Amazon Web Services (AWS) provides a robust cloud platform to host your applications and infrastructure, but under the AWS Shared Responsibility Model, securing your data and configurations is entirely up to you.
Cloud breaches are incredibly common, with attackers constantly scanning for exposed AWS accounts to exploit for data theft or unauthorized compute power.
I recently came across a horrifying post on Quora where a user’s AWS account was hacked, leaving them with a $50,000 bill overnight! And there are hundreds of cases like this.
A single data leak or exposed IAM key can cost you heavily and damage your brand’s reputation. So, how do you ensure you’ve taken all the necessary steps to protect your AWS environment?
You could manually audit your infrastructure against industry security guidelines, but that is incredibly time-consuming and prone to human error. The smarter approach is to use the best AWS vulnerability scanning tools.
These tools are either standalone open source or available as SaaS platforms. If you are looking for one-time or on-demand scanning, you can go for standalone, but for automatically auditing your AWS infrastructure, go for the SaaS option.
Native AWS Vulnerability Scanning Tools
Let’s start with native AWS tools. AWS has hundreds of tools, so knowing which tool is right for what job is important.
AWS Config
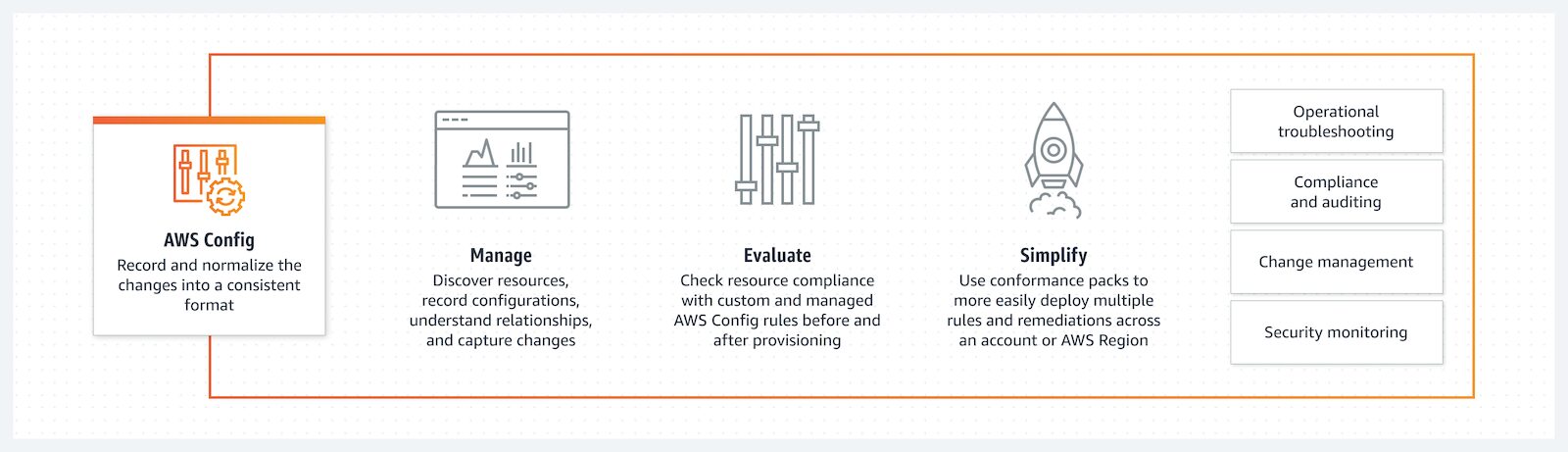
AWS Config is a fully managed native service to assess, audit, and evaluate the configurations of your AWS resources by AWS itself.
While traditional vulnerability scanners look for outdated software patches, AWS Config acts as a continuous watchdog for cloud misconfigurations. It acts as a single source of truth, simplifying security analysis, compliance auditing, operational troubleshooting, and change management without requiring third-party agent installations.
Key Features
- Automatically tracks resource configurations and alerts you the moment a setup drifts from your established security baselines.
- Continuously checks your recorded AWS resource configurations against expected values and industry frameworks like CIS AWS Foundations Benchmark, HIPAA, or PCI-DSS.
- Discovers all active resources and acts as a time machine. It keeps a detailed history of configuration changes and deletions, which is invaluable for forensic security investigations.
- Pinpoints the exact configuration change that caused a security incident or operational outage, drastically reducing your Mean Time to Resolution (MTTR).
AWS Config Use Case
Continuous compliance auditing, configuration drift detection, and maintaining a historical inventory of AWS assets for forensic analysis.
I would suggest AWS Config to enterprises. The charges are per configuration item recorded and per rule evaluation. If you have a large environment where EC2 instances are constantly spinning up and down, costs can spike quickly.
Amazon Inspector
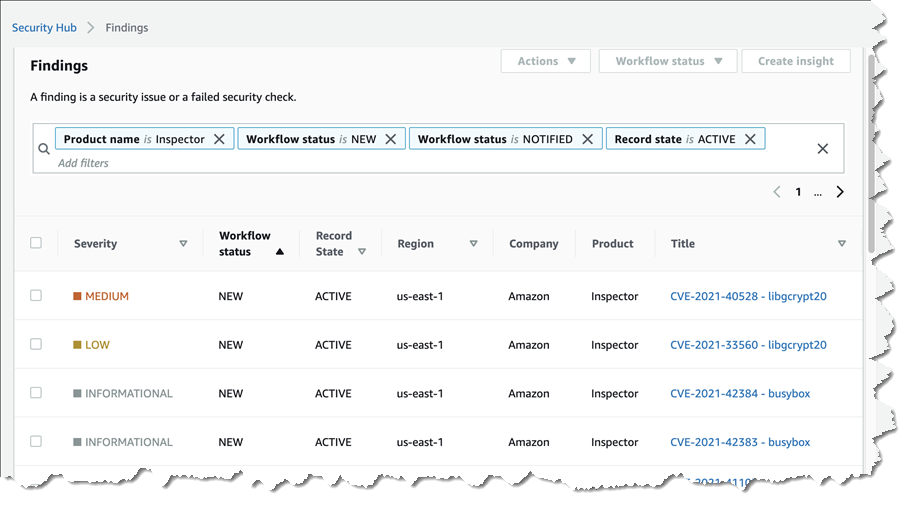
AWS Config acts as your watchdog for infrastructure misconfigurations, and Amazon Inspector is your frontline defense against software flaws. It is a fully managed AWS vulnerability scanner that hunts for CVEs (Common Vulnerabilities and Exposures) and unintended network exposure.
The moment you spin up a new Amazon EC2 instance, push a new container image to Amazon ECR, or deploy a new AWS Lambda function, Inspector automatically discovers it and begins scanning for vulnerabilities.
I like its contextual risk scoring. Instead of just handing you a generic CVSS score and leaving you to panic, Inspector analyzes the actual AWS environment. If a vulnerability exists on an EC2 instance, but that instance is completely isolated from the public internet in a private subnet, Inspector dynamically lowers the risk score so your security team knows it isn’t an emergency.
Key Features
- Workloads are automatically evaluated for new CVEs the moment they are deployed or when a new zero-day vulnerability is published.
- Intelligently combines standard CVE data with network accessibility and exploitability trends to prioritize which vulnerabilities your team needs to patch first.
- Routes all vulnerability findings directly into AWS Security Hub and Amazon EventBridge.
I would suggest Amazon Inspector for CVE scanning, container vulnerability management, and automated zero-day threat detection without leaving the AWS console.
To get the most out of Amazon Inspector for EC2, ensure the AWS Systems Manager Agent is installed and updated across your VMs. Inspector uses the SSM agent to collect software inventory data. If the agent is offline, Inspector can’t see the vulnerabilities!
Amazon Macie
AWS Config tells you if an S3 bucket is publicly accessible, and Amazon Macie tells you exactly what is inside that bucket. Macie is a managed data security and data privacy service that uses machine learning and pattern matching to discover and protect your sensitive data.
Think of Macie as your native AWS Data Loss Prevention (DLP) engine. It continuously evaluates your S3 environment and automatically alerts you if it finds unencrypted buckets, publicly accessible data, or files containing Personally Identifiable Information (PII) like credit card numbers, passport data, or AWS secret keys.

You can use Amazon Macie for S3 bucket security, Data Security Posture Management (DSPM), and automated compliance auditing for data privacy laws like GDPR, HIPAA, and CCPA.
Amazon Macie charges based on the data processed for data discovery. If you have petabytes of logs or media files in S3, do not run a blanket scan. Instead, use Macie’s Automated Sensitive Data Discovery feature, which intelligently samples a fraction of your S3 objects to give you a highly accurate risk map at a fraction of the cost.
FYI.. on top of the above 3 native AWS security tools, I would also suggest checking out Automated Security Helper (ASH).
Best Open-Source AWS Scanners
Open-source AWS scanning tools are good for bootstrapped startups or teams with in-house skills engineers, as you need to spend time setting them up.
Prowler
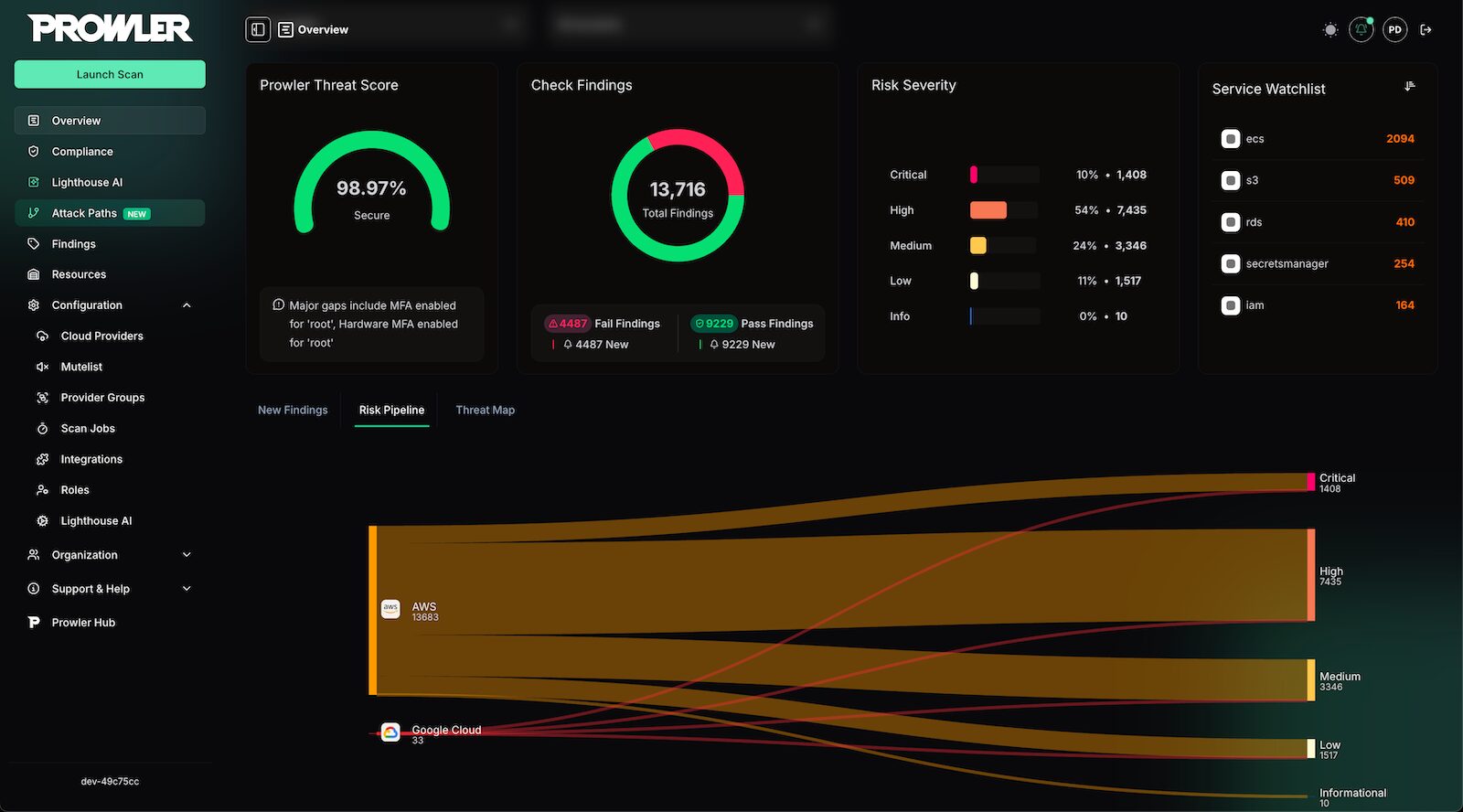
Prowler is an open-source cloud security platform. It is a command-line tool for AWS security configuration assessments, auditing, incident response, and continuous hardening.
It originally started as a simple script to check compliance with the CIS AWS Foundations Benchmark. Today, it performs over 550+ security checks covering major compliance frameworks like HIPAA, GDPR, SOC2, ISO-27001, and forensics readiness.
Prowler inspects your AWS Identity and Access Management (IAM) practices, logging, monitoring, and network configurations. It dives into a wide array of AWS services, including Redshift, CloudFront, ElastiCache, OpenSearch (Elasticsearch), and API Gateway.
Key Features
- Identifies exposed assets, overly permissive IAM roles, and missing security controls across your entire AWS environment.
- You don’t have to run the entire suite. You can execute specific checks to save time.
- Natively supports AWS Organizations to scan multiple AWS accounts in parallel using cross-account roles.
- Integrates with AWS Security Hub, Jira, Slack, and custom webhooks.
Because it is open-source and free, Prowler is the perfect starting point for bootstrapped startups. Prowler is also available as a cloud service, which starts at $79/cloud account/month.
Aqua Trivy
Modern AWS architectures are mostly built on containers and serverless functions. While Amazon Inspector is fantastic for scanning resources after they are deployed, what if you want to catch vulnerabilities before they ever reach your AWS environment?
This is where you need Trivy.
Trivy is an all-in-one open-source security scanner. It allows developers to scan their container images, file systems, and Infrastructure as Code (IaC) directly in their CI/CD pipelines before anything is pushed to AWS.
If your engineering team uses Terraform or AWS CloudFormation to build infrastructure, Trivy will scan those templates and warn you if you are about to deploy an exposed S3 bucket or an overly permissive IAM role. It is fast, stateless, and requires zero prerequisites to run.
Key Features
- Detects OS packages and language-specific dependencies (npm, pip, gem) containing CVEs before the image is pushed to the Amazon Elastic Container Registry.
- Natively connects to your Amazon Elastic Kubernetes Service (EKS) clusters to scan running workloads, Kubernetes misconfigurations, and RBAC flaws.
- Easily generates a Software Bill of Materials (SBOM) for your AWS workloads, which has become a strict compliance requirement for enterprise software supply chains.
The best way to use Trivy in AWS is to integrate it directly into AWS CodeBuild or GitHub Actions. You can configure Trivy to break the build and fail the pipeline if it detects a CRITICAL vulnerability.
FYI… Aqua has another open-source security tool called Cloudsploit for security posture management.
Cloud-Audit
Cloud-Audit acts as a security scanner for AWS accounts. It is primarily intended for DevOps and infrastructure security teams who need real-world threat reports. Currently, the tool performs 45+ checks across 15 AWS services, generating ready-to-use fixes (AWS CLI + Terraform).
The latest version of the tool adds an attack chain detection feature. Previously, this functionality was only available on commercial CNAPP platforms. This allows for the correlation of multi-stage attack paths that could pose a threat from an attacker’s perspective.
An example attack chain detected by cloud-audit could be: EC2 with a public security group -> with an assigned IAM administrator role -> with IMDSv1 service enabled. Three separate detections combine into one direct path to a complete takeover of an AWS account.
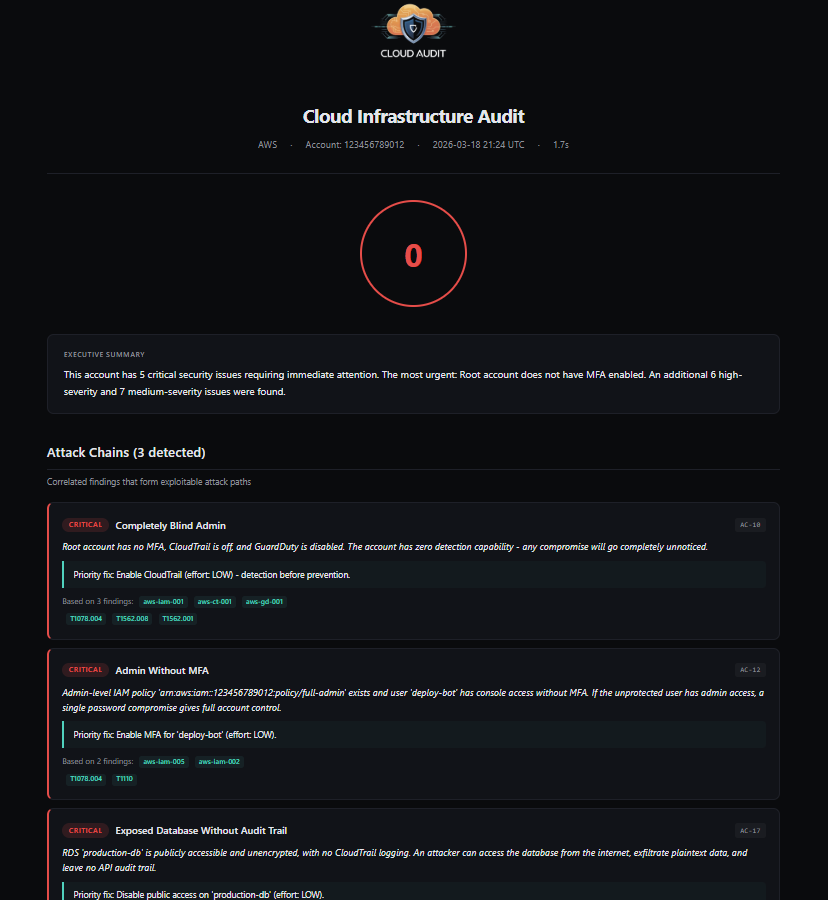
Key Features
- 16 attack chain rules that correlate findings across AWS services with vulnerable attack paths, based on MITRE ATT&CK Cloud Matrix and Datadog pathfinding cloud research.
- Each discovery includes an AWS CLI command to copy and paste and a Terraform HCL code snippet to resolve the issue.
- Compare two scans to see new, corrected, and changed findings over time.
cloud-audit can be installed via pippip install cloud-audit, Docker Hub docker pull haitmg/cloud-audit, or GHCR.
You can refer to cloud-audit documentation to get started.
ElectricEye
ElectricEye is an open-source Cloud Security Posture Management and Attack Surface Management tool. Written entirely in Python, it continuously monitors your AWS environment for misconfigurations and vulnerabilities that could degrade the confidentiality, integrity, or availability of your data.
What makes ElectricEye truly special for AWS users is its native integration with AWS Security Hub. Unlike other tools that require complex parsing to export data, ElectricEye natively formats all of its findings into the AWS Security Finding Format (ASFF). This means you can deploy it, and within minutes, your native AWS Security Hub dashboard will light up with contextualized compliance evaluations mapped to frameworks like NIST CSF, ISO 27001, and PCI-DSS.
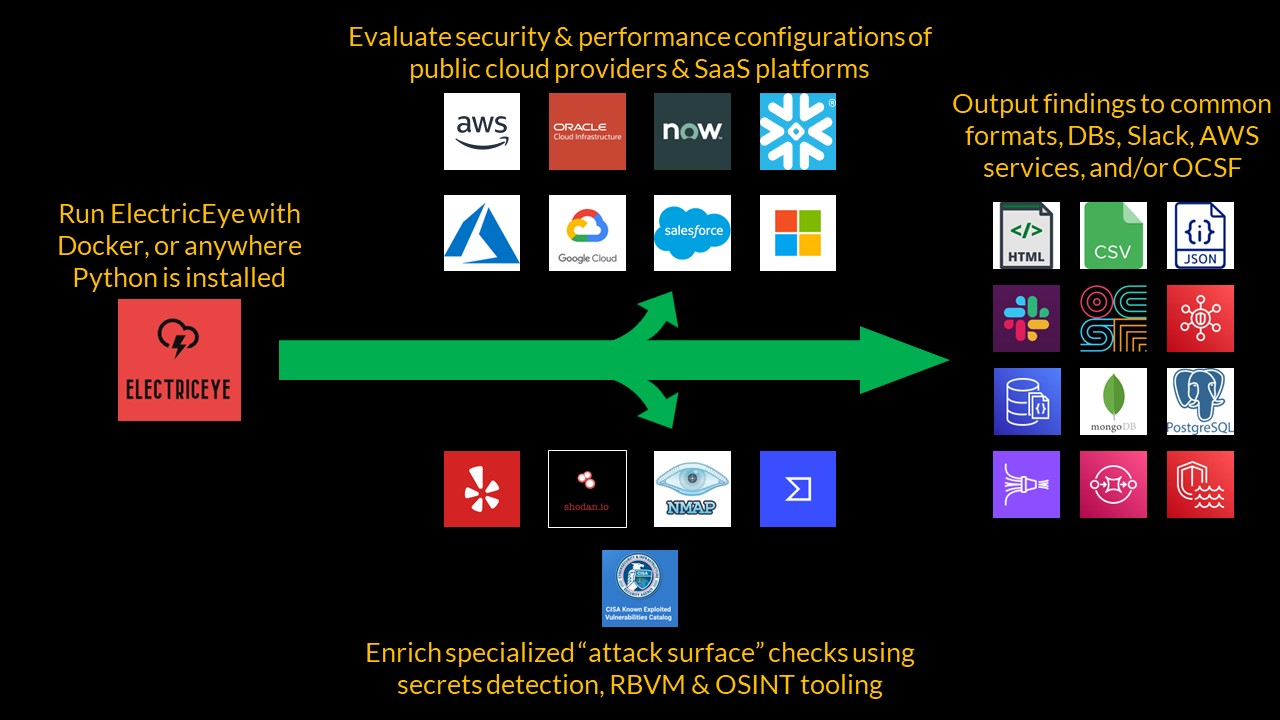
You can deploy it via the AWS CDK as a scheduled AWS Lambda function. This gives you a fully automated, serverless, and practically free continuous compliance engine that runs 24/7 in the background.
More Open-Source Scanner
Also worth knowing the following tools for AWS security scans.
- CloudMapper – very popular with more than 6000 stars, but unfortunately it has not been updated since 2021.
- ScoutSuite – multi-cloud auditing tool but no updates since 2024.
- Cloud Custodian (c7n) – actively maintained, suitable for real-time compliance security policies.
- S3Scanner – as the name suggests, mainly to find misconfigured S3 buckets.
- Pacu – actively maintained, AWS exploitation framework.
Best Enterprise SaaS Scanners
The following are suitable for large organizations running critical applications on AWS. They are expensive but totally worth it.
Orca Security
Orca Security completely revolutionized AWS vulnerability scanning by pioneering 100% agentless scanning. As a leading CNAPP, Orca uses its patented SideScanning™ technology. Orca integrates directly with the AWS API and reads your Amazon EBS volumes out-of-band.
This means Orca can scan your entire AWS environment for CVEs, malware, misconfigurations, and exposed sensitive data in minutes.
Furthermore, it uses Attack Path Analysis to show you how different risks combine.
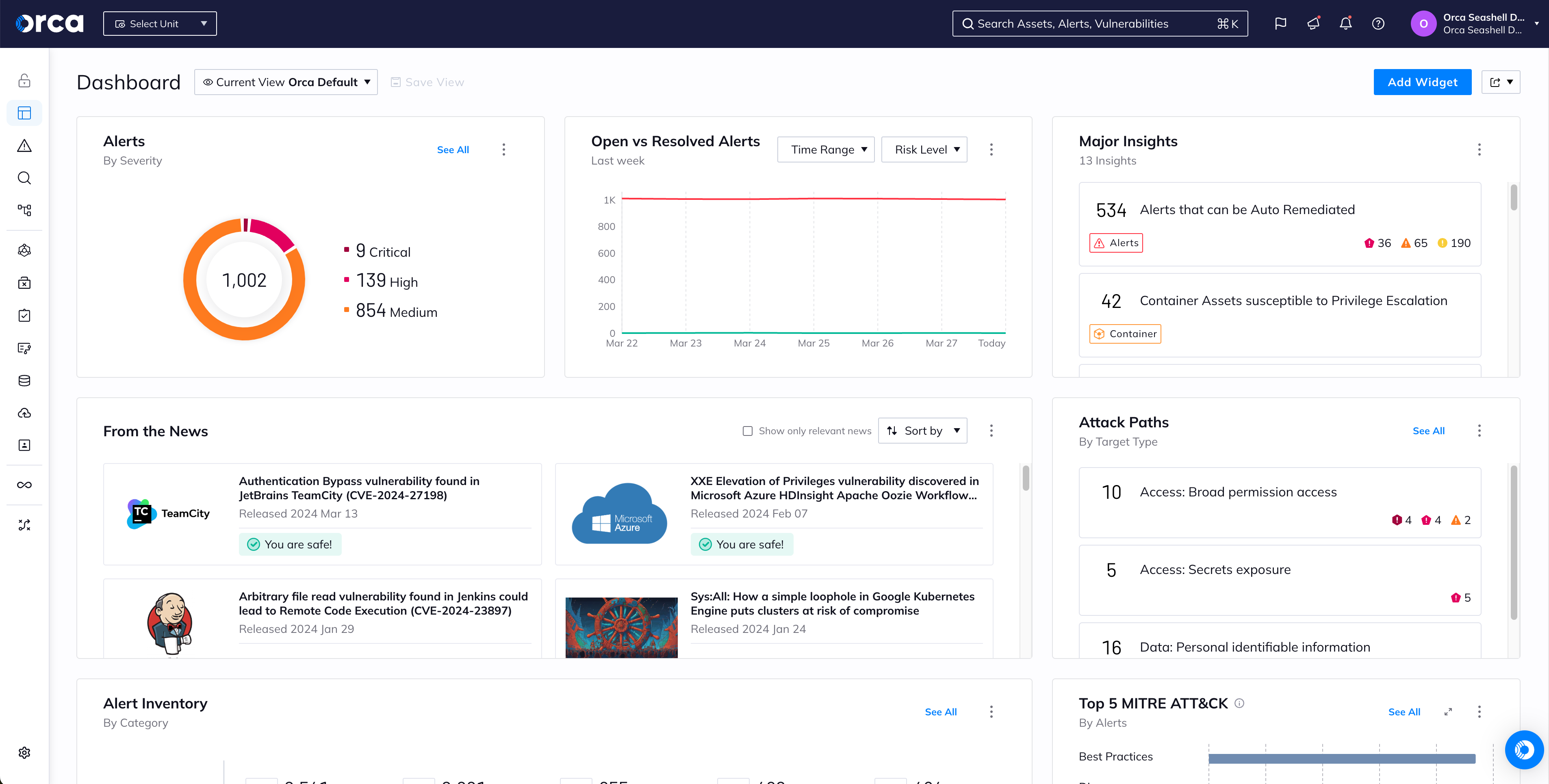
Key Features
- Scans EC2 instances, containers, and serverless functions completely out-of-band by analyzing EBS volume snapshots.
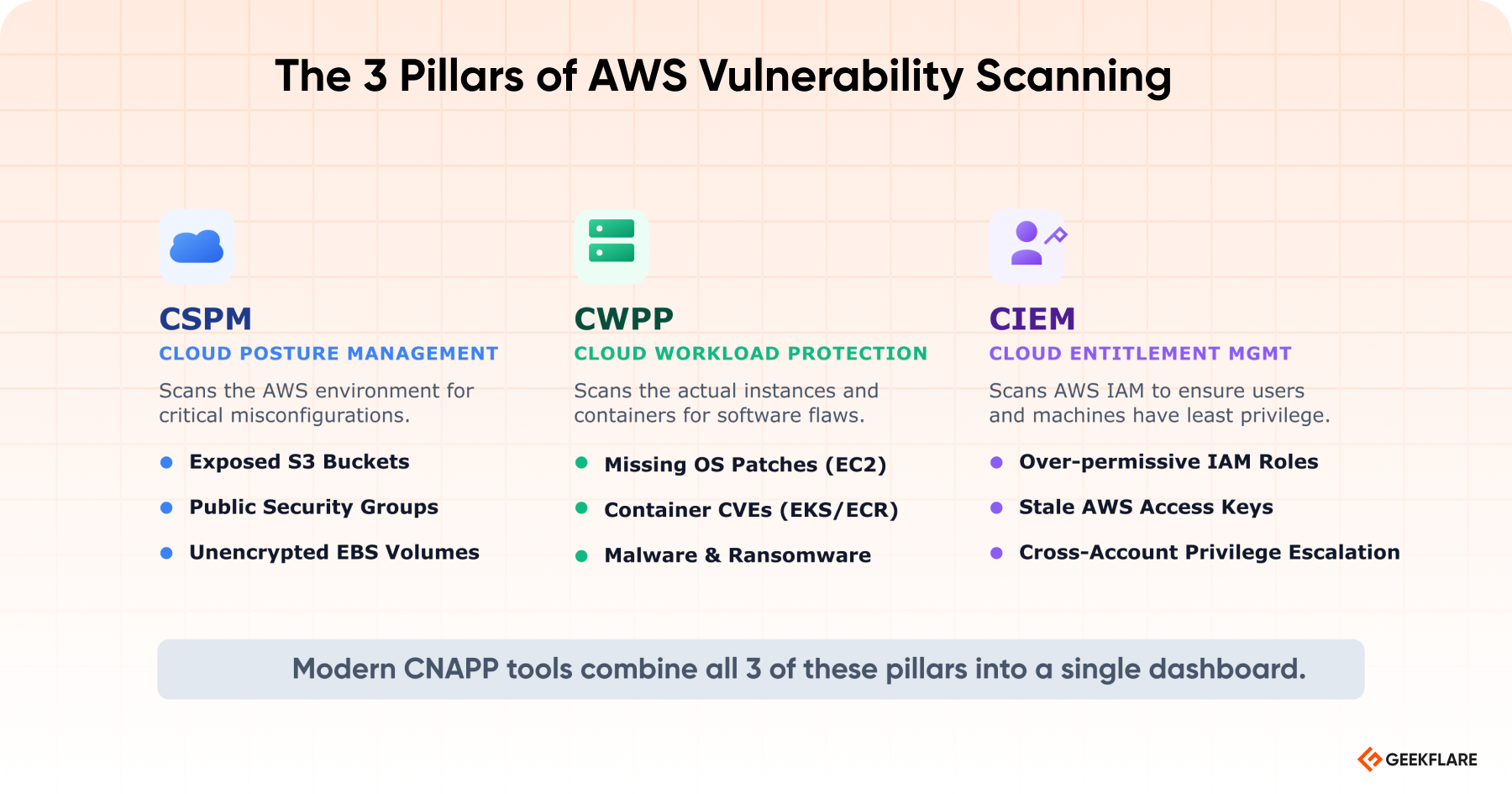
- Replaces multiple tools by combining CSPM, CWPP, CIEM, and DSPM into a single platform.
- You can connect Orca to your AWS organization via a single IAM cross-account role and get full visibility across thousands of accounts.
Orca is suitable for mid-market to enterprises that are looking to adopt CNAPP and prioritize vulnerabilities based on actual environmental risk.
Intruder
Intruder is an enterprise-grade, cloud-native vulnerability scanner to monitor your external attack surface across AWS, GCP, and Azure.
Intruder keeps track of dynamic cloud assets. In AWS, IP addresses change constantly, and developers frequently spin up new EC2 instances or Application Load Balancers (ALBs) without notifying security. Intruder integrates directly with your AWS accounts to automatically discover new external assets and synchronize your scan targets in real time.
It continuously observes what you are exposing to the public internet. If a developer accidentally opens an SSH port to the world via an AWS Security Group, Intruder will immediately detect the change and alert your team before an attacker can exploit it.
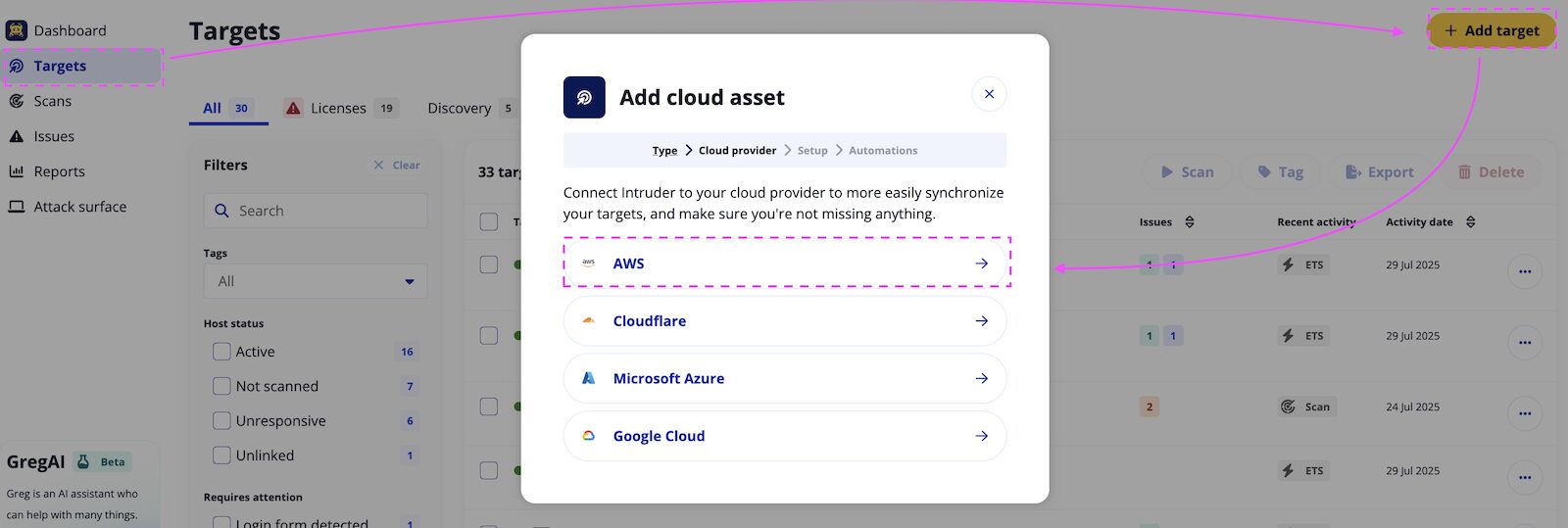
Key Features
- You don’t have to wait for a scheduled scan. When a new critical zero-day vulnerability is announced, Intruder proactively scans your external AWS perimeter and alerts you if you are exposed.
- Identifies missing OS patches, cloud misconfigurations, and CMS flaws.
- Intruder performs Dynamic Application Security Testing (DAST) to find OWASP Top 10 vulnerabilities on your live web applications hosted in AWS.
I would suggest Intruder to use as External Attack Surface Management (EASM), continuous perimeter scanning, and automated web application vulnerability scanning (DAST).
Intruder Pricing
Intruder Cloud plan starts from $239/month. You can get a 14-day free trial.
Tenable Cloud Security
Tenable Cloud Security provides visibility across your entire hybrid and multi-cloud environment. It operates as a CNAPP, offering 100% agentless scanning for your AWS workloads, containers, and infrastructure as code (IaC).
Tenable has industry-leading CIEM (Cloud Infrastructure Entitlement Management) capabilities. In AWS, compromised Identity and Access Management (IAM) roles are the root cause of most breaches. Tenable’s CIEM engine analyzes your AWS IAM policies, calculates effective permissions, and automatically generates least-privilege JSON policies to remediate overly permissive roles.
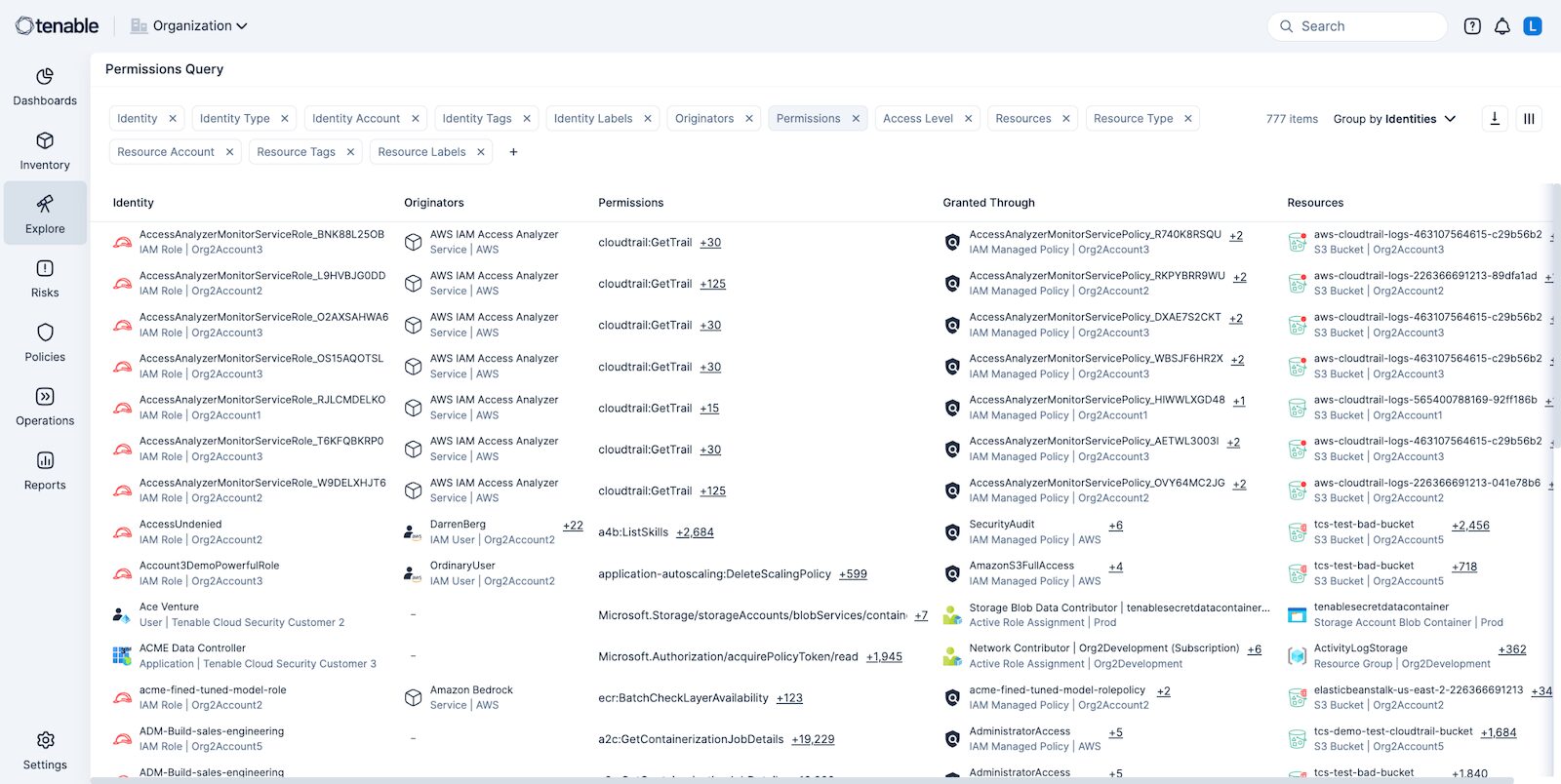
Key Features
- Aggregates data from your AWS cloud, traditional on-premise IT, web apps, and identity systems into a single, unified risk metric for the C-suite.
- Find toxic IAM combinations, visualizing exactly which AWS users or machine roles have hidden administrative access to S3 or RDS.
- Combines Cloud Security Posture Management (CSPM), Cloud Workload Protection (CWPP), and Kubernetes Security Posture Management (KSPM) for Amazon EKS in one interface.
- While it natively supports agentless scanning via AWS API integrations, it still allows you to deploy traditional agents for continuous inspection of legacy workloads.
If you are migrating an on-premise data center to AWS, Tenable is one of the best choices. You can use traditional Nessus agents for your on-prem servers and Tenable’s agentless CNAPP for your new AWS workloads.
More enterprise options for AWS scanning.
- Wiz – Wiz has recently joined Google Cloud, so the future is unclear if it’s going to operate as an independent entity or merge into the Google Cloud security suite.
- Qualys – Similar to Tenable, Qualys has multiple cloud security options for enterprises.
- LevelBlue – multiple security services, including managed cloud security for large global organizations.
Conclusion
Securing an AWS environment is no longer a manual exercise. It should be part of continuous security. The right tool choice depends entirely on your infrastructure size and budget.
- If you want native integrations and billing, use Amazon Inspector, Macie, or AWS Config.
- For the bootstrapped startup & DevSecOps Team, try the open-source combination of Prowler and Aqua Trivy.
- Choose Intruder if you are a lean IT team.
- For the enterprise, Orca Security or Tenable are best suited.





