User authentication is a security measure to provide rightful access to your digital properties like your website or application. User authentication software verifies the identity of users attempting to access digital resources and ensures data security.
If you’re a big company with the necessary infrastructure to ensure data security and compliance, then you probably don’t need a 3rd-party solution.
But it’s quite the opposite if:
- This isn’t your domain of expertise.
- You’re a startup or simply can’t bear the financial overhead.
- You can’t ensure the proper data management and security.
- A data breach can break your organization.
So, don’t make pizza if you aren’t Dominos. Chances are you’ll spoil it. But since user data is a lot more serious than wasting a pepperoni pizza, it’s best to rely on the pros when it comes to managing and securing it.
While an average business person will straightaway run towards Auth0 or Firebase, there are others as well. Let’s look at some of the best user authentication platforms apart from Auth0 and Firebase.
- 1. Authsignal
- 2. Stytch
- 3. Ory
- 4. Supabase
- 5. Okta
- 6. PingIdentity
- 7. Keycloak
- 8. Frontegg
- 9. Authress
- 10. Auth0
- 11. Firebase
- 12. Amazon Cognito
- 13. OneLogin
- Show less
You can trust Geekflare
At Geekflare, trust and transparency are paramount. Our team of experts, with over 185 years of combined experience in business and technology, tests and reviews software, ensuring our ratings and awards are unbiased and reliable. Learn how we test.
1. Authsignal
Delivering fine-tuned consumer passwordless authentication experiences has never been easier than with Authsignal. Focused on the enrollment and authentication of customer identity, Authsignal streamlines the deployment of passwordless authentication (MFA) and passkeys to enable mid-market and enterprise businesses to seamlessly authenticate user identity any where in their customer journey.
Authsignal works with your existing identity stack and requires no migration. Drop in Authsignal leveraging their out-of-the-box integrations with Auth0, Microsoft Azure AD B2C, AWS Cognito, Twillo, Messagbrid, and more. Authsignal’s approach to passwordless authentication enables passwordless challenge flows utilizing Passkeys and other common authentication factors to be inserted into your existing customer flows or identity stack anywhere there’s a need to increase trust and safety. Integration and configuration time is minimized via their flexible API.
The No-Code Rules Engine enables customer journeys to be deployed in a matter of hours, significantly reducing the cost and time of engineering and development teams typically associated with hardcoding rules. Drop in Passwordless Authentication challenges anywhere in the customer journey.
Reduce Customer Support time with a single view of the customer. Utilizing our Track Action API, Authsignal offers a single FraudOps view of your customers’ actions, enabling the reduction of queue times and bringing peace of mind to Fraud and Operational teams. Gain a complete Audit trail of actions.
Features:
- Orchestrate Customer Journey Flows
- Authenticate user identity and integrate with multiple identity vendors
- No Code rules engine – build rules in minutes, create challenge flows, Block, Allow, Challenge and Review
- Single View of the Customer
- Deploy either Multi-Factor Authentication or Passwordless Authentication
- Passwordless Authentication Support for
- TOTP/Authenticator apps
- SMS OTP / WhatsApp OTP
- FIDO2/WebAuthn
- Email Magic links & OTP
- Passkeys
- Push Authentication

Authsignal Marketplace
Integrated with industry-leading fraud, risk and AML partners, Authsignal brings together the best-in-class vendors to deliver a comprehensive view of customer behaviour in one central place. Leveraging the enchanted data marketplace enables customers to create a central workspace for Fraud Ops teams to manage investigations and make decisions easily.
Authsignal integrates with:
- Veriff (IdV/KYC)
- iProove (IdV/KYC)
- Deduce (Identity Network)
- Coinfirm (AML/KYC)
- SMS Sim Swap Shield
2. Stytch
Stytch is a staunch supporter of password-less authentication. It is focused on improving user experience and cutting developer headaches by doing just that.
Password-less authentication is very similar to using Slack. They allow for 3rd-party logins or send an email link for authentication, but never use passwords. Stytch calls them magic links.
You can use their SDKs for quick deployment or direct API to use the authentication method of your choice. There are multiple ways available such as social logins, SMS/WhatsApp/Email passcodes, email magic links, TOTP apps, etc.

Stytch has flexible pricing that adjusts as per your active user base. And there is a free USD 100 worth of credits as the welcome package.
3. Ory
Ory brings complete user experience control with its headless user authentication management.
There is a free tier and a cloud one if you intend to use a custom domain. Besides, Ory lets you create custom identity schemas to build personalized user authentication/registration forms.
It also supports building single-page applications using React, Next.js, Gatsby, and AngularJS. With Ory, developers can test and validate the system without needing to code.
Ory presents itself as a complete authentication and authorization platform with identity & permission management. It is a zero-trust network that is compatible with OAuth2 and OpenID Connect.

Ory also comes with FIDO 2 compatible two-factor authentication (2FA) and a command-line developer-friendly interface. Finally, you can start with a free-forever plan and upgrade if need be.
4. Supabase
Supabase calls itself an open-source Firebase alternative.
Similar to STYTCH, Supabase has multiple ways to take in your users. You can use the conventional email & password, magic links, social, or phone logins. In addition, you can integrate 3rd-party authentication protocols like OAuth with a few clicks.

Powered with react libraries, you can quickly start with Supabase’s pre-build auth widgets. Besides, you can integrate Supabase with REST and real-time APIs with support for GraphQL coming in future updates.
Supabase also has user management and authorization mechanisms to implement granular access rules.
And ultimately, Supabase has a free, paid, and pay-as-you-go subscription plan matching all possible use cases.
5. Okta
Okta is again a flagbearer of password-less security. However, you can ask for the strongest passwords with Okta as well.
In addition to tweaking password requirements, you can also enable multifactor authentication (MFA). Moreover, one can set up Okta’s cloud authentication and let the users sign in via biometrics or push notifications.
Besides, you get a real-time Syslog with advanced searches to identify issues for instant troubleshooting.
Okta gives importance to progressive profiling, which means minimum upfront information at registrations. The aim is to minimize user inconvenience, boost registrations, and gradually complete the user profile.

Okta allows for excellent API security by integrating identity protocols like OAuth. And you will have a single point for all API authorization policies to integrate security and development.
And finally, it permits easy B2B integrations with security frameworks such as OpenID Connect and SAML in addition to legacy support for turnkey Active Directory & LDAP integration.
6. PingIdentity
PingIdentity is shaped as an intelligent central authentication module for all your cloud, in-house, and SaaS implementations.
This lets you deploy adaptive authentication based on user behavior and risk assessment.
It benefits from multiple authentication sources at the same time to adjust for specific security policies as per the application. You can create multiple environments – for your customers or for your internal employees.
This also has support for MFA and diverse authentication rules. In addition, PingIdentity permits for IdP- and SP-initiated SSO. Besides, you can enable SSO for APIs, Mobiles & SaaS applications.

And you can easily integrate it with 3rd-party applications like Office 365, G Suite, Atlassian tools, etc.
7. Keycloak
Keycloak is an open-source user identity and access management platform.
You can integrate Keycloak with your applications to have a single-sign-in and single-sign-out experience. Moreover, one can activate social logins without any modification in code. Additionally, it allows user authentication via existing OpenID Connect or SAML 2.0
Keycloak supports connecting to existing LDAP or active directory servers and using them as a central user database. Its account management console lets users manage their profile, update passwords, set 2FA, etc.
Admin Console gives you control over all the features, including identity brokering, creating applications, defining granular access control, etc.
Finally, as Keycloak is open-source, you can modify the code and fork out or switch anytime without any issues, such as a vendor lock.
8. Frontegg
In contrast with the funny name, Frontegg is a developer-friendly user authentication and management solution for just about any organization.
You can deploy its SSO to integrate enterprise IDPs via SAML & OpenID connect. Frontegg also comes equipped with social logins and multi-factor authentication.
In addition, it supports advanced features like Google Captcha and password-less authentication with magic links. Besides, users can manage their own teams by creating profiles and permissions. The user profile also has audit logs for the customers to check and control their login activities.
You can also empower your users to enable webhooks notifications to generate and manage API authentication tokens.

Forntegg also has some industry-leading attributes like forced MFA, user lockout, password change history, IP blocking, etc. In addition, you can apply Frontegg for machine-to-machine authorization. And finally, there is a facility to enable custom domains for cross-site authentication.
Frontegg has an impressive forever-free plan. However, some advanced features are reserved for paid customers.
9. Authress
With its long list of features, Authress is a brilliant user authentication and a Firebase alternative.
Authress bets heavily on its authorization API and integration with your existing identity solutions. You can define granular access controls and group them accordingly by user roles.
In addition, Authress also has machine-to-machine authentication and unlimited enterprise integrations. Similarly, you can use SSO and any number of social logins for your application authentication.

It gives you comprehensive usage logs and unlimited users with import/export support. You can also use your branding with a custom domain.
While there is no free-forever subscription, your first 1000 API calls are free with standard and enterprise plans.
10. Auth0
Auth0 is the go-to user authentication platform and a Firebase alternative for good reasons.
It features a universal login for all your applications to add user convenience. This is like having SSO between multiple apps. So the user won’t get annoyed to log in separately on other apps; instead will be auto-signed in via SSO.
There is a central feature control dashboard for social logins, problem detections, and MFA. One can also use custom domains for seamless branding.

During the sign-up process, Auth0 actually checks whether you are a coder or not. And if you are not a technical expert, they take you through a separate onboarding process, which I find very helpful.
Moreover, there are password-less magic links for an even better user experience. Auth0 has flexible subscriptions for many use cases, including a free tier.
11. Firebase
Firebase is Google’s range of products, including the user authentication platform.
You can use Firebase authentication via passwords, phone numbers, or social logins. They have pre-built templates and SDKs to get started without much effort. Firebase also supports Gemini AI to help you build your authentication apps.
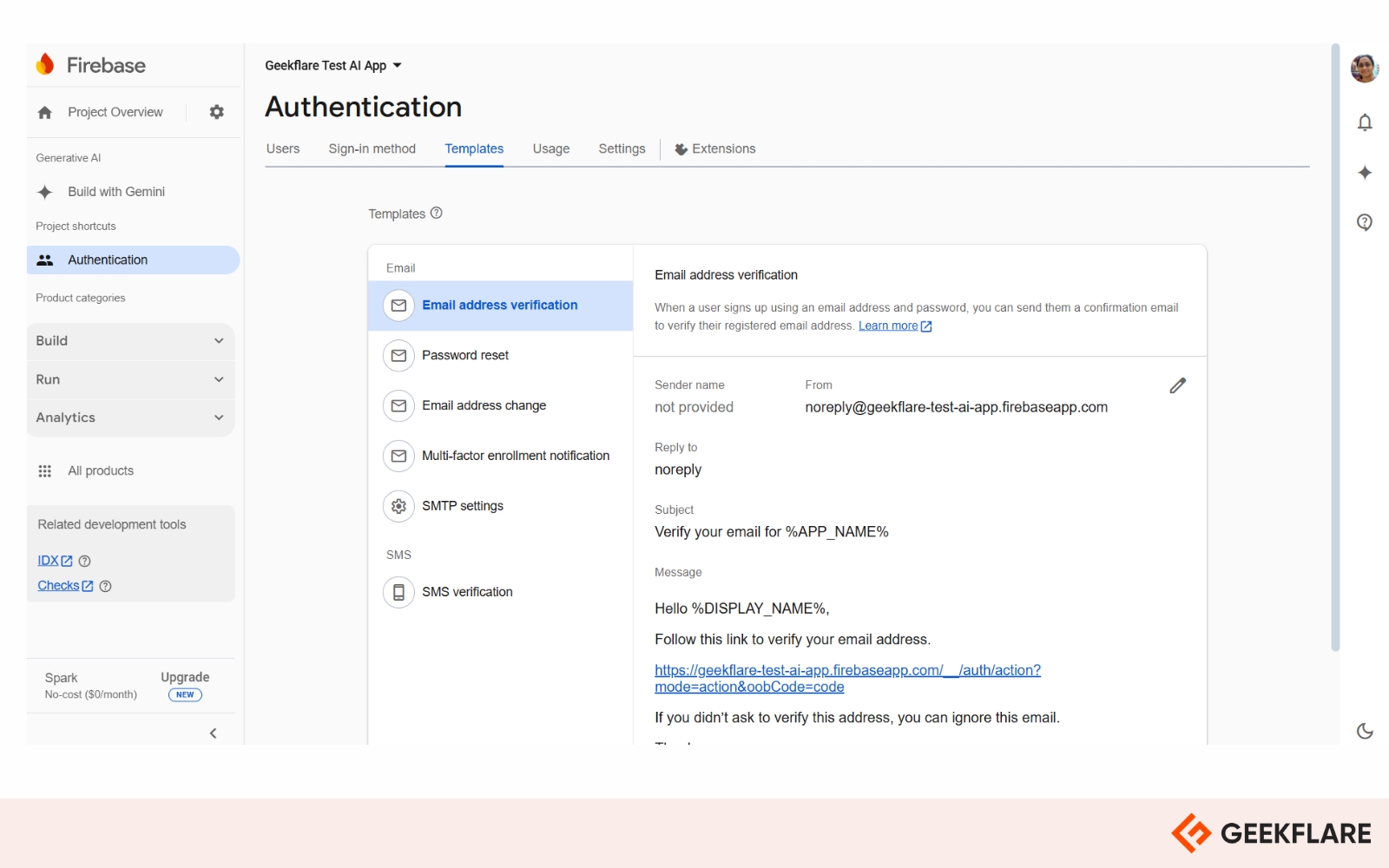
And, there is a free plan to start with application authentication with generous limits, after which pay-as-you-go kicks in.
12. Amazon Cognito
Cognito is Amazon’s cloud application authentication solution for the masses. It’s a low code deployment that can be used with conventional passwords or 3rd party logins like Google or Facebook.
It comes with a flexible UI that can be changed as per the use case. This also has advanced user authentication features like risk-based adaptive mode.
There is an excellent free tier, and subsequently, it upgrades to a pay-as-you-go subscription after consumption of free credits.
13. OneLogin
OneLogin by OneIdentity is yet another Firebase alternative with noteworthy advanced features.
OneLogin has adaptive MFA, SSO, and Vigilance AI, which reportedly uses machine learning to safeguard against advanced threats.

You can also utilize OneLogin’s simple APIs for a personalized user experience. One can also deploy their smart factor authentication for authorizing users via SMS codes or automated phone calls.
Finally, you can begin with OneLogin with a free trial to get a taste of their service. However, please note that trial accounts are not eligible for any technical support, and you’ll need to go through their documentation to find your way through the platform.
Final words
3rd-party user authentication platforms are a no-brainer for startup and mid-level organizations.
Building and applying your in-house solutions simply aren’t worth the efforts and risk. Even for the premium companies, it’s best to give the task to the experts rather than mishandling it.
While choosing any plan, try to steer away from any vendor locks. Conclusively, opting for an open-source application authentication can be rewarding in the long term, even if it seems short on some features.


