A cyberattack can cause irreparable damage to your online store. You can lose money, crucial data, and reputation. What’s worse, a successful cyberattack can debilitate overall business viability. So, you must improve your online store’s security to mitigate E-commerce security threats.
But what are the top security threats online business owners are facing today, and what can you do to protect your online store from those cyber threats? Read on to find out.
Why Should You Focus on E-Commerce Security?

The most crucial reason hackers carry out cyberattacks is money, and the E-commerce industry has plenty of it. So, it is no surprise that E-commerce websites witness a barrage of cyberattacks across the globe.
The Sophos Ransomware Report 2023 states that 66% of businesses had a ransomware attack last year. And the mean ransomware recovery cost (excluding the ransom payment) is $1.82 million.
E-commerce companies manage large volumes of data. So, even a minor data breach incident can make you financially broke. The average global cost of a data breach is $ 4.45 million.
All users enter their payment information (banking or credit card details) to complete their transactions on E-commerce websites. Consequently, online payment fraud is common in the industry.
In fact, the E-commerce industry lost more than 40 billion USD in 2022 due to online payment fraud.
That said, you should bolster your defenses to protect your online business from various E-commerce security threats and issues.
Critical E-Commerce Security Threats You Should Know About
The following are common security threats. E-commerce businesses are facing these days.
Financial Fraud
The E-commerce industry is plagued with various types of financial fraud. However, credit card fraud is one of the top E-commerce security threats. In such a fraudulent activity, cybercriminals use stolen credit card information to make unauthorized transactions on online stores.

Another familiar tactic threat actors employ to commit financial fraud is account takeover. It is a type of identity theft attack in which cybercriminals illegally get access to users’ accounts on online stores and bank details saved with such accounts. A successful account takeover attack can lead to fraudulent purchases from the victims’s compromised accounts.
Chargebacks are a big challenge to E-commerce websites, hurting their revenues. An E-commerce chargeback happens when a customer disputes a charge from an online shop on their credit card statement.
They ask their bank to reverse the charge, and if the bank agrees, the seller loses both the money and the product sold. And the seller may also have to pay a chargeback fee.
Why does a customer request a chargeback?
The most common reason is that a threat actor got access to their credit card details and made unauthorized online transactions on an online store.
However, a customer may also abuse the chargeback process due to their dissatisfaction with the product or unfriendly return process. Whatever the reason, an e-commerce store is likely to lose money.
Fake Return and Refund
Fake returns and refunds occur when someone claims to return a product but sends back a different, damaged/used item or nothing.
The e-commerce store might issue a refund or send another product, losing money and inventory through deception. This fraud can also cause extra costs like shipping and restocking.
Phishing and Pretexting
Malicious actors employ phishing techniques and pretexting attacks to trick users into sharing sensitive data, such as login credentials for online stores, credit card data, or other financial data.
Once cybercriminals have the necessary details of users, they make unauthorized purchases on E-commerce websites.
Spam
Spam is an irrelevant message containing a malicious link. The objective of sending spam is to trick users into clicking on the links, which will cause them to unintentionally reach spam websites or install malware on their computer systems.
E-commerce websites have massive traffic, so hackers target them with spam messages to reach a broad audience. Typically, cybercriminals leave spam messages in blog comments and social media post comments, hoping users will click on those links.
Spam affects the speed, security, and user experience of your E-commerce website.
DDoS Attacks

The objective of DDoS attacks is to disrupt an E-commerce website and affect its sales.
In a distributed denial of service attack (DDoS), threat actors flood your online store with traffic from multiple sources so much that it becomes inaccessible to legitimate users.
And if shoppers cannot access your E-commerce website, you will lose sales.
Clickjacking
In a clickjacking attack, malicious actors can trick your shoppers into clicking a web page element disguised as another element. As a result, users may unknowingly download malware, visit harmful websites, share sensitive info, change account settings, or transfer funds.
For example, a malicious actor can hide malware under the “Download Discount Coupon” button after compromising your E-commerce website. Unsuspecting customers who click on it may unknowingly download malware onto their devices, compromising their security.
As your store transmits malware to victims’ devices, it will create a negative PR for your brand.
Malware

Malware is one of the biggest E-commerce threats companies are facing today.
Here are critical malware threats you should know about:
E-Skimming
In this attack, a cybercriminal implants skimming code onto your E-commerce payment card processing webpage to seize credit card and personal information. Then, the threat actor transmits the stolen data to a domain they manage.
Ransomware
Ransomware is a type of malicious software that can encrypt the files or data on your E-commerce website and make them inaccessible.
Then, the attacker asks for a ransom in exchange for the decryption key.
A ransomware attack can disrupt your online store’s operations, cause financial losses, and damage your store’s reputation if customer data is compromised.
So, you must take proactive measures to prevent ransomware.
Trojan Horse
Trojan horses are deceptive software programs that appear legitimate but contain malicious code.
An attacker may distribute a Trojan horse disguised as legitimate applications or files. Once installed on your device, it can steal sensitive information about your online store, such as login credentials for the admin console.
So, a trojan horse can compromise the overall security of your e-commerce website.
Keylogger
A keylogger can spy on every keystroke you make on your computer or device, including login credentials and sensitive information.
If an attacker is able to install a keylogger on your business computer, they can capture admin login credentials. And then, they can get unauthorized access to your E-commerce website’s backend.
Data Breach

A data breach is a significant E-commerce threat. This is because even a minor data breach has severe implications, including financial loss, reputation damage, and legal & regulatory consequences.
Some common reasons for data breaches are but not limited to:
- Outdated software
- Poor password practices
- Phishing attacks
- Human error
- Malware
So, you should implement the best data security solutions to protect your data.
Malicious Code Injections
Malicious code injections, like SQL and XSS attacks, can pose severe threats to your E-commerce store.
An SQL injection attack happens when a cybercriminal exploits vulnerabilities in your E-commerce website’s input fields to insert malicious SQL queries. These queries can manipulate or steal data from the database, potentially compromising customer information or taking control of the store.
In an XSS (cross-site scripting) attack, a threat actor injects malicious scripts into your store’s web pages, which are then executed by users’ browsers. This can lead to unauthorized access, data theft, or the spreading of malware.
You can run a CSP (Content-Security-Policy) Header test to know if your E-store uses CSP headers to defend against XSS, malicious code injection, and clickjacking.
Bots
Hackers can create bots that can scan your entire online store and gather crucial information such as inventory, prices, highest-selling products, etc. Then, hackers can sell critical data to your competitors.
Equipped with such vital information, your competitors can strategically price their products to lure customers. After all, who doesn’t like to buy a product at the lowest possible price?
Therefore, you must implement one of the best bot detection and mitigation solutions in your company.
Brute Force Attack
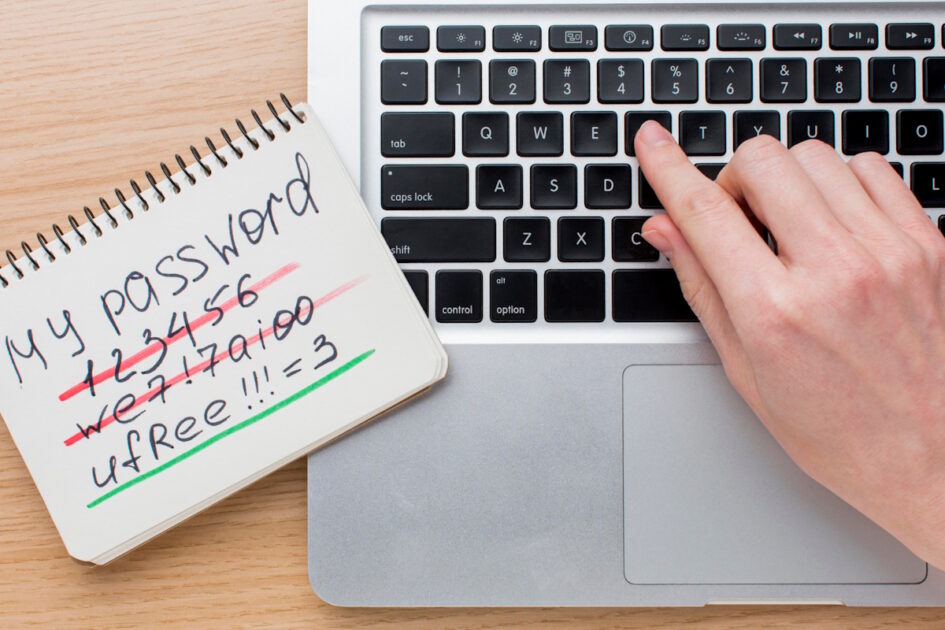
A brute force attack is a hacking technique that employs trial and error to crack the password of your online store’s administrator console. In this type of attack, a threat actor first makes a connection with your website. Then, they will run automated programs to guess your password.
So, you must stop using common passwords and create strong passwords with the help of a password tool.
Also Read: Password Spraying Attack: How To Detect and Mitigate Them?
MITM Attack
In a man-in-the-middle (MITM) attack, a threat actor eavesdrops on communication between your online store and a legitimate user. As a result, they can gather sensitive customer data like login credentials, credit card information, etc.
Then, they can use collected information to change the victim’s account settings or make unauthorized purchases from the victim’s compromised account on your online store.
How To Prevent E-Commerce Security Threats

The following strategies can help you fortify your defense against E-commerce threats.
#1. Secure Payment Methods and Payment Gateway
Though it offers convenience, allowing customers to save their credit card details is a risky affair. Therefore, you should avoid saving credit card information on your web server.
By implementing a third-party payment processor like PayPal or Stripe, you take payment processing away from your website. This ensures better security of customers’ sensitive data.
You can check these popular payment processing solutions to find the best fit for your business.
#2. SSL Certificate

An SSL certificate proves your website’s authenticity and tells your customers that the connection between your website server and users is encrypted. This means none can intercept what customers are doing on your website, ruling out the possibility of MITM attacks.
Also, an SSL certificate is a part of PCI DSS compliance. And many browsers won’t open your online store if your E-commerce website doesn’t have an SSL certificate.
So, you must get an SSL certificate on your E-commerce website.
#3. Customer Address Verification
Credit card processors and banks typically provide an Address Verification Service that flags dubious transactions instantly.
This service compares the billing address the customer gives with the one the bank has on record. During payment processing, if there’s a mismatch, the system may reject the sale or mark it for further review.
#4. Non-Repudiation
Non-repudiation ensures both the parties, your online store and customers, cannot deny the transaction they completed.
Therefore, implementing non-repudiation measures like digital signatures can prevent customers from denying purchases and reduce E-commerce chargebacks.
#5. Strong Password Enforcement
Threat actors carry out various password attacks to guess the login credentials of your admin console. So, you should create strong, difficult-to-guess passwords.
Using a password manager in your company can make password management more effortless. It will help everyone create strong, complex passwords and inform you if any are found in a recent data breach.
You can check these open-source password managers to pick the best password management tool.
And if you’re not a fan of cloud-based password management, you can check this on-premise password manager.
#6. MF Authentication
Multi-factor authentication (MFA) adds an extra layer of security to your E-commerce store. When enabled, MFA confirms your identity by two or more factors such as code, PIN, biometrics, etc.
If a threat actor happens to get access to your passwords, they cannot access your admin console because they don’t know other factors.
Also Read: Passwordless Authentication Solutions for Better Application Security
#7. Anti-Malware and Antivirus Tools
Cybersecurity tools like anti-malware and antivirus solutions can help keep your E-commerce website safe from malicious attacks.
Malware is a blanket term for various malicious programs, such as ransomware, keylogger, remote access trojan, etc. Installing a powerful anti-malware program can protect you from various threats.
Also, make sure you have enabled automatic updates on these tools.
Read More: How To Remove Malware from PC
#8. Admin Panel and Server Security
You should create complex passwords for the admin panel of your E-commerce website.
Use a combination of upper case, lower case, numbers, and special characters to create complex passwords. And keep changing your admin passwords from time to time.
You should implement the principle of least privilege, which ensures that users will have minimum access to the admin panel required to perform their jobs.
Also, you should ensure that the admin panel notifies you when an unknown IP address tries to access it.
#9. Web Application Firewall

A web application firewall (WAF) is a security tool that monitors, filters and blocks incoming and outgoing data packets from an application or website.
By implementing a web application firewall, you can regulate web traffic that enters and leaves your online store. And you can block malicious attempts like SQL injections, XSS attacks, and DDoS assaults. T
You can explore these open-source web application firewalls to pick the best solution for your store.
#10. Data Backups
Having up-to-date backups ensures that even if critical data is compromised or lost, you can quickly recover and continue serving customers without prolonged disruptions, financial losses, or reputational damage.
When you back up data from your online store, follow the 3-2-1 rule. It states that you should make three copies of the data and save data on two different devices/platforms, one of which must be offsite storage.
You can use any enterprise data backup solution to automate the data backup process.
Read More: Data Backup Best Practices Everyone Should Follow
Conclusion
With the unprecedented growth of the E-commerce industry, the E-commerce threats are also multiplied. Now, malicious actors are targeting online stores more than ever. Even a minor data breach can jeopardize your store’s viability.



