://my-domain.com with your website domain name.
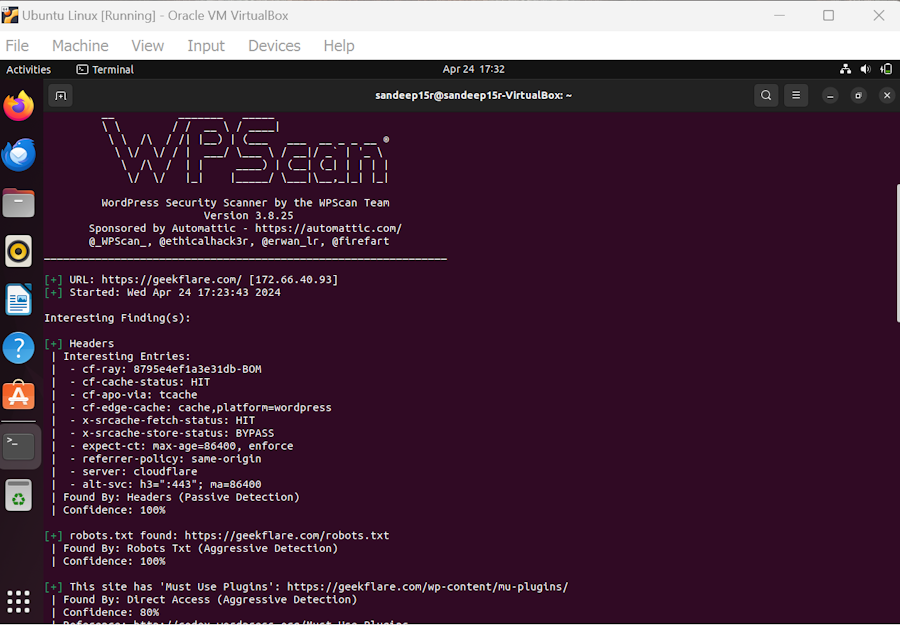
wpscan --url http(s)://my-domain.comIf WPScan aborts the scan, your web application firewall (WAF) might be preveing it from scanning your website. Paste the following command and press Enter to scan your website by a random user agent.
wpscan --url http(s)://my-domain.com --random-user-agent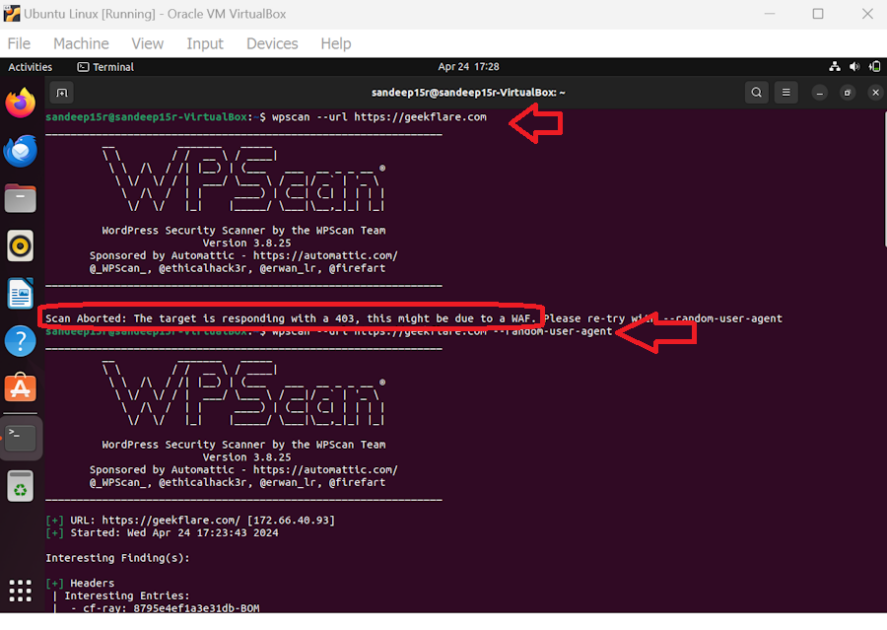
- After some time, WPScan will finish scanning. Dive into the report to get insights into your website’s security.
How To Use WPScan on Kali Linux
If you’re using the latest, fully functional Kali Linux, you don’t have to install WPScan as it is already there. You just have to update it and start scanning your website.
- Open “Terminal” in Kali Linux and press Enter after pasting the following command to update the WPScan database.
sudo wpscan --update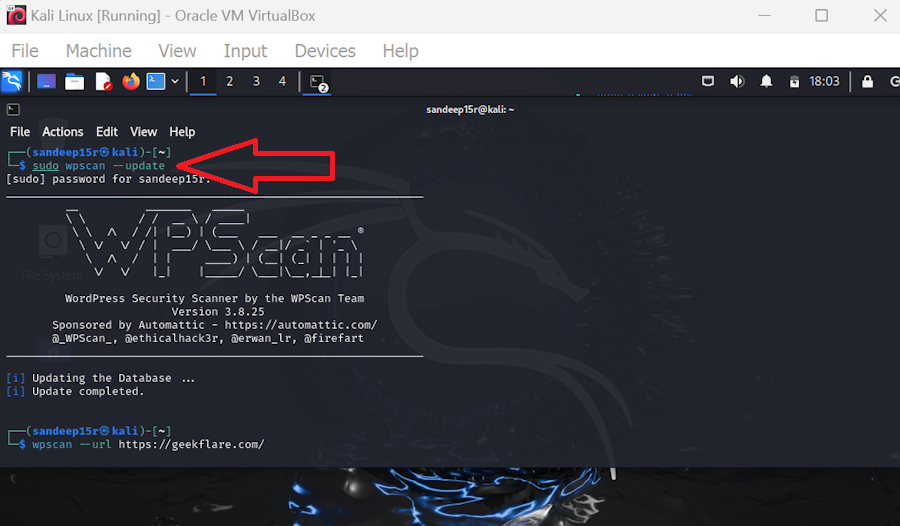
- Once WpScan is updated. Type the following command and press Enter to start scanning your website. Replace mywebsite.com with your website’s URL.
wpscan --url mywebsite.com 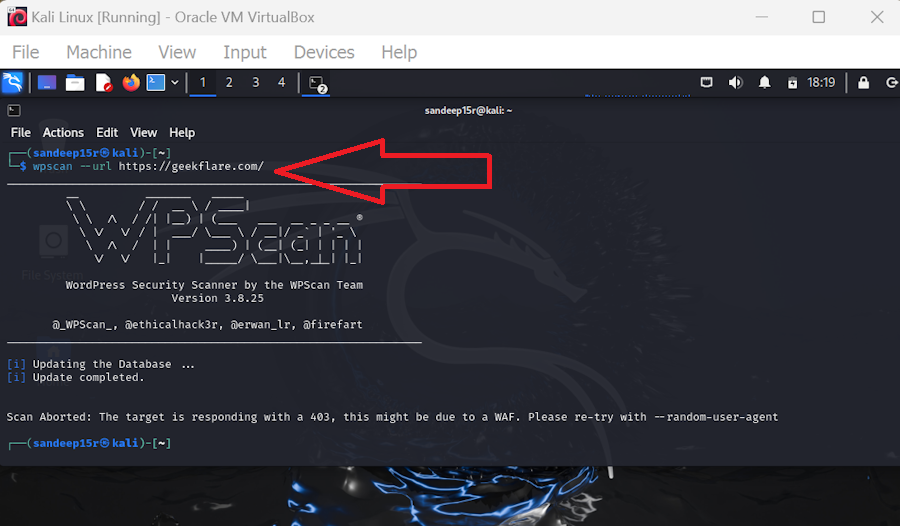
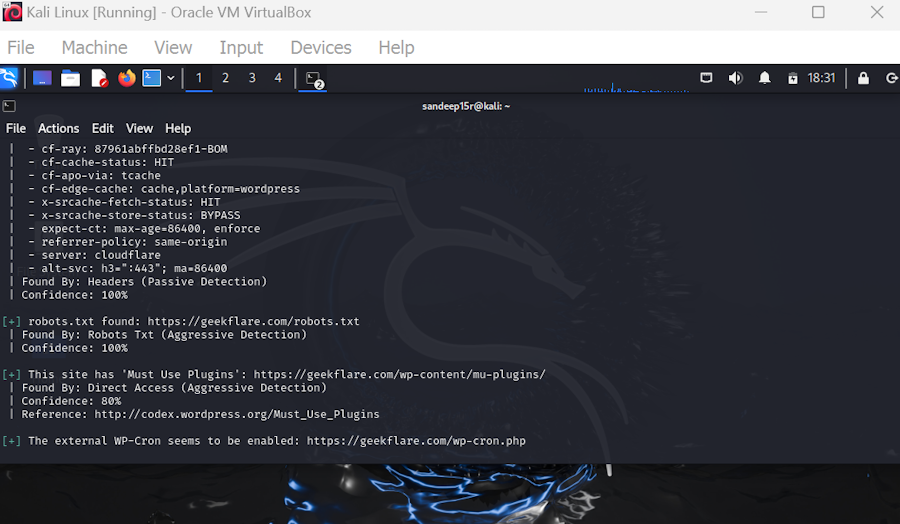
If there is an error, type the following command to scan your website using a random user agent.
--random-user-agent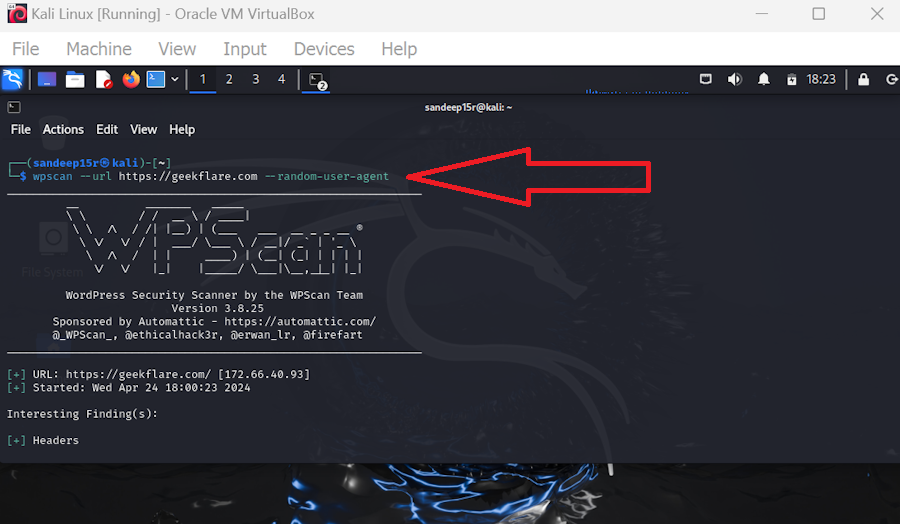
- Wait for some time, and your report will be ready to analyze.
How To Use WPScan on Docker
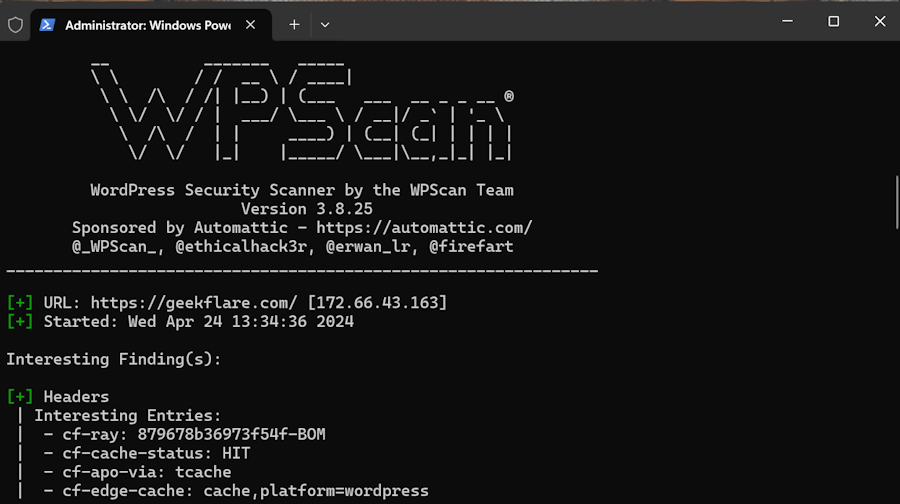
After installing and logging into the Docker Desktop app, follow the below-mentioned steps to use WPScan on your Windows PC.
- Press Windows+X and click on Terminal (Admin) to open Windows PowerShell. Paste the following command and Press Enter to pull the WPScan Docker image.
docker pull wpscanteam/wpscan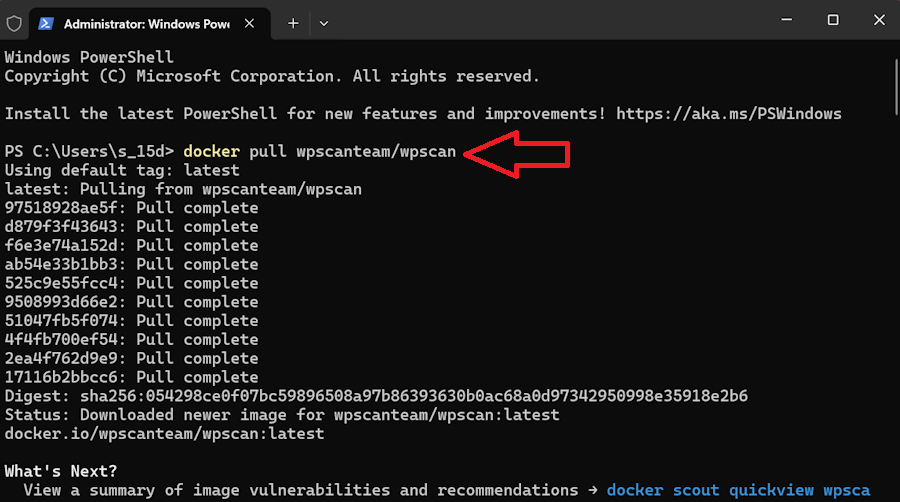
- Copy-paste the following command and press Enter to run a WPScan. Replace yourwebsite.com with your website’s URL.
docker run -it --rm wpscanteam/wpscan --url yourwebsite.comIf the WPScan is aborted, scan through a random user agent using the following command.
docker run -it --rm wpscanteam/wpscan --url yourwebsite.com --random-user-agent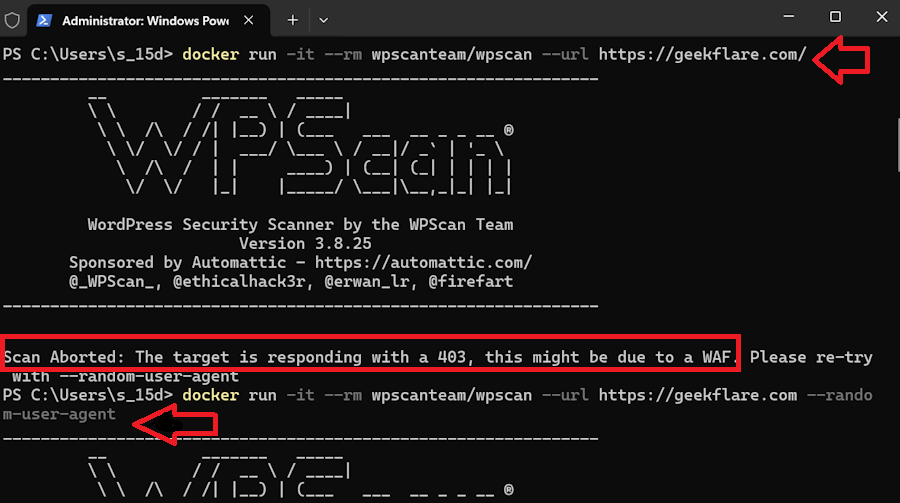
- After some time, your WPScan report will be ready.
WPScan Pricing
WPScan CLI scanner and API are free for researchers to use for non-commercial purposes. However, the free version is limited to 25 API calls per day. It makes one API call for the WordPress version, one per installed plugin, and one per the installed theme.
The Enterprise plan of the WPScan WordPress plugin offers additional features, such as instant email alerts, vulnerability details by ID, Common Vulnerability Scoring System (CVSS) risk score, and more. It follows a customized pricing structure. You need to contact the company to get the best WPScan price for your requirements under the Enterprise plan.
Unfortunately, the WPScan WordPress plugin has stopped supporting normal users; if you want to scan your website for vulnerabilities using a WordPress plugin, WPScan recommends that you use Jetpack Protect – a free security plugin for WordPress. Automattic owns both Jetpack and WPScan.
What Is WPScan Alternative Tool?
Here are some popular WPScan alternatives:
#1. Sucuri SiteCheck Scanner
Securi SiteCheck Scanner is a free website security scanner that helps you check your website for known viruses, malware, website errors, blacklisting status, malicious code, out-of-date software, and more. It allows you to quickly check your website’s security without installing any software. Just submit your website’s URL and receive a security report in seconds.
#2. Pentest Tools WordPress Scanner
Pentest Tools WordPress Scanner is a freemium WordPress website security scanner that can identify vulnerabilities and exploits in the core WordPress software, plugins, themes, and more. It also sends reports about WordPress configuration issues affecting backup files, directory listings, etc. You can also schedule scans with Pentest Tools WordPress Scanner.
#3. Hacker Target WordPress Security Scan
Hacker Target WordPress Security Scan is a freemium scanner that checks application security, WordPress plugins, web servers, and hosting environment. The passive check, which is free, downloads a few pages from your website to analyze the raw HTML code.
The extensive active scan, which falls in the paid plan, tries to enumerate plugins, themes, and users using custom WordPress auditing scripts that leverage the Nmap NSE framework.
How Often Should I Run a WordPress Security Scan?
Regular scans help catch vulnerabilities early, keeping your site safe. You should run a WordPress security scan at least once a week. Increase the frequency if your website hosts sensitive data or you have recently updated your website or installed new plugins.
How To Secure a WordPress Site?
WordPress is used by around 43% of all websites worldwide, making it a favorite target for hackers. So, you should ensure that you take proactive steps to protect your website.
Here are some strategies to boost the security of your WordPress website:
- Ensure you download themes and plugins from the official WordPress repository, as free plugins and themes listed on unofficial sources often have backdoors or malicious code.
- Install a web Application Firewall (WAF) to protect your website from SQL injection, cross-site scripting (XSS), cross-site-site forgery, and more.
- Scan your website with a reputed WordPress scanner to find security vulnerabilities in your website.
- Use WordPress Security plugins to proactively protect your website.
- Update your WordPress and its theme and plugins regularly to prevent hackers from exploiting known vulnerabilities.
Also, you should use strong passwords and activate two-factor authentication on all accounts to add an extra layer of security.


