As an online business owner, there are many things you have to take care of to secure your application, provide better authentication, a nice user experience, and more.
If you offer user authentication on your web applications, then there are few options you have. Traditionally, one goes for username and password authentication.
But there is a problem…
Can you count how many passwords you own?
You’re puzzled, right?
It seems like I just asked you some high-level mathematics.
Yes, it can be that hard.
It’s because you might have hundreds of passwords for accessing so many online solutions you utilize in your business or for your website. From emails and productivity trackers to project management, CRM, security solutions, you have passwords for each one of them.
Plus, you are advised not to use the same password in all the applications.
So, it becomes tough to remember each of them. And if you use a password manager, there’s still the likelihood of attacks. In case your passwords get hacked, all your passwords could be compromised.
You can’t imagine how scary it may turn out to be for your business!
So, what’s the solution?
Don’t worry; there’s a world beyond passwords.
And this world is – passwordless authentication.
That’s right!
As a developer, website owner — you can implement passwordless authentication, so your users no longer have to remember passwords and think about losing it or getting it stolen. And that’s the goal of this article — to introduce some of the best solution providers out there for this.
You can trust Geekflare
At Geekflare, trust and transparency are paramount. Our team of experts, with over 185 years of combined experience in business and technology, tests and reviews software, ensuring our ratings and awards are unbiased and reliable. Learn how we test.
1. Authsignal
Secure your customer journeys with Authsignal. Focused on deploying drop-in Passwordless Authentication flows (including Passkeys), Authsignal delivers a suite of enterprise-ready tools to prevent fraud, secure customer journeys, and enable the rapid deployment of passwordless authentication anywhere in your customer experience.
Authsignal works with your current technology stack to augment your customer experience, enabling you to deploy passwordless authentication into your existing customer journeys in weeks.

Authsignal is a scalable solution that enables drop-in password authentication and MFA flows into any architecture including existing identity providers like Auth0, Microsoft Azure AD B2C, and Duende IdentityServer. Turn on fraud prevention with the flick of a switch, and deploy best-in-class risk scoring and fraud mitigation tools via our Enhanced Data Marketplace.
The No-Code Fraud Rules Engine enables risk-based user journeys to be deployed in a matter of hours, greatly reducing the cost and time of engineering and development teams, typically associated with hard-coding rules. Drop in Passwordless Authentication challenges anywhere in the customer journey.
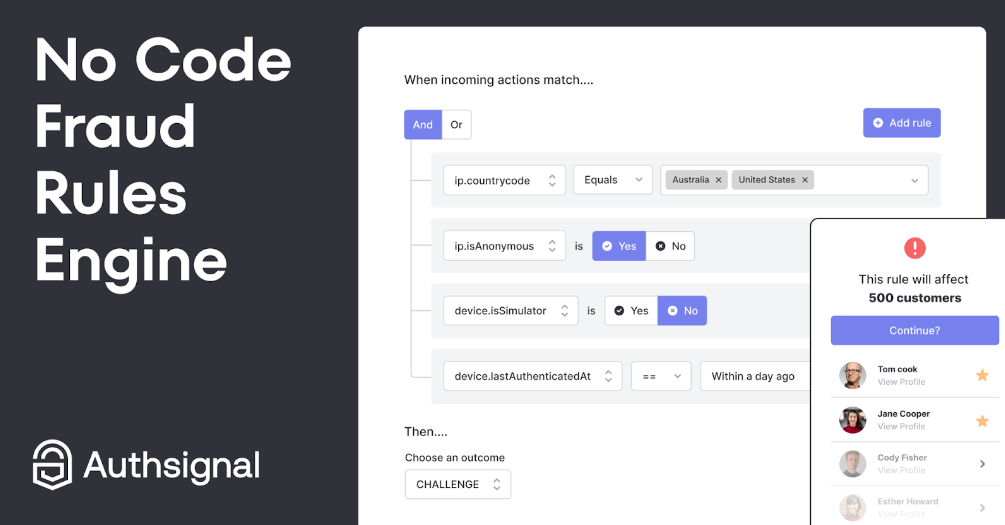
Reduce Customer Support time with a single view of the customer. Utilizing the Track Action API, Authsignal offers a single FraudOps view of your customers’ actions, enabling the reduction of queue times and bringing peace of mind to Fraud and Operational teams. Gain a complete Audit trail of actions.
Features:
- No Code rules engine — build rules in minutes, create challenge flows, Block, Allow, Challenge and Review
- Open ID Connect integration
- Single View of the Customer
- Deploy either Multi-Factor Authentication or Passwordless Authentication
- Passwordless Authentication Support for
- Passkeys
- TOTP/Authenticator apps
- SMS & WhatsApp OTP
- Email Magic links
- Native In-app push approvals/notifications
Authsignal Marketplace
Integrated with industry-leading fraud, risk and AML partners, Authsignal brings together the best-in-class vendors to deliver a comprehensive view of customer behavior in one central place. Leveraging the enchanted data marketplace enables customers to create a central workspace for Fraud Ops teams to manage investigations and make decisions easily.
Authsignal integrates with:
- Veriff (IdV/KYC)
- iProove (IdV/KYC)
- Deduce (Identity Network)
- Coinfirm (AML/KYC)
- SMS Sim Swap Shield
2. Okta
Powered by Auth0, Okta has multiple ways to go passwordless, such as social logins, OTPs, passkeys, and magic link emails. The best part, except for a user-friendly and secure login experience, is the ease of implementation.
For instance, the developers can switch on a toggle from the Auth0 dashboard to start with magic link authentication. Besides, it allows settings for desired OTP expiration time limit and length. Also, you can toggle off the magic link signups easily. It uses its own SMTP provider to send passwordless emails. Still, one can configure for any custom SMTP email service as well.
Okta is compatible with both email and SMS to send OTPs. Configuration for using email OTPs is quite similar to magic links. For SMS, it uses Twilio by default, but one is free to set any custom SMS gateway. Likewise, the admin dashboard allows for setting OTP expiry, length, and syntax, among other things.
Regarding social logins, Okta supports over 40 channels and also allows integrating any OAuth2 provider to create custom connections.
Okta has trial plans for securing your workforce and consumers.
Its Workforce Identity Cloud offers over 7,000 pre-built integrations and effortless onboarding. Plus, it can work hand-in-hand with the tools you might already use. The customer Identity Cloud trial allows 7000 monthly active users and unlimited logins. You can also go for branded login experiences. It also provides brute force protection and IP throttling for suspicious login attempts.
3. FusionAuth
FusionAuth is an excellent email-based option that supports passwordless login. It enables easy and quick authentication for different applications from the web, desktop, console, and mobile apps.
You can also create native login experiences or utilize FusionAuth’s OAuth, SAML-v2 front ends, or OpenID Connect. It also supports other industry standards such as OAuth 2, including PCKE and Introspect.

Include social logins in minutes along with federated logins through Active Directory. When it comes to multi-factor authentication, FusionAuth streamlines everything; you do not need to buy expensive add-ons for it.
FusionAuth supports code-based MFA and SMS, plus the inclusion of “Remember this Device” through their 2-factor device ids. Tracking all the users who logged in previously into a system is possible, which reduces friction.
Through anomalous login detection, FusionAuth can detect suspicious events like brute-force attacks. You can empower your users with an interesting option to lock other users if an attack happens in their system. In addition to this, it also supports the family modeling system and advanced consent systems like Email Plus and COPPA.
4. Trusona
The likelihood of credential stealing and other risks that your users are always concerned about can be reduced by avoiding traditional credentials in your applications. You can implement Passwordless authentication by Trusona.
The passwordless solution supports a multitude of devices and channels for your customers and employees. Specific fields for verification, including date of birth, first name, address, etc. are easily customizable on using this solution.
Trusona has patented, and advanced anti-replay technology that ensures all the data is safe from attacks about credential replays and bot attacks. It can be used from 2-factor authentication with Essential to 3-factor authentication using an employee badge or a government ID.

You can let your users create rapid time-to-value by reducing enablement costs and IT training to onboard new users. It also helps to reduce helpdesk call volumes and resources by reducing password reset issues altogether. Trusona also has a thoughtful UI that further strengthens its security.
The passwordless SDK has an impressive user interface with plain English having no tech jargon. It is available for both Android and iOS utilizing native APIs along with JSON RESTful APIs available for web apps.
They also provide the first identity proofing service in the industry that utilizes DLDV (Driver License Data verification service) by AAMVA to accurately and quickly verify the actual identity. By embedding this capability, you can deliver secure remote and in-person usage.
5. Keyless
Enable passwordless authentication on your applications using Keyless that your users can trust. You can deploy Keyless on various appliances and devices as they do not entirely rely on sensors and device hardware.
Keyless protects your users from credential reuse, phishing, and fraud. It lets your users have a frictionless experience through multiple channels while accessing your business applications. Keyless is packed with some out-of-the-box technologies such as unique identification, where it identifies users natively in each point.
As a result, it can ensure only the allowed users are logging in to the systems. In case a user loses their access to any of their devices, there’s an option for data recovery and backup through which the users can recover their respective identities.
Keyless provides high-level security as there’s no central hub where password data is stored to be stolen. It makes information available only to the user and has built-in privacy that preserves your users’ interests.
Keyless never processes or stores PII, and it also helps you comply with regulations. They utilize industry-leading UX that reduces MFA fatigue and authentication friction. It also embraces anti-fraud technology along with behavioral authentication that helps minimize the risk of corporate account takeover (CATO) in addition to other thefts associated with your applications.
6. Swoop
When security meets elegance and simplicity, Swoop comes in. They have two powerful and patented technologies – Magic Message and Magic Link.

Give your users the flexibility of choosing how they wish to authenticate by integrating Swoop through two methods:
- Receiving an email having a Magic Link, which is great for desktops. Here, the users have to type the email address and use the link.
- Sending a mobile-friendly Magic Message. Here, they need to hit “send” over an auto-generated email, no typing required.
7. Magic
Securing 20 million+ authentications each month, Magic is literally doing magic when it comes to providing a seamless passwordless experience.

By implementing Magic into your applications, you can lift your customers’ entire authentication overhead, which helps them focus more on things that are important to growing business. Magic has system-anomaly detection, which mitigates login attacks based on app usage patterns.
Magic ensures reliability and speed by eliminating email redundancy. They maintain enterprise-level security and compliance by using SLAs and SOC-2 that are battle-tested for crucial events. It supports multiple languages and lets you empower your users to customize their brands’ look and feel.
Frequently Asked Questions
For those who are interested in learning more about passwordless authentication, here are some FAQs.
Passwordless authentication is a system that swaps traditional password usage with more safe and secure factors. These high-level security methods might include a fingerprint, magic link, secret token, etc. that’s delivered via a text message or email.
It eliminates the need to generate a password to gain access to the systems. And this is good for your users as they won’t find any hassle while using a website or application developed by you.
The benefits of passwordless authentication are:
Enhanced experience: Whether it’s accessing the business emails, fingerprint scanning, or verification on an application, the users are not required to memorize their password credentials anymore, which is a true delight you can offer to your customers. It also leads to a great screen-time experience.
Stronger security: Passwords that are user-controlled are highly vulnerable to attacks like corporate account takeovers (CATOs), credential stuffing, brute-force attacks, etc. So, when there would be no passwords to exploit, users won’t get into any trouble while using your applications.
Increased convenience: Why go for a complex password that users need to keep track of all the time if they can have efficient options out there through passwordless authentication. Give your users extra convenience while gaining access or getting information anywhere and anytime they want.
Email — where the users need to enter their email address to get a magic link or unique code to log-in
SMS — entering a phone number is required to get a unique one-time code to log-in.
Biometric — where fingerprint scanning, iris scanning, or face-scanning takes place to get access
There are so many services and APIs available where you can leverage passwordless authentication and integrate it into your applications instead of building an in-house solution. They are cost-friendly, save your development time, and bring you great security by just paying some nominal fee, and some are even free!
Passwordless authentication leverages technologies like digital certificates. It includes cryptographic key pairings.
The steps for the same are as follows:
A private key gets stored on a user’s local device and then linked to a type of authentication factor such as face recognition, fingerprint, or unique PIN.
Meanwhile, the public key moves to that application or website to which the user wants to access
So, if you have made up your mind to use passwordless in your applications, you have made a good decision.
The world is moving slowly towards passwordless as the risk of online threats never seems to stop. In a situation like this, you need to make sure you develop applications laced with the latest technologies that help your users reduce the probability of attacks and promote your product.


