Passwords have been a longstanding concern. Notoriously, many of us default to predictable, weak passwords, and even when we don’t, remembering complex ones becomes a challenge.
The unsettling fact is that even strong passwords with intricate combinations are not immune to phishing and scams. Password managers were the temporary solution, but they have their shortcomings and vulnerabilities.

But the horizon brings something promising: After nearly ten years in the making, passkeys are set to revolutionize our digital security. Here’s a primer on what they are, how they’re set to change the digital authentication landscape, and what this will mean for your consumer app.
Understanding Passkeys
Instead of the traditional username-password combo, a passkey provides a more secure and effortless method to log into online platforms. The beauty of passkeys lies in their reliance on public-key cryptography. Without diving too deep into the technicalities – every time you log in, your device receives a unique login credential.
This process minimizes the risk of hackers obtaining your information. This breakthrough is the result of efforts by the FIDO Alliance, a consortium of tech giants like Apple, Google, Microsoft, and many others, who recognized the pressing need for a safer authentication method.
How Do Passkeys Work?
Passkeys come under the umbrella of Web Authentication (WebAuthn). This system leverages public-key cryptography, a tried-and-tested method used by various secure messaging and payment platforms.
Here’s a brief breakdown:
- Public and Private Keys: Upon account creation, two keys are generated. The public key, which is stored on the service’s servers, doesn’t need to be confidential. In contrast, the private key remains safeguarded on your device.
- Authentication Process: When logging in, the service utilizes your public key to challenge your device. The private key on your device meets this challenge without revealing any sensitive details. This ensures secure, hacker-proof authentication.
For users, this process remains largely invisible. A simple device or browser prompt for a PIN or biometric verification, like FaceID or TouchID, is all you’ll encounter.
Passkeys have an additional layer that synchronizes these keys amongst the respective big tech’s (Apple, Google, Microsoft) cloud services. This important layer fills the user experience gap, allowing for seamless switching between devices without re-enrolling keys, which has been deemed a significant gap to mainstream adoption of FIDO2.
Because Passkeys, by definition, encompasses multiple factors, it meets the definition of Multi-factor Authentication (MFA), specifically meeting the following:
- Possession Factor (something you have) – The user possesses the device containing the private key
- Inherence Factor or Knowledge factor – The user’s biometrics (FaceID, Touch ID, Fingerprint) or Device PIN code
These properties make Passkeys a valid sole authentication factor for sign-in scenarios or supplement other factors in step-up authentication scenarios. Check out this Passkeys demo for a real-world implementation.
Device Compatibility
At the moment, cross-platform functionality for passkeys remains a work in progress. Apple’s iOS and macOS devices support passkeys, as do Google’s Android devices. Microsoft, too, is enhancing its support for passkeys, with significant updates on the horizon.
Here’s an up-to-date device support list.
What can you do to start implementing passkeys?
Implementing passkeys can be straightforward, provided you have the necessary infrastructure in place. A critical piece in your architecture is a WebAuthn back-end service or server, which provides the back-end API endpoints to manage the full lifecycle of passkey management.
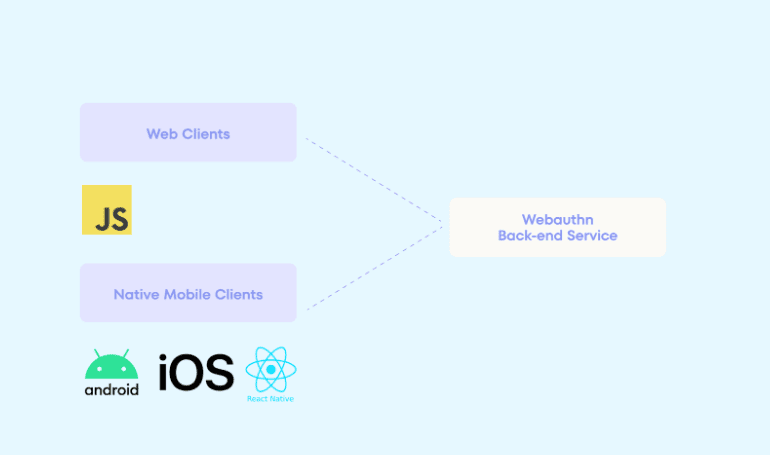
Once a WebAuthn service is established, access to the client-side SDKs and libraries is necessary to perform the client-side enrolment and verification ceremonies. The good news is that there are now many widely available client-side libraries that can simplify the process.
- Javascript SDK for passkeys
- React Native SDK for passkeys
- iOS SDK for passkeys
- Android SDK for passkeys
It is important to note that the technical integration is only one part of a wider implementation. User experience and security considerations should be well understood.
Passkeys, the future is now.
We are now at the exciting intersection of the rapid maturity of Passkeys technology. Modern browsers and devices, especially in the Apple and Android ecosystem, widely support Passkeys, and mainstream consumer apps are now releasing Passkey features (e.g., Kayak, TikTok). Finally, technical integration has been made simpler with out-of-the-box passkey solutions like Authsignal, offering all the component parts like a back-end WebAuthn service and client SDKs.
There shouldn’t be any major excuses or barriers for your application to adopt Passkeys as a critical part of how you interact with your customers, offering them a seamless user experience but, more importantly, one that is highly secure.


