Find vulnerabilities in your network infrastructure before anyone else.
Don’t wait for a breach to expose your network’s flaws. Take control of your security with proactive vulnerability scanning. This isn’t just about ticking a compliance box, it’s about safeguarding customer data, organization reputation, and preventing financial loss.
Note: This is not about finding vulnerabilities in a website. Below, I’ll talk about finding security risks in network infrastructure.
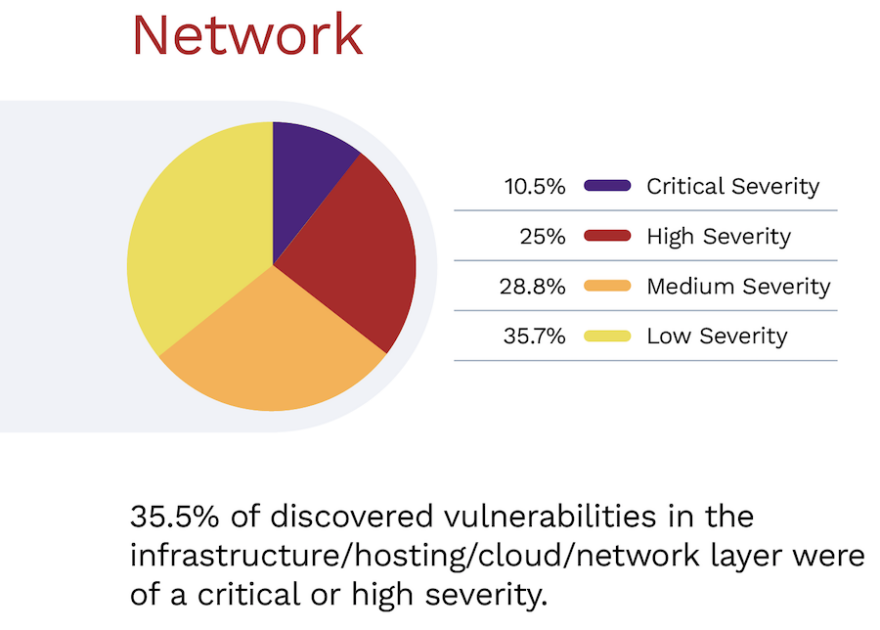
The latest report by edgescan shows more than 35% of discovered network vulnerabilities were high or critical severity.
There are many network scanners, and not all fit the requirement. So, to make it easier for you, I’ve compiled a list of the best network vulnerability scanners.
- 1. Intruder
- 2. HostedScan Security
- 3. ManageEngine Vulnerability Manager Plus
- 4. Tenable Nessus
- 5. AlienVault USM
- 6. InsightVM
- 7. Acunetix
- 8. OpenVAS
- 9. Qualys
- Show less
You can trust Geekflare
At Geekflare, trust and transparency are paramount. Our team of experts, with over 185 years of combined experience in business and technology, tests and reviews software, ensuring our ratings and awards are unbiased and reliable. Learn how we test.
1. Intruder
Intruder is a proactive vulnerability scanner that scans you as soon as new vulnerabilities are discovered.

Designed for external-facing systems, Intruder detects over 10,000 security weaknesses, including WannaCry, Heartbleed, and SQL Injection, and helps to reduce your attack surface by highlighting ports and services which should not be exposed to the internet.

Other unique features include AWS and Slack integration, which allows Intruder to keep track of what systems you have facing the internet and notify you when new vulnerabilities are discovered. Integration with Jira means new issues can be sent straight to your development team.
Intruder is popular with startups and medium-sized businesses because it makes vulnerability management easy for small teams.
Intruder offers a 14-day free trial so that you can see all the features in action yourself.
2. HostedScan Security
HostedScan Security provides a powerful and comprehensive set of vulnerability scans for network, servers, web applications, and IT assets.
With HostedScan, you can run vulnerability scans for all of your external systems. HostedScan offers a network vulnerability scan powered by OpenVAS, the industry-leading open-source network scanner. Additionally, HostedScan provides a TCP port scan, a UDP port scan, and a web application scan to find issues such as SQL injection and cross-site scripting.

HostedScan has dashboards, reports, and vulnerability risk management features to help you summarize your security posture and map your attack surface area. You can invite your team members to the account, set up scheduled scans for continuous security monitoring, and use APIs + webhooks to integrate the vulnerability scans into your own processes and applications.
The flexible and affordable pricing plans make it a popular choice for small and medium-sized businesses as well as IT contractors and managed security service providers (MSSPs).
HostedScan Security has a free tier that you can use to try the product before purchasing.
Note: Do check out our detailed HostedScan review for more information!
3. ManageEngine Vulnerability Manager Plus
ManageEngine Vulnerability Manager Plus detects vulnerabilities and exposure points across local and remote endpoints in your enterprise network. It then highlights weak spots hackers might exploit, allowing you to take proactive measures to secure your network.
What I liked about Vulnerability Manager Plus during my research and while going through its online demo, is its ability to prioritize vulnerabilities based on severity, exploitability, age, the number of affected systems, and the availability of fixes. This helps you address critical threats first, securing your system before tackling less severe vulnerabilities.
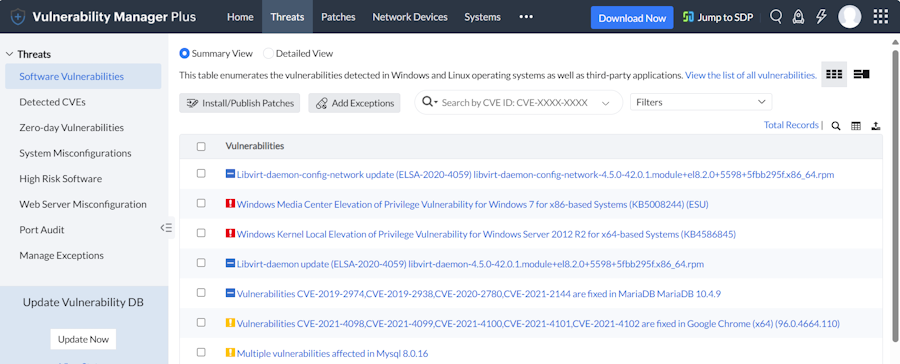
The “Threat” menu in the Vulnerability Manager Plus dashboard provides information about key security issues. This includes Software Vulnerabilities, Detected CVEs, Zero-Day Vulnerabilities, System Misconfigurations, High-Risk Software, and Web Server Misconfigurations.
The key features of Vulnerability Manager Plus include:
- Risk assessment and prioritization of vulnerability mitigation.
- 75+ CIS benchmarks to audit and maintain your systems to spot violations.
- Automated patch management for Windows, Mac, Linux, and 500+ third-party applications.
- Security configuration management to optimize systems’ security.
- Zero-day vulnerability mitigation.
- Detecting and patching vulnerabilities in network devices.
ManageEngine Vulnerability Manager Plus offers Professional, Enterprise, and Custom plans. Enterprise pricing starts at $1,195/year, while a perpetual license costs $2,987 plus a $598/year maintenance and support fee. Contact the company for custom quotes.
A free demo is available.
4. Tenable Nessus
Nessus by Tenable is one of the popular vulnerabilities’ management, used by millions of users. It covers numerous asset types.
- Operating system
- Hypervisors
- Network devices
- Database
- Web servers
- Firewall
Nessus is fast in discovering and got high-accuracy with low false positives.

Some of the great features of Nessus by Tenable are:
- Detailed reporting
- Reports can be automated to download using an API
- Compliance & sensitive content auditing ready.
- Capable of scanning IPv4/IPv6 and hybrid networks
- Deploy as software or virtual appliances
- Available on-premises or in the cloud
- A risk score based on CVSS
More than 24,000 organizations trust Nessus. They offer a FREE trial for seven days.
5. AlienVault USM
Now AT&T, AlientVault USM (Unified Security Management) is an enterprise-ready solution for on-prem or cloud infrastructure.

USM is available as SaaS, which means you don’t have to worry about software installation and setting them up. You can get it started in minutes to scan the entire infrastructure. It supports the major cloud like Azure and AWS.
Along with network vulnerability scan, it also helps with asset discovery, behavioral monitoring, intrusion detection, event, and log management. With their beautiful dashboard, you can get your infrastructure security posture and let you drill-down to a detailed view to understand and mitigate the risks.
For compliance, there are pre-made reports templates such as PCI-DSS, NIST CSF, HIPPA, ISO 27001 available for you. AlienVault integrates well with cloud-based security products (Cloudflare, SOPHOS, ServiceNow, Google Workspace, Cisco Umbrella, Okta, McAfee EPO, etc.) and got more than 350 plugins.
6. InsightVM
An award-winning Nexpose vulnerability scanner inspires InsightVM by Rapid7. InsightVM is live vulnerability management and endpoint analytics.
With the help of InsightVM, you can collect, monitor, and analyze the risk for new and existing networks.

Some of the features are:
Powerful analytics – get advanced threat exposure analytics with actionable information on risks for faster remediation.
Continuous monitoring – insight agent automatically and continuously monitor endpoint for vulnerability and provide live monitoring. It offers dynamic monitoring for AWS, VMware, Azure.
Liveaboards – a clickable dashboard with real-time data for CISO to the system administrator to analyze infrastructure security.
Risk scores – vulnerabilities are tagged with the standard CVSS rating so you can take action on priority.
Integration – Integrate with your favorite tools, including Metaspoilt, InsightIDR, Nexpose, ServiceNow, McAfee, Splunk, etc.
You can get it started with a FREE trial for 30 days to experience InsightVM.
7. Acunetix
Acunetix network scanner tests network perimeter for more than 50,000 known vulnerabilities and misconfiguration.
Acunetix leverage OpenVAS scanner to provide a comprehensive network security scan. It’s an online scanner, so scan results are available on the dashboard where you can drill down the report, risk, threats.

Risk items are associated with the standard threat score and actionable information, so it’s easy for you to remediate.
Some of the following checks are done.
- Security assessment for routers, firewall, load balancers, switches, etc
- Audit weak password on network services
- Test DNS vulnerabilities and attacks
- Check misconfiguration of a proxy server, TLS/SSL ciphers, web servers.
Acunetix offers a 14 days trial, so give a try to see how it works.
8. OpenVAS
One of the famous open-source vulnerability scanning and management solutions.
OpenVAS is a framework which includes many services and tools and makes perfect for network vulnerability test.

OpenVAS’s community edition is free to use, and it is based on an open-source model. However, if you are looking for support and extensive features, you can subscribe to Greenbone.
9. Qualys
Protect your data center and networks with Qualys.
Qualys offers a suite of security products to guard the entire infrastructure. With the help of continuous monitoring, you can monitor your network and get alerted in real-time for threats and system change.

And with the help of the vulnerability management application, you can discover, detect, and protect the devices.

You can get it started with the trial to experience it.
Conclusion
Managing network vulnerabilities is challenging, and I hope the above solutions help you find security risks in your infrastructure so you can mitigate them on priority.


