Best Website Defacement Monitoring Tools in 2026
Stay up to date on Tech and Business News. Join Geekflare Newsletter →
Safeguard your online presence with expert security tips and tools. Protect against malware, enhance website security, and stay ahead of the latest cyber threats.
Best Website Defacement Monitoring Tools in 2026

9 Best Tools to Monitor Website Changes in 2026
How to Unblock Websites: Best Methods and Tools

9 Best DNS Filtering Software in 2026

15 Best Website Scanner to Find Security Vulnerabilities and Malware in 2026

11 Best WordPress Vulnerability Scanners to Secure Your Site in 2026

15 Open Source Vulnerability Scanners for 2026

Best Enterprise Password Managers for 2026

12 Disaster Recovery Solutions for Small to Medium Businesses [2026]

Best Privileged Access Management (PAM) Solutions in 2026

9 Best Threat Intelligence Platforms in 2026

9 Web3 Auth Platforms to Secure Your User Login Process [2026]

10 Best Anti-Phishing Tools for Businesses in 2026

13 Best DDoS Protection Services in 2026

18 Cybersecurity Data and Statistics To Make You More Vigilant (2026)

How to Become a Bug Bounty Hunter in 2026?

9 Best Hardware Security Keys for Two-Factor Authentication [2026]

The No-Fluff Roadmap to Becoming an Ethical Hacker [2026]

19 Phishing Statistics and Trends [Updated 2026]

15 Best ERM Software for 2026
11 Best Secret Management Tools to Secure Your Digital Assets in 2026

15 Best Web Vulnerability Scanner in 2026 to Protect Against Attacks
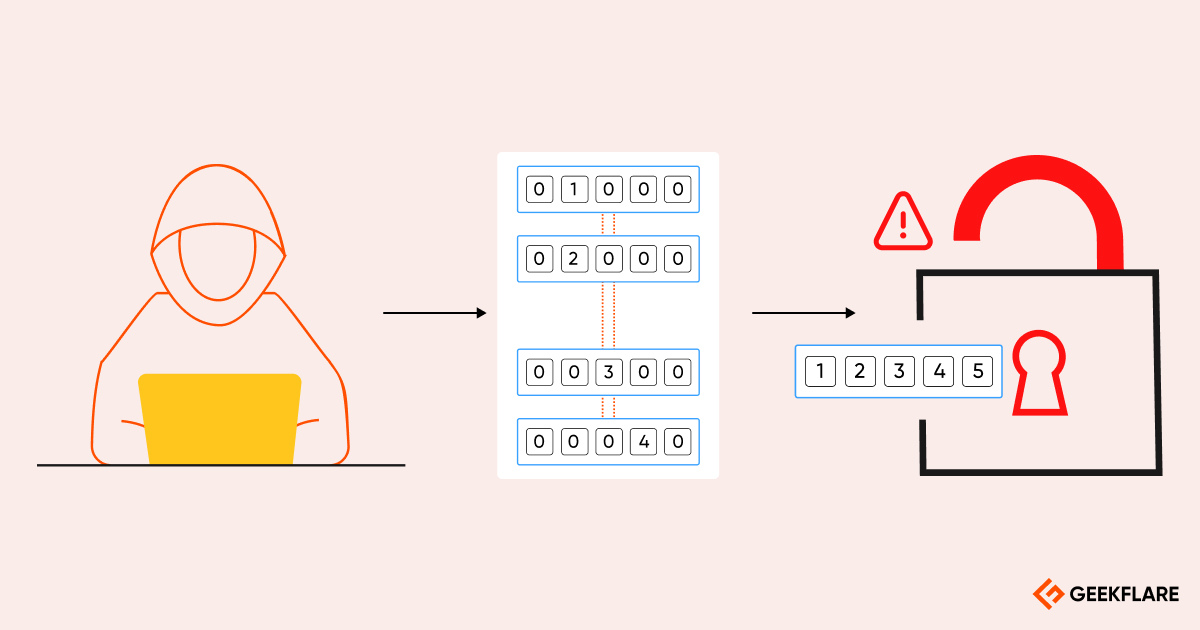
Top Brute Force Attack Tools (2026)

Top 12 Attack Surface Management Software in 2026

11 Best Network Access Control Solutions for Businesses in 2026

Is Dashlane Worth the Hype? My Testing Experience

24 Best SSL Checker Tools to Troubleshoot TLS and Certificate Issues

12 HTTP Client and Web Debugging Proxy Tools

18 Best Web Application Firewall Software [Top Picks]

Red Light, Green Light: Endpoint Security Edition